If your origin server is an Elastic Compute Service (ECS) instance or a public-facing Server Load Balancer (SLB) instance, you can use the transparent proxy mode as an alternative to the CNAME record mode. This topic describes how to add a website to WAF by using the transparent proxy mode.
If your WAF instance is upgraded to WAF 3.0, you can use the cloud native mode to add your Elastic Compute Service (ECS) instances, Classic Load Balancer (CLB) instances, and Application Load Balancer (ALB) instances to WAF. The cloud native mode includes the features of the transparent proxy mode of WAF 2.0. For more information, see Cloud native mode.
Limitations
Item | Description |
Cloud service instance types | The transparent proxy mode does not support private Server Load Balancer (SLB) instances and public-facing IPv6 SLB instances. |
SLB and ECS regions | The supported regions include:
Due to legacy network architecture, some public-facing SLB instances do not support the transparent proxy mode. |
Number of traffic redirection port configurations | The number of traffic redirection port configurations that you can add varies based on the WAF edition.
The transparent proxy mode applies to specific ports of an origin server with a public IP address. For example, you can enable this mode for ports 80 and 443. WAF then redirects and protects traffic sent to these ports. For example, enabling this mode for ports 80 and 443 on SLB instance A and for the same ports on SLB instance B counts as four configurations: one for each port on each instance. |
Supported port range | You can protect any standard or non-standard port from 0 to 65535. For more information, see Ports supported by WAF. Note Only subscription WAF instances of the Business, Enterprise, or Exclusive editions support non-standard ports. |
Services protected by both Anti-DDoS Pro and WAF | If your service requires protection from both Anti-DDoS Pro and WAF, you can add the service to WAF in transparent proxy mode only if the service is added to Anti-DDoS Pro in Website Config mode, which is a Layer 7 access mode. If the service is added to Anti-DDoS Pro in Port Config mode, which is a Layer 4 access mode, you cannot add the service to WAF in transparent proxy mode. Instead, add the service to WAF in CNAME record mode. For more information, see Add a domain name to WAF (CNAME record mode). |
Prerequisites
You have purchased a Web Application Firewall (WAF) instance.
You have an IPv4 public-facing Server Load Balancer (SLB) instance with a public IP address. Mutual authentication must be disabled for its ports.
NoteIf you use a private SLB instance that is associated with an Elastic IP Address (EIP), you can add your website to WAF in transparent proxy mode.
If your website is hosted in the Chinese Mainland, its domain name has an ICP filing from Alibaba Cloud. When you submit an ICP filing application in the Alibaba Cloud ICP Filing system, the system automatically identifies the ICP filing type and displays the required steps based on the basic information that you enter. .
The certificate for the ports you are configuring must meet the following requirements:
The certificate is either centrally managed in or purchased from the Certificate Management Service console.
The certificate is assigned to the listener in the Server Load Balancer (SLB) console.
NoteThis prerequisite applies only when you add web traffic from a Layer 7 SLB instance. It does not apply when you add web traffic from a Layer 4 SLB instance or an ECS origin server.
You have authorized WAF to access your cloud resources. For more information, see Authorize WAF to access cloud resources.
Step 1: Add a domain name
Adding an instance to WAF may cause brief connection interruptions (a few seconds) due to DNS updates, network changes, and WAF initialization.
WAF automatically removes a listener port from its protection if you perform any of the following operations. You must re-add the port to resume protection.
For a Classic Load Balancer (CLB) instance with a Layer 7 listener: replace the public IP address that is associated with the instance, replace the listener port's certificate with a third-party certificate, or enable mutual authentication.
For an ECS instance or a Classic Load Balancer (CLB) instance with a Layer 4 listener: replace the public IP address that is associated with the instance or enable mutual authentication.
For an ECS instance, WAF redirects traffic from the EIP or public IP address.
If you unbind an EIP from an ECS instance, the traffic redirection configuration is automatically deleted.
Log on to the Web Application Firewall console. In the top navigation bar, select the resource group and region (Chinese Mainland or Outside Chinese Mainland) of your WAF instance.
In the left-side navigation pane, select .
On the Domain Names tab, click Website Access.
On the Add Domain Name page, select Transparent Proxy for Access Mode.
In the Add Domain Name section, configure parameters such as the domain name and origin server port.
Parameter
Description
Domain Name
Enter your website's domain name. This can be an exact-match domain name such as
www.aliyundoc.comor a wildcard domain name such as*.aliyundoc.com. Note the following points:A wildcard domain name automatically matches all of its subdomains. For example,
*.aliyundoc.commatcheswww.aliyundoc.comandtest.aliyundoc.com.ImportantA wildcard domain name does not match the main domain (for example,
*.aliyundoc.comdoes not matchaliyundoc.com). If you need to protect the main domain with WAF, you must add a separate domain configuration for it (for example, addaliyundoc.comseparately).If both a wildcard and an exact-match domain name configuration exist, the rules for the exact-match domain name take precedence.
Origin server port
Select the origin server ports to protect.
