Product Dynamic
Newly Released
The general-purpose computing instance type u2a is now available for public preview.
Open for claiming
ECS-exclusive security protection package offers multi-layered, all-around protection.
Newly Released
The general-purpose computing instance type u2i is now officially available for commercial use.
Newly Released
The 9th-generation AMD instance g9a is now officially available for commercial use.
Product Introduction
Benefits

High-stability commitment to ensure business continuity.
The SLA for a single instance reaches 99.975%, while the SLA for multiple instances across multiple availability zones reaches 99.995%. Cloud disks offer reliability of 99.9999999%. The system supports automatic failover upon downtime and snapshot-based backups. It also enables high-availability architecture designs spanning multiple availability zones, along with automated recovery capabilities, to ensure business continuity.
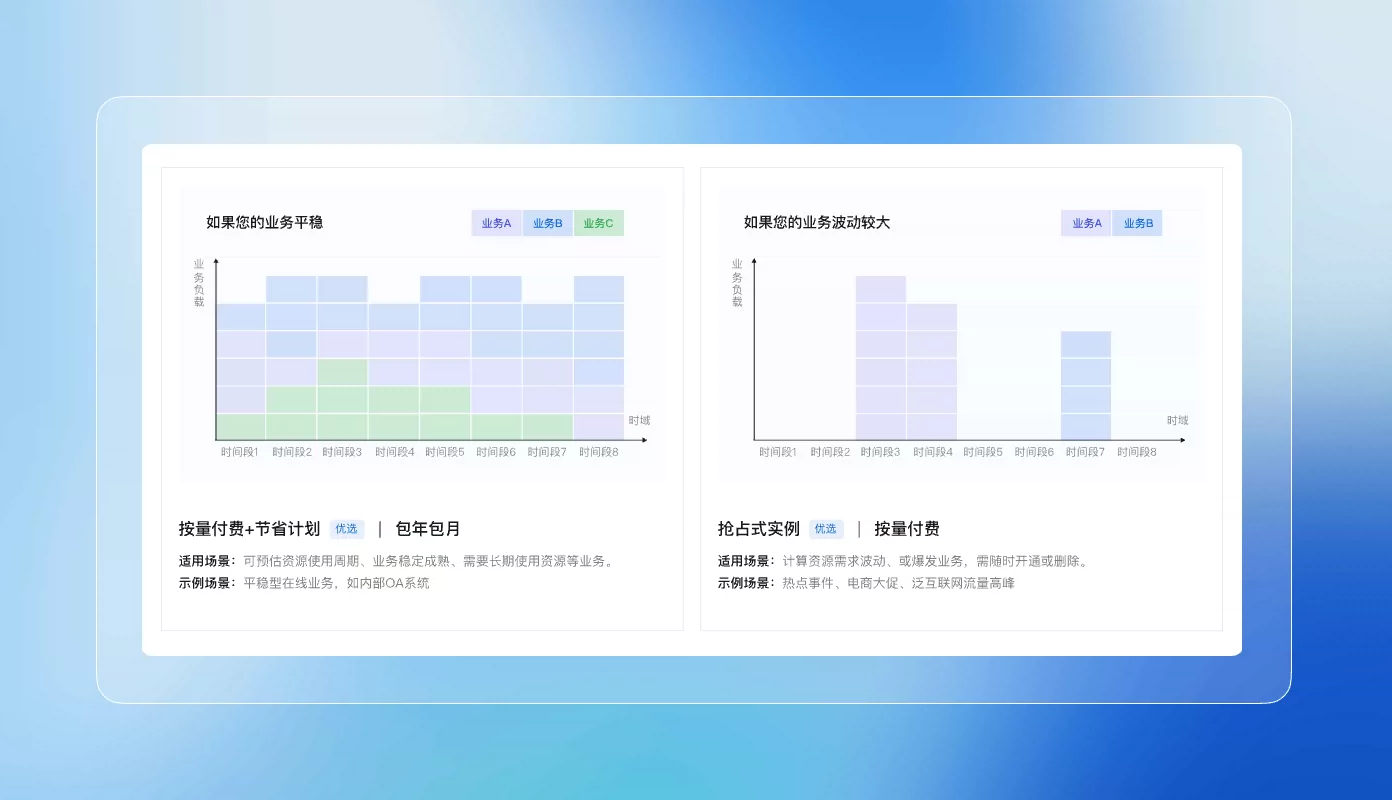
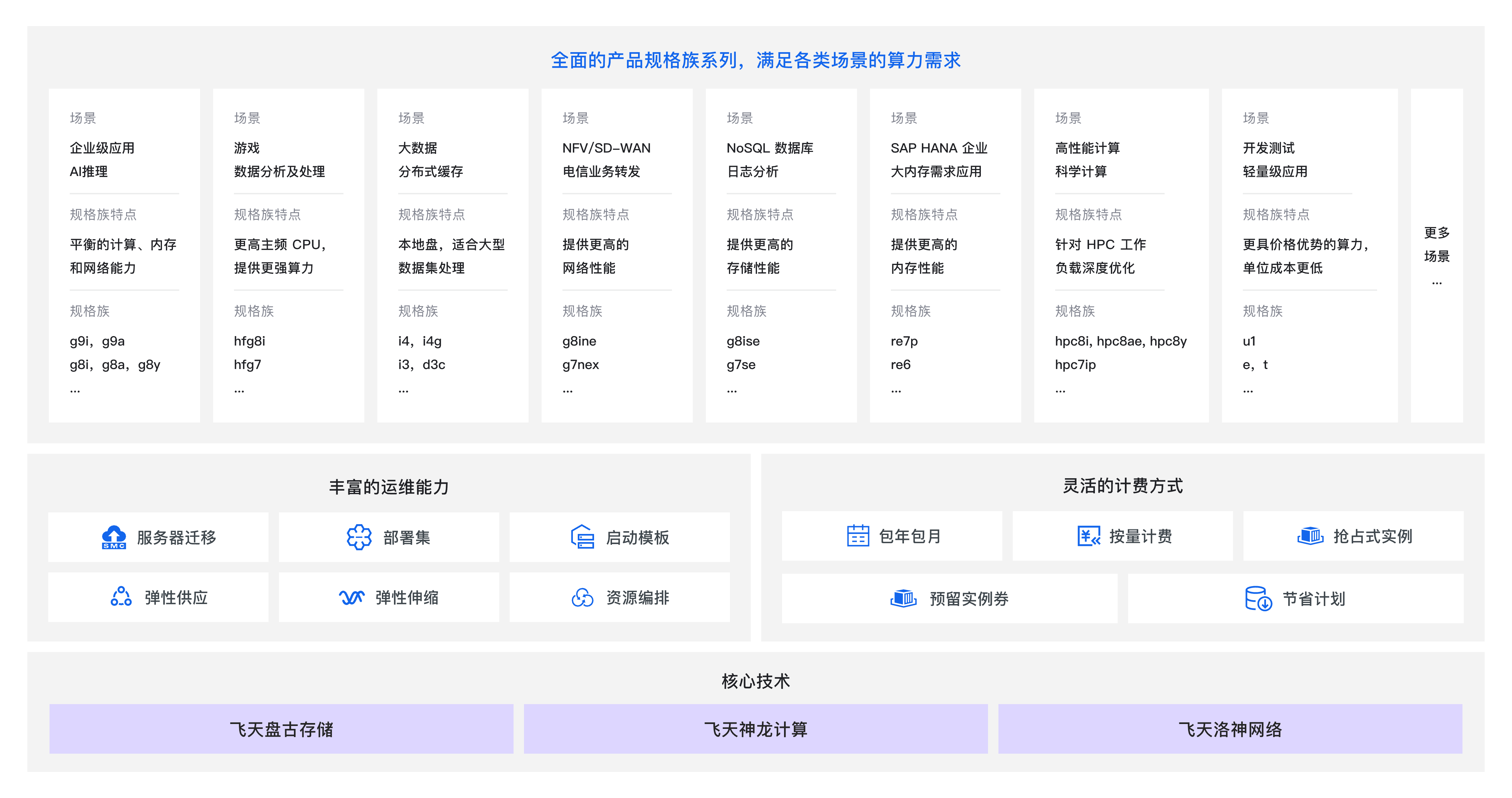
Flexible sales models and elastic guarantees significantly reduce resource costs.
It offers a variety of flexible payment options to effectively reduce enterprise IT costs. The platform supports the creation of tens of thousands of instances within minutes, enabling agile and elastic scaling to meet sudden demand spikes. Compute resources, storage capacity, and network bandwidth can each be scaled up or down on demand.

