Application Load Balancer (ALB) offers advanced Layer 7 load balancing and enhanced routing compared to Classic Load Balancer (CLB). ALB handles high-volume application-layer traffic and integrates with Web Application Firewall (WAF), decoupling traffic forwarding from security protection. This topic shows you how to manually migrate Layer 7 listeners from CLB to ALB.
Example scenario
This topic describes the following example scenario. A company has an Internet-facing CLB instance in the Alibaba Cloud China (Hangzhou) region. This CLB instance is configured with forwarding rules for redirection, domain names, and paths, and provides services over the Internet by using a DNS domain name. When a client accesses the domain name www.example.net, DNS directs the traffic to the CLB instance based on an A record. The CLB instance then forwards the traffic to ECS01 and ECS02 for processing based on its forwarding rules.

To meet business development needs, the company needs to migrate its services from a CLB instance to an ALB instance. To maintain service stability, the company wants to avoid changing the public-facing DNS domain name and the IP addresses of the backend servers. The company can create a new ALB instance in the China (Hangzhou) region and complete the relevant configurations to ensure that the ALB forwarding rules provide the same functionality as the CLB forwarding policies. Then, the company can use the weight settings for DNS resolution to complete the traffic migration.

Considerations
CLB supports the Pay-as-you-go billing methods, and ALB supports the Pay-as-you-go billing method. The billing items and pricing for CLB and ALB are different. If you migrate services from a CLB instance to an ALB instance, your billing will change. For more information about billing rules, see:
The ALB and CLB instances must use the same backend servers deployed in the same Virtual Private Cloud (VPC).
You can migrate only HTTP and HTTPS Listeners from a CLB instance to an ALB instance; TCP and UDP Listeners cannot be migrated.
You can migrate an IPv4 CLB instance to an IPv4 or dual-stack ALB instance. You can migrate an IPv6 CLB instance only to a dual-stack ALB instance.
Prerequisites
The CLB instance to be migrated has listeners and backend servers configured, and the CLB instance uses an A record to resolve its domain name and provide services to the public. For more information, see Overview.
The backend servers for the CLB instance are Elastic Compute Service (ECS) instances ECS01 and ECS02. Both ECS instances are in Virtual Private Cloud (VPC) 1 (VPC1).
The CLB instance has a redirect rule and forwarding rules. For more information, see Redirect HTTP requests to HTTPS and Forward requests based on domain names or URLs.
Two additional Elastic Compute Service (ECS) instances, ECS03 and ECS04, exist in VPC1. ECS03 is for testing traffic before the migration, and ECS04 is for verifying traffic during the migration. ECS04 has the dig command installed.
Step 1: Create an ALB instance
Log on to the ALB console.
On the Instances page, click Create ALB.
On the Application Load Balancer page, configure the following parameters.
Parameter
Description
Region
Select the region for the ALB instance. This region must be the same as that of the Classic Load Balancer (CLB) instance you are migrating. In this example, China (Hangzhou) is selected.
Network Type
Select the network type for the instance. The system assigns a private or public IP address based on your selection. The network type must match that of the CLB instance you are migrating. In this example, Public is selected.
Private: The ALB instance is assigned only a private IP address. It is accessible only by resources within the same VPC and cannot be accessed from the internet.
Public: The ALB instance is assigned both a public and a private IP address. By default, public-facing ALB instances use an Elastic IP Address (EIP) to provide public services. If you select Public, you are charged for the EIP instance and for data transfer.
Public IP address: The EIP provides services, allowing the ALB instance to be accessed from the internet.
Private IP address: Allows resources within the VPC to access the ALB instance.
ALB allows you to change the network type of an instance. For more information, see Change the network type of an ALB instance.
NoteFor dual-stack instances, the IPv4 address is used to provide services over the internet by default. To use an IPv6 address for public access, you must change the network type. In this case, you are charged IPv6 Gateway fees. For more information, see IPv6 Gateway billing.
VPC
Select the VPC where the Backend Servers of the CLB instance are deployed. In this example, VPC1 is selected.
