By Shantanu Kaushik
Sensitive data may be scattered across the enterprise in different cloud storage resources. The amount of visibility you can maintain throughout the data lifecycle depends on how efficient your data discovery practice is.
In Part 2, we discussed the Alibaba Cloud Sensitive Data Discovery and Protection (SDDP) suite and its benefits. This article discusses how Alibaba Cloud SDDP works with cloud resources undergoing continuous evolution some of the prominent features and usage scenarios.
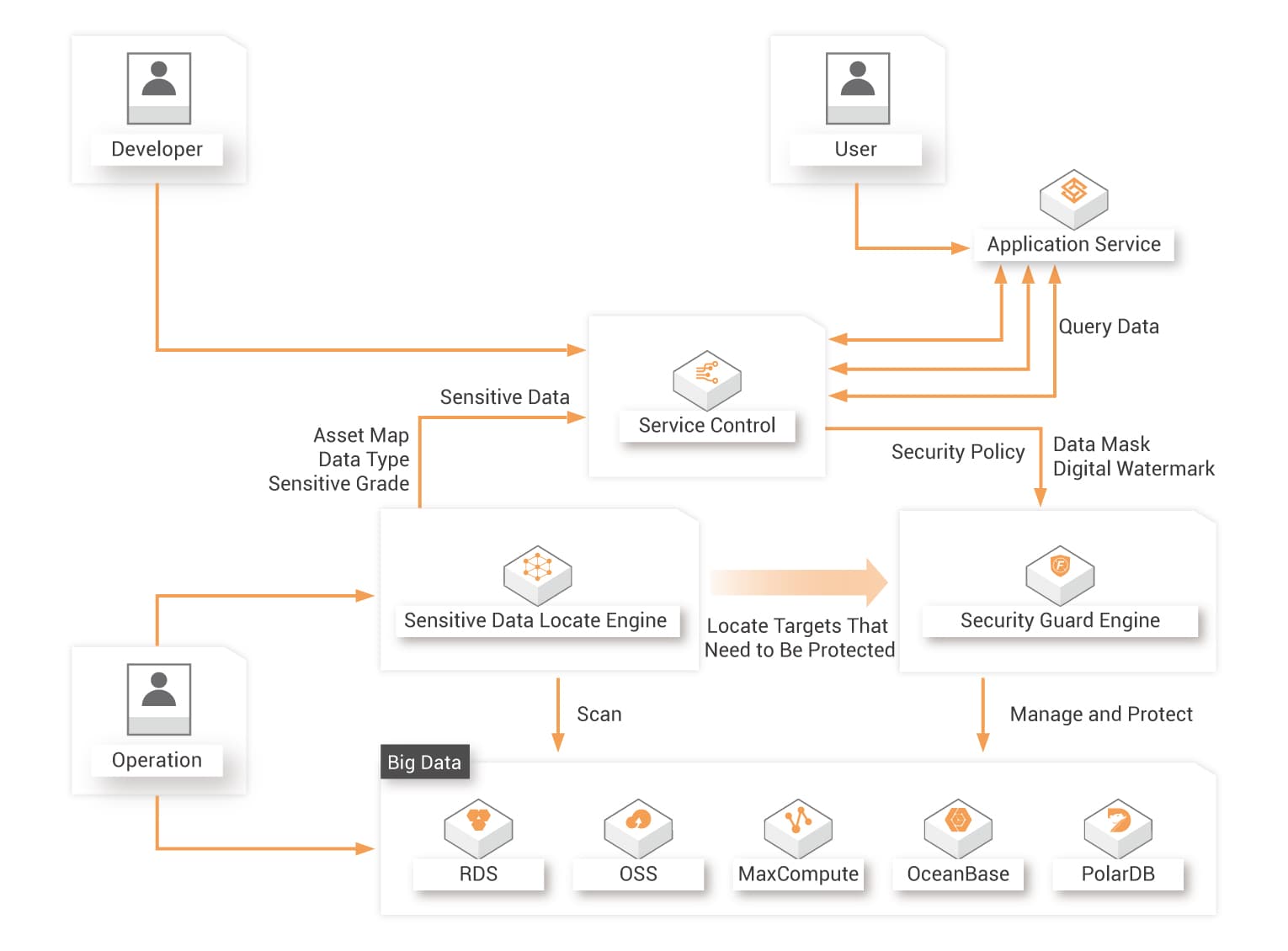
Alibaba Cloud Sensitive Data Discovery and Protection is an end-to-end data monitoring and management solution that provides an extensive data security service with multi-level classification.
