MSE Ingress gateways are Higress Enterprise Edition gateways fully compatible with NGINX Ingress. Compared with open source self-managed Ingress gateways, the performance of MSE Ingress gateways is doubled. MSE Ingress gateways are certified by the China Academy of Information and Communications Technology (CAICT) based on security maturity. They provide the advantages of low cost, security protection, high integration, and high availability. This topic walks you through installing MSE Ingress Controller, deploying a backend service, and routing external traffic to it.
MSE Ingress gateways cannot expose services in the kube-system namespace.
Prerequisites
Before you begin, ensure that you have:
-
An ACK managed cluster, an ACK Serverless cluster, or an ACS cluster running Kubernetes V1.18 or later. To create one, see Create an ACK managed cluster, Create an ACK Serverless cluster, or Create an ACS cluster. If your cluster version is earlier than V1.18, upgrade it before proceeding
-
RAM permissions granted to MSE Ingress Controller:
-
ACK managed cluster or ACK Serverless cluster: Grant permissions
-
ACS cluster: Grant permissions
-
Considerations:
-
If an IngressClass resource named
msealready exists in your cluster before you install MSE Ingress Controller, the gateway and the associated MseIngressConfig resource are not automatically created during installation. -
Deleting an MseIngressConfig resource also deletes the associated MSE cloud-native gateway instance. Do not delete MseIngressConfig resources unless instructed to do so.
Step 1: Install MSE Ingress Controller
-
Log on to the ACK console. In the left-side navigation pane, click Clusters.
-
On the Clusters page, find the cluster you want and click its name. In the left-side navigation pane, click Add-ons.
-
On the Add-ons page, enter
msein the search box, and click Install in the MSE Ingress Controller resource card.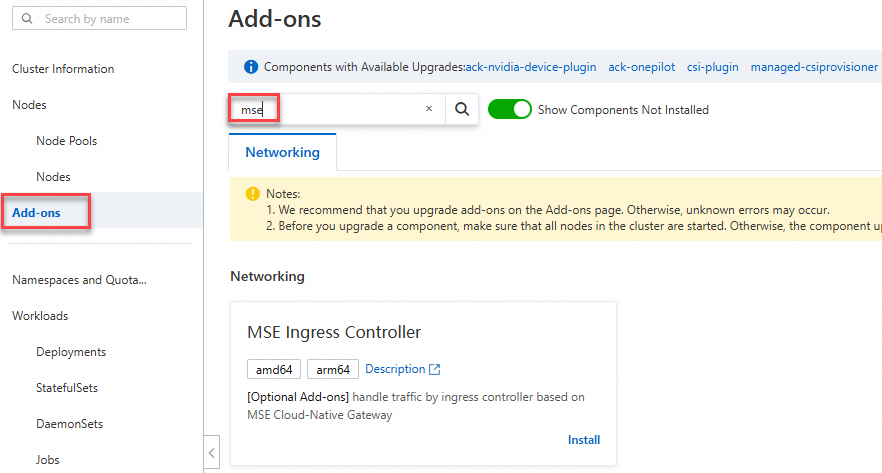
-
In the Install MSE Ingress Controller dialog box, configure the parameters and click OK. Create a new cloud-native gateway or select an existing one. If preflight checks fail during installation, authorize MSE Ingress Controller to access MSE.