Zone ID
Select zones and vSwitches.
ALB supports deployment across multiple Availability Zones. If the current region supports two or more Availability Zones, select at least two to ensure high availability. ALB does not charge extra for the Availability Zones.
Select a vSwitch for each zone. If a vSwitch is not available in a zone, follow the prompts to create one.
Optional: Select an EIP in each selected zone.
If no EIP is available, keep the default option Auto-assign Public IP. The system automatically creates a Pay-as-you-go (pay-by-data-transfer) EIP. This EIP uses BGP (multi-ISP) bandwidth and the default security protection mode. The system then associates the EIP with the ALB instance.
Select an existing EIP: You can select an existing EIP and associate it with the new ALB instance.
ImportantYou can associate only Pay-as-you-go (pay-by-data-transfer) EIPs that are not part of an Internet Shared Bandwidth instance.
The EIPs that you specify for different zones of the same ALB instance must be of the same type.
IP Version
Select the IP version for the instance. You can migrate services from an IPv4 CLB instance to an IPv4 or dual-stack ALB instance. You can migrate services from an IPv6 CLB instance only to a dual-stack ALB instance. Select an IP version based on your business requirements.
IPv4: The ALB instance can be accessed only by clients that use IPv4 addresses.
Dual-stack: Clients can access the ALB instance by using both IPv4 and IPv6 addresses. For more information about the limitations of dual-stack instances, see ALB instance overview.
Edition (Instance Fee)
Select the edition of the instance.
Basic: Provides the basic features of Application Load Balancer, such as routing based on domain names, URL paths, and HTTP headers.
Standard: Provides all the features of the Basic edition, plus advanced routing features such as custom TLS security policies, redirection, and rewrites.
WAF Enabled: Provides all the features of the Standard edition and adds WAF protection. If you select this edition, web traffic to the listeners of the ALB instance is automatically forwarded to WAF 3.0 for protection. For more information about the limitations of the WAF Enabled edition, see Enable WAF protection for an ALB instance.
For more information about the differences between the Basic, Standard, and WAF Enabled editions, see Features.
Associate with Internet Shared Bandwidth
By default, an ALB instance deployed in two Availability Zones has a maximum public bandwidth of 400 Mbit/s.
If you require more bandwidth, select Associate with Internet Shared Bandwidth. You must then select a shared bandwidth package. If no shared bandwidth packages are available, click Purchase Shared Bandwidth Package and complete the purchase. Then, return to the ALB purchase page and click the
 icon to select a shared bandwidth package.
icon to select a shared bandwidth package.We recommend that you purchase a Pay-as-you-go Internet Shared Bandwidth instance. For more information, see Create and manage an Internet Shared Bandwidth instance.
NoteThis parameter is available only when Network Type is set to Public.
Internet Metering Method
The default billing method is Pay-By-Data-Transfer. The maximum bandwidth is an upper limit for reference only and not a service-level commitment. During resource contention, the actual bandwidth may be limited. For more information about EIP billing, see Elastic IP Address (EIP) billing.
NoteThis parameter is available only when Network Type is set to Public and Associate with Internet Shared Bandwidth is not selected.
Instance Name
Enter a custom name for the instance.
Resource Group
Select the resource group to which the ALB instance belongs.
Note:
When creating your first Application Load Balancer instance, you must click Create to create a Service-Linked Role. This role grants ALB access to other cloud resources, such as Elastic Network Interfaces (ENIs), Security Groups, EIPs, and Internet Shared Bandwidth instances. For more information, see Service-linked roles for ALB.
NoteThis parameter is displayed only when you create an ALB instance for the first time.
Click Buy Now to complete the purchase.
Step 2: Create an ALB server group
Log on to the ALB console.
In the top navigation bar, select the region where your ALB instance is located. In this example, select China (Hangzhou).
In the left-side navigation pane, choose .
On the Server Groups page, click Create Server Group.
In the Create Server Group dialog box, set the following parameters and click Create.
This topic describes only the relevant parameters. Use the default values for all other parameters. For more information, see Create and manage server groups.
Parameter
Description
Server Group Type
Select a server group type. In this example, select Server.
Server Group Name
Enter a name for the server group. In this example, enter RS1.
VPC
Select a virtual private cloud (VPC). Only servers in the selected VPC can be added to the server group. In this example, select VPC1, which contains the backend servers of the CLB instance.
Backend Server Protocol
Select the protocol for the backend servers. In this example, select HTTP.
Scheduling Algorithm
Select a scheduling algorithm. In this example, select Weighted Round-robin.
In the wizard, click Add Backend Server. On the Backend Servers tab, click Add Backend Server.
In the Add Backend Server panel, select the same backend servers used by your CLB instance and click Next.
In this example, ECS01 and ECS02 are selected.
On the Ports/Weights page, set the port and weight for each ECS instance and click OK.
In this example, set the port to 80 and use the default weight of 100.
NoteTo handle traffic spikes, you can use Auto Scaling to automatically add or remove backend servers, which helps reduce costs.
Step 3: Configure listeners and forwarding rules
This section explains how to configure redirect, domain name-based, and path-based forwarding rules for the Application Load Balancer (ALB) instance.
If CLB is configured with HTTP redirection, the HTTP listener of ALB also needs to be configured with a redirection forwarding rule.
CLB is configured with forwarding policies for domain names and paths, and ALB must also be configured with forwarding rules for domain names and paths to provide the same functionality as CLB.
Add HTTP and HTTPS listeners
Log on to the ALB console.
In the top navigation bar, select the region where your ALB instance is located. In this example, select China (Hangzhou).
Use one of the following methods to open the listener configuration wizard:
On the Instances page, find the target instance and click Create Listener in the Actions column.
On the Instances page, click the ID of the target instance. On the Listener tab, click Create Listener.
In the Configure Listener wizard, set the following parameters for the HTTP listener and then click Next.
Parameter
Description
Listener Protocol
Select the protocol for the listener.
This example selects HTTP.
Listener Port
The port that receives and forwards requests to backend servers. Valid ports range from 1 to 65535. Typically, port 80 is used for HTTP and port 443 is used for HTTPS.
NoteListener ports must be unique per instance.
This example uses port 80.
Listener Name
Enter a name for the listener.
Advanced Settings
Click Modify to expand the advanced settings. This example uses the default settings.
In the Select Server Group wizard, select a server group of the Server, review its backend server information, and then click Next.
This example selects the server group RS1.
In the Configuration Review wizard, confirm the settings and click Submit.
Repeat these steps to create an HTTPS listener. For more information, see Add an HTTPS listener.
Use the following parameters:
Listener Protocol: Select HTTPS.
Listener Port: Enter 443.
Configure a redirect rule
Configure a redirection forwarding rule for the HTTP listener of an ALB instance to redirect all HTTP requests sent to the ALB to HTTPS port 443.
On the Listener tab, click the ID of the HTTP listener. On the listener details page, click the Forwarding Rules tab.
On the Forwarding Rules tab, click Add New Rule.
In the Add Forwarding Rule panel, configure the following parameters and click OK.
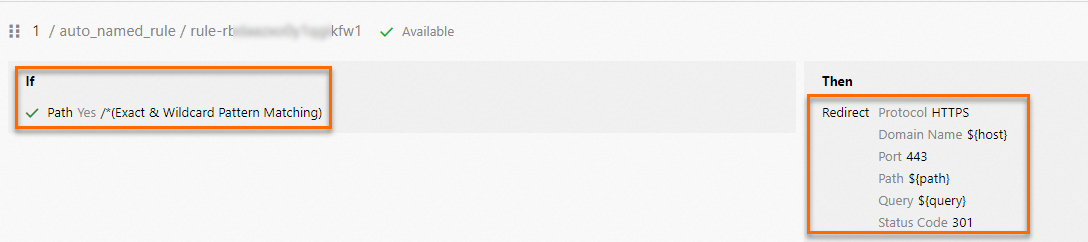
Parameter
Description
Add Condition
Select Path and Exact & Wildcard Pattern Matching. Enter
/*.Action
Select Redirect and configure the following parameters:
Protocol: Select HTTPS.
