The WAF Protection Configuration module lets you combine multiple security capabilities—Core Protection Rule, HTTP Flood Protection, Bot Management, and more—to defend against SQL injection, cross-site scripting (XSS), HTTP flood attacks, and malicious bots.
How it works
Protected objects and protected object groups: When you onboard a domain name or cloud service instance to WAF, the system automatically creates a protected object for it. Group multiple protected objects into a protected object group for centralized management.
Protection modules: WAF offers modules for different threat categories, such as Core Protection Rule, API Security, and Bot Management. Enable a module by creating a protection template. Select modules based on your needs.
Protection templates: A protection template defines what to detect and who to protect. Each template has three parts:
Template type: Either a default protection template (automatically covers all current and future protected objects) or a custom protection template (applied only to objects you specify).
Protection rules: The detection logic and response action for each threat.
Effective objects: The protected objects or groups the template applies to.
Configuration process

WAF automatically creates protected objects for onboarded resources. View them on the Protection Configuration > Protected Object page.
Select protection modules based on your business needs. For example, to use the Custom Rule module, create a new protection template. For more information, see Create a protection template.
Add protection rules to the template. For more information, see Add protection rules to a protection template.
Select protected objects to apply the template. For more information, see Configure effective objects for a protection template.
Supported protection modules
Supported modules vary by WAF edition. For example, the Subscription Basic edition does not support Peak Traffic Throttling. For details, see Edition comparison.
Core web protection - Common
| Protection module | Use cases and recommendations | Initial status |
|---|---|---|
| Core Protection Rule | Uses Alibaba Cloud's built-in rule sets to block common web attacks: SQL injection, XSS, code execution, WebShell uploads, and command injection. Keep the default settings; adjust only to resolve false positives. | Includes an initial default protection template, enabled by default with the Block action. All onboarded resources are protected automatically. |
| Protection Rule Group (Legacy WAF only) Note This module has been upgraded to the engine configuration feature. For details, see the Announcement. | Rule groups referenced by Web Application Protection Rules. Keep the default settings. | Includes medium, strict, and loose rule groups. The medium rule group is enabled by default. Switch rule groups manually if false positives or false negatives occur. |
| IP Blacklist | Add specific IP addresses to block when you identify frequent malicious requests from them. | No initial protection template. |
| Custom Rules | Build personalized protection policies with flexible matching conditions and rule actions to block specific attacks—such as malicious calls, malicious requests, or high-frequency scanning. | — |
| Geo-blocking | Block all IP addresses from specific regions with a single click. Ideal for regions with no legitimate business traffic. | — |
| Scanning Protection | Identifies scanning behavior and scanner signatures to block large-scale scanning attempts, reducing intrusion risks and unwanted traffic. | Subscription Advanced, Enterprise, and Ultimate editions: initial default template enabled by default. Other editions: no initial template. |
| HTTP Flood Protection | Mitigates HTTP flood attacks using built-in algorithms. Combine with Custom Rules for better results. | — |
Core web protection - Others
| Protection module | Use cases and recommendations | Initial status |
|---|---|---|
| Custom Response | Customize the style and content of the block page WAF returns to the client when a request is blocked. | No initial protection template. |
| Website Tamper Protection | Locks protected pages to prevent malicious tampering. WAF returns the cached page for any request to a locked page. | — |
| Data Leakage Prevention | Masks sensitive information—such as ID card numbers and bank card numbers—in server responses, including error pages and keywords. | — |
| Peak Traffic Throttling | Limits QPS or sets throttling ratios by URL and region. Use during traffic surges from major events to keep the origin server available. | — |
Whitelist
Unlike other modules, the Whitelist module allows—rather than blocks—requests with specific characteristics. Matching requests bypass detection by all or specific protection modules. Add known trusted sources (such as O&M IP addresses) to the whitelist.
Initial status: Includes an initial default template with no rules defined, enabled by default.