Alibaba Cloud has done extensive research with solutions spanning a variety of scenarios and solving complexities related to real-world issues. When it comes to data security, Alibaba Cloud has a widely-defined security suite of products classified using cloud security, business security, identity management, and data security.
Alibaba Cloud SDDP can discover, classify, and protect the objects even when dealing with large amounts of data. Alibaba Cloud SDDP performs comprehensive detection by enabling precise scanning, classification, and grading throughout structured and unstructured data. Alibaba Cloud SDDP uses identity and access management to access built-in algorithms and customizable sensitive data detection rules.
Alibaba Cloud SDDP provides security protection based on the detection results with fine-grained access control and encryption mechanisms to store the discovered sensitive data securely. Alibaba Cloud SDDP can distinguish between sensitive data and non-sensitive data using intelligent scanning mechanisms.
Alibaba Cloud SDDP scans your structured and unstructured data sources and classifies the sensitive data discovered. Then, it marks it with risk levels to enable extra protection using Alibaba Cloud’s in-house fine-grained access control and storage encryption.
Alibaba Cloud SDDP provides diversified built-in de-identification algorithms based on meticulous parameters for precise data handling. Within an enterprise, there is no space for erroneous data classification. If a service declassifies and de-identifies viable data, it could be chaotic.
Alibaba Cloud SDDP allows you to create custom de-identification rules that can provide you with a highly viable environment for data classification. You can use SDDP to de-identify sensitive data in the production environment and within the pre-production environment.
After your data has been de-identified, you can use this data again in pre-production environments, such as development environments and test environments. Alibaba Cloud SDDP ensures the authenticity and availability of the de-identified data for any future uses you might have.
Alibaba Cloud SDDP lets you control the security risks and issues within your enterprise system-related data by enabling a smooth optimization workflow in-sync and aligned with your security policies based on the information displayed in the SDDP console. The Alibaba Cloud SDDP console will display the storage objects that contain sensitive data and reflect all the users that can access that particular data. It will also give detailed reports regarding security policies that apply to different storage resources and the anomalous data flows and activities related to the whole system.
Alibaba Cloud SDDP enables highly instrumental visualization scenarios that depict the results of sensitive data discovery and allows you to obtain a clear view of the security status of your data resources.
Highlights:
Alibaba Cloud’s extensive experience with cloud security and data protection for cloud-native solutions for enterprises enables four core data security capabilities to help organizations migrate to the cloud without worrying about security issues. Alibaba Cloud SDDP detects and monitors sensitive data and data activities at high risks and provides risk management solutions using big data and machine learning technologies.
Highlights:
Alibaba Cloud SDDP detects sensitive data automatically by utilizing a data detection engine. This engine scans, classifies, and grades sensitive data in structured data storage services, such as ApsaraDB RDS, and unstructured data storage services, such as OSS and MaxCompute. This enables a highly efficient practice that copes with blind spots in data management.
Highlights:
Alibaba Cloud SDDP has a strict policy towards plugging any possible data leaks. Right after the sensitive data is detected, SDDP de-identifies the data in the production, test, and analysis environments to prevent any data leaks. Alibaba Cloud SDDP uses highly refined de-identification algorithms to facilitate data de-identification. SDDP provides a flexible approach for data de-identification.
Highlights:
Enterprises today are generating data at unprecedented rates, increasing the data discovery complexities in the process. Maintaining your organization’s security requirements with a highly viable data discovery and protection system is paramount.
Enterprises want to adopt a solution that can adequately assess the full data practice and implement the appropriate security measures to prevent sensitive data loss.

2,593 posts | 794 followers
FollowAlibaba Clouder - April 2, 2021
Alibaba Clouder - April 2, 2021
Alibaba Clouder - April 1, 2021
Alibaba Clouder - April 1, 2021
Alibaba Cloud Native Community - January 4, 2026
Alibaba Clouder - March 31, 2021

2,593 posts | 794 followers
Follow Platform For AI
Platform For AI
A platform that provides enterprise-level data modeling services based on machine learning algorithms to quickly meet your needs for data-driven operations.
Learn More Epidemic Prediction Solution
Epidemic Prediction Solution
This technology can be used to predict the spread of COVID-19 and help decision makers evaluate the impact of various prevention and control measures on the development of the epidemic.
Learn More Secure Access Service Edge
Secure Access Service Edge
An office security management platform that integrates zero trust network access, office data protection, and terminal management.
Learn More RAM(Resource Access Management)
RAM(Resource Access Management)
Secure your cloud resources with Resource Access Management to define fine-grained access permissions for users and groups
Learn MoreMore Posts by Alibaba Clouder