Domain Name: Use the default value ${host}.
Port: Enter the port of the HTTPS listener. This example uses 443.
Path: Use the default value ${path}.
Search: Use the default value ${query}.
Status Code: Select 301.
Configure domain and path forwarding rules
Configure domain name-based and path-based forwarding rules on the ALB instance's HTTPS listener.
Return to the Listener tab and click the ID of your HTTPS listener. On its details page, click the Forwarding Rules tab.
On the Forwarding Rules tab, click Add New Rule.
In the Add Forwarding Rule panel, configure the following parameters and click OK.
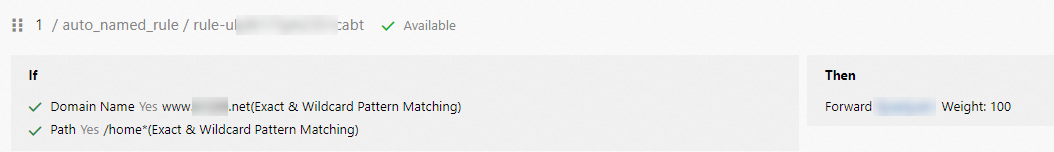
Parameter
Description
Add Condition
Select Domain Name and Exact & Wildcard Pattern Matching. Enter
www.example.net.Click Add Condition and select Path. Enter /home*.
Action
Select Forward and choose a server group. This example selects the server group RS1.
NoteEnsure the backend servers in the selected server group match those in the vServer group defined in the CLB instance's forwarding policy.
Step 4: Test traffic
Enable access logs
Application Load Balancer (ALB) integrates with Simple Log Service (SLS) to provide the Access Log feature. You can use access logs to monitor the load on your ALB instances and troubleshoot issues.
Log on to the ALB console.
In the top navigation bar, select the region where your ALB instance is located. In this example, select China (Hangzhou).
On the Instances page, find the desired ALB instance and click its instance ID.
On the instance details page, click the Access Logs tab. On this Access Logs, click Create Access Log.
In the Create Access Log dialog box, configure the Project and Logstore parameters, and then click OK. In the confirmation dialog box that appears, click OK again.
Parameter
Description
Project
A resource management unit in Simple Log Service (SLS) used for resource isolation and access control.
Select Project: Select a project from the drop-down list.
Create Project: Enter a name for the new project.
Logstore
A unit in Simple Log Service (SLS) for collecting, storing, and querying log data.
Select Logstore: Select a Logstore from the drop-down list.
Create Logstore: Enter a name for the new Logstore. If you create a new project, you must also create a new Logstore.
Notes on Creating Service-linked Role
When you perform this operation, the system automatically creates a service-linked role to grant ALB the required permissions.
Test traffic
Log on to ECS03. For instructions, see Connect to an ECS instance.
Run the following command to modify the hosts file:
sudo vi /etc/hostsAdd the following entry to the hosts file to map the IP address of the ALB instance to its domain name. Then, save your changes and exit.
118.XX.XX.39 www.example.netRun the following command to test the redirect configuration:
curl -X GET -L -v http://www.example.netThe command returns the following output:
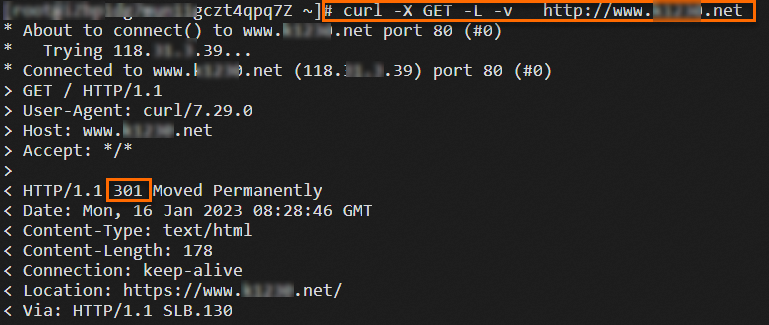
Return to the ALB Console, go to the Access Logs tab of the desired ALB instance, and then click the link next to Simple Log Service to view the access log.
