Contact Us
Contact Us
You can enjoy a private discount if you purchase multiple security services at a time.
| Type | Product | Scenario |
|---|---|---|
Infrastructure Security |
 Anti-DDoS Basic
Anti-DDoS Basic
Free |
Basic DDoS protection integrated with ECS Get it Free > |
 Anti-DDoS
Anti-DDoS
|
BGP-based DDoS mitigation, low latency, X Tbit/s bandwidth, and anycast Buy Now > | |
 Security Center
Security Center
|
Assets/Baseline/Compliance/Ransomware/Mining/Tamper-proofing/AccessKey pair leak-proofing/Attack source tracing/Cloud security configuration monitoring/Cloud asset risk monitoring 7-day Free Trial > Buy Now > | |
 Web Application Firewall
Web Application Firewall
|
Professional, stable, one-stop solution to core security pain points of web applications, supporting multi scenario deployment and flexible access methods Buy Now > | |
 Bastionhost
Bastionhost
|
Risky operation interception and operation playback Multiple O&M protocols and automatic synchronization between cloud resources Buy Now > |
|
 Cloud Firewall
Cloud Firewall
|
Access control and IPS at the cloud perimeter, visualized east-west and north-south traffic, and interception of outbound traffic 7-day Free Trial > Buy Now > | |
 Certificate Management Service (Original SSL Certificate)
Certificate Management Service (Original SSL Certificate)
|
Flexible HTTPS for websites and applications Centralized management of certificates on and out of the cloud Buy Now > |
|
Identity Security |
 ActionTrail
ActionTrail
|
Records of all operations Real-time and visual reports Free Trial > |
 Resource Access Management
Resource Access Management
|
Multiple authorization methods and global validation upon one-time configuration Free Trial > | |
 Identity as a Service (IDaaS)
Identity as a Service (IDaaS)
|
Provides account, authentication, authorization, application, and audit features Get it Free > | |
Business Security |
 Fraud Detection
Fraud Detection
|
Real-time analysis and accurate identification of risk management solution Activate Now > |
 Content Moderation
Content Moderation
|
Detection for pornography, violence, and terrorism in images, text, audios, and videos; Daily update of compliance intelligence Buy Now > | |
 ID Verification
ID Verification
|
A digital ID verification solution to provide highly secure, convenient, and flexible remote ID verification Activate Now > | |
 Captcha
Captcha
|
Provide authentication services that distinguish between bot scripts and natural person behaviors Buy Now> | |
Data Security Assurance |
 Sensitive Data Discovery & Protection
Sensitive Data Discovery & Protection
|
Sensitive data identification and data risk monitoring; Static and dynamic data desensitization to ensure asset security Contact Sales > |
 Cloud Hardware Security Module (HSM)
Cloud Hardware Security Module (HSM)
|
Cloud-based encryption and low costs Full qualifications, compliant with commercial cryptographic standards Buy Now > |
|
 Key Management Service
Key Management Service
|
Cloud-based key hosting; Cloud service integration and encryption with ease Buy Now > | |
 Cloud Config
Cloud Config
|
Audit of all behavior and interception of risky operations Maintenance-free, no downtime, and quick deployment Buy Now > |
|
Security Service |
 Managed Security Service
Managed Security Service
|
Expert hosting support Routine security configuration, monitoring, and O&M Buy Now > |
 Penetration Test
Penetration Test
|
Simulates attacks to test your system security in full scale and in depthBuy Now > |
Infrastructure Security
Identity Security
Business Security
Data Security Assurance
Security Service
Security Scenarios
-
 Ensure the stable operation of business O&M systems.
Ensure the stable operation of business O&M systems.
-
 Defend against web attacks and malicious frauds.
Defend against web attacks and malicious frauds.
-
 Protect business servers from intrusion and prevent data loss.
Protect business servers from intrusion and prevent data loss.
-
 Hackers blackmail, database leaks
Hackers blackmail, database leaks
-
 Service unavailability due to competitor HTTP flood attacks
Service unavailability due to competitor HTTP flood attacks
-
 Web pages are tampered with or embedded in dark chains
Web pages are tampered with or embedded in dark chains
-
 Perform unified monitoring, management, and audit to guarantee standard operating procedures in the cloud.
Perform unified monitoring, management, and audit to guarantee standard operating procedures in the cloud.
