When you create an ACK managed cluster, you need to only configure worker nodes. The master nodes are created and managed by Container Service for Kubernetes (ACK). This reduces O&M costs and allows you to focus on your business applications. This topic describes how to create an ACK managed cluster in the ACK console, by calling API operations, and by using Terraform, SDKs, and CLI.
Before you create an ACK cluster, we recommend that you familiarize yourself with the relevant basic information. For more information, see Kubernetes concepts, Product introduction, and Clusters.
The first time you use an ACK managed cluster, you can start with a cube game. For more information, see Use ACK to deploy a magic cube game application. After you finish with the trial, release resources at the earliest opportunity to avoid unexpected costs.
Planning and design
Before you create a cluster, plan and design the cluster based on your business requirements to ensure that the cluster can run stably, efficiently, and securely. Most ConfigMaps can be adjusted after the cluster is created. However, some ConfigMaps cannot be changed after the cluster is created, especially the configurations related to cluster availability and cluster network. When you make the plan, make sure that the following requirements are met.
Category | Description |
Deployment location |
|
Version and specification |
|
Network planning |
|
Preparations
Before you create a cluster, make sure that you activated ACK and assigned the ACK system role to your Alibaba Cloud account or RAM user. In addition, make sure that you activated cloud services such as VPC, Server Load Balancer (SLB), and NAT gateway. For more information, see Quickly create an ACK managed cluster.
If you purchase services such as CLB based on the pay-as-you-go billing method, make sure that the balance of your Alibaba Cloud account is sufficient to avoid overdue payments.
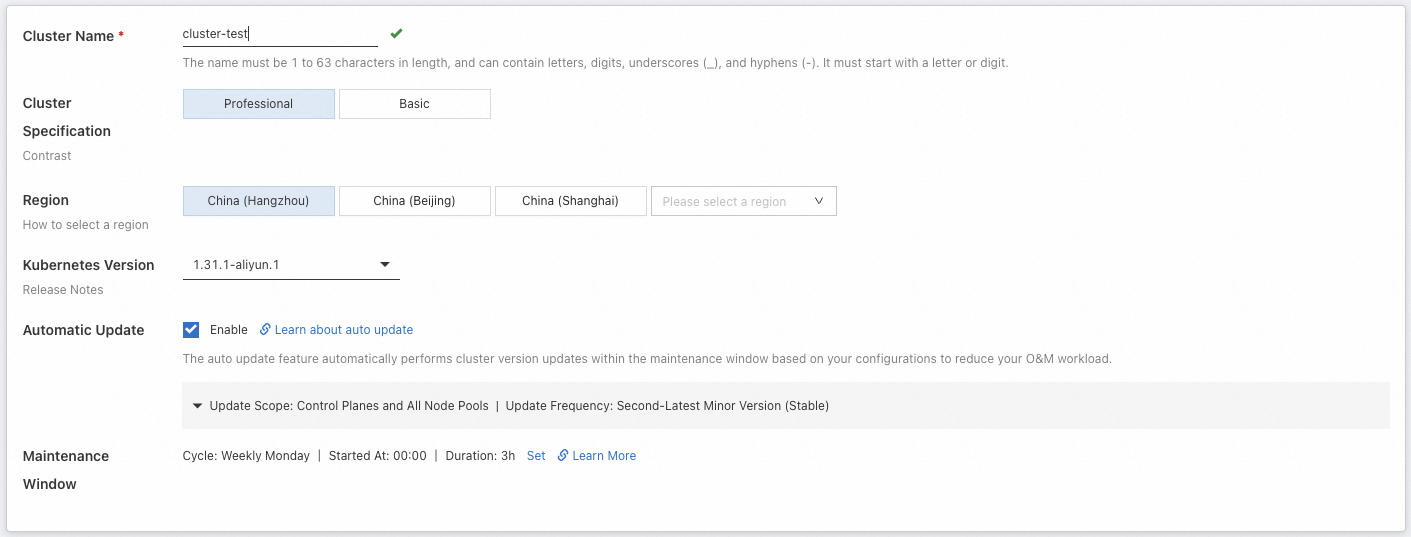
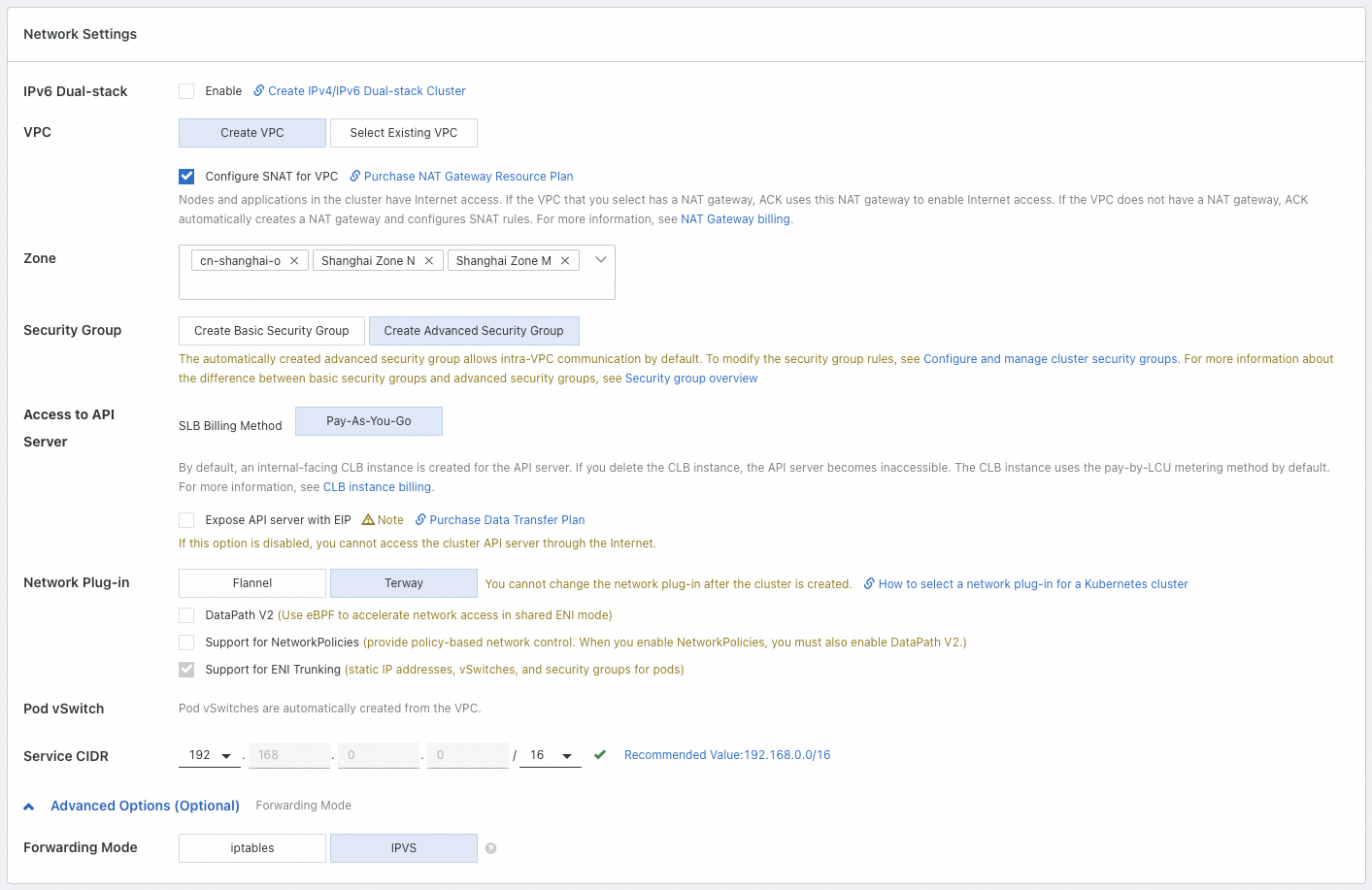
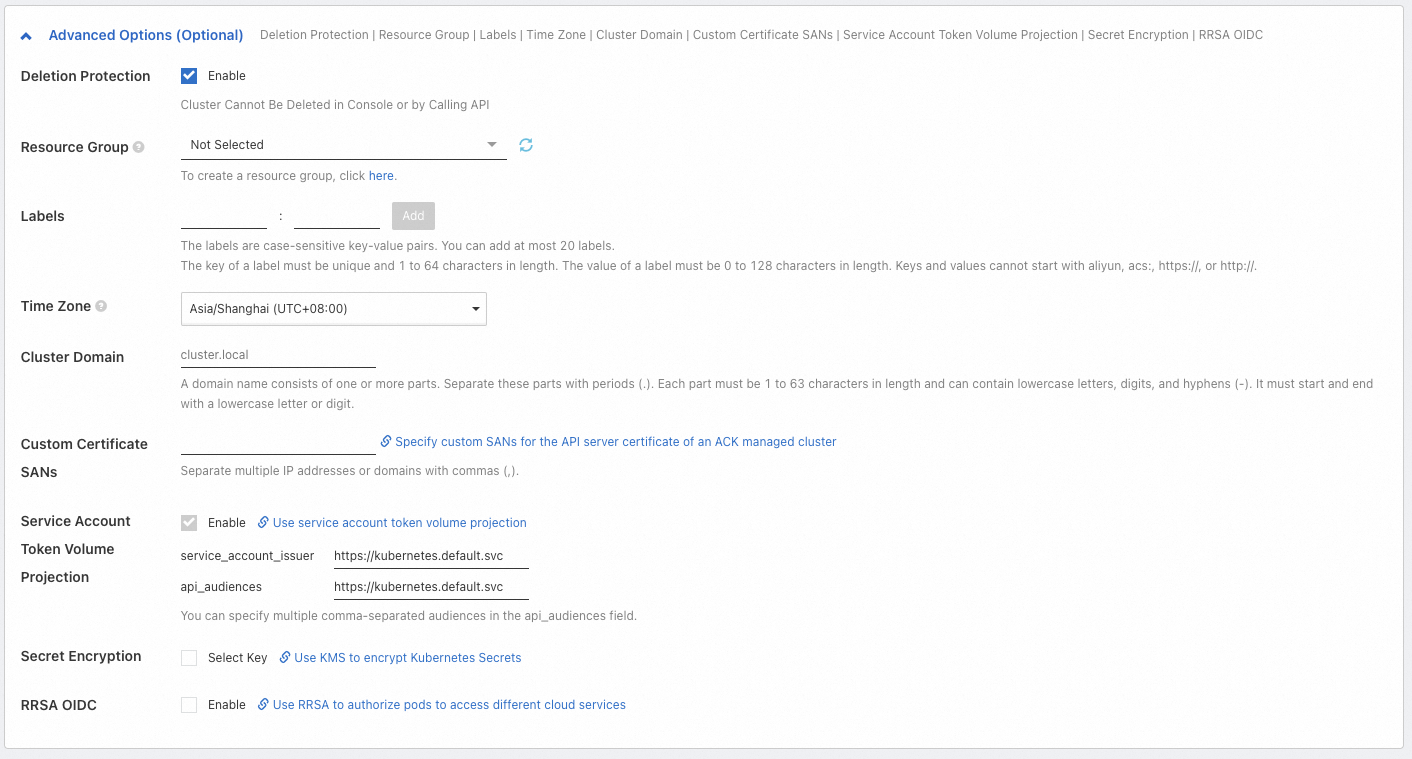
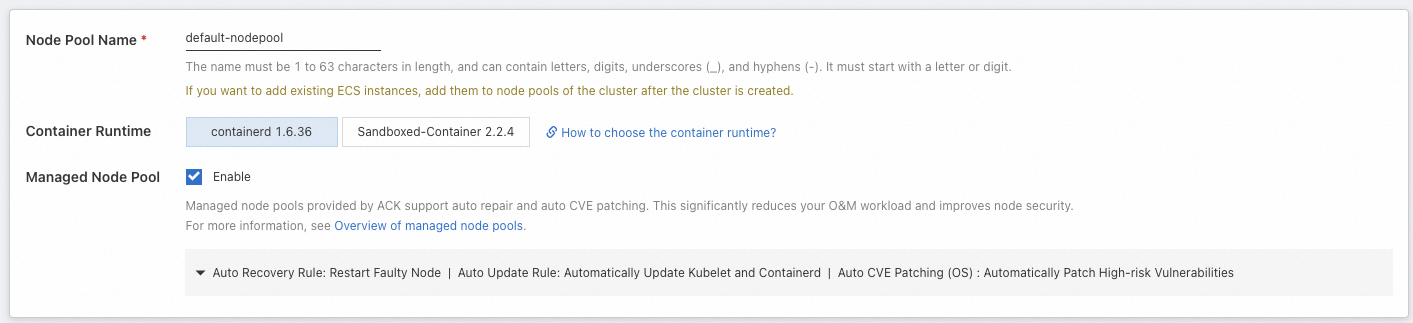
Create a cluster
ACK allows you to create clusters in the ACK console, by calling API operations, and by using SDKs, Terraform, and CLI.
