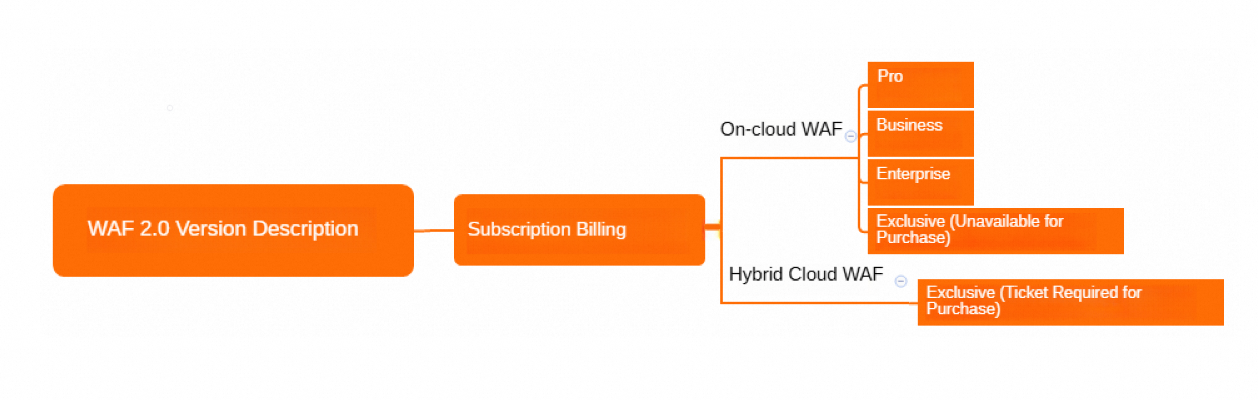
Web Application Firewall (WAF) uses subscription billing. This page describes the available deployment plans, editions, and the features each edition supports. supports the subscription billing method. This topic describes the business scales and protection features offered by different editions.
WAF plans and editions
WAF offers two deployment plans:
On-cloud WAF: Available in Pro, Business, Enterprise, and Exclusive (sales suspended) editions.
Hybrid Cloud WAF: Available in the Exclusive edition only.
References:
Applicable business scales
The following table compares capacity and scale limits across editions. For medium-sized enterprise websites, Business or Enterprise is the typical choice.
| Specification | On-cloud WAF Pro | On-cloud WAF Business | On-cloud WAF Enterprise | On-cloud WAF Exclusive (sales suspended) | Hybrid Cloud WAF Exclusive |
|---|---|---|---|---|---|
| Site scale | Small and medium-sized websites with no special security requirements. | Medium-sized enterprise websites or internet-facing services with high data security requirements. | Medium and large-sized enterprise websites with large business scale or special custom security requirements. | Large-sized enterprise websites with large business scale that require custom configurations based on business features. | Medium and large-sized enterprise websites with on-premises services and web traffic that cannot be protected by On-cloud WAF, requiring the same high-standard web security protection. |
| Peak concurrent requests (On-cloud WAF) | 2,000 QPS | 5,000 QPS | Over 10,000 QPS | 5,000 QPS | 0 QPS (extendable) |
| On-premises cluster nodes and peak concurrent requests | Not supported | Supported for a fee | Supported for a fee | Supported for a fee | 2 protection nodes, 10,000 QPS |
| Service bandwidth (origin on Alibaba Cloud) | 50 Mbps | 100 Mbps | 200 Mbps | 100 Mbps | 0 Mbps (extendable) |
| Service bandwidth (origin not on Alibaba Cloud) | 10 Mbps | 30 Mbps | 50 Mbps | 30 Mbps | — |
| Default protected root domain names | 1 | 1 | 1 | 1,000 | 200 (regardless of domain level; +100 per additional node) |
| Default total protected domain names (wildcard domains supported) | 10 | 10 | 10 | 1,000 | — |
Feature list by edition (Chinese mainland)
The following table lists features supported by each WAF edition for instances deployed in the Chinese mainland region.