Advanced protection
| Protection module | Use cases and recommendations | Initial status |
|---|---|---|
| API Security | Protects APIs (such as mobile apps) from unauthorized access and data leaks. Automatically discovers API assets, identifies risks, and provides remediation suggestions and compliance references. | N/A |
| Bot Management | Creates precise protection policies based on traffic analysis to stop automated threats: data scraping, fraud, spam registration, scalping, coupon abuse, and SMS interface abuse. Reduces server load and protects core data assets. | No initial protection template. |
| Critical Event Protection | Provides customized defense during specific time periods for critical business events. | — |
| AI Application Protection | Protects internet-facing AI applications against prompt injection and non-compliant content generation. Automatically identifies high-risk requests and blocks attacks to keep model output secure and compliant. | — |
Disable WAF protection
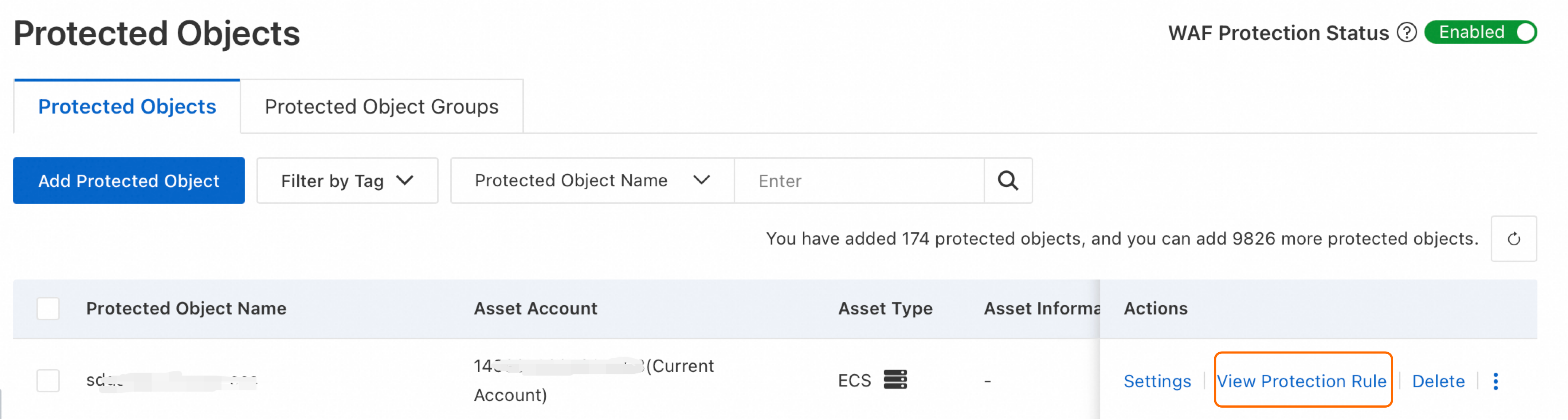
To temporarily bypass WAF, turn off the WAF Protection Status switch in the upper-right corner of the Protected Objects page.

When the switch is off, traffic to your website bypasses the WAF protection engine and is no longer logged. After completing operations that require temporarily suspending WAF (such as emergency testing), turn the switch back on as soon as possible to reduce asset exposure risk.
Billing: For Pay-as-you-go WAF instances, turning off this switch still incurs feature fees, base request fees, and API security traffic fees (if API Security is enabled).
API Security: The API Security module's detection is not affected by this switch.
Unsupported configurations: This feature is not supported for Microservices Engine (MSE) and Function Compute (FC) instances onboarded via cloud native mode. For hybrid cloud access, a specific version is required—contact your account manager.
Manage multiple protection templates
Define multiple protection templates within a module to apply independent rules to different objects. WAF supports two template types:
| Template type | Description | Use cases |
|---|---|---|
| Default protection template | Applies to all current and future protected objects and groups by default. You can manually exclude specific objects (set as Ineffective). Only one default protection template is allowed per protection module. | Deploy general protection rules that apply globally. |
| Custom protection template | Applies only to the protected objects or groups you manually specify. | Deploy targeted rules for specific business scenarios—such as login or payment endpoints. |
If a protected object is set as Ineffective in all templates, it is not protected by WAF.