-
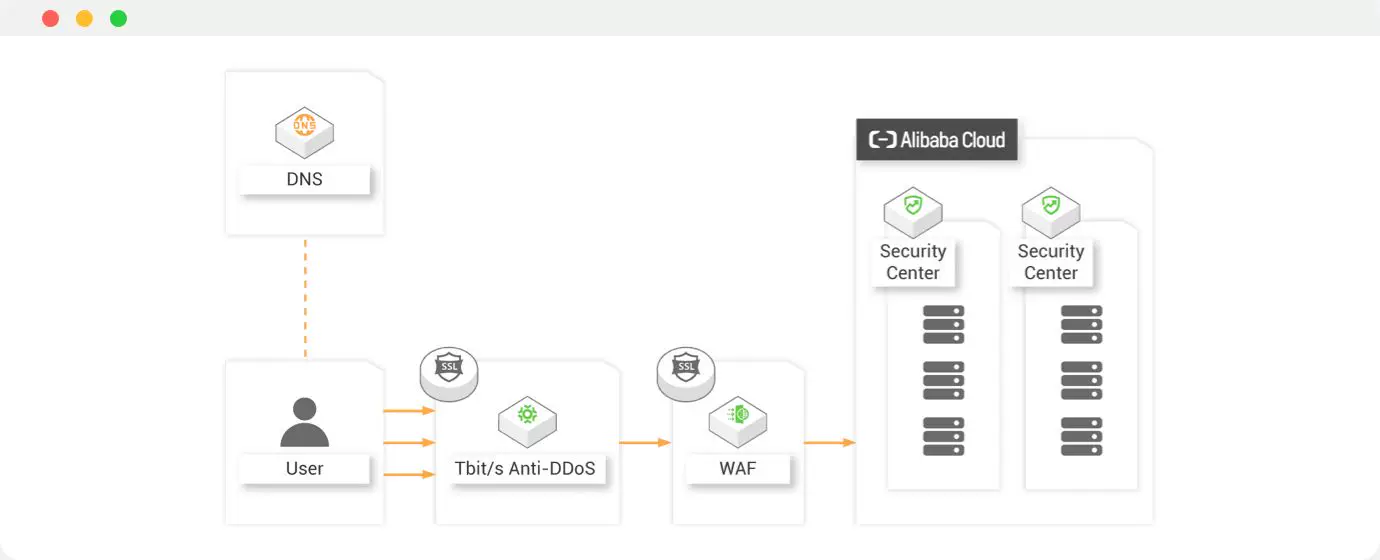
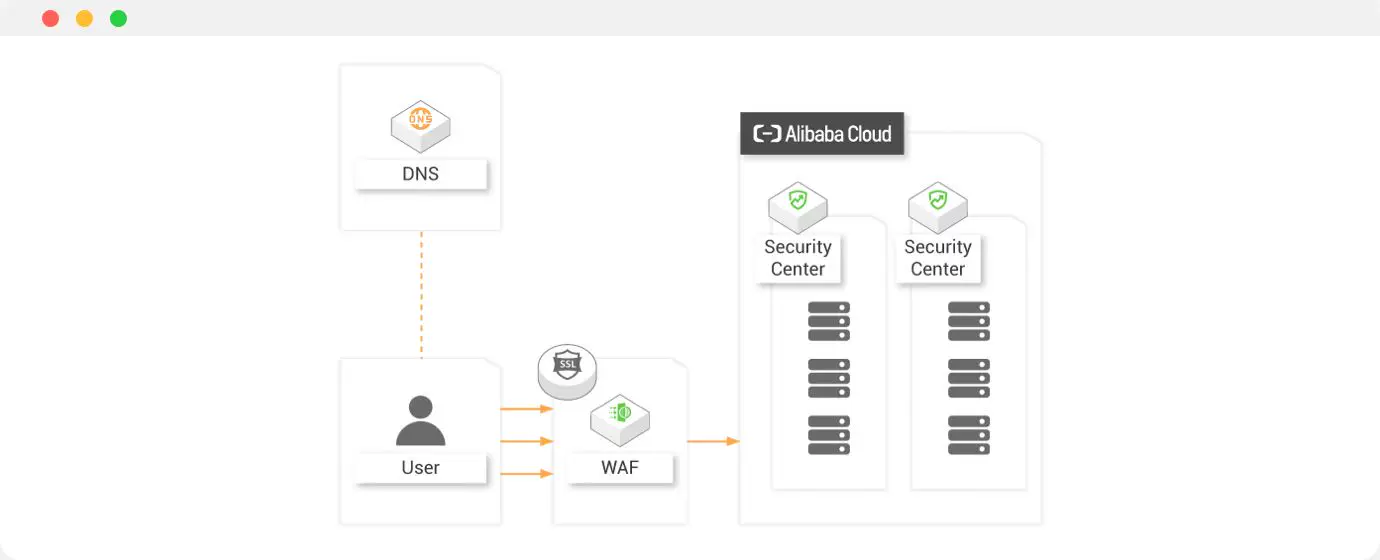
 Ensure the continuity of cloud-based business and defend against DDoS and web attacks.