Global cloud infrastructure accelerates enterprises’ expansion overseas and their business growth.
We provide efficient and stable computing services across 29 regions and 90 availability zones worldwide. We have already delivered computing power to 5 million customers globally, helping enterprises achieve digital transformation and business innovation while providing robust computing support for their expansion into overseas markets and new regions.

High-stability commitment to ensure business continuity.
The SLA for a single instance reaches 99.975%, while the SLA for multiple instances across multiple availability zones reaches 99.995%. Cloud disks offer reliability of 99.9999999%. The system supports automatic failover upon downtime and snapshot-based backups. It also enables high-availability architecture designs spanning multiple availability zones, along with automated recovery capabilities, to ensure business continuity.
Multi-layered protection for comprehensive enterprise security.
Leveraging multiple international security certifications, we provide comprehensive security safeguards for enterprises. Our services include DDoS protection, operating system vulnerability detection, and malware removal to help reduce business security risks. We also offer instances and cloud disk data encryption features that support trusted computing, hardware-based encryption, and virtualized encrypted computing, further minimizing the risk of data leakage.
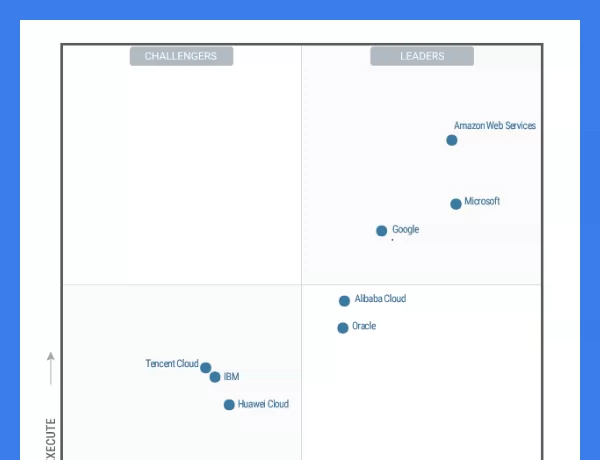
Gartner®
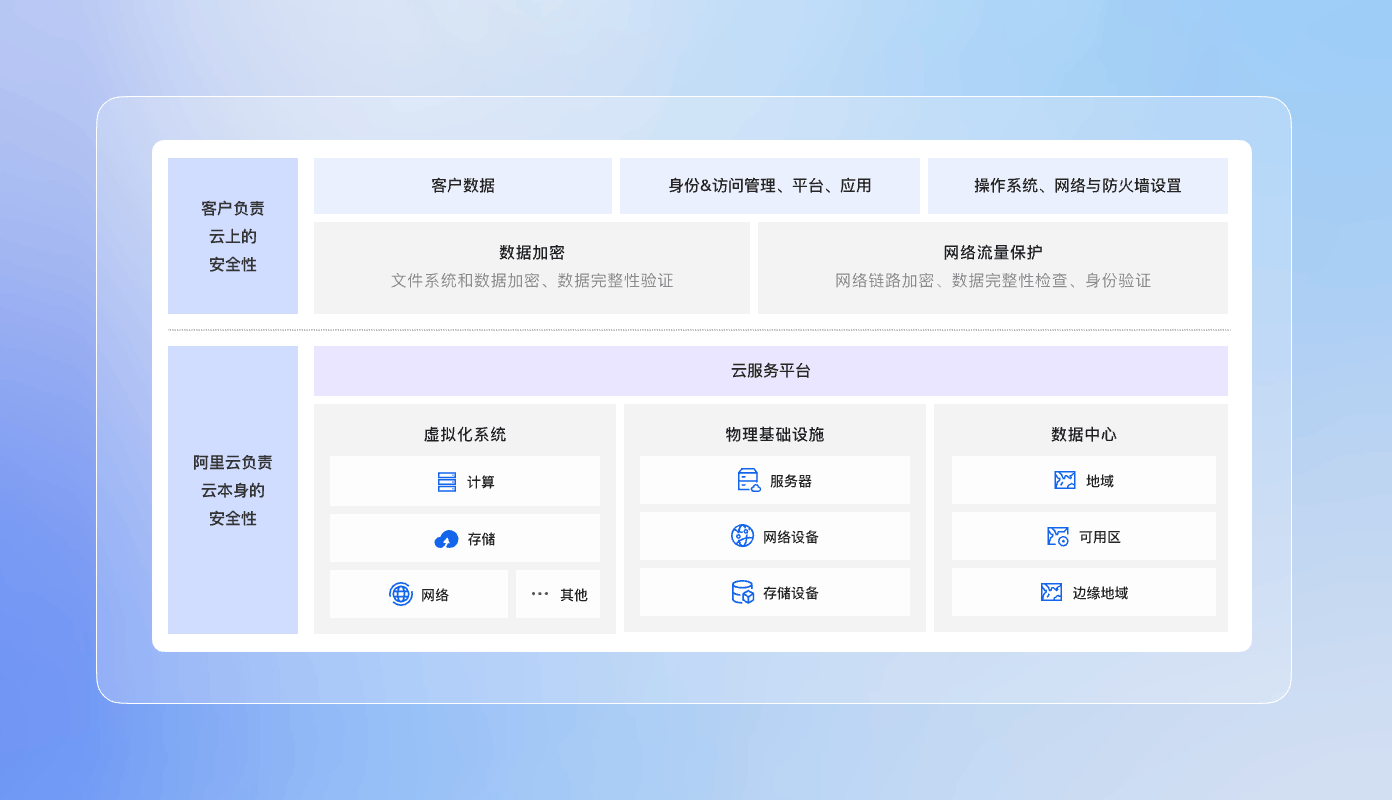
Security Compliance
Security covers a broad scope. Alibaba Cloud ensures the security of its cloud infrastructure and services, such as data centers, virtualization stacks, network security, and data security. However, adhering to security best practices during the use of cloud products is equally important, such as securing your Alibaba Cloud account, safeguarding confidential information, and implementing access control.

Cybersecurity

Storage security

Computational security
Customer Use Cases