Cloud Firewall includes a powerful built-in threat detection engine that blocks malicious traffic and common internet-based attacks in real time. It also delivers precise virtual patching. The Mitigation Settings feature lets you flexibly configure the threat detection engine’s operating mode. You can enable and adjust modules such as threat intelligence, basic protection, intelligent defense, and virtual patching to identify and block potential intrusions with greater accuracy. This topic describes how to configure the intrusion prevention system (IPS) feature.
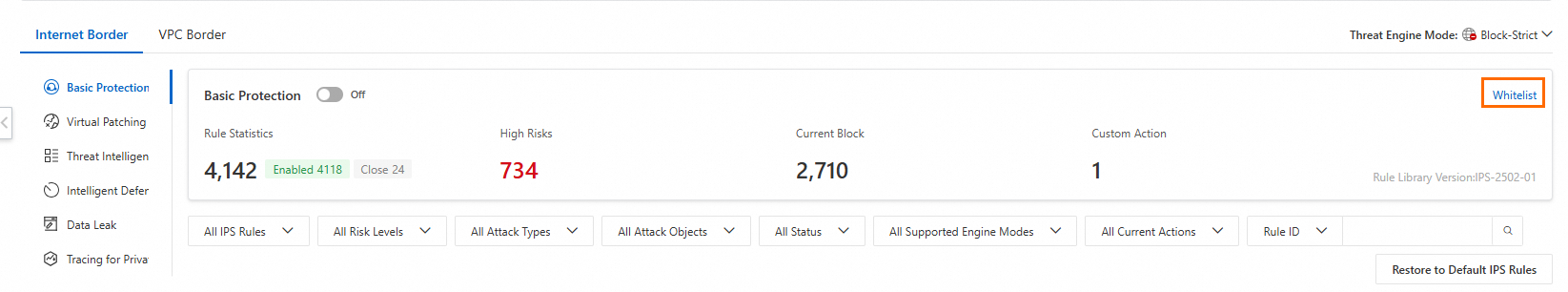
IPS capabilities for the Internet border
Threat detection engine operating modes
After you enable Cloud Firewall, the threat detection engine operates in Block Mode by default. Cloud Firewall automatically selects the appropriate block mode level based on your traffic. Basic protection and virtual patching block threats only when Block Mode is enabled. If Block Mode is disabled, the intrusion prevention feature monitors threats and malicious traffic without blocking them.
For more information about the threat detection engine’s operating modes, see IPS capabilities overview.
Log on to the Cloud Firewall console. In the left navigation pane, choose .
On the Internet Border tab, set the Threat Engine Mode on the far right.
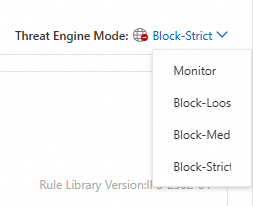
You can select one of the following two modes for the threat detection engine:
Monitor: When Monitor mode is enabled, Cloud Firewall logs and alerts on attacks but does not block them. Threat intelligence, basic protection, and virtual patching all operate in Monitor mode.
Block: When Block mode is enabled, Cloud Firewall blocks malicious traffic to prevent intrusions.
Select a block mode level that meets your protection requirements:
Block - Loose: Provides coarse-grained protection, primarily covering rules with low false positive rates. This mode is suitable for business scenarios sensitive to false positives.
Block - Medium: Provides moderately coarse-grained and precise protection, falling between Loose and Strict modes. This mode is suitable for routine daily O&M protection.
Block - Strict: Provides fine-grained protection, covering nearly all rules. This mode may have a higher false positive rate than Medium mode and is suitable for scenarios sensitive to false negatives, such as major event support.
Function introduction
The IPS Configuration for the Internet border supports features such as Basic protection, Virtual patching, Threat intelligence, Intelligent defense, Data leak detection, and IPS Private IP Tracing. Use the switches on the left to enable or disable these features.
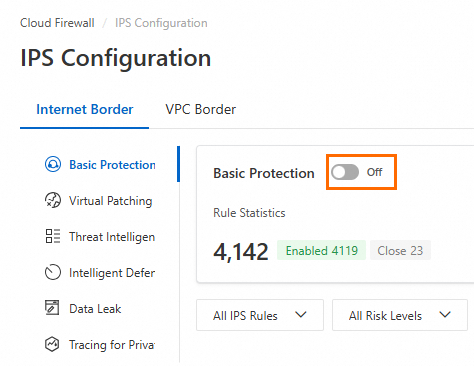
Basic protection
The Basic Protection switch is enabled by default. Cloud Firewall activates detection rules for common threats. This provides fundamental intrusion prevention, including blocking command execution vulnerabilities and managing the behavior of infected devices connecting to command-and-control (C&C) servers. Enable basic protection to enhance asset security.
Modify a protection rule: In the Current Action column, modify the protection rule. The modified rule is marked as a custom rule.
Restore default protection rules: Click Restore to Default IPS Rules, then click OK.
Enable or disable a rule: Click the switch in the Status column.
Enabled: The rule is active. Custom protection rules take precedence over default rules.
Disabled: The rule is inactive.
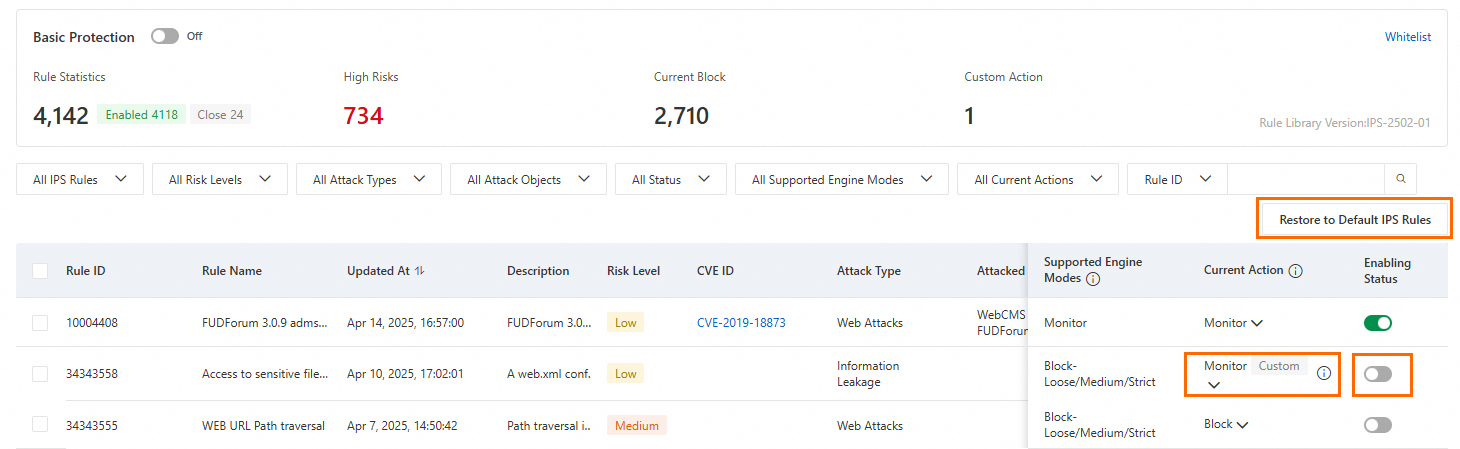
Virtual patching
The Virtual Patching switch is enabled by default. Cloud Firewall provides real-time protection against popular important and emergency vulnerabilities. Virtual patching delivers hot patches at the network layer for remotely exploitable important and emergency vulnerabilities, blocking vulnerability-based attacks in real time and preventing business interruptions caused by host-level vulnerability remediation. You do not need to install virtual patches on your servers. If virtual patching is disabled, it cannot be updated automatically in real time. Enable all virtual patches.
Modify a protection rule: In the Current Action column, modify the protection rule. The modified rule is marked as a custom rule.
Restore default protection rules: Click Restore to Default IPS Rules, then click OK.
Enable or disable a rule: Click the switch in the Status column.
Enabled: The rule is active. Custom protection rules take precedence over default rules.
Disabled: The rule is inactive.
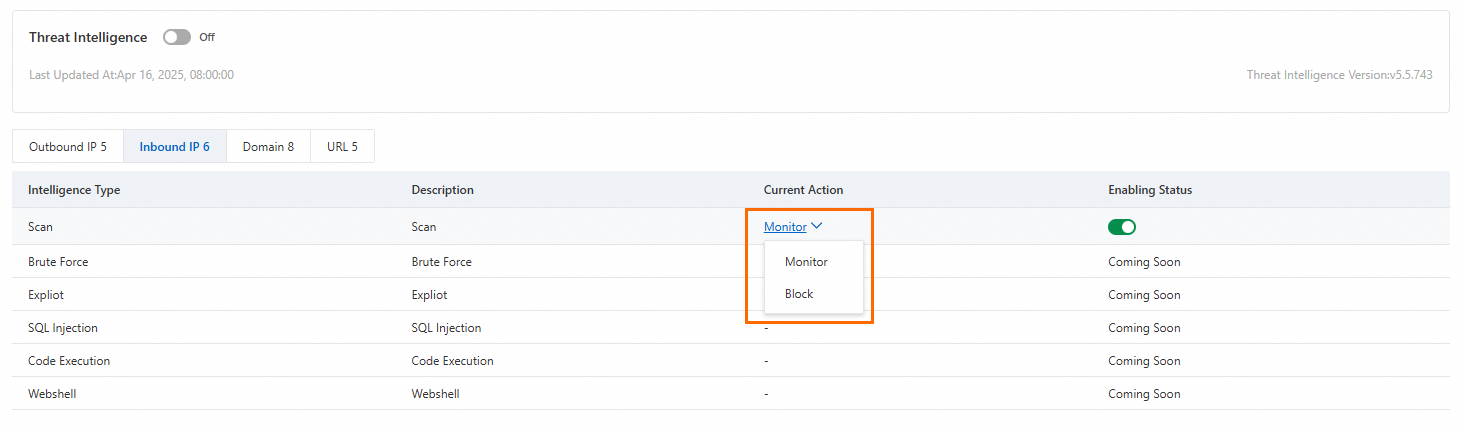
Threat intelligence
The Threat Intelligence switch is enabled by default. Cloud Firewall scans for threat intelligence and applies either Monitor or Block actions. This feature synchronizes malicious IP addresses detected across the Alibaba Cloud network—including malicious access sources, scan sources, and source IP addresses of brute-force attacks—to Cloud Firewall. This enables precise blocking and early detection of network threats. Enable threat intelligence.
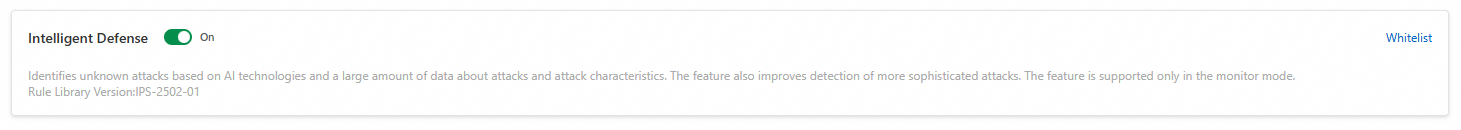
Intelligent defense
The Intelligent Defense switch is enabled by default. Cloud Firewall learns from cloud-wide attack data to improve threat and attack detection accuracy. Currently, intelligent defense is supported only when the threat detection engine operates in Monitor mode.
To enable Intelligent Defense, first enable Basic Protection.
Data breach
Cloud Firewall inspects outbound traffic—traffic from your business assets to the internet—for sensitive data to help identify risks of sensitive data leakage.
First, enable data leak detection for your assets.
In the Common Industry Template list, review the data types Cloud Firewall can detect. Enable detection for specific data types as needed.
Click Configure Assets, locate the target public asset, and click Enable Data Leak Detection in the Actions column.
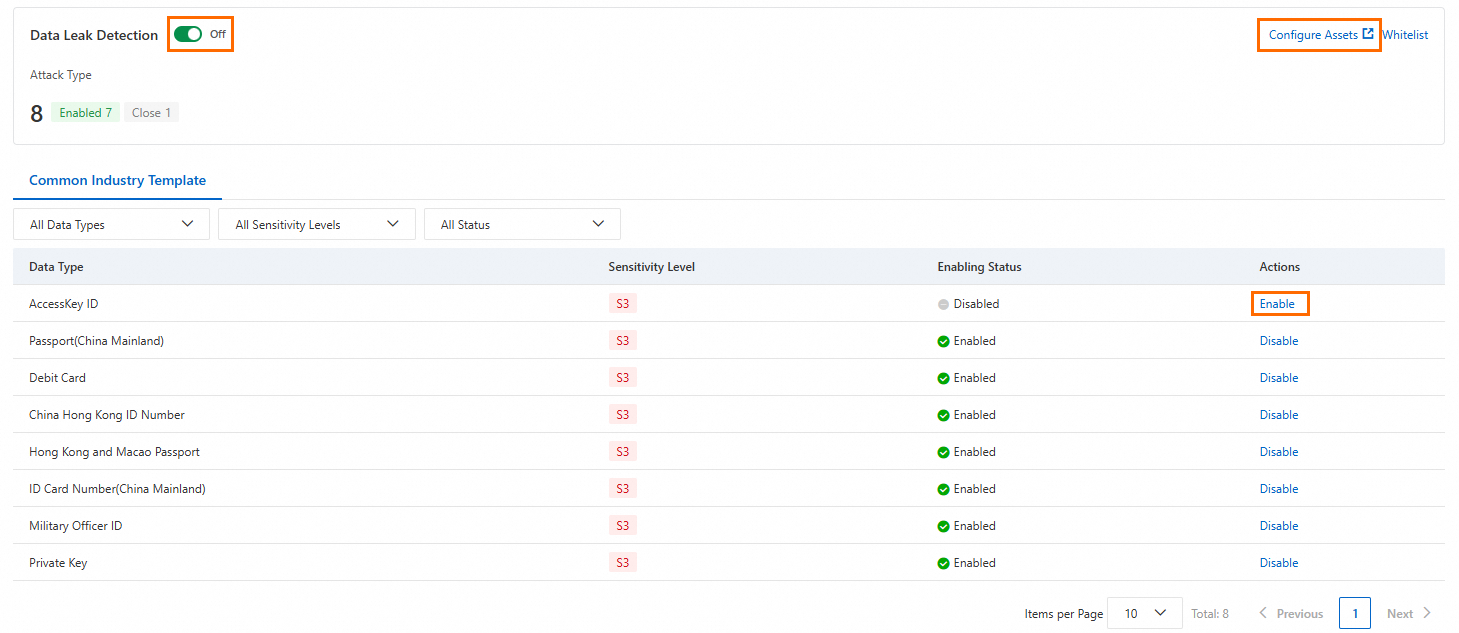
On the Data Leak Detection page, you can view the data leak detection dashboard provided by Cloud Firewall. This helps you better understand asset information, leak events, and risk payloads related to data leaks. For more information, see Data Leak Detection.