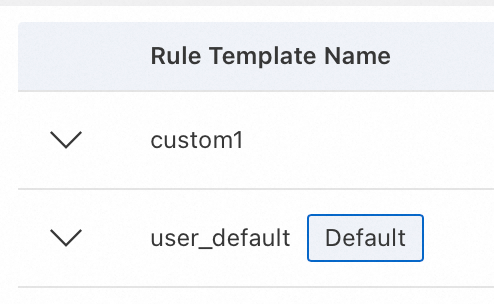
The default protection template is marked withDefault. Templates without this label are custom protection templates.
Modules that support default protection templates: Core Protection Rule, Whitelist, IP Blacklist, Custom Rules, HTTP Flood Protection, Custom Response, Scanning Protection, Geo-blocking, and Peak Traffic Throttling.
Modules that do not support default protection templates: All templates created for these modules are custom templates. You must manually specify effective objects.
Applying multiple templates to a single protected object
The following modules support associating multiple protection templates with a single protected object or group: Whitelist, IP Blacklist, Custom Rules, Bot Management, and Prompt Injection Protection.
For the modules listed above: associating an object with a custom template does not remove it from the default template's scope. The object is protected by both the default template and all associated custom templates simultaneously.
For modules that do not support multiple templates (such as Core Protection Rule): when you associate an object with a custom template, it is automatically removed from the default template's scope.
Example 1: Different protection modes for new and existing objects
Scenario: You want to apply Monitor mode (log attacks without blocking) to newly onboarded objects while keeping Block mode for existing objects.
The Core Protection Rule module includes an initial default template with the Block action applied to all newly onboarded objects.
Steps:
Set the Action of the default protection template to Monitor.
Create a Core Protection Rule template (custom protection template), set its Action to Block, and set Apply To to all currently protected objects.
Example 2: Adding a whitelist rule for a specific object
Scenario: You want to allow IP1 for all protected objects, and also allow IP2 for one specific object.
The Whitelist module includes an initial default template (with no rules defined) that is enabled for all objects by default.
Steps:
In the default template, add a rule to allow
IP1. All protected objects and groups are selected by default.Create a Whitelist template (custom protection template) to allow
IP2, and set Apply To to the specific protected object.
FAQ
When must I manually configure protected objects?
Manually add protected objects in two situations:
Multiple domains on the same cloud instance (cloud native mode): If multiple domains resolve to the same cloud instance but need different protection rules, add each domain as a separate protected object. For details, see Manually add protected objects.
Advanced function configuration: If you need to modify WAF cookie issuance, WAF decoding, or account extraction settings, configure protected objects manually. For details, see Configure advanced protection behavior for protected objects.
How do I verify that protection is working?
Go to the Protected Object page, find the target object, and click View Protection Rule in the Actions column. On the Core Web Protection page, review the object's active protection rules. If no template appears, the configuration is inactive—check the effective objects setting of the protection template.
What if legitimate requests are being blocked?
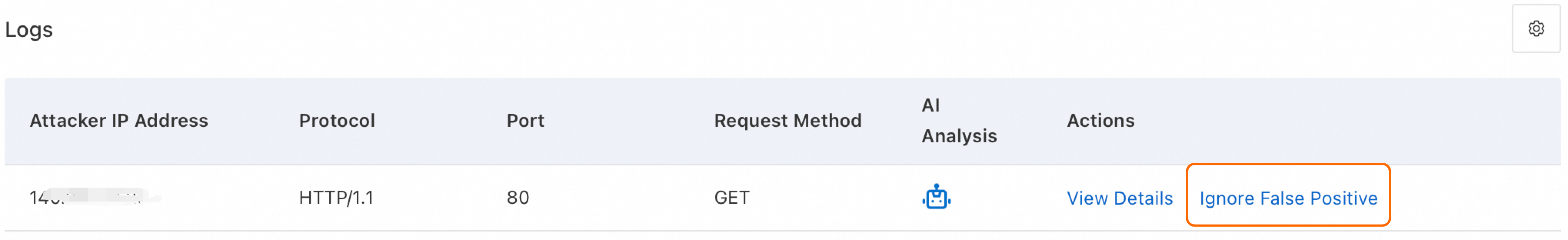
Go to Detection and Response > Security Report. Search by time, client IP, or URL to identify which protection module and rule triggered the block.
In the Logs, locate the request and click Ignore False Positive in the Actions column to create a whitelist rule.