Custom protection policies let you define precise traffic rules for your website — blocking unwanted requests, throttling high-frequency traffic, or monitoring suspicious patterns without blocking.
Rule types
Custom protection policies consist of two rule types:
Access control list (ACL) rule — Filters requests based on match conditions such as client IP addresses, request URLs, and request headers. WAF evaluates each request against the conditions and performs the configured action when all conditions are met.
HTTP flood protection rule — Combines match conditions with rate limiting. WAF starts counting requests only when match conditions are met, then applies the action when the request rate exceeds your threshold. Use this rule type for hotlink protection, website backend protection, and brute-force prevention.
The rule type is set automatically: disable rate limiting to create an ACL rule, enable it to create an HTTP flood protection rule.
Limitations
The following specifications apply to subscription WAF instances.
| Specification | Pro edition | Business edition | Enterprise edition and higher |
|---|---|---|---|
| Custom rules per domain | 200 | 200 | 200 |
| Advanced match fields (beyond IP and URL) | Not supported | Supported | Supported |
| Rate limiting | Not supported | Supported | Supported |
| Custom statistical objects | Not supported | Supported | Supported |
Prerequisites
Before you begin, ensure that you have:
A WAF instance
Your website added to WAF (see Tutorial)
Create a custom rule
Log on to the WAF console.
In the top navigation bar, select the resource group and the region where your WAF instance is deployed. Select Chinese Mainland or Outside Chinese Mainland.
In the left-side navigation pane, choose Protection Configurations > Website Protection.
At the top of the Website Protection page, select your domain name from the Switch Domain Name drop-down list.

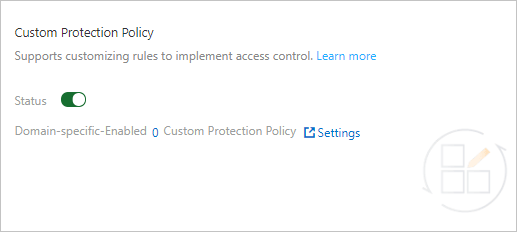
Click the Access Control/Throttling tab, find the Custom Protection Policy section, turn on Status, and click Settings.
NoteWhen custom protection policy is enabled, all requests to your website are checked. To exempt specific requests from inspection, configure a whitelist rule for Access Control/Throttling. For more information, see Configure a whitelist for Access Control/Throttling.
On the Custom Protection Policy page, click Create Custom Protection Policy.
In the Add Rule dialog box, configure the rule parameters.
Parameter Description Rule name A name for the rule. Matching Condition The conditions that trigger the rule. Click Add rule to add conditions — up to five. All conditions must be met for the rule to trigger. For supported fields, see Fields in match conditions. Rate Limiting Toggle to enable rate limiting and convert this rule to an HTTP flood protection rule. When enabled, configure the rate limiting parameters described below. Action The action WAF performs when the rule is triggered. See Actions below. TTL (Seconds) How long the action remains in effect after rate limiting is triggered. Required when rate limiting is enabled. Protection Type Set automatically based on rate limiting status: ACL (rate limiting off) or HTTP Flood Protection (rate limiting on). 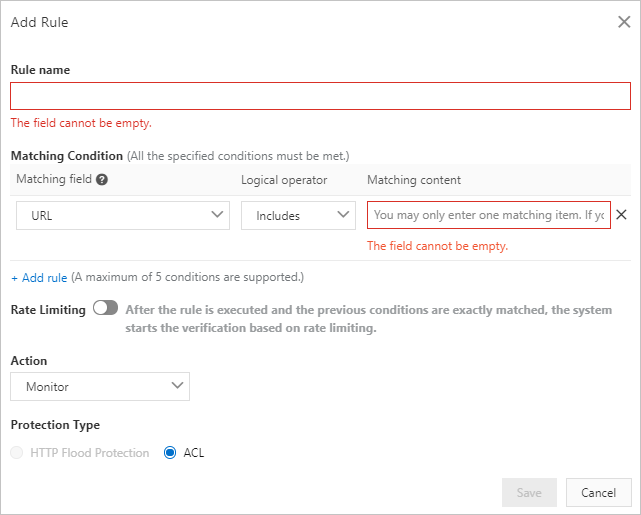
If you enabled rate limiting, configure the rate limiting parameters.
Parameter Description Statistical Object The attribute WAF uses to group and count requests. See Statistical objects below. Interval (Seconds) The time window during which requests are counted. Threshold (Occurrences) The maximum number of requests allowed from the statistical object within the interval. Exceeding this triggers the action. Status Code Counts the number or percentage of a specific HTTP status code within the interval, instead of counting all requests. Select Amount for a count limit, or Percentage (%) for a ratio limit. Take Effect For Which requests are counted: Feature Matching Objects counts only requests that meet the match conditions; Applied Domains counts all requests to the domain. 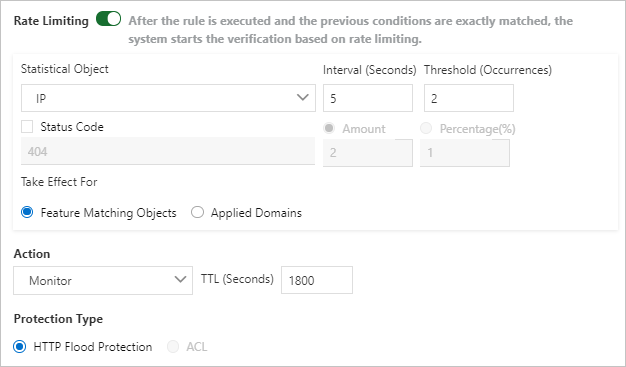
Click Save.
ImportantThe rule is enabled immediately after you save it. Verify your match conditions and action before saving to avoid unintended traffic impact.
After creating a rule, you can view, enable, disable, modify, or delete it from the rule list.
Actions
| Action | Behavior |
|---|---|
| Monitor | Triggers alerts but does not block requests. Use this to evaluate a new rule before enforcing it. |
| Block | Blocks the request. |
| CAPTCHA | Redirects the request to a CAPTCHA verification page. |
| Strict Captcha | Redirects the request to a stricter slider CAPTCHA verification page. |
| JavaScript Validation | Performs JavaScript validation on the request. |
CAPTCHA and JavaScript Validation apply to static pages only. For async requests (XMLHttpRequest or Fetch), enable these validations in the bot management module instead. For more information, see Configure anti-crawler rules for websites.
When rate limiting is enabled, latency may occur in rate calculations. WAF aggregates request data across multiple servers in the cluster, which can introduce a short delay before an action takes effect.
Statistical objects
The statistical object determines how WAF identifies and groups requests for rate counting. Choose based on your use case.
| Statistical object | What WAF counts | When to use |
|---|---|---|
| IP | Requests from the same IP address. | General rate limiting when clients connect directly without proxies. |
| Session | Requests from the same session. | Limiting per-user activity without relying on IP addresses. |
| Custom-Header | Requests that share the same value in a specified request header. | Tracking requests by a user ID, API key, or other custom header. |
| Custom-Param | Requests that share the same value in a specified query parameter. | Tracking requests by a specific URL parameter value. |
| Custom-Cookie | Requests that share the same value in a specified cookie. | Tracking requests by a session token or user identifier in a cookie. |
Custom-Header, Custom-Param, and Custom-Cookie are available on Business edition and higher.
Typical use cases
The following examples show how to combine match conditions and rate limiting parameters for common protection scenarios.
Hotlink protection
Block external sites from embedding your images or media files.
| Parameter | Configuration |
|---|---|
| Matching Condition | HTTP Referer does not contain your domain name |
| Rate Limiting | Off |
| Action | Block |
| Protection Type | ACL |
Website backend protection
Restrict access to admin paths to authorized IP addresses only.
| Parameter | Configuration |
|---|---|
| Matching Condition | URL starts with /admin |
| Rate Limiting | Off |
| Action | Block (combine with an IP whitelist rule to allow admin IPs) |
| Protection Type | ACL |
Login endpoint brute-force prevention
Limit the number of login attempts per IP address within a time window.
| Parameter | Configuration |
|---|---|
| Matching Condition | URL equals /login and Method equals POST |
| Rate Limiting | On |
| Statistical Object | IP |
| Interval (Seconds) | 60 |
| Threshold (Occurrences) | 10 |
| Action | Block |
| TTL (Seconds) | 600 |
What's next
Configure monitoring and alerting for your custom rules using CloudMonitor and Log Service. When traffic matches a custom rule, you receive alert notifications so you can respond quickly. For more information, see Configure WAF alerting.
Related topics: