Cloud Firewall's built-in intrusion prevention system (IPS) detects and blocks malicious traffic in real time—covering malicious attacks, exploits, brute-force attacks, worms, mining programs, backdoor trojans, and denial-of-service (DoS) attacks—without disrupting your running workloads.
Common network attacks on the cloud
Enterprise cloud environments typically host critical systems accessible from both public and internal networks: development environments, production services, and data platforms. These systems face a range of network threats that can cause data breaches, resource exhaustion, or service outages.
Common attack types include:
Malware: Attackers trick users into downloading viruses, worms, or trojans that infect cloud servers, enabling persistence or lateral movement.
Port scanning and brute-force attacks: Automated tools scan for open ports and attempt to crack credentials. After a successful intrusion, attackers typically deploy backdoors, mining programs, or ransomware.
Web application attacks: SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), and remote code execution (RCE) let attackers steal data, tamper with content, or gain system-level access.
Transport-layer protocol attacks: Vulnerabilities in TCP/UDP stacks can lead to DoS conditions or privilege escalation.
Database attacks: Unauthorized access to or misconfiguration of Redis, MySQL, or similar services results in data theft or injection of malicious instructions.
Command execution and reverse shells: Attackers exploit system or application vulnerabilities to run arbitrary commands or establish outbound reverse-shell connections that bypass perimeter controls.
To counter these threats, deploy a defense-in-depth strategy: enable Cloud Firewall, harden network security configurations, and patch vulnerabilities promptly.
Cloud Firewall IPS capabilities
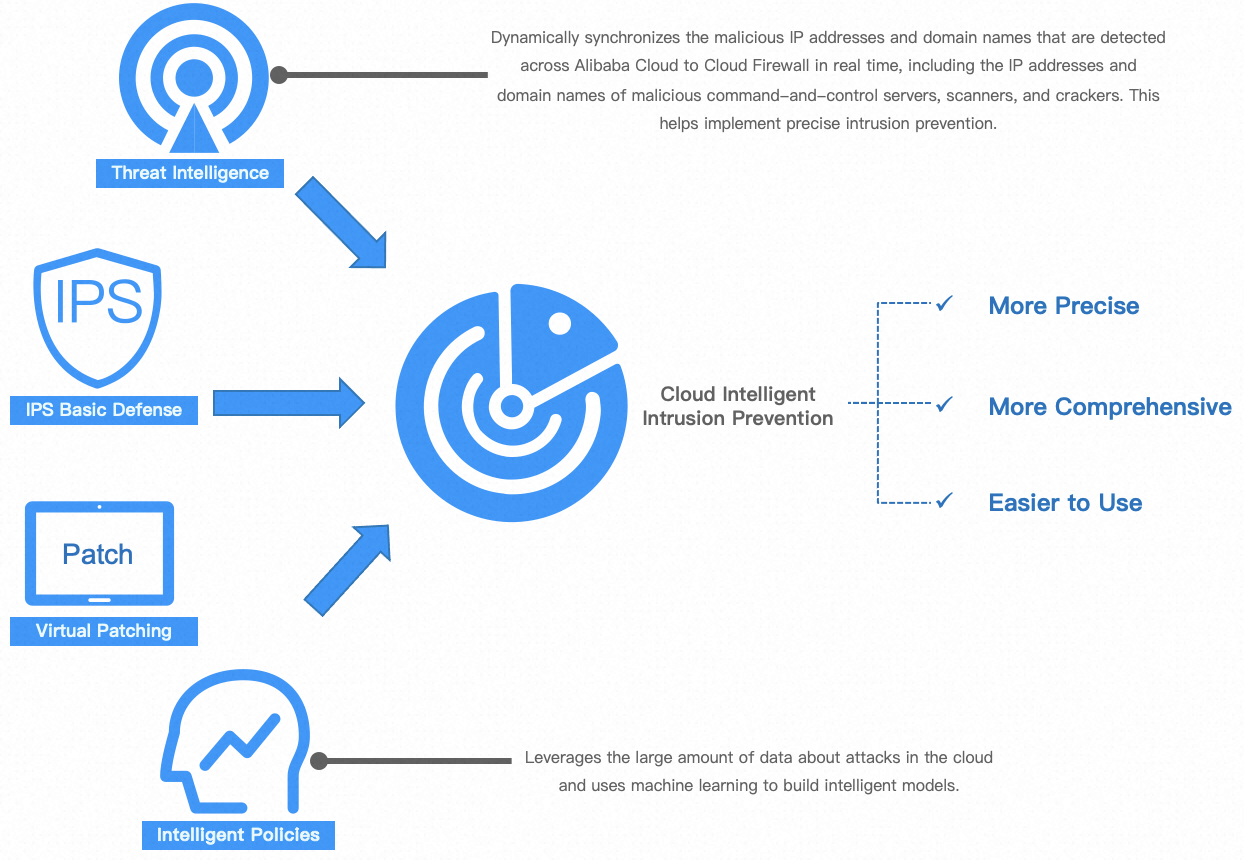
Cloud Firewall integrates an IPS that uses real-time traffic inspection, virtual patching, outbound threat protection, threat intelligence, and machine learning to protect your cloud workloads.
Vulnerability exploit blocking Over 5,000 built-in basic protection policies and virtual patches block known exploits immediately, significantly narrowing the attack window.
Virtual patching For systems with unpatched vulnerabilities, Cloud Firewall delivers mitigation policies within three hours—no system patches to install, no service restarts required. This effectively neutralizes high-risk and 0-day vulnerabilities until a formal patch is available.
Outbound malicious traffic protection Detects and blocks compromised hosts communicating with Command and Control (C&C) servers, outbound mining connections, and abnormal data exfiltration—containing internal threats before they spread or leak sensitive data.
Threat intelligence Synchronized in real time from Alibaba Cloud's global security awareness system, threat intelligence covers malicious IP addresses, malicious domain names, C&C addresses, scan sources, and brute-force sources for dynamic, up-to-date protection.
Intelligent threat identification Machine learning models trained on a large volume of attack samples and behavioral data extend detection to unknown threats and emerging attack patterns.
Together, these capabilities give your cloud workloads proactive, continuous, automated protection at both the network and application layers.
Cloud Firewall's IPS supports TLS inspection to decrypt and inspect encrypted outbound traffic at the Internet border. For inbound traffic protection, use Web Application Firewall.
Threat intelligence capabilities
Alibaba Cloud generates threat intelligence through multi-dimensional data fusion and intelligent analysis to ensure high-confidence, actionable results.
Data sources
Cloud-wide attack events: Sensors deployed in the public cloud and partner networks capture attack traffic and samples in real time.
Anonymized security traffic logs: Attack patterns and malicious connections are extracted from analysis of anonymized network traffic.
Global open-source threat intelligence: Open Source Intelligence (OSINT) from authoritative industry organizations and security communities is integrated and verified.
Partner intelligence sharing: Trusted data is exchanged with carriers, cloud vendors, and security organizations.
Production methods and identification standards
Multi-dimensional association analysis IP addresses, domain names, URLs, file hash values, and attack techniques are correlated to build a complete threat graph and reduce false positives.
Intelligent analysis engine
Big data and machine learning models: Behavior analysis and anomaly detection models automatically identify suspicious malicious patterns and emerging threat families from large-scale data.
Expert rule system: Precise detection rules refined by security experts deliver fast and accurate matching of known threat types.
Dynamic reputation scoring: A dynamic reputation score is calculated for each threat indicator based on activity history, distribution range, threat type, and confidence level.
Manual review For high-value or complex threat scenarios, a professional security analysis team performs a final review to confirm accuracy and reliability.
Core threat intelligence categories
Alibaba Cloud threat intelligence covers three categories: IP threat intelligence, domain name threat intelligence, and URL threat intelligence. IP threat intelligence is further divided into outbound and inbound based on traffic direction.
Outbound IP threat intelligence
Matching object: Destination IP addresses that internal hosts actively connect to.
Core value: Detects whether internal hosts are compromised (for example, infected with trojans or part of a botnet) or are engaging in unauthorized outbound activity such as mining or C&C communication.
| Type | What it means when triggered |
|---|---|
| Tor node | An internal host is connecting to a known Tor exit, entry, or relay node—likely attempting anonymous communication to hide malicious activity such as data theft or command and control. |
| Mining | An internal host is communicating with cryptocurrency mining infrastructure—a sign the system may be implanted with a mining program consuming compute resources. |
| C&C | An internal host is reaching a C&C server associated with botnets, remote access trojans, or ransomware—indicating the host may be under attacker control. |
| APT | An internal host is connecting to infrastructure owned or used by an advanced persistent threat (APT) group—likely indicating a targeted, organized attack. |
| Reverse shell | An internal host is establishing an outbound connection to an IP historically observed receiving reverse shells—an attempt to create a remote control channel that bypasses the firewall. |
| Phishing | An internal host has connected to a phishing backend server—a user may have clicked a phishing link. |
| Malicious download source | An internal host is contacting a server used to distribute malware such as viruses, trojans, or spyware—a malicious payload may be downloading or updating. |
Inbound IP threat intelligence
Matching object: Source IP addresses from external networks actively accessing internal assets.
Core value: Real-time detection of external attacks targeting the network perimeter, servers, and application systems.
| Type | What it means when triggered |
|---|---|
| Scanning | The source IP is performing reconnaissance such as port scanning, service probing, or network mapping—a typical preparatory step before an attack. |
| Brute-force attack | The source IP is launching many login attempts against SSH, RDP, FTP, databases, or web portals. |
| Exploit | The source IP is sending attack payloads targeting known vulnerabilities such as Apache Log4j2 or EternalBlue. |
| SQL injection | The source IP is injecting malicious SQL code into web application parameters in an attempt to manipulate the database. |
| Code execution | The source IP is attempting to remotely execute system commands by exploiting web application or service vulnerabilities. |
| Webshell | The source IP is attempting to upload webshell files or communicate with known webshell backdoors. |
| XSS attack | The source IP is injecting malicious scripts into web pages via cross-site scripting. |
Domain name threat intelligence
Matching object: Domain names that internal hosts resolve or access.
Core value: Attackers frequently use dynamic domain names to rotate IP addresses and evade IP-based blocking. Domain name intelligence provides more persistent detection of access to malicious infrastructure.
| Type | What it means when triggered |
|---|---|
| DNS log platform domain | An internal host has resolved a DNS log platform domain (often used to detect injection or exfiltration)—a sign that a vulnerability such as blind injection or RCE may have been exploited, causing unintentional DNS resolution leaks. |
| Dark web proxy | An internal host is accessing a proxy domain that provides entry to the dark web (such as a Tor2web service)—often the starting point for dark web activity. |
| Blackhole domain | An internal host has attempted to resolve a domain flagged as malicious and sinkholed by security vendors or carriers—indicating potential malware or a configuration error. |
| Mining | An internal host is connecting to a miner pool domain or update server used by mining scripts or trojans. |
| C&C | An internal host is resolving a domain associated with malware families that use domain-based C&C to avoid static IP blocking. |
| APT | An internal host is accessing a domain registered and used by an APT group for long-term campaign infrastructure. |
| Phishing | An internal host is accessing a phishing domain impersonating a legitimate organization such as a bank or social platform. |
| Malicious download source | An internal host is resolving a domain used to distribute malware, often concealed by URL shortening or CDN services. |
URL threat intelligence
Matching object: Full URLs that internal hosts access.
Core value: Provides precise identification of specific malicious pages hosted on legitimate cloud services or shared IP addresses, where IP- or domain-level intelligence alone is insufficient.
| Type | What it means when triggered |
|---|---|
| Mining | An internal host is accessing a page with an embedded web mining script (such as a Coinhive-style script) or a miner pool management interface. |
| C&C | An internal host is communicating with a specific URL path serving as a control panel or data exchange interface for a trojan or botnet. |
| APT | An internal host is accessing a URL used in APT campaign activity, such as a download link for a weaponized document or an exploit page. |
| Phishing | An internal host is accessing a phishing page designed to steal account credentials or payment information. |
| Malicious download source | An internal host is downloading directly from a link pointing to a malicious executable (.exe, .dll), script, or document. |
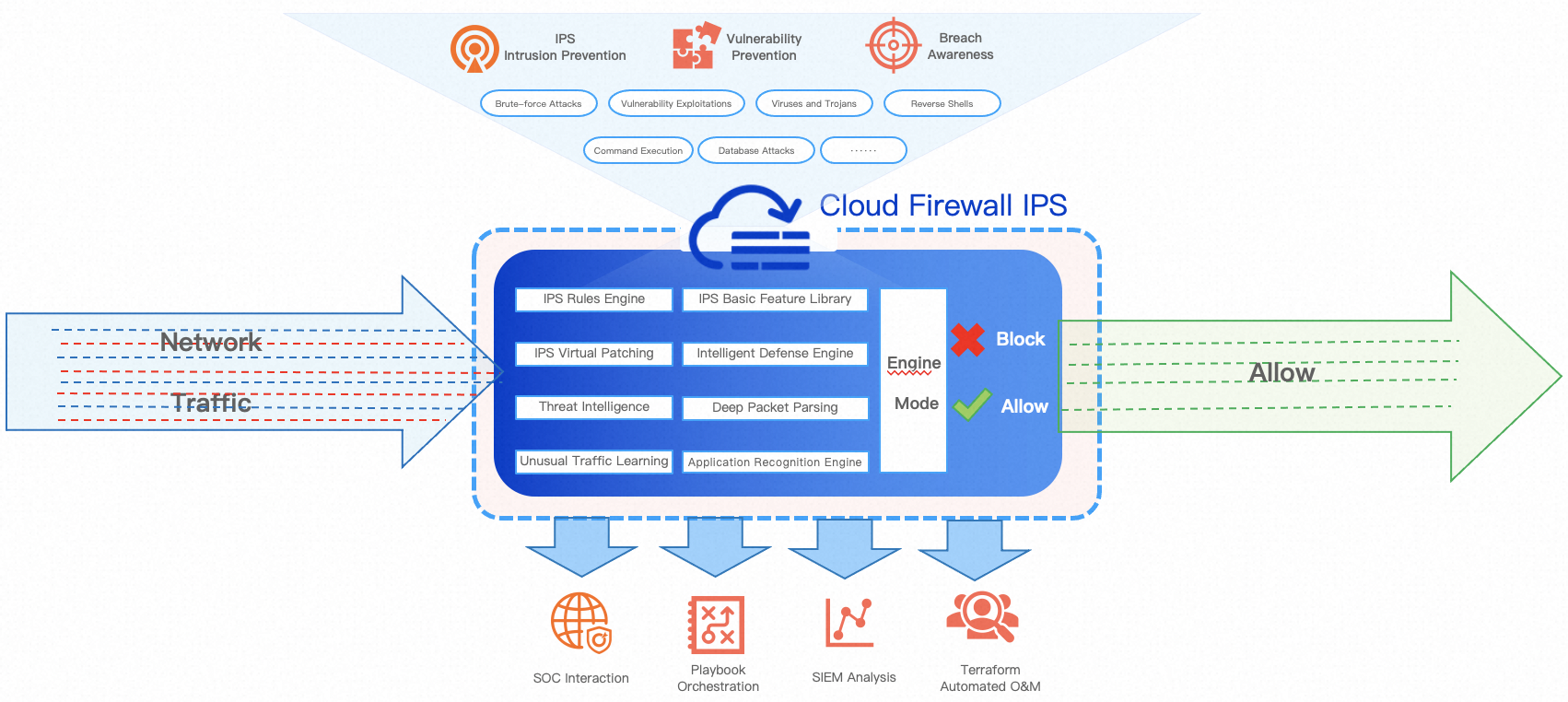
How Cloud Firewall IPS protection works
Cloud Firewall is deployed inline on cloud network links, covering inbound and outbound Internet traffic, NAT borders, cross-VPC traffic, and connections between the cloud and on-premises data centers.

All traffic passing through Cloud Firewall is filtered by both the IPS engine and the Access Control List (ACL) engine before forwarding.
Cloud Firewall uses a Deep Packet Inspection (DPI) engine to identify protocols and parse packets. For IPS and threat intelligence handling, it performs stream and packet filtering. When traffic matches a configured threat engine mode (Monitor Mode, Block Mode - Loose, Block Mode - Medium, or Block Mode - Strict) and an IPS rule action, the matching packet is dropped or allowed, providing real-time alerting and blocking.
Attack types and protection recommendations
For instructions on configuring the IPS threat engine mode, see IPS Configuration.
| Attack type | Risk | Protection recommendation |
|---|---|---|
| Abnormal connection | Exposed database ports or services with weak credentials can lead to data loss or breaches—unauthorized Redis access is a common example. | If your business runs non-web applications (such as MySQL or SQL Server) and exposes ports other than 80, 443, or 8080, monitor rules for non-web attacks such as Shellcode and sensitive command execution. If your business does not run such applications, use Block Mode - Strict. |
| Command execution | Arbitrary command execution lets attackers take control of a machine, steal data, or pivot to other systems. The Log4j vulnerability is a well-known example. | Block Mode - Loose covers most common and uncommon remote command execution attacks on web applications and meets daily protection needs. However, because remote command execution attacks are among the most harmful, monitor rule hits across various components in Block Mode - Medium. For complex environments with many non-web applications, use Block Mode - Strict. |
| Scan | Network scanning can overload machines or devices, causing interruptions or instability. | If your business does not require SMB named pipes, disable the feature to reduce exposure. If SMB named pipes are required, use Block Mode - Medium or Block Mode - Strict. |
| Information leak | Exposed personally identifiable information, contact details, and financial data can be exploited maliciously. | Start with Monitor Mode for one business cycle (24 hours to one week). If no legitimate traffic is incorrectly flagged, switch to Block Mode - Medium or Block Mode - Strict. |
| DoS attack | Denial-of-service attacks overload servers and devices, causing interruptions or crashes. | Monitor for unexplained outages. If none occur, Block Mode - Loose is sufficient. For workloads with high Service-Level Agreement (SLA) requirements, use Block Mode - Medium or Block Mode - Strict. |
| Overflow attack | Overflow attacks exploit insufficient input validation in binaries, causing memory errors that can lead to command execution or information leaks. | If your business is primarily web-based, Block Mode - Loose is sufficient. For environments with many non-web applications, use Block Mode - Medium or Block Mode - Strict. |
| Web attack | Web attacks can give attackers control of a machine, expose sensitive data, and disrupt business. Common vectors include SQL injection, XSS, and arbitrary file uploads (OWASP Top 10). | Test rules during both canary and official release phases. For daily operations, use Block Mode - Medium or Block Mode - Strict. |
| Backdoor trojan | Backdoor trojans provide persistent access even after vulnerabilities are patched, enabling long-term surveillance and data theft. Trojan communications frequently use encryption, obfuscation, and encoding as evasion techniques. | For daily operations, use Block Mode - Medium or Block Mode - Strict. Pay close attention to detection in Strict mode due to weak-feature matching. |
| Virus and worm | Viruses and worms provide persistent access and enable long-term data theft, with similar legal and reputational risks to backdoor trojans. | If a rule triggers in Monitor Mode, perform traceability analysis to identify the attack source and take action. Use Block Mode - Medium. |
| Mining behavior | Mining malware consumes bandwidth and compute resources, degrading performance and user experience. | If a rule triggers in Monitor Mode, perform traceability analysis to identify the attack source and take action. Use Block Mode - Medium. |
| Reverse shell | Reverse shells provide persistent remote access that survives patching, enabling long-term surveillance and data theft. | If a rule triggers in Monitor Mode, perform traceability analysis to identify the attack source and take action. Use Block Mode - Medium. |
| Other | Includes unauthorized outbound connections and attacks that do not fit other categories. | If your business has minimal outbound activity, Block Mode - Loose is sufficient. For hosts with many browsers and applications where outbound communication is uncontrolled, use Block Mode - Strict. |
IPS protection modes
The threat engine operates in Monitor Mode and Block Mode. The action taken when a basic protection rule or virtual patching rule is matched depends on the configured mode.
| Mode | When to use | How it works | Example CVEs |
|---|---|---|---|
| Monitor Mode | Your business cannot tolerate any risk of blocking legitimate traffic, or you are evaluating which rules apply before enforcing a block mode. | Records and generates alerts for matched attack behaviors. Does not block traffic. | Apache Tomcat chunk request remote DoS (CVE-2014-0075), Atlassian Jira SSRF attack (CVE-2019-16097), Godlua backdoor software communication. |
| Block Mode - Loose | Your business is sensitive to false positives and needs a conservative starting point. | Blocks only rules with a low false positive rate—clear exploit keywords, obvious attack patterns, minimal risk of incorrectly blocking legitimate traffic. | Struts 2 remote code execution (CVE-2018-11776), Spark REST API unauthorized access (CVE-2018-11770), Jenkins remote command execution (CVE-2018-1000861). |
| Block Mode - Medium | Standard daily operations and maintenance. Suitable for most production environments. | Covers each attack type using multiple exploit analysis methods. Standard rules with an extremely low false positive rate. | Oracle WebLogic Server remote code execution (CVE-2020-2551), Microsoft Windows RDP Client remote code execution (CVE-2020-1374), SMBv1 DoS attack (CVE-2020-1301). |
| Block Mode - Strict | Your security posture requires a low false negative rate and you can tolerate some risk of blocking legitimate traffic. | Covers nearly all rules, including high-risk vulnerabilities such as stack overflow and buffer overflow. Most require protocol analysis, keyword matching, multi-step jumps, and keyword offsets—this may result in a higher false positive rate than Medium mode. | Squid Proxy HTTP Request Processing buffer overflow (CVE-2020-8450), Nginx 0-Length Headers Leak DoS (CVE-2019-9516), Oracle WebLogic rda_tfa_ref_date command injection (CVE-2018-2615). |