Use the ACK console
API
Terraform
SDK
CLI
What to do next
Application deployment: You can create and manage workloads, such as Deployments, StatefulSets, and Jobs. For more information, see Deploy a workload.
Service discovery and network management
Service: provides a fixed access portal for a group of pods to allow intra-cluster access and Internet access.
Ingress: You can use Ingresses to configure different forwarding rules. For example, you can forward requests to different Services based on domain names or access paths for load balancing.
DNS-based service discovery: provides domain name resolution services for workloads in a cluster. This way, services in the cluster can access each other by using service names without the need for specific IP addresses.
Observability: allows you to collect cluster logs, monitor alerts, and diagnose cluster status. For more information about the observability solutions provided by ACK in terms of infrastructure, containers, and workloads, see Observability.
Storage: The CSI plug-in is used to meet storage requirements such as persistent storage of application data, storage of sensitive and configuration data, and dynamic provisioning of storage resources.
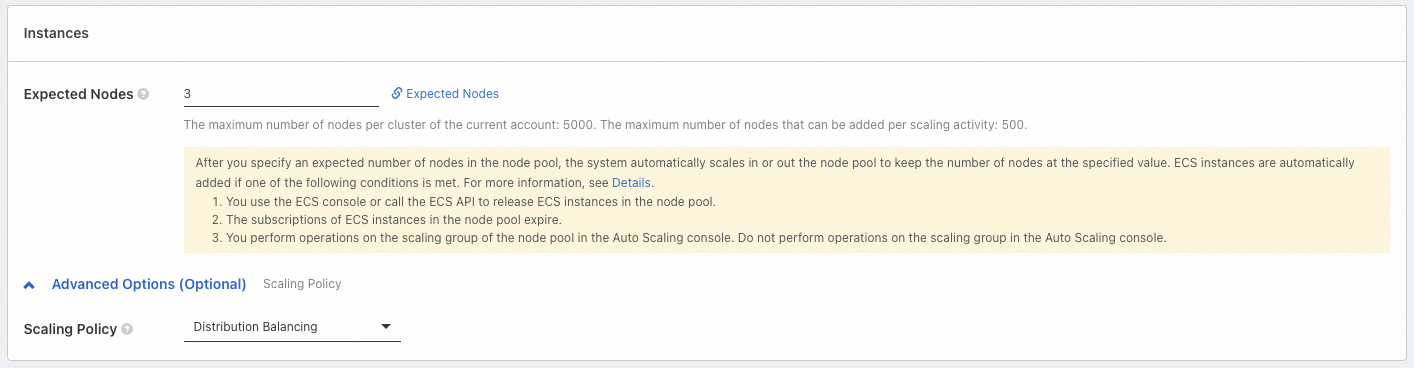
Auto scaling configurations: If business resource requirements are difficult to predict or periodically change, such as for web applications, game services, and online education, we recommend that you enable auto scaling. This feature includes workload scaling , such as HPA, CronHPA, and VPA, and computing resource scaling, such as node auto scaling and instant node elasticity .