Legend: Supported = included in the edition. Paid add-on = available for an additional fee. Not supported = unavailable.
| Feature | Description | On-cloud WAF Pro | On-cloud WAF Business | On-cloud WAF Enterprise | On-cloud WAF Exclusive (sales suspended) | Hybrid Cloud WAF Exclusive |
|---|
Service access HTTPS security protection| One-click, site-wide HTTPS protection.| Supported| Supported| Supported| Supported| Supported Asset discovery| Proactively discovers and manages site assets; supports one-click protection.| Supported| Supported| Supported| Supported| Supported Transparent proxy mode| Forwards traffic from origin servers (SLB and ECS instances) directly to WAF for protection.| Supported| Supported| Supported| Supported| Not supported HTTP/2 security protection| Protects websites that use HTTP/2.| Not supported| Supported| Supported| Supported| Supported Non-standard port protection| Protects services on non-standard ports (ports other than 80, 8080, 443, and 8443).| Not supported| Supported| Supported| Supported| Supported IPv6 protection| Detects and blocks IPv6-based requests.| Not supported| Supported| Supported| Supported| Supported Exclusive cluster| Custom access and protection capabilities tailored to your business requirements.| Not supported| Not supported| Not supported| Supported| Supported On-premises protection cluster deployment| Deploys a WAF protection cluster in an on-premises data center to protect web traffic that does not pass through Alibaba Cloud.| Not supported| Paid add-on| Paid add-on| Paid add-on| Supported Intelligent load balancing| Multi-node intelligent traffic scheduling with automatic failover across origin servers.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Exclusive Resource Plan for Domain Names| Exclusive IP address protection for a specific domain name.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Website protection Protection Rules Engine| Defends against common web attacks such as SQL injection and XSS.| Supported| Supported| Supported| Supported| Supported Auto-updates protection rules against web zero-day vulnerabilities.| Supported| Supported| Supported| Supported| Supported Website tamper-proofing| Locks website pages to prevent malicious tampering.| Supported| Supported| Supported| Supported| Supported Data leakage prevention| Blocks responses containing sensitive data such as phone numbers, ID card numbers, and bank card numbers.| Supported| Supported| Supported| Supported| Supported CC attack protection| Defends against CC attacks with built-in and emergency protection modes.| Supported| Supported| Supported| Supported| Supported Account security| Detects dictionary attacks, brute-force attacks, spam registrations, weak password sniffing, and bot traffic on CAPTCHA interfaces for login and registration pages.| Supported| Supported| Supported| Supported| Supported IP blacklist| One-click blocking of traffic from specific IP addresses and CIDR blocks.| Supported| Supported| Supported| Supported| Supported Geo-blocking: one-click blocking of traffic from IP addresses in specified geographic locations. (Includes IP blacklist.)| Not supported| Supported| Supported| Supported| Supported Scan protection| Blocks high-frequency web attacks (default rule), directory traversal (default rule), scan tool traffic, and collaborative defense.| Supported| Supported| Supported| Supported| Supported Custom rules for high-frequency web attack blocking and directory traversal blocking. (Includes scan protection.)| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Basic precise access control| ACL-based rules using IP, URL, Referer, User-Agent, and Params.| Supported| Supported| Supported| Supported| Supported Custom mitigation policies — Advanced precise access control| Includes basic fields plus Cookie, Content-Type, Header, and Http-Method.| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Rate limiting (by IP or session)| Custom CC protection rules with rate limiting based on IP address or session.| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Rate limiting (by custom fields)| Rate limiting policies based on custom fields including IP and session.| Not supported| Not supported| Supported| Supported| Supported DDoS attack prevention| Free DDoS protection. For mitigation thresholds, see thresholds that trigger blackhole filtering in Anti-DDoS Basic.| Supported| Supported| Supported| Supported| Not supported Custom protection rule groups| Custom rule groups for fine-grained protection policy management.| Not supported| Supported| Supported| Supported| Supported Proactive defense| Deep learning-based traffic analysis for proactive threat detection.| Not supported| Not supported| Supported| Supported| Supported Data risk control| Defends against bot-driven fraud on key pages such as registration, login, campaigns, and forums.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Not supported Legitimate bots| Allowlist for legitimate search engine bots to permit their requests to your domain.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Bot threat intelligence| Intelligence-driven rules covering dial-up IP pools, data center IPs, malicious scan tool IPs, and real-time cloud model threat libraries. Blocks malicious bot traffic to specific domains or URL paths.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on App protection| Security protection for native apps, including trusted communication and bot prevention. Detects requests from proxies, emulators, and tampered app signatures.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Security analytics and support Alerting settings| WAF event monitoring and threshold-based alerts via CloudMonitor.| Supported| Supported| Supported| Supported| Supported Simple Log Service| Stores all WAF logs in Simple Log Service with near-real-time query, analysis, and online reporting.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on
Editions and features (outside the Chinese mainland)
The following table describes the features supported by different editions of subscription WAF instances in regions outside the Chinese mainland.