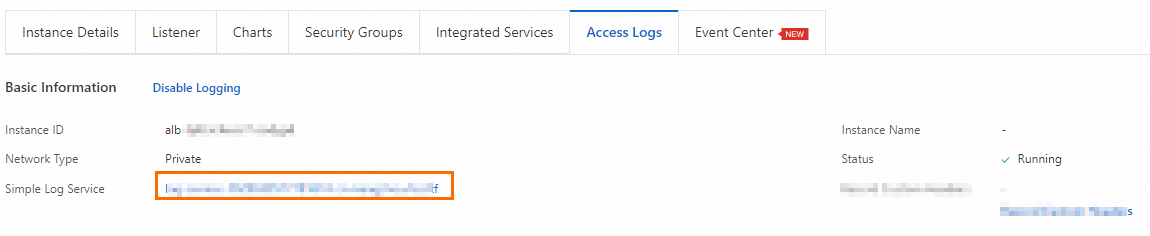 In the Simple Log Service (SLS) console, you can view the logs for the domain name-based and URL-based forwarding rules of the ALB instance by examining the
In the Simple Log Service (SLS) console, you can view the logs for the domain name-based and URL-based forwarding rules of the ALB instance by examining the request_uri,http_host,upstream_addr, andstatusfields.
Step 5: Migrate traffic to ALB
This guide uses an example in which a Classic Load Balancer (CLB) processes requests as shown in the following figure. A rule is configured to redirect requests from HTTP port 80 to HTTPS port 443. The HTTPS listener supports multiple domain names. In this example, the domain name is example.net.

Before you migrate traffic, compare the configurations of your Classic Load Balancer (CLB) forwarding policies and Application Load Balancer (ALB) forwarding rules to ensure that they provide identical capabilities and that all configurations are fully tested and accepted. This prevents unexpected impacts on your business during the migration process.
We recommend that you migrate Classic Load Balancer (CLB) traffic during off-peak hours.
Before you migrate traffic, domain name resolution must be configured for the target CLB instance, and you must have pointed your business domain name to the service address of the CLB instance by using an A record.

After you verify the configuration of your Application Load Balancer (ALB) instance, this topic uses Alibaba Cloud DNS as an example to describe the steps that you can follow to migrate traffic from a Classic Load Balancer (CLB) to an ALB. For more information about Alibaba Cloud DNS, see Public Authoritative DNS Resolution.

Step 1: Add a CNAME record for the CLB
Using CNAME resolution is recommended for ALB instances. To meet the prerequisites for enabling domain name weight configuration, you must add a CNAME record for a temporary domain name and point the temporary domain name to the service address of the CLB instance that you want to switch over. This topic assumes that the business domain name configured for the CLB instance is www.example.net.
To use weighted routing, you must have multiple A, CNAME, or AAAA records for the same hostname and query source.
Log on to the Alibaba Cloud DNS console.
On the Public Zone page, find the domain name
example.netfor the Classic Load Balancer (CLB) instance that you want to migrate, and click the domain name.On the Settings page, find the A Record that points to the service address of the Classic Load Balancer (CLB) instance that you want to migrate, and in the Actions column, click Modify.
In the Edit Record panel, change the Hostname and click OK. In this example, change the Hostname to web0. Keep the default values for the other parameters.
On the Settings tab, click Add Record. In the Add Record panel, configure the following parameters and click OK.
Parameter
Description
Record Type
Select CNAME from the drop-down list.
Hostname
The prefix for your domain name. This example uses www.
Query Source
Select Default.
TTL
Specifies how long a DNS record is cached on a DNS server. This example uses 5 seconds.
Record Value
Enter the temporary domain name. This example uses web0.example.net.
Step 2: Add a CNAME record for the ALB
On the Settings tab, click Add Record. In the Add Record panel, configure the following parameters and click OK.
Parameter | Description |
Record Type | Select CNAME from the drop-down list. |
Hostname | The prefix for your domain name. This example uses www. |
Query Source | Select Default. |
TTL | Specifies how long a DNS record is cached on a DNS server. This example uses 5 seconds. |
Record Value | Enter the DNS name of your Application Load Balancer (ALB) instance. |
Step 3: Start the canary release
On the Settings tab, find the CNAME record that you added in Step 2. Click the arrow next to Modify and select Edit Record Set.
In the Record Values section of the Edit Record panel, set the weights for the DNS records of the Classic Load Balancer (CLB) and Application Load Balancer (ALB) instances. Set the weight of the DNS record for the CLB instance to 100 and the weight of the DNS record for the ALB instance to 0. Click OK to save the settings and exit.

After confirming that your services are not affected, gradually decrease the weight of the DNS record for the CLB instance while gradually increasing the weight of the DNS record for the ALB instance.
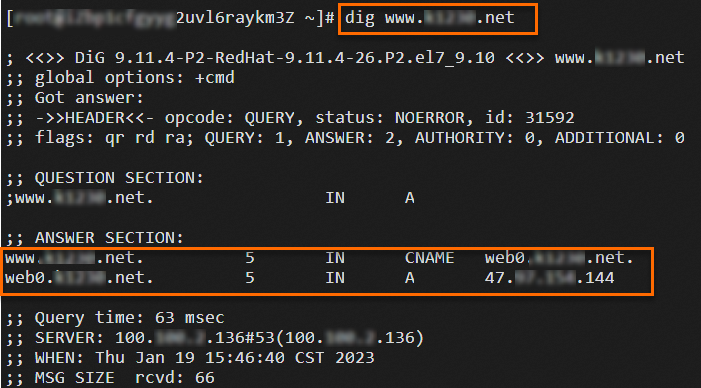
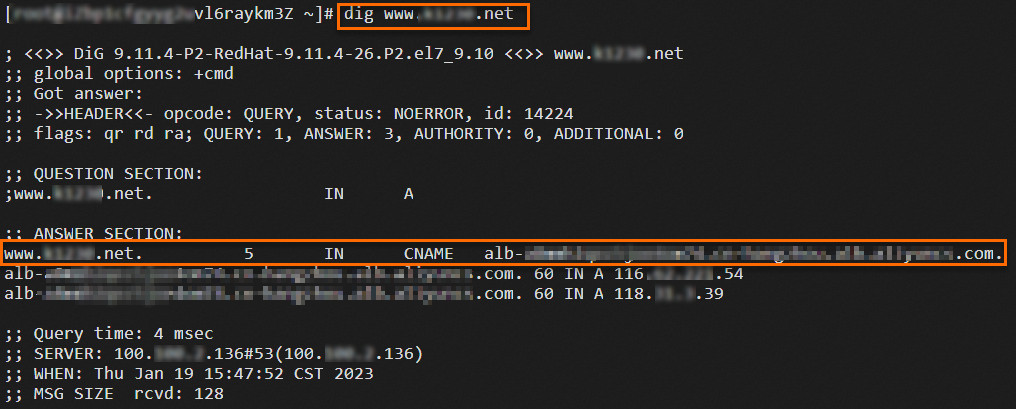
Log on to the ECS04 instance and run the
digcommand multiple times to verify the traffic migration.dig www.example.netThe results are shown in the following figures. You can run the test multiple times to observe that requests are distributed to either the Application Load Balancer (ALB) or the Classic Load Balancer (CLB) for processing based on the weights.
Step 4: Complete the traffic migration
Based on the traffic migration verification results, gradually decrease the weight of the DNS record for the CLB instance to 0 while gradually increasing the weight of the DNS record for the ALB instance to 100. You have now completed the migration of traffic from the CLB instance to the ALB instance. After all persistent connections to the CLB instance are closed and no new traffic is directed to the CLB instance, you can monitor the instance for a period of time based on your business scenario and then release the CLB instance. For more information about how to release a CLB instance, see Create and manage CLB instances.