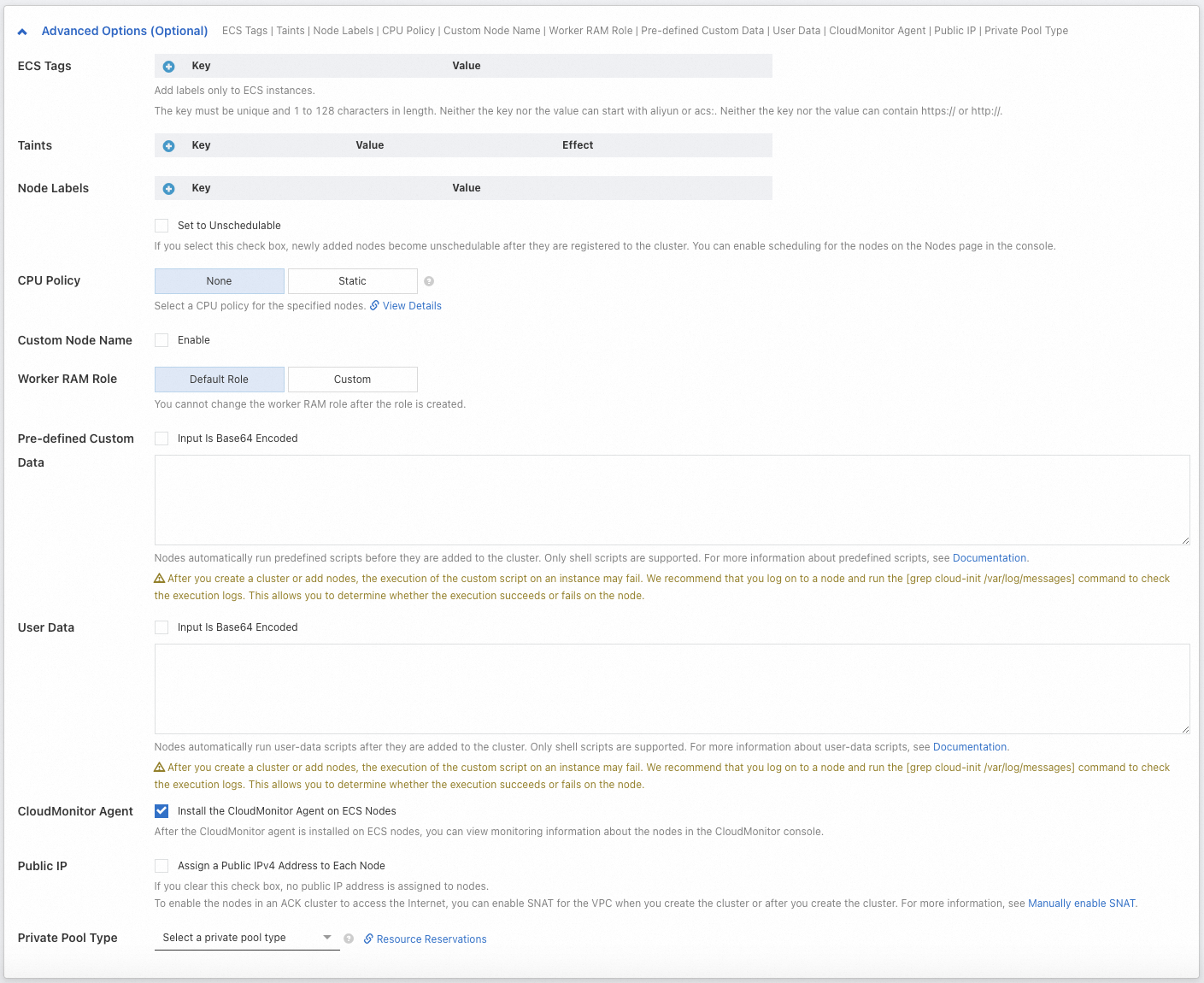
Fine-grained authorization
For more information about how to grant fine-grained permissions on basic resources (Alibaba Cloud services that ACK depends on) and cluster internal resources (Kubernetes resources), ACK provides multiple permission management solutions based on RAM and the native RBAC mechanism of Kubernetes. For more information, see Authorization.
Quotas and limits
If the cluster size is large or the account has a large number of resources, follow the quotas and limits specified for ACK clusters. For more information, see Quotas and limits.
Limits: ACK configuration limits, such as account balance and capacity limit of a cluster, which is the maximum capacity of different Kubernetes resources in a cluster.
Quota limits and how to increase quotas: Quota limits for ACK clusters and the quota limits of cloud services that ACK depends on, such as ECS or VPC. If you want to increase the quota, see the related topics.
FAQ
For more information about how to troubleshoot issues when you use ACK clusters, see Troubleshooting and FAQ.