Ensure the continuity of cloud-based business and defend against DDoS and web attacks.
-
 Implement complete network isolation to ensure that communications between different regions in the cloud are compliant and under control.
Implement complete network isolation to ensure that communications between different regions in the cloud are compliant and under control.
-
 Provide all-round protection at the server level to keep servers safe.
Provide all-round protection at the server level to keep servers safe.
-
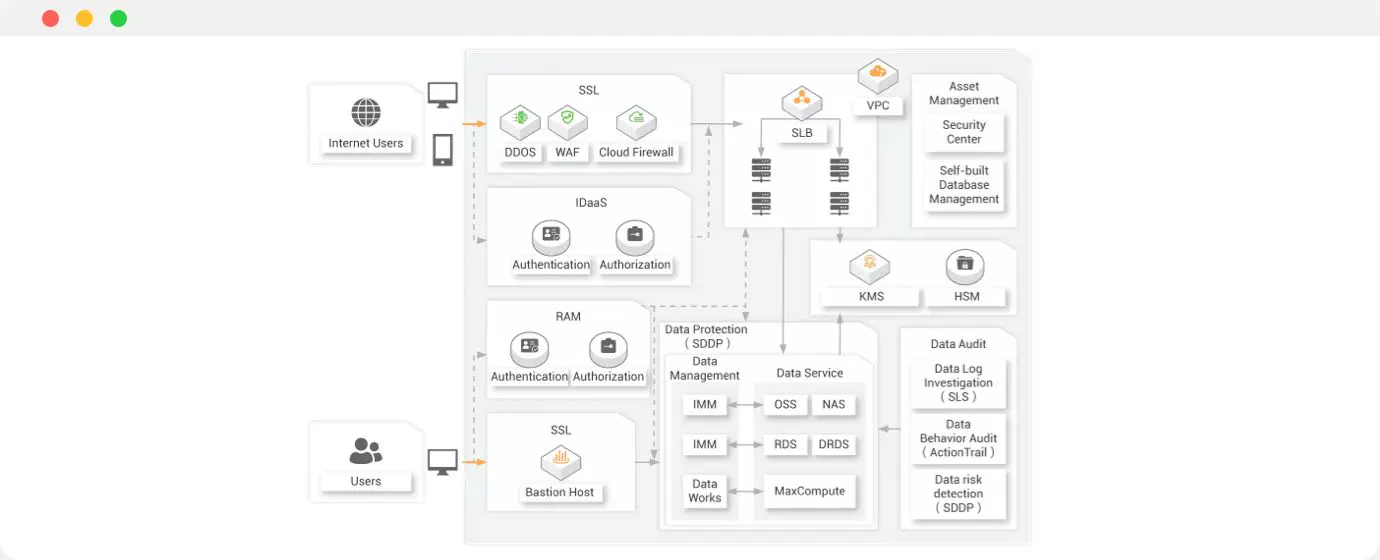
 Provide data lifecycle management.
Provide data lifecycle management.
-
 Focus on key topics in protecting data security.
Focus on key topics in protecting data security.
-
 Improve the overall defense and response capabilities against risks.
Improve the overall defense and response capabilities against risks.
Related Products
-
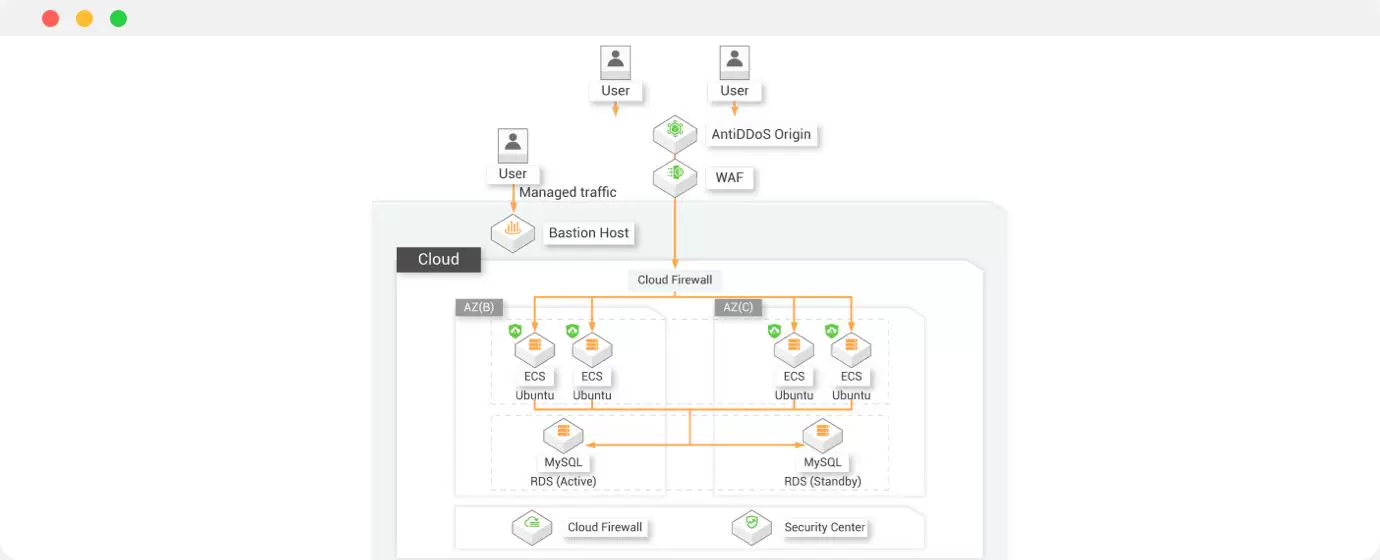
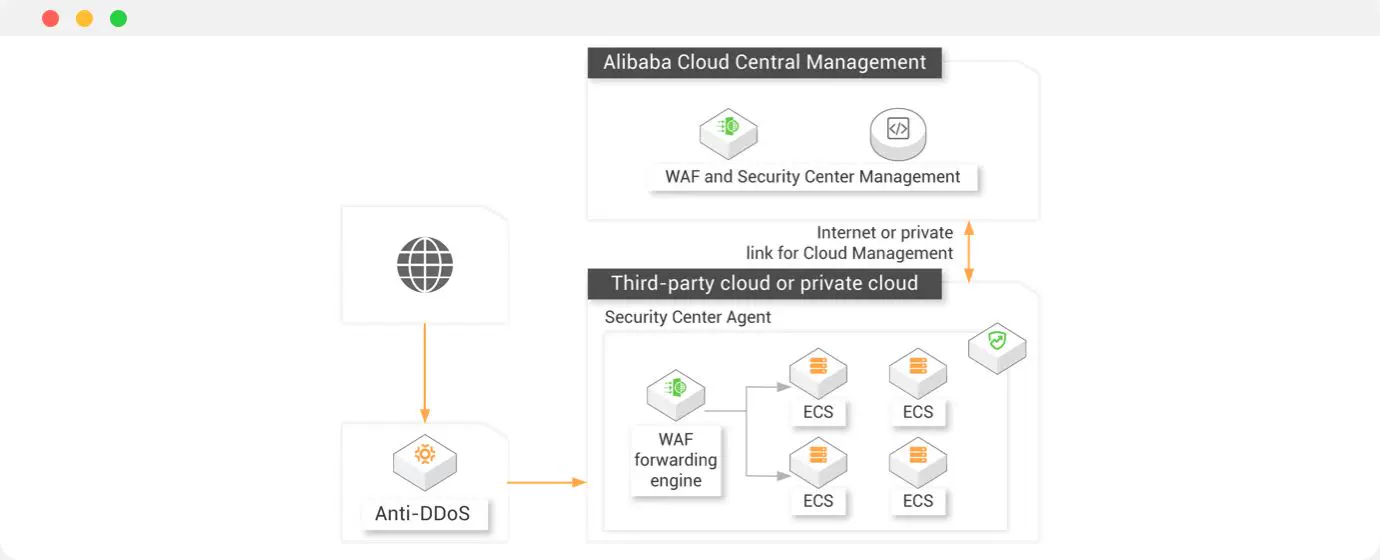
 1.Defend against DDoS attacks, web attacks, and server attacks that aim at on-premises assets.
1.Defend against DDoS attacks, web attacks, and server attacks that aim at on-premises assets.
-
 2.Share the information about the most recent attacks in the cloud with customers in their self-managed environments.
2.Share the information about the most recent attacks in the cloud with customers in their self-managed environments.
-
 3.Centralize the management and control of both cloud and on-premises assets by using unified security policies.
3.Centralize the management and control of both cloud and on-premises assets by using unified security policies.
-
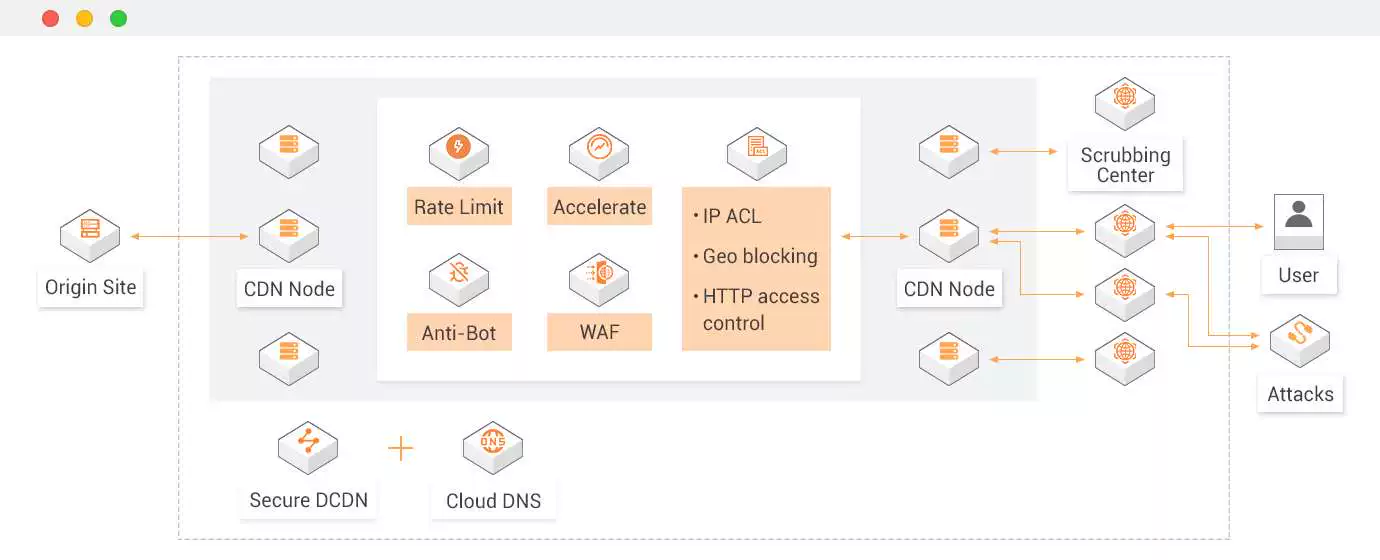
 Accelerate static and dynamic content delivery with optimal acceleration strategy based on the request
Accelerate static and dynamic content delivery with optimal acceleration strategy based on the request
-
 Protect your online business from various threats, such as zero-day attacks and DDoS
Protect your online business from various threats, such as zero-day attacks and DDoS
-
 Leverage rich Open APIs for easy DevOps on programmable orchestration and automation
Leverage rich Open APIs for easy DevOps on programmable orchestration and automation
Related Products
 GDPR
GDPR
 EU Cloud CoC
EU Cloud CoC
 ISO 27001
ISO 27001
 PCI DSS
PCI DSS
 PCI 3DS
PCI 3DS
 SOC Report
SOC Report







Being a Cloud Security Expert
Get hands-on experiences and certificates with your featured courses.
Cloud Security Overview
Cloud Platform Security Overview
Learn about Alibaba Cloud's security products line and their design strategy.
Application Security
Protect Your Web Application on Alibaba Cloud
Learn the main security risks faced by web applications on internet and solutions offered.
Network Security
Use Anti-DDoS Basic and Pro to Defend DoS Attack
Learn how Alibaba Cloud Anti-DDoS products protect your business continuity and security.
Enable Alibaba Cloud End-to-End Security Services
Adopt leading cloud security technology to escort your business