After the migration is complete, the ALB instance processes requests as shown in the following figure:

Advanced features
Application Load Balancer (ALB) is an upgrade to the Layer 7 load balancing capabilities of Classic Load Balancer (CLB). The two products differ in the implementation of some features. You can learn more about ALB instances, quotas and limits, quick start, and Anti-DDoS protection from the following documents:
For an overview of ALB instances, see Overview of ALB instances.
For information about quotas and limits, see Quotas and Limits.
To get started with ALB, see Balance the load for IPv4 services by using ALB and Balance the load for IPv6 services by using ALB.
ALB provides basic DDoS protection by default. For more information, see What is Anti-DDoS Origin?.
The following table compares the advanced features of CLB and ALB:
Feature | CLB | ALB |
Server group management | Supports default server groups, vServer groups, and primary/secondary server groups. | Consolidates these types into a single Server Group. |
Redirect HTTP requests to HTTPS | You can configure redirects when you create a listener. For instructions, see Redirect HTTP requests to HTTPS by using CLB. | You can implement redirects by using forwarding rules. For instructions, see Redirect HTTP requests to HTTPS by using ALB. |
Attach multiple certificates to an HTTPS listener | For instructions, see Configure an HTTPS website that uses multiple domain names on a single CLB instance. | For instructions, see Configure an HTTPS website that uses multiple domain names on a single ALB instance. |
Deploy HTTPS services with one-way authentication | Supports Alibaba Cloud-issued certificates and uploaded third-party certificates. For instructions, see Deploy an HTTPS service with one-way authentication by using CLB. | Manages certificates by using Certificate Management Service. For instructions, see Configure end-to-end HTTPS access for encrypted communication. |
Deploy HTTPS services with Mutual Authentication | Supports CA certificates issued by Alibaba Cloud and uploaded third-party CA certificates. For instructions, see Deploy an HTTPS service with mutual authentication by using CLB. | Uses Certificate Management Service to manage CA certificates issued by Alibaba Cloud and uploaded third-party CA certificates. For instructions, see Deploy an HTTPS service with mutual authentication by using ALB. |
WAF Protection | Supports transparent proxy mode and CNAME record mode. For instructions, see Enable WAF protection for a CLB instance and Enable WAF protection for a website by using a CNAME record. | Supports service integration mode, transparent proxy mode, and CNAME record mode.
|
FAQ
Which configurations of the CLB instance and the ALB instance must remain consistent before and after the migration?
The region, network type, listener protocol, and backend servers must be the same. The VPC of the ALB instance must be the same as the VPC of the backend servers of the CLB instance. The availability zones do not need to be the same.
What are the differences between the certificates used by CLB and ALB?
Both Classic Load Balancer (CLB) and Application Load Balancer (ALB) support encrypted transmission over the HTTPS protocol. CLB natively supports uploading certificates issued by Alibaba Cloud and third-party certificates, whereas ALB uses certificates that are managed by the Certificate Management Service.
To upload a certificate for a Classic Load Balancer (CLB) instance, see Upload Certificate.
For certificate upload operations for ALB instances, see Purchase a commercial certificate and Upload, synchronize, and share SSL certificates.
What are the differences in access control between Classic Load Balancer (CLB) and Application Load Balancer (ALB)?
CLB provides listener-level access control. You can configure different access policies for different listeners. For more information, see Access Control.
The protocol version of an Application Load Balancer (ALB) can be IPv4 or dual-stack. ALB IPv4 instances support configuring different access policies for different listeners. For more information, see Access Control. ALB dual-stack instances do not support access control.
What are the differences in domain name resolution between Classic Load Balancer (CLB) and Application Load Balancer (ALB)?
A CLB instance requires an A record to point a custom domain name to the service address of the CLB.
For ALB instances:
Use a CNAME record to point a custom domain name to the DNS name of the ALB instance. This makes it easier to access network resources.
If a custom domain name must resolve to a fixed IP address, use an ALB instance in Fixed IP Mode. Create an A record to point the custom domain name to the IP address provided by the ALB.