WAF supports enabling transparent proxy mode for the origin server ports of SLB-based Domains, Layer 7 SLB-based Domains, Layer 4 SLB-based Domains, and ECS-based Domains instances. In the origin server port configuration area, select the tab that corresponds to the type of instance that you want to add to WAF. For example, if you use an Application Load Balancer (ALB) instance as the entry point for your web service and need to enable WAF protection for traffic on its listener ports, click the SLB-based Domains tab.
On the corresponding tab, you can perform the following operations:
Add ports
For SLB-based Domains and Layer 7 SLB-based Domains instances, ports are synchronized automatically. Select the ones you want to protect.
For Layer 4 SLB-based Domains and ECS-based Domains instances, you must add ports manually by clicking Add.
After you add a server port, you can select the port in the instance list. You can also delete the port or disable traffic redirection on the Servers tab. For more information, see View origin servers and manage traffic redirection ports
Select the listener ports of the instance to enable WAF protection. For more information, see Configure a traffic redirection port for an ALB instance.
Is a Layer 7 proxy such as Anti-DDoS Proxy or CDN deployed in front of WAF
Enable Traffic Mark
Specifies whether to add custom headers to requests that WAF forwards to your origin server. These headers can mark requests that have passed through WAF or contain the client's real IP address.
If you select Enable Traffic Mark, you must configure the mark fields.
ImportantDo not use standard HTTP header fields, such as User-Agent. Otherwise, the content of the standard header field is overwritten by the value of the custom field.
If an attacker obtains the IP address of your origin server before the domain is added to WAF and uses another WAF instance to forward requests to the target origin server, you can Enable Traffic Mark and set a mark field. After the origin server receives a request, we recommend that you verify this field. If the specified mark field is present, access is allowed.
Click Add Mark to add a mark field. You can configure up to five mark fields.
Resource Group
From the resource group list, select the resource group to which the domain name belongs.
NoteYou can use Resource Management to create resource groups and manage your cloud resources by department or project. For more information, see Create a resource group.
In the Check and Confirm Added Information section, review the configuration information and click Next.
In the Add Completed section, click Complete. Return to Domain Name List.
After you add the domain name, you can view the domain name and origin server information on the Domain Names tab. You can also edit or delete the domain name configuration as required.
By default, WAF inspects traffic on the origin server ports that you enabled in the Add Domain Name section and forwards normal requests to the origin server. You can change the traffic protection status of the origin server ports on the Servers tab as needed.
Step 2: View and manage traffic redirection ports
View and manage origin servers and ports
After adding the domain name, you can view detailed protection information for the origin server. You can also disable or delete port redirection for emergency recovery.
On the Website Access page, click the Servers tab.
Click the
 icon next to an instance to view its protected ports.
icon next to an instance to view its protected ports.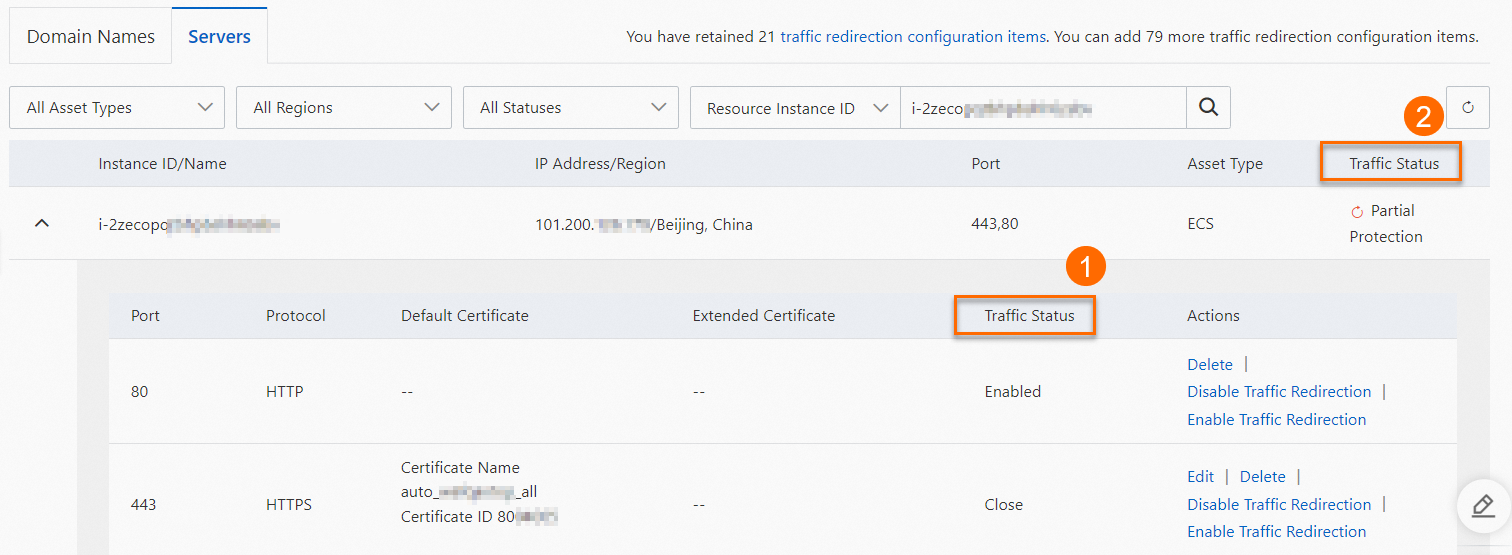 Note
NoteThe ports of Layer 4 SLB-based Domains and ECS-based Domains instances are not automatically synchronized to the server list. You must manually add the ports. For more information, see Add ports.
