When Access Control/Throttling modules—HTTP Flood Protection, IP Blacklist, Scan Protection, and Custom Protection Policy—block legitimate requests, you can create a whitelist rule to let matching requests skip the modules causing the false positives.
Prerequisites
Before you begin, ensure that you have:
A WAF instance purchased
A website added to WAF. See Tutorial
How whitelist rules work
Access Control/Throttling provides application-layer access control and traffic management through four detection modules:
| Module | Configuration guide |
|---|---|
| HTTP Flood Protection | Rate-based protection against HTTP flood attacks |
| IP Blacklist | Block requests from specific IP addresses |
| Scan Protection | Detect and block automated scanning activity |
| Custom Protection Policy | User-defined access control rules |
When a whitelist rule matches a request, WAF skips evaluation by the modules you select in Bypassed Modules. The request is not evaluated by those modules and passes through to your website. Other enabled modules that you did not select continue to evaluate the request normally.
Define match conditions as precisely as possible to avoid allowing unintended traffic.
Create a whitelist rule
Log on to the WAF console.
In the top navigation bar, select the resource group and the region where your WAF instance is deployed. You can select Chinese Mainland or Outside Chinese Mainland.
In the left-side navigation pane, choose Protection Configurations > Website Protection.
At the top of the Website Protection page, select the domain name from the Switch Domain Name drop-down list.

Click the Access Control/Throttling tab, and then click Settings.
On the Access Control/Throttling - Whitelisting page, click Create Rule.
In the Create Rule dialog box, configure the following parameters.
Parameter Description Rule name Enter a name for the rule. Matching Condition Define the conditions that a request must meet to trigger this rule. Click Add rule to add more conditions (up to five). All conditions must be met simultaneously (AND logic). For field details, see Fields in match conditions. Bypassed Modules Select one or more detection modules to skip when the match conditions are met. Options: HTTP Flood Protection, Custom Rules, IP Blacklist, Anti-Scan. 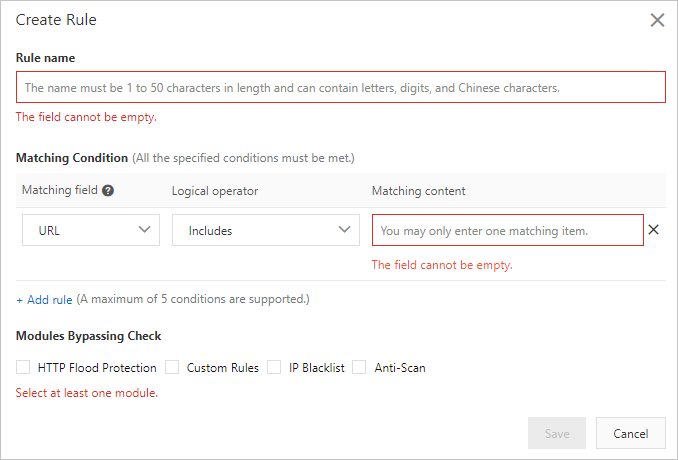
Click Save.
The rule is automatically enabled and appears in the rule list on the Access Control/Throttling - Whitelisting page.
Manage whitelist rules
After creating a rule, you can manage it from the rule list on the Access Control/Throttling - Whitelisting page:
| Action | Description |
|---|---|
| Disable | Temporarily stop the rule from matching requests without deleting it |
| Edit | Modify the rule name, match conditions, or bypassed modules |
| Delete | Permanently remove the rule |