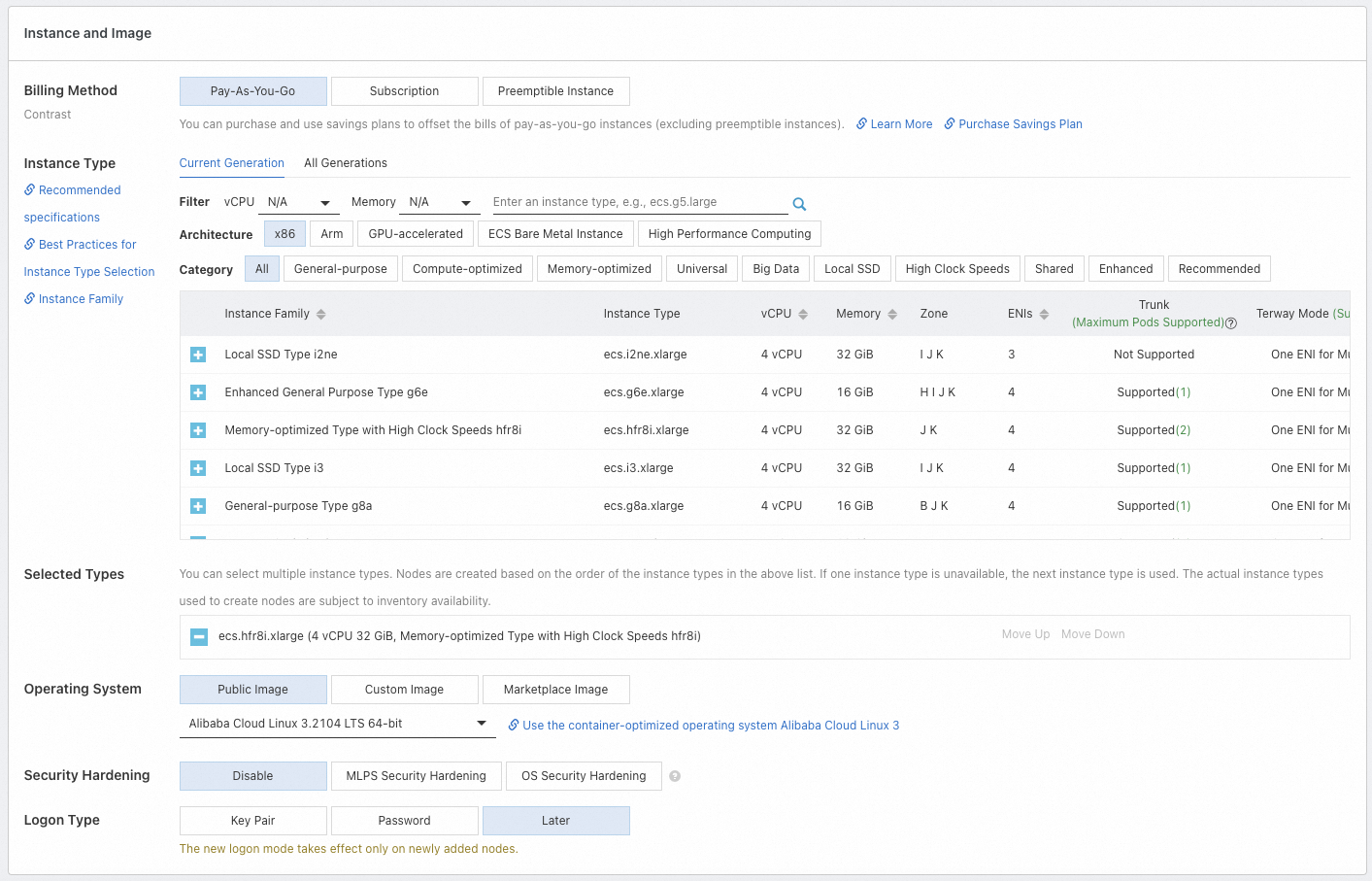
Can I create a cluster with zero nodes?
Yes, you can. If you want to skip node creation or add purchased ECS instances to a cluster after the cluster is created, you can set the Expected Nodes parameter to 0 during the configuration. This also sets the number of instances in the cluster to 0. Then, configure the other required parameters. You can update the configurations of a node pool or create more node pools. For more information, see Create and manage a node pool. For more information about how to add an existing ECS instance to a cluster, see Add existing ECS instances to an ACK cluster.
How do I add purchased ECS instances to a cluster?