-
After installation, the system automatically creates an MseIngressConfig resource and a cloud-native gateway, both named
mse-ingress-premium-{clusterid}. To check the gateway status, go to the cluster detail page and choose Workloads > Deployments > Custom Resources. On the Resource Objects tab, search formsein the API Group section to find the MseIngressConfig resource. Gateway statuses progress in the following order: Wait 3–5 minutes for thephasefield to change to Listening before proceeding. To verify from the command line, run:Status Description Pending The cloud-native gateway is being created. Wait about 3 minutes. Running The cloud-native gateway is created and running. Listening The cloud-native gateway is running and listening to Ingress resources in the cluster. Failed The cloud-native gateway is in an invalid state. Check the Messagefield inStatusfor the cause.kubectl get mseingressconfig -AThe gateway is ready when the
PHASEcolumn showsListening.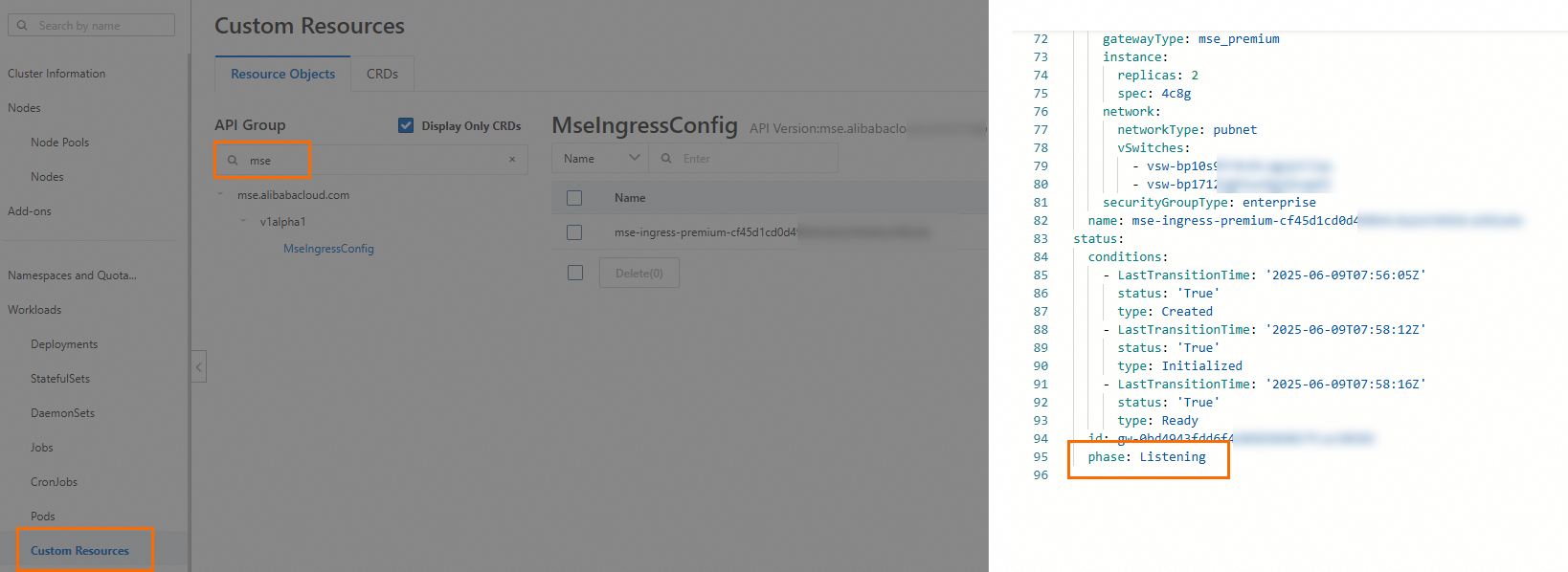
-
Log on to the MSE console to confirm that a cloud-native gateway named
mse-ingress-premium-{clusterid}is created in your region.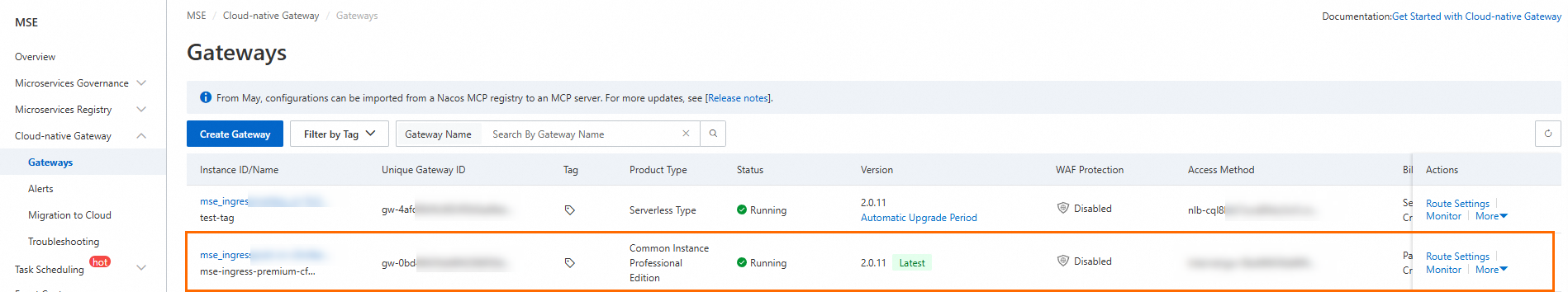
Step 2: Deploy a backend service
-
Log on to the ACK console. In the left-side navigation pane, click Clusters.
-
On the Clusters page, find the cluster you want and click its name. In the left-side navigation pane, choose Workloads > Deployments.
-
On the Deployments page, click Create from YAML and apply the following manifest to deploy a Deployment and a Service named
httpbin:apiVersion: apps/v1 kind: Deployment metadata: name: httpbin namespace: default spec: replicas: 1 selector: matchLabels: app: httpbin template: metadata: labels: app: httpbin version: v1 spec: containers: - image: registry.cn-hangzhou.aliyuncs.com/mse-ingress/go-httpbin args: - "--version=v1" imagePullPolicy: Always name: httpbin --- apiVersion: v1 kind: Service metadata: name: httpbin namespace: default spec: ports: - port: 8080 protocol: TCP selector: app: httpbinTo verify the Deployment is running, run:
kubectl get deployment httpbin -n defaultThe expected output is similar to:
NAME READY UP-TO-DATE AVAILABLE AGE httpbin 1/1 1 1 30s
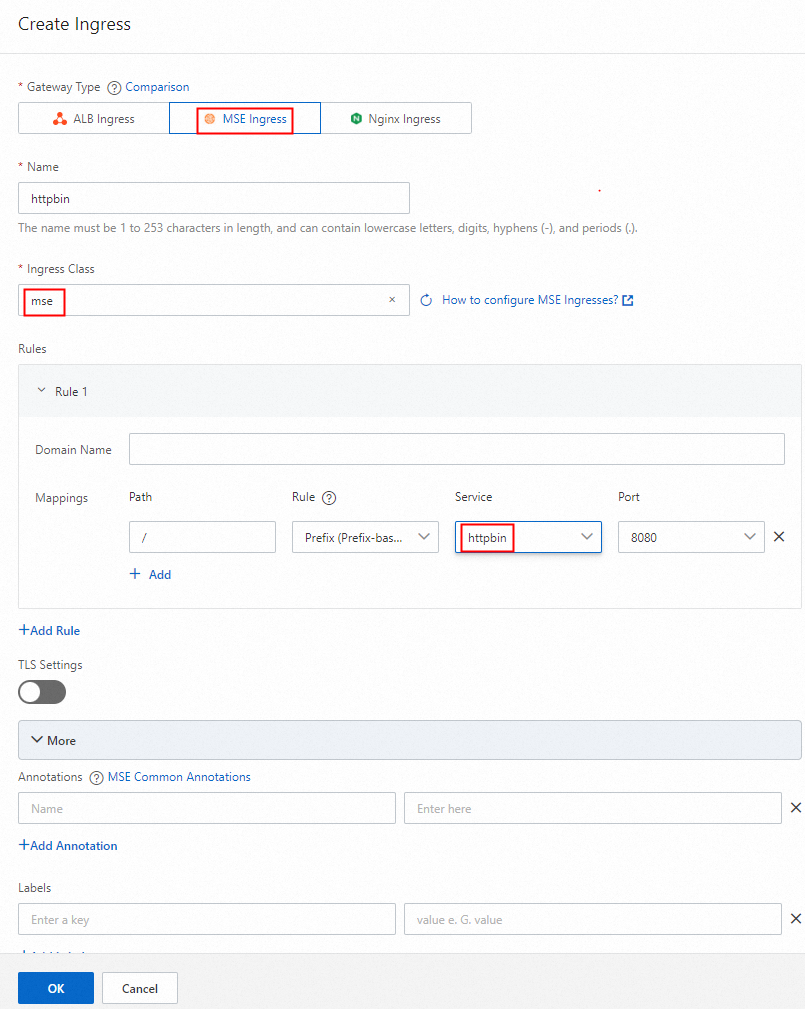
Step 3: Configure an MSE Ingress route
-
Log on to the ACK console. In the left-side navigation pane, click Clusters.
-
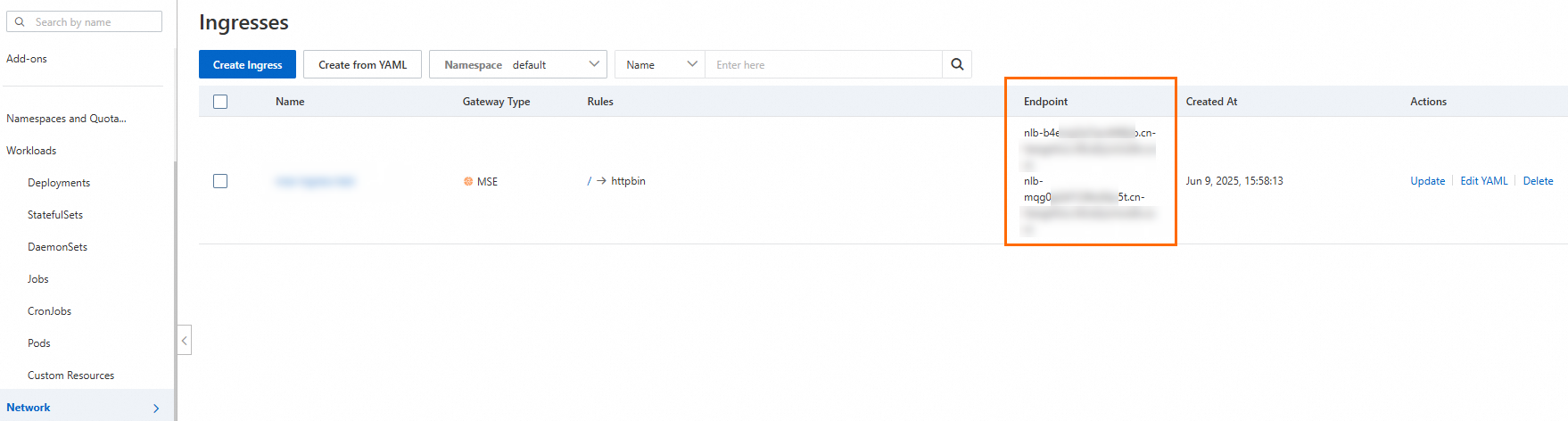
On the Clusters page, find the cluster you want and click its name. In the left-side navigation pane, choose Network > Ingresses.
-
On the Ingresses page, click Create Ingress.
-
In the Create Ingress dialog box, set Gateway Type to MSE Ingress and configure the route: Click OK.
-
Set Ingress Class to
mse. -
Under Rule, select Prefix (Prefix-based Match) from the drop-down list.
-
Set Path to
/. -
Set Service to
httpbin.
-
-
Log on to the MSE console to confirm a route containing
httpbinis configured for the cloud-native gateway. To verify from the command line, run:kubectl get ingress -n defaultThe expected output is similar to:
NAME CLASS HOSTS ADDRESS PORTS AGE httpbin mse * nlb-b4ewsj2******.cn-hangzhou.nlb.aliyuncsslb.com 80 30s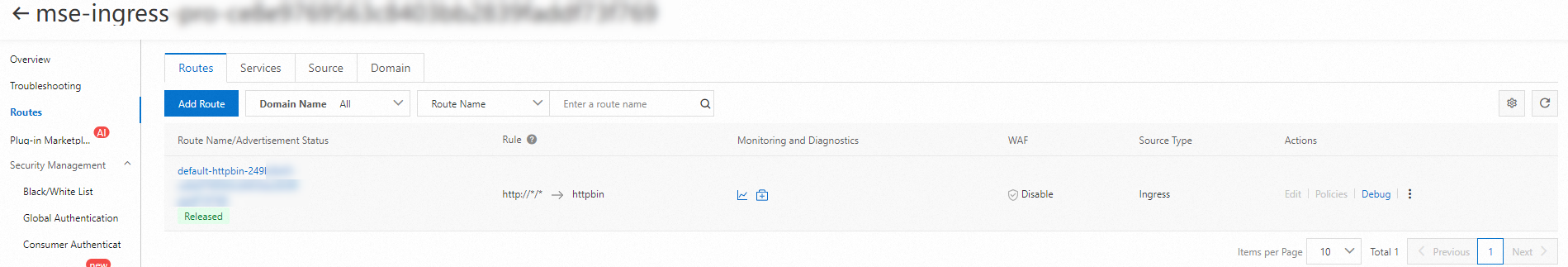
Step 4: Access the service
-
Log on to the ACK console. In the left-side navigation pane, click Clusters.
-
On the Clusters page, find the cluster you want and click its name. In the left-side navigation pane, choose Network > Ingresses.
-
On the Ingresses page, find the Ingress endpoint in the Address column.
-
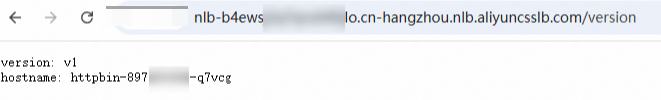
Access the service using the NLB domain name or the public IP address of the gateway. For example, run:
curl http://nlb-b4ewsj2******.cn-hangzhou.nlb.aliyuncsslb.com/versionA successful response confirms the service is accessible through the MSE Ingress gateway.
What's next
-
Advanced routing: Configure annotations on your Ingress resources to enable traffic splitting, canary releases, and request rewriting.
-
TLS termination: Add HTTPS support by configuring a certificate on the MSE cloud-native gateway.
-
Monitoring: View gateway metrics and access logs in the MSE console to monitor traffic and diagnose issues.
-
Clean up: To remove the test resources, delete the
httpbinDeployment, Service, and Ingress from the ACK console, or runkubectl delete deployment,service,ingress httpbin -n default.