IPS Private IP Tracing
In scenarios such as NAT Gateway and Server Load Balancer deployments where the real IP addresses of service instances are not exposed, identifying the specific service instance under attack—such as an ECS instance or server—is challenging. The IPS Private IP Tracing feature automatically correlates session logs of NAT gateways and displays the corresponding private IP address. This supports attack attribution and helps you quickly locate risky assets.
This feature currently supports only public assets of the NAT Gateway type.
Enabling IPS Private IP Tracing incurs no additional charges for Cloud Firewall itself. However, the system creates an index for your session logs of NAT gateways and performs queries, which generates fees. For details about Simple Log Service (SLS) billing, see SLS billing standards.
When IPS Private IP Tracing is enabled, if the system detects that the index for the session logs of NAT gateways is not enabled or is missing required fields, it automatically recreates the index or adds the missing fields.
On the IPS Private IP Tracing page, you can view a list of public assets that support tracing. For each NAT Gateway, you must first enable Internet Firewall Status and Session Log for NAT Gateway before Cloud Firewall can perform IPS private IP tracing. When you click the switch in the Actions column, a prompt appears. Click the link and follow the instructions to enable the features. Alternatively, refer to the following configuration documents:
Enable Internet Firewall Protection: Enable the firewall
Enable NAT Session Log: NAT session log configuration flow
NoteYou do not need to enable NAT session logs if you use only DNAT.
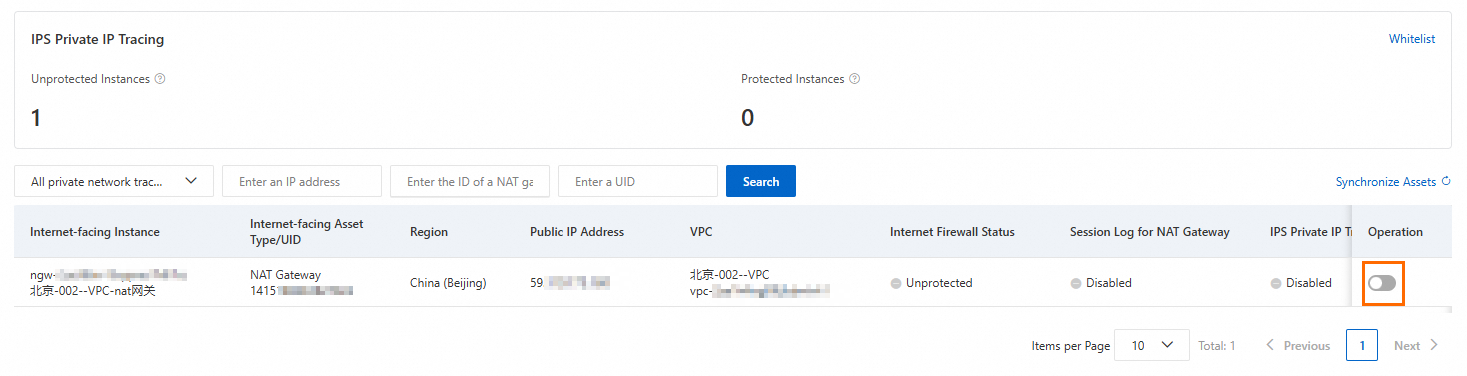
After both Internet Firewall Protection and NAT Session Log are enabled, click OK to enable IPS Private IP Tracing. When the IPS Private IP Tracing shows Enabled, the tracing feature is active for this public asset.
NoteThe IPS Private IP Tracing feature of Cloud Firewall works with the NAT Gateway session log feature. Because of data latency in capturing and delivering NAT Gateway logs, querying private IP tracing results may be delayed by approximately 20 minutes.