Feature module | Description | On-cloud WAF Pro | On-cloud WAF Business | On-cloud WAF Enterprise | On-cloud WAF Exclusive (No longer available) | Hybrid Cloud WAF Exclusive |
Website access | ||||||
Enables site-wide HTTPS protection with a single click. |
|
|
|
|
| |
Directs traffic from your origin server, such as an SLB instance or an ECS instance, to WAF for protection. |
|
|
|
|
| |
Protects websites that use the HTTP/2 protocol. |
|
|
|
|
| |
Protects services on ports other than 80, 8080, 443, and 8443. |
|
|
|
|
| |
Provides custom access and protection capabilities based on your business requirements. |
|
|
|
|
| |
Detects and protects against threats in IPv6 traffic. |
|
|
|
|
| |
Provides automatic scheduling and disaster recovery for your origin server by distributing traffic across multiple nodes and network lines. |
|
|
|
|
| |
Protects traffic not routed through the public Alibaba Cloud WAF service by letting you deploy a protection cluster in your on-premises data center |
|
|
|
|
| |
Enables protection for a domain name by using an exclusive IP address. |
|
|
|
|
| |
Website Protection | ||||||
Detects security risks on account-related endpoints, such as registration and login pages. These risks include credential stuffing, brute-force attacks, spam registration, weak password sniffing, and SMS verification code abuse. |
|
|
|
|
| |
Defends against common web attacks, such as SQL injection and XSS. |
|
|
|
|
| |
Automatically updates protection rules for zero-day web vulnerabilities. |
|
|
|
|
| |
Defends against common HTTP flood attacks with a built-in protection mode and an emergency mode. |
|
|
|
|
| |
Blocks access from specified IP addresses and CIDR blocks. |
|
|
|
|
| |
Also blocks access from specified geographic locations. |
|
|
|
|
| |
Blocks high-frequency web attacks and directory traversal attempts by using default rules. It also supports scanner blocking and collaborative defense. |
|
|
|
|
| |
Lets you create custom rules to block high-frequency web attacks and directory traversal. |
|
|
|
|
| |
Basic access control: Creates access control list (ACL) rules based on basic fields such as IP, URL, Referer, User-Agent, and Params. |
|
|
|
|
| |
Advanced access control: Includes basic fields and supports advanced fields such as Cookie, Content-Type, Header, and Http-Method. |
|
|
|
|
| |
Lets you configure rate limiting policies (custom HTTP flood protection rules) to filter abnormal requests based on precise match conditions, with rate limits applied per IP address or session. |
|
|
|
|
| |
Extends rate limiting to include policies based on custom fields, in addition to IP addresses and sessions. |
|
|
|
|
| |
Locks website pages to prevent malicious content tampering. |
|
|
|
|
| |
Prevents the leakage of sensitive data, such as phone numbers, ID card numbers, and bank card numbers. |
|
|
|
|
| |
Lets you create and manage custom protection rule groups. |
|
|
|
|
| |
Uses deep learning to analyze your website traffic and proactively defend against threats. |
|
|
|
|
| |
Defends against bot-driven fraud on critical business endpoints, such as registration, login, promotion, and forum pages. |
|
|
|
|
| |
DDoS attack mitigation | Provides free DDoS attack mitigation. For more information about the protection capabilities, see Anti-DDoS Basic blackhole filtering thresholds. |
|
|
|
|
|
Maintains a whitelist of legitimate search engine crawlers to ensure they can access your domain. |
|
|
|
|
| |
Blocks malicious bots using threat intelligence rules derived from sources like dial-up IP pools, data centers, and malicious scanners. These rules can be applied to an entire domain or specific paths. |
|
|
|
|
| |
Protects native apps with features such as trusted communication and anti-bot scripting. It identifies and blocks requests from proxies, emulators, and illegally signed apps. |
|
|
|
|
| |
Security analysis and support | ||||||
支持通过云监控服务配置WAF事件监控、阈值监控规则。 |
|
|
|
|
| |
支持采集WAF所有的日志信息并存储至日志服务中,提供准实时查询分析和在线报表展示等功能。 |
|
|
|
|
| |
Feature list by edition (outside the Chinese mainland)
The following table lists features supported by each WAF edition for instances deployed outside the Chinese mainland.
Legend: Supported = included in the edition. Paid add-on = available for an additional fee. Not supported = unavailable.
| Feature | Description | On-cloud WAF Pro | On-cloud WAF Business | On-cloud WAF Enterprise | On-cloud WAF Exclusive (sales suspended) | Hybrid Cloud WAF Exclusive |
|---|
Service access HTTPS security protection| One-click, site-wide HTTPS protection.| Supported| Supported| Supported| Supported| Supported Transparent proxy mode| Forwards traffic from origin servers (SLB and ECS instances) directly to WAF for protection.| Supported| Supported| Supported| Supported| Not supported HTTP/2 security protection| Protects websites that use HTTP/2.| Not supported| Supported| Supported| Supported| Supported Non-standard port protection| Protects services on non-standard ports (ports other than 80, 8080, 443, and 8443).| Not supported| Supported| Supported| Supported| Supported Exclusive cluster| Custom access and protection capabilities tailored to your business requirements.| Not supported| Not supported| Not supported| Supported| Supported IPv6 protection| Detects and blocks IPv6-based requests.| Not supported| Not supported| Not supported| Not supported| Supported Intelligent load balancing| Multi-node intelligent traffic scheduling with automatic failover across origin servers.| Not supported| Paid add-on| Paid add-on| Paid add-on| Paid add-on On-premises protection cluster deployment| Deploys a WAF protection cluster in an on-premises data center to protect web traffic that does not pass through Alibaba Cloud.| Not supported| Paid add-on| Paid add-on| Paid add-on| Supported Dedicated resource plan for Domain Names| Exclusive IP address protection for a specific domain name.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Website protection Account security| Detects dictionary attacks, brute-force attacks, spam registrations, weak password sniffing, and bot traffic on CAPTCHA interfaces for login and registration pages.| Supported| Supported| Supported| Supported| Supported Protection Rules Engine| Defends against common web attacks such as SQL injection and XSS.| Supported| Supported| Supported| Supported| Supported Auto-updates protection rules against web zero-day vulnerabilities.| Supported| Supported| Supported| Supported| Supported CC attack protection| Defends against CC attacks with built-in and emergency protection modes.| Supported| Supported| Supported| Supported| Supported IP blacklist| One-click blocking of traffic from specific IP addresses and CIDR blocks.| Supported| Supported| Supported| Supported| Supported Geo-blocking: one-click blocking of traffic from IP addresses in specified geographic locations. (Includes IP blacklist.)| Not supported| Supported| Supported| Supported| Supported Scan protection| Blocks high-frequency web attacks (default rule), directory traversal (default rule), scan tool traffic, and collaborative defense.| Supported| Supported| Supported| Supported| Supported Custom rules for high-frequency web attack blocking and directory traversal blocking. (Includes scan protection.)| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Basic precise access control| ACL-based rules using IP, URL, Referer, User-Agent, and Params.| Supported| Supported| Supported| Supported| Supported Custom mitigation policies — Advanced precise access control| Includes basic fields plus Cookie, Content-Type, Header, and Http-Method.| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Rate limiting (by IP or session)| Custom CC protection rules with rate limiting based on IP address or session.| Not supported| Supported| Supported| Supported| Supported Custom mitigation policies — Rate limiting (by custom fields)| Rate limiting policies based on custom fields including IP and session.| Not supported| Not supported| Supported| Supported| Supported Website tamper-proofing| Locks website pages to prevent malicious tampering.| Not supported| Supported| Supported| Supported| Supported Data leakage prevention| Blocks responses containing sensitive data such as phone numbers, ID card numbers, and bank card numbers.| Not supported| Supported| Supported| Supported| Supported Custom protection rule groups| Custom rule groups for fine-grained protection policy management.| Not supported| Not supported| Supported| Supported| Supported Proactive defense| Deep learning-based traffic analysis for proactive threat detection.| Not supported| Not supported| Supported| Supported| Not supported Data risk control| Defends against bot-driven fraud on key pages such as registration, login, campaigns, and forums.| Not supported| Not supported| Not supported| Not supported| Not supported DDoS attack prevention| Free DDoS protection. For mitigation thresholds, see thresholds that trigger blackhole filtering in Anti-DDoS Basic.| Not supported| Not supported| Not supported| Not supported| Not supported Legitimate bots| Allowlist for legitimate search engine bots to permit their requests to your domain.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Bot threat intelligence| Intelligence-driven rules covering dial-up IP pools, data center IPs, malicious scan tool IPs, and real-time cloud model threat libraries. Blocks malicious bot traffic to specific domains or URL paths.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on App protection| Security protection for native apps, including trusted communication and bot prevention. Detects requests from proxies, emulators, and tampered app signatures.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on Security analytics and support Alerting settings| WAF event monitoring and threshold-based alerts via CloudMonitor.| Supported| Supported| Supported| Supported| Supported Simple Log Service| Stores all WAF logs in Simple Log Service with near-real-time query, analysis, and online reporting.| Paid add-on| Paid add-on| Paid add-on| Paid add-on| Paid add-on