Traditional WAF protection relies on known attack signatures, which means it cannot detect novel or unknown attacks. The positive security model uses machine learning to automatically learn your website's legitimate traffic patterns, establish a behavioral baseline, and generate custom protection rules that catch unknown attacks — without manual rule authoring.
How it works
The positive security model uses unsupervised learning to analyze your website's historical traffic. It assigns a security score to each incoming request and flags requests that deviate significantly from the established baseline. Based on these scores, WAF generates custom protection rules specific to your website. These rules work alongside WAF's other protection modules to defend against attacks at multiple network layers.
The model has two modes:
| Mode | Behavior | When to use |
|---|---|---|
| Warn (default) | Scores and logs suspicious requests without blocking them | During the initial learning period, to build confidence in the generated rules and identify false positives |
| Block | Blocks requests that match the generated protection rules | After you confirm the generated rules do not flag legitimate traffic |
Start in Warn mode. Switch to Block only after you review the security reports and confirm the generated rules are not causing false positives.
Prerequisites
Before you begin, ensure that you have:
A WAF instance running the Enterprise edition or higher
Your website added to WAF (see Tutorial)
Enable the positive security model
Log on to the WAF console.
In the top navigation bar, select the resource group and the region where your WAF instance is deployed. You can select Chinese Mainland or Outside Chinese Mainland.
In the left-side navigation pane, choose Protection Configurations > Website Protection.
At the top of the Website Protection page, select your domain name from the Switch Domain Name drop-down list.

On the Web Security tab, find the Positive Security Model section and configure the following parameters.
Parameter Description Status Enables or disables the positive security model. Mode The action WAF takes on detected suspicious requests. Set to Warn (default) to log requests without blocking, or Block to block malicious requests. 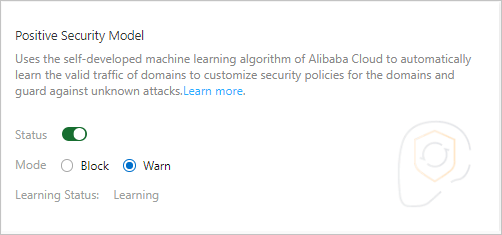
Enable the Status toggle. WAF begins learning your website's historical traffic. The initial learning process takes approximately 1 hour, though this varies with traffic volume. When learning is complete, WAF notifies you via internal messages, text messages, or email.
Monitor the security reports while the model runs in Warn mode. Review whether any legitimate traffic is being flagged. Check the reports over several days to account for normal variation in traffic patterns. Look for recurring false positives before proceeding.
Once you confirm the generated rules produce no false positives, set Mode to Block.
Manage the model lifecycle
| Scenario | Behavior |
|---|---|
| Disable the model | Learning results become invalid. Re-enabling the model triggers a full relearning cycle. |
| Upgrade your WAF instance | Upgrading to a higher edition does not affect existing learning results. |
| Traffic pattern changes significantly | Existing learning results may no longer reflect your actual traffic baseline (for example, if you change the service type). Reconfigure the positive security model to relearn your traffic. |
What's next
After the positive security model is running in Block mode, monitor your security reports regularly to catch any new false positives introduced by traffic pattern changes.