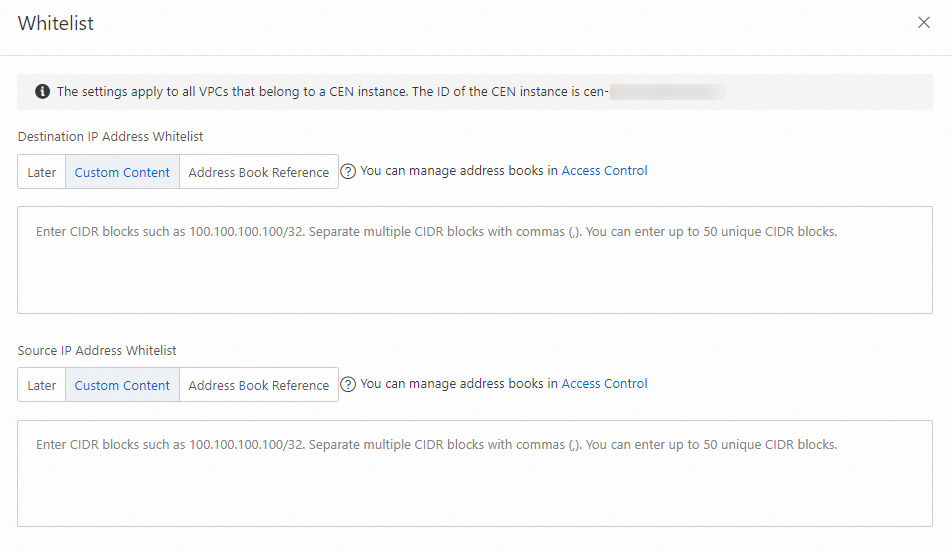
Protection whitelist
To allow trusted bidirectional inbound and outbound traffic for specific IPv4 and IPv6 destination or source IP addresses, add them to the protection whitelist. Traffic from IP addresses in the protection whitelist bypasses basic protection, intelligent defense, and virtual patching rules. You can add up to 50 IP addresses to the custom destination IP whitelist and up to 50 IP addresses to the custom source IP whitelist.
On the right side of the page, click Whitelist to configure it.
The protection whitelist applies only to basic protection, intelligent defense, and virtual patching.
IPS capabilities for the VPC border
You can configure IPS protection for the VPC border only after enabling the VPC firewall.
Configure basic protection policies
Basic protection provides fundamental intrusion prevention, including blocking command execution vulnerabilities and managing the behavior of infected devices connecting to C&C servers. It delivers baseline protection for your assets.
Click .
In the Basic Protection panel, configure the Current Action and Status for the rules.
Modify a protection rule: In the Current Action column, modify the protection rule. The modified rule is marked as a custom rule.
Restore default protection rules: Click Restore All IPS Rules of VPC Firewall, then click OK.
Enable or disable a rule: Click the switch in the Status column.
Enabled: The rule is active. Custom protection rules take precedence over default rules.
Disabled: The rule is inactive.
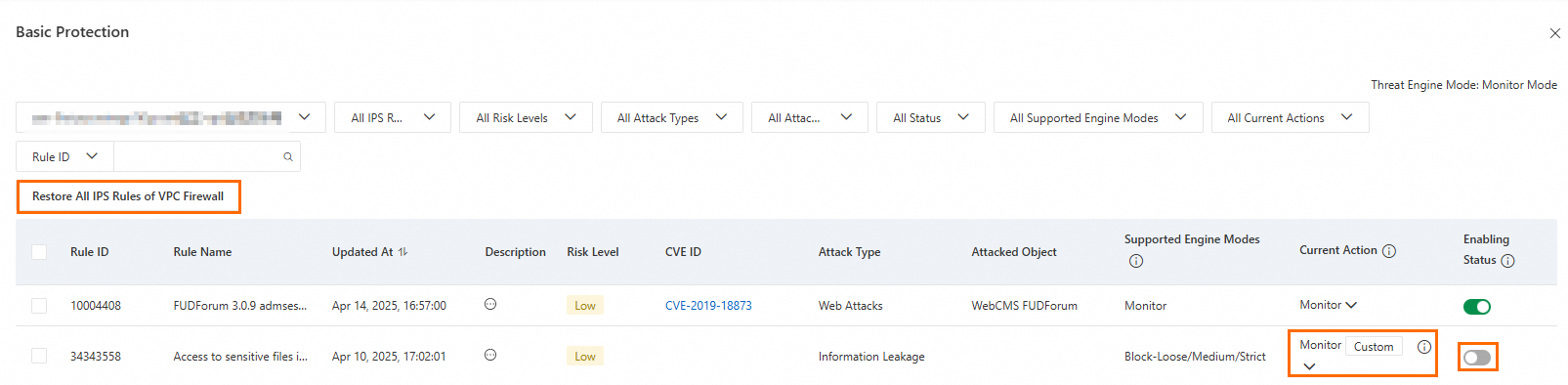
Enabled protection rules apply to all VPC firewalls in your services.
Configure virtual patching rules
Cloud Firewall provides real-time protection against popular important and emergency vulnerabilities. Virtual patching addresses remotely exploitable important and emergency vulnerabilities by applying real-time network-layer patches to block vulnerability-based attacks and prevent business interruptions caused by host-level vulnerability remediation. You do not need to install virtual patches on your servers. However, if virtual patching is disabled, it cannot be updated automatically in real time.
Click View Virtual Patching Policies.
In the Virtual Patching panel, configure the Current Action and Status for the rules.
Modify a protection rule: In the Current Action column, modify the protection rule. The modified rule is marked as a custom rule.
Restore default protection rules: Click Restore All IPS Rules of VPC Firewall, then click OK.
Enable or disable a rule: Click the switch in the Status column.
Enabled: The rule is active. Custom protection rules take precedence over default rules.
Disabled: The rule is inactive.
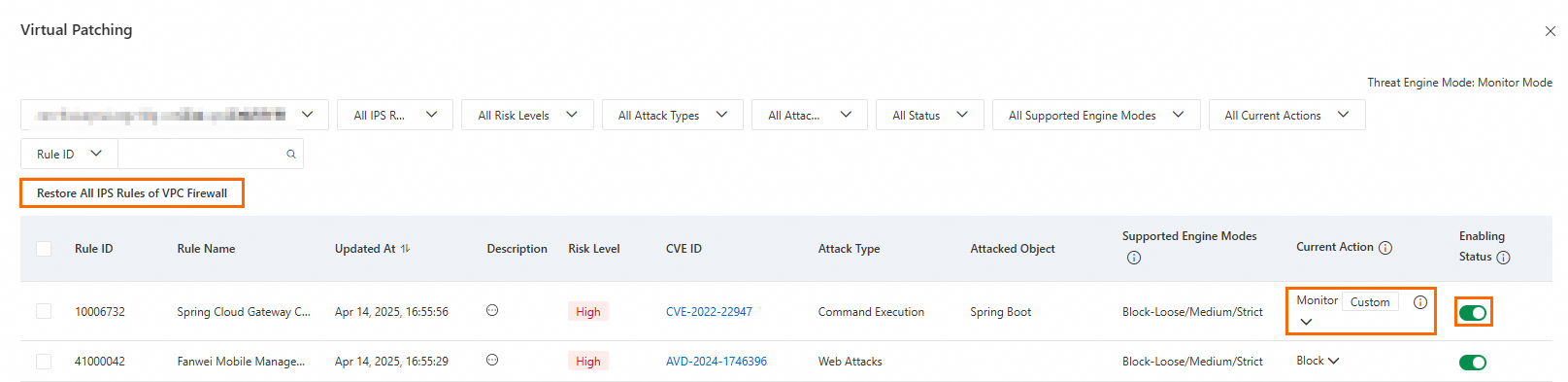
Enabled virtual patching rules apply to all VPC firewalls in your services.
Configure the IPS protection mode
Click Configure IPS Mode.