Description of Traffic Status:
Traffic Status (as shown in Figure ①) indicates whether the traffic for the port is protected by WAF. The available options are Enable or Close. You can click Disable Traffic Redirection or Enable Traffic Redirection in the Actions column to change the traffic redirection status of the port.
NoteIf you disable traffic redirection for a port, traffic to that server port is no longer protected by WAF.
Traffic Status (labeled as ② in the preceding figure) indicates the overall protection status of all ports that are added to WAF for the instance. Valid values are Unprotected, Partial Protection, and Running.
Optional: If the instance is a Layer 4 SLB instance or an ECS instance, you can click Delete in the Actions column for the port and then click OK in the Note dialog box to delete a port that no longer requires traffic protection.
Update certificates for traffic redirection ports
ALB instances and Layer 7 SLB instances: You do not need to re-upload the certificate in the WAF console.
If you update a listener's certificate in SLB, WAF automatically synchronizes the change within about 30 minutes.
ImportantIf you switch to a third-party certificate (not from Alibaba Cloud), you must re-add the instance to WAF after the update.
If the SLB instance is associated with an expired certificate, WAF cannot synchronize the latest certificate. You must delete the expired certificate before you can synchronize the latest one.
If the automatically synchronized certificate does not take effect, you can click the
 icon on the Servers tab to manually update the certificate for the instance's listener port.
icon on the Servers tab to manually update the certificate for the instance's listener port.
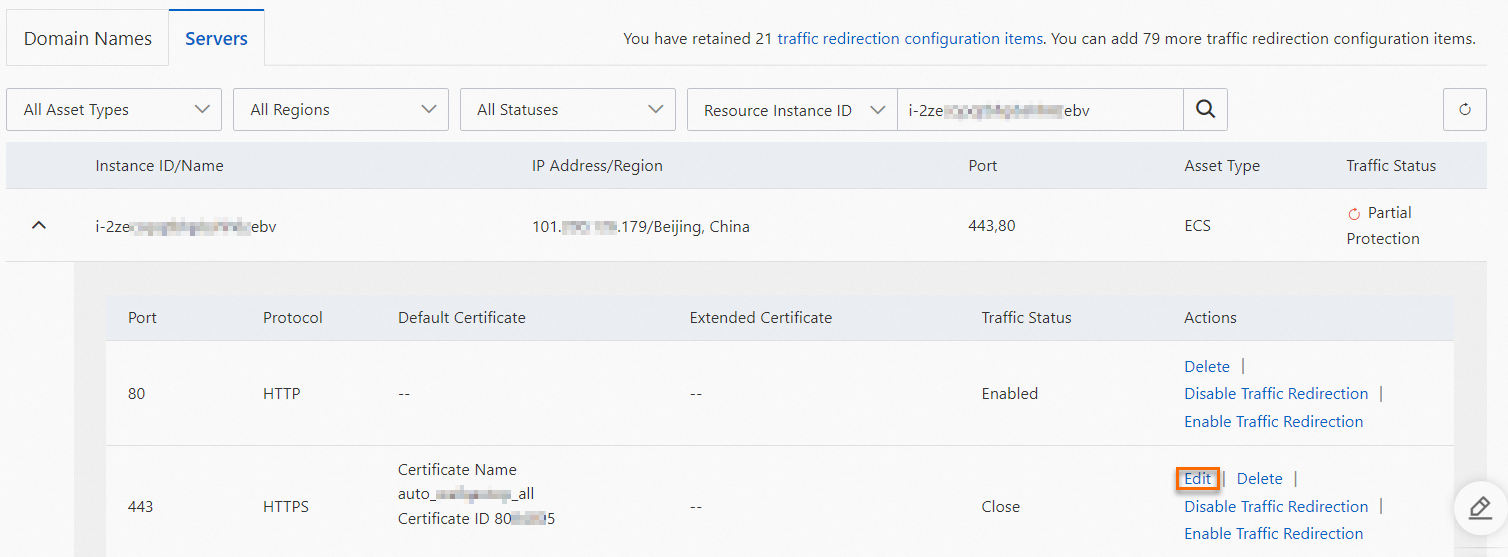
ECS instances and Layer 4 SLB instances: You must re-upload the certificate in the WAF console.
On the Servers tab, find the instance for which you want to update the certificate. In the Actions column of the target port, click Modify. You can upload a certificate by using the Manual Upload or Select Existing Certificate method.
Next steps
After onboarding, WAF protects your website by routing its traffic. The Protection Rules Engine and HTTP Flood Protection modules are enabled by default. The Protection Rules Engine defends against common web attacks like SQL injection, XSS, and webshell uploads, while CC Security Protection defends against CC attacks. You must manually enable other modules and configure their rules. For more information, see Overview of website protection configuration.