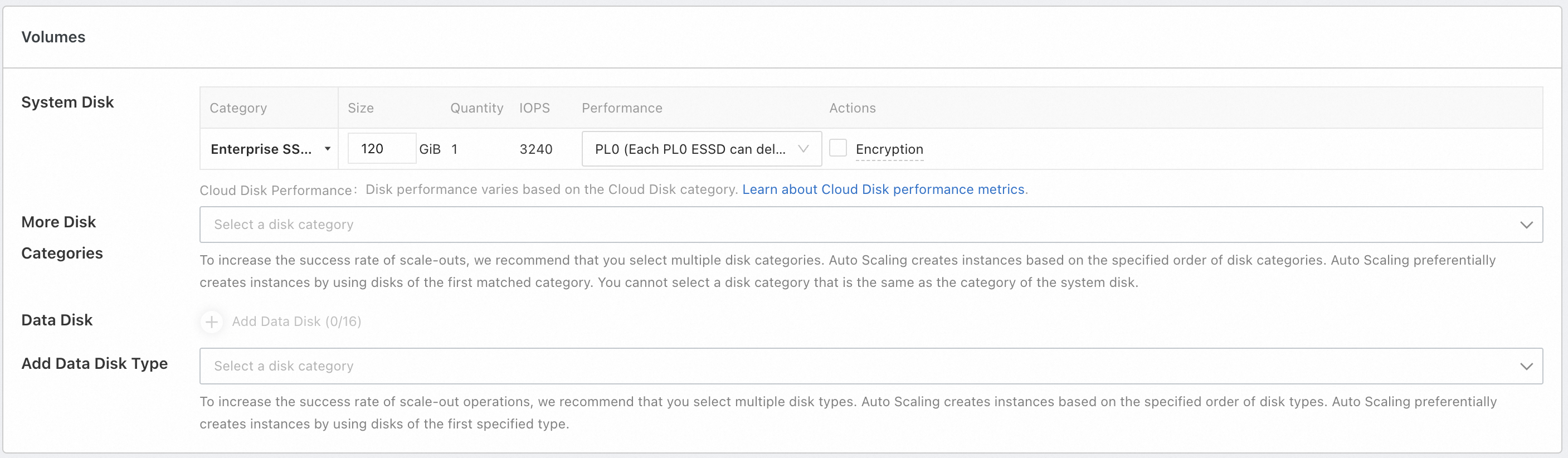
ACK allows you to manually or automatically add existing ECS instances to a node pool. When you add an existing node to a node pool in Auto mode, the OS of the ECS instance is changed to the OS used by the node pool and the original system disk of the node is released. To retain the operating system of the ECS instance, you can manually add the ECS instance. For more information about the operations and usage notes, see Add existing ECS instances to an ACK cluster.
We recommend that the ECS instances and the node pool that you want to add have the same or similar configurations, such as the billing method, disk configurations, and instance type. This facilitates centralized management of subsequent nodes.
Can I add a pay-as-you-go instance to a subscription node pool?
Yes, you can. For more information, see Add existing ECS instances. However, if the billing method of the node pool is subscription, all nodes added to the node pool are subscription nodes. We recommend that you create different node pools to manage different types of nodes, such as nodes that have different billing methods, disk configurations, and instance types. For more information, see Create and manage a node pool.
Why is the number of pods insufficient when a cluster is created?
This error message appears due to one of the following reasons:
Consumed by components: Cluster components are deployed in pods. The pods consume node resources. Specific components may require multiple pods. If you install a large number of components in the cluster, a large number of pods are created for the components.
Small-sized instances: In Terway mode, the maximum number of pods supported by a node varies based on the number of elastic network interfaces (ENIs) provided by the instance family. Although the maximum number of pods supported by a node is not directly related to the CPU and memory, ECS instances that have lower specifications support a smaller number of ENIs and the maximum number of pods per node is also smaller.
When the number of pods on a node reaches the upper limit, new pods fail to be scheduled. This affects service performance. You can increase the number of pods that can be used by scaling out the node pool to add more available nodes or by updating nodes to increase the maximum number of pods per node. For more information, see Increase the maximum number of pods in a cluster.
Why are the available CPU and memory resources of a node less than those of the instance type that I purchased?
ACK reserves a specific amount of node resources to run Kubernetes components and system processes. This ensures that the operating system kernel, system services, and Kubernetes daemons can run as expected. However, this causes the amount of allocatable resources of a node to differ from the resource capacity of the node. For more information, see Resource reservation policy.
References
When you use an ACK cluster, service failures may occur due to improper operations. For more information, see Usage notes and instructions on high-risk operations.
For more information about how to connect to the cluster, see Obtain the kubeconfig file of a cluster and use kubectl to connect to the cluster.
Outdated Kubernetes versions may have security and stability issues. We recommend that you update your clusters to the latest version. For more information, see Manually update ACK clusters and Automatically update a cluster.
For more information about how to pull cross-region container images that reside outside the Chinese mainland, see Using GA instances for cross-domain accelerated pulling of container images.
If you have questions about the services, contact us.