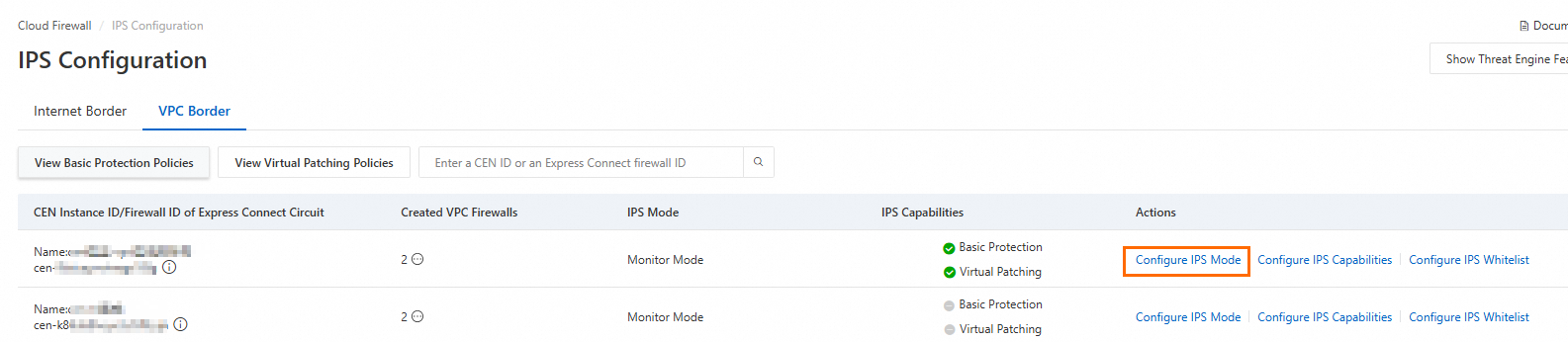
In the Configure IPS Mode dialog box, select a protection mode and click OK.
You can select one of the following two IPS protection modes:
Monitor Mode: Cloud Firewall monitors malicious traffic and generates alerts.
Block Mode: Cloud Firewall blocks malicious traffic to prevent intrusions. You can select a protection level based on your security requirements.
Loose: blocks attacks in a loose manner by using rules that prevent a high rate of false positives. This level is suitable for business that requires the false positive rate to be minimized.
Medium: blocks attacks in a standard manner by using common rules. This level is suitable for daily O&M.
Strict: blocks attacks in a strict manner by using all rules. This level is suitable for business that requires the false negative rate to be minimized, such as major events or cybersecurity protection activities launched by public service sectors. The activities are rehearsals for network attack and defense. This level may cause a higher false positive rate than the Medium level.
Configure IPS mitigation capabilities
You can configure basic protection and virtual patching. After configuration, Cloud Firewall inspects traffic according to the enabled basic protection policies and virtual patching rules.
Locate the target CEN instance ID or Express Connect firewall ID. In the Actions column, click Configure IPS Capabilities to configure the settings.
Configure the IPS whitelist
To allow trusted destination or source IP addresses, add them to the protection whitelist. Traffic from IP addresses in the protection whitelist bypasses basic protection, intelligent defense, and virtual patching rules. You can add up to 50 IP addresses to the custom destination IP whitelist and up to 50 IP addresses to the custom source IP whitelist.
Locate the target CEN instance ID or Express Connect firewall ID. In the Actions column, click Configure IPS Whitelist to configure the settings.
References
After you enable the Basic Protection switch, go to the Intrusion Prevention page to view unusual inbound and outbound traffic from the internet and between VPCs that Cloud Firewall blocks.
After you enable Cloud Firewall, go to the Vulnerability Prevention page to view network-exploitable vulnerabilities automatically detected by Security Center’s vulnerability detection feature and synced to Cloud Firewall. The page also displays Cloud Firewall’s attack prevention capabilities.
After you enable Cloud Firewall, go to the Threat Detection page to view details about intrusion activities detected by the threat detection engine.
FAQ: