Web Application Firewall (WAF) identifies and blocks malicious traffic targeting your websites or applications. It helps protect against common web attacks by scrubbing and filtering traffic. WAF forwards legitimate, safe traffic to your servers while blocking malicious requests. This ensures smooth website operation and safeguards business stability and data security.
Scenarios
WAF is designed for all users, whether their web servers are deployed on Alibaba Cloud or in other environments. It is widely used across various industries, including financial services, e-commerce, O2O, Internet+, gaming, government, and insurance. Alibaba Cloud WAF protects HTTP/HTTPS traffic for websites and web applications, defending against a wide range of Web attacks to keep your business secure and stable.
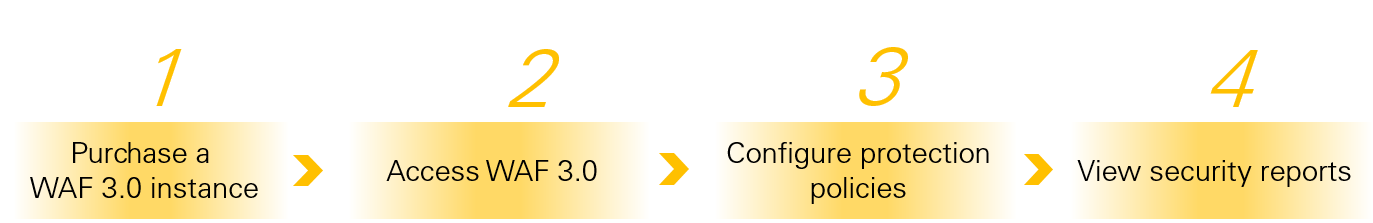
Get Started with WAF
For a quick start example, see Protect an ECS instance against CC attacks using WAF.
WAF 3.0 versus WAF 2.0
Version relationship: WAF 3.0 is a next-generation Web Application Firewall built on WAF 2.0. It features a new underlying architecture, updated pricing plans, redesigned console configuration logic, and an improved user experience. You cannot run WAF 2.0 and WAF 3.0 in the same Alibaba Cloud account.
Purchase policy: You can no longer purchase new WAF 2.0 instances. Only WAF 3.0 is available for purchase. If you already use WAF 2.0, you can continue to use, renew, or upgrade your existing instances. Your Service-Level Agreement (SLA) remains valid.
Upgrade method: To access enhanced features and an improved experience, upgrade from WAF 2.0 to WAF 3.0. Use the self-service migration tool to automatically migrate your WAF 2.0 instances to WAF 3.0. For steps, see How to upgrade a WAF 2.0 instance to WAF 3.0.
Main differences between WAF 3.0 and WAF 2.0
Billing method
Difference | WAF 3.0 | WAF 2.0 | |
Subscription instance editions | Basic Edition, Pro Edition, Enterprise Edition, Ultimate Edition. | Pro Edition, Enterprise Edition, Ultimate Edition. | |
Billing items | Traffic specification | Uses queries per second (QPS) as the sole traffic unit. You do not need to manage bandwidth. Subscription instances support elastic pay-as-you-go QPS, which prevents sandboxing due to QPS overuse. | Supports both QPS and bandwidth. You must convert between them. |
Domain name specification | No distinction between primary domain names and subdomains. You are billed per domain name added. | Distinguishes between primary domain names and subdomains. | |
Hybrid cloud access | Enterprise Edition and Ultimate Edition include hybrid cloud access. | You must purchase Hybrid Cloud WAF Exclusive separately. | |
Pay-as-you-go billing unit | Introduces a unified billing unit: Security Capacity Unit (SeCU). This simplifies billing. Each SeCU costs USD 0.01. | There is no standard unit of measurement. | |
Asset onboarding and mitigation settings
Difference | WAF 3.0 | WAF 2.0 |
Cloud native mode |
| Transparent proxy mode supports only ALB, ECS, and CLB instances. |
Protected objects for mitigation rules | After you add a domain name or cloud product instance, WAF automatically creates a protected object. Create a mitigation template, configure mitigation rules in the template, and assign one or more protected objects to the template. | Configure mitigation rules for each domain name individually. If you use transparent proxy mode to integrate a cloud product instance, you must add all domains associated with that instance to WAF before you can configure custom mitigation rules. Otherwise, traffic applies only default mitigation rules. |
View mitigation rules |
| View only mitigation rules configured for a single domain name. |
Supported mitigation modules | New features include Custom Response, Threat Intelligence, Whitelist, Asset Center, and Security Report. For a full list of supported mitigation modules, see Mitigation Settings Overview. | For a full list of supported mitigation modules, see Overview. |