Bolster the growth and digital transformation of your business amid the outbreak through the Anti COVID-19 SME Enablement Program. Get a $300 coupon package for all new SME customers or a $500 coupon for paying customers.
With the current pandemic, distance teaching and e-learning has become the new normal. Teachers and students across China and all over the world have begun to go online. However, with this change, also followed several challenges, of which fierce competition and a greater degree of threats to security were two major problems.
Consider this situation. Company A is an education group that has a global business presence. On its first day responding to China's education authority's call for "suspension of classes but not of teaching and learning", a malicious attack was launched through massive waves of "zombie bots" on the company's teaching platform paralyzed its business and prevented a large number of users from accessing the platform.
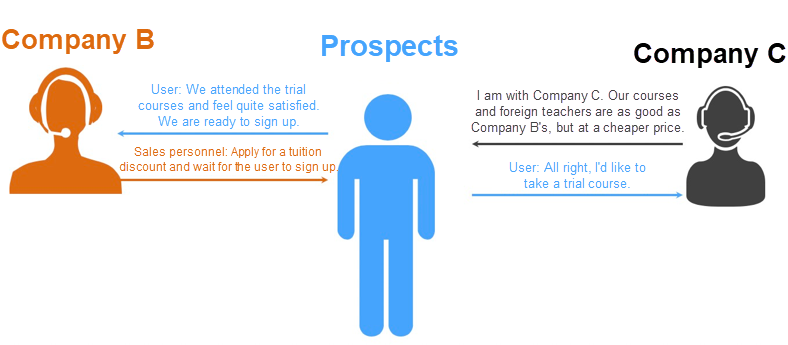
As a result of a massive leak of core data from Company B, another online education brand, all the parents who signed up for Company B's trial courses for their children received marketing SMS messages and phone calls from Company C, and many of Company B's prospects were poached by its competitor who offered a lower price. In addition, due to the data leak, Company B received complaints from many parents.
With the epidemic in full swing, teachers and students across China went online. This quickly brought the online education industry to the attention of the whole of society. Meanwhile, keeping pace with the mounting public attention led to escalating security challenges.
Online education and e-learning businesses have become prime targets for hackers. Hackers are driven by profits and go wherever they can find an opportunity. When public attention began to shift to online education and huge amounts of high-quality data started flowing into online education companies, hackers naturally saw these companies as prime targets. Common attack methods included the following:
Besides these, malicious competitors may even place malicious ads, hidden links, malicious documents and the like on a company's website by tampering the source code, for the purpose of damaging the victim company's reputation.
This outbreak has brought the online education industry into the limelight and has put the security efforts of many companies and organizations to an unprecedented test. The major concerns are as follows.
First, core data is "exposed" on the Internet. Generally, online education companies provide services through websites or apps. However, most companies lack effective website vulnerability discovery mechanisms and intrusion prevention measures to protect their systems from being intruded by hackers. Moreover, many of these companies may have no idea that their loophole-ridden security systems may expose their core data assets on the Internet, leaving behind hundreds of web vulnerabilities that can be easily exploited, and let data be stolen unknowingly.
Second, the design defects of business systems are left unattended. Many online education companies are running business systems that are flawed in design, making it easy to obtain server permissions. However, most education service companies find it difficult to defend themselves effectively against hacker attacks, because they neither hire an in-house security team nor know how to thoroughly check for system vulnerabilities and security design defects.
Given these issues, therefore, attacks occur frequently but no protection measures are taken. Some companies have implemented no protection measures against frequent hacker attacks. In particular, they are quite helpless in the face of zero-day vulnerabilities.
Their security management and security awareness are falling short. Today, as online education is taking off, most companies and organizations in the business focus on how to quickly acquire customers, but neglect the need to develop security capabilities. Some companies have their O&M personnel undertake the concurrent responsibility of security operation. Some are even not in the least concerned about security.
The boundaries of cloud security responsibility are not clear. Some online education companies lack a clear understanding of their security responsibilities after migrating their business to the cloud. They live under the misconception that "buying cloud services means the cloud service provider is obliged to ensure security and will be held liable for all security matters." However, the fact is, both cloud service providers and users have their respective security responsibilities. In other words, the fundamental security guarantee on the cloud platform alone is far from enough, so users need to be responsible for the security of their cloud systems and businesses as well.
Today, these concerns are still widespread in many businesses. What is more terrifying than a hacker attack is not knowing how to defend oneself and having no clue about the fact that one has been attacked.
Alibaba Cloud has developed a complete set of security solutions to address the security challenges in the online education industry.
Traditional security solutions mainly solve various security concerns by using plug-in devices. However, in the new cloud environment, plug-in devices pose many compatibility risks. It has been proven, more than ever, that more efficient, stabler, and more secure solutions are needed to replace the simple approach of transforming plug-in devices into software installed on virtual machines in the cloud. What businesses need is a set of native security solutions "grown" in the cloud.
Cloud-native security solutions differ from traditional plug-in solutions in the following aspects:
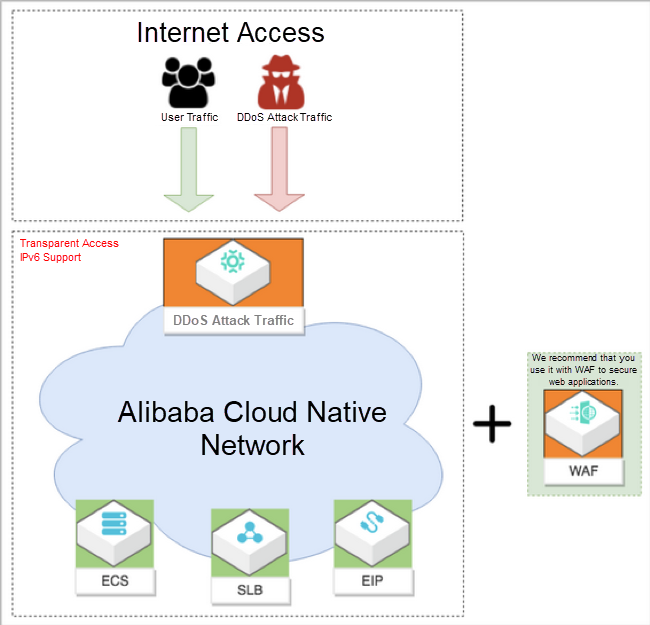
The following describes the types of cloud-native technologies and products included in the cloud-native security solutions provided by Alibaba Cloud and the issues that they can address.
Even for enterprises without security professionals, these capabilities can be easily built in minutes. This is also one of the greatest advantages of cloud-native security. Cloud-native is so convenient.
Take an online education company as an example. TAL Education Group has many education brands that vary in forms of education, customer base, and operation models. Centralized security control across all business platforms is one of the major challenges in building security capabilities. After being tested and verified, Alibaba Cloud's host security product, Security Center, became TAL's choice for centralized server security control. In the meantime, the solution also integrates the capabilities of Cloud Security Scanner to regularly verify vulnerabilities and monitor content security for web services on all of its business platforms, in a bid to build a sound security detection and protection system from the underlying servers to the upper-layer business platforms.
Currently, Alibaba Cloud's online education security solution has more than 100 customers. During China's battle against the coronavirus outbreak, our solution has ensured that hundreds of millions of teachers and students can safely and smoothly teach and learn online and puts the principle of "suspension of classes but non-stop learning" to practice.
While continuing to wage war against the worldwide outbreak, Alibaba Cloud will play its part and will do all it can to help others in their battles with the coronavirus. Learn how we can support your business continuity at https://www.alibabacloud.com/campaign/fight-coronavirus-covid-19
Learn How the VFX Artists of The Wandering Earth Using Alibaba Cloud to Get Back to Work?
Alibaba Cloud's Providing Efficient Gene Sequence Retrieval for COVID-19 Sequence Analysis

2,593 posts | 794 followers
FollowAlibaba Clouder - July 8, 2019
Alibaba Clouder - December 15, 2017
Alibaba Cloud Security - December 25, 2018
Alibaba Container Service - October 21, 2019
Alibaba Clouder - January 21, 2021
Alibaba Clouder - July 27, 2020

2,593 posts | 794 followers
Follow ECS(Elastic Compute Service)
ECS(Elastic Compute Service)
Elastic and secure virtual cloud servers to cater all your cloud hosting needs.
Learn More Elastic IP Address (EIP)
Elastic IP Address (EIP)
An independent public IP resource that decouples ECS and public IP resources, allowing you to flexibly manage public IP resources.
Learn MoreLearn More
More Posts by Alibaba Clouder