When a server is compromised, Cloud Firewall Breach Detection identifies intrusion events so you can investigate and respond before they cause business losses. Use this page to review security threats by risk level, analyze event details with AI-assisted tools, and enable blocking to prevent further damage.
Prerequisites
Before you begin, make sure that:
The Internet firewall is enabled. For more information, see Enable the firewall switch.
Block Mode is enabled for the threat engine. For more information, see IPS Configuration.
Open the Breach Detection page
Log in to the Cloud Firewall console.
In the navigation pane, choose Detection and Response > Breach Detection.
On the Breach Detection page, you can perform the following operations.
View and filter intrusion events
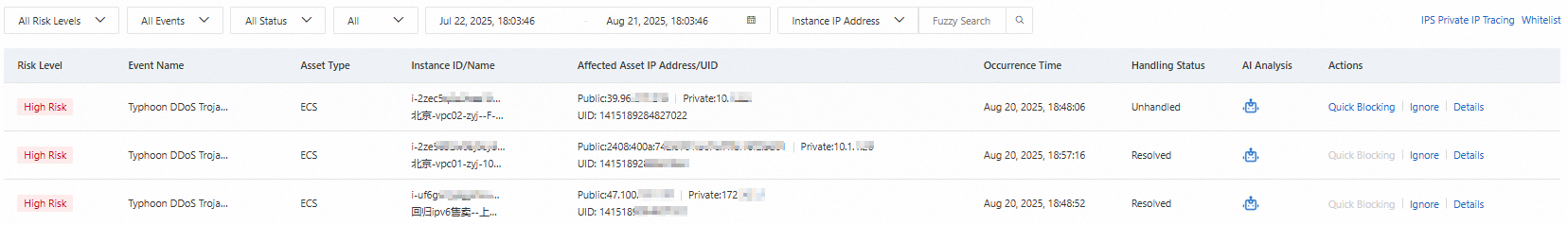
The intrusion event list displays the following columns:
| Column | Description |
|---|---|
| Risk Level | The severity of the intrusion event |
| Event Name | The name of the detected intrusion event |
| Asset Type | The type of the affected asset |
| Instance ID/Name | The ID or name of the affected instance |
| Affected Asset IP Address/UID | The IP address and UID of the affected asset |
| Occurrence Time | The time when the intrusion event occurred |
| Handling Status | The current handling state of the event |
| AI Analysis | AI-assisted analysis entry point |
| Actions | Available operations for the event |
To find a specific event, use the filter options in the menu bar:
All Risk Levels: Filter by risk level.
All Events: Filter by event type.
All Status: Filter by handling status.
Ignored/Not Ignored: Filter by whether the event has been ignored.
You can also perform a fuzzy search by instance IP address, ID, name, or UID.
Analyze events with AI
Click the ![]() icon in the AI Analysis column to analyze breach alerts with the Security AI Assistant. The analysis covers three areas:
icon in the AI Analysis column to analyze breach alerts with the Security AI Assistant. The analysis covers three areas:
| Analysis component | Description |
|---|---|
| Payload content analysis | A brief description of the selected alert and the AI analysis results |
| Attacker intent | The predicted intent of the attacker based on AI analysis |
| Defense recommendations | Suggestions for Cloud Firewall mitigation settings, such as Access Control List (ACL) policies and intrusion prevention system (IPS) configurations, and asset investigation |
View event details
Find the event and click Details in the Actions column to view detailed information about the intrusion event and the corresponding security recommendations.
Ignore an intrusion event
If an intrusion event is normal activity, find the event and click Ignore in the Actions column.
An ignored event is removed from the intrusion event list. Cloud Firewall no longer generates alerts for this event.
Enable Block Mode for the threat engine
After you enable the Internet firewall, Block Mode is enabled for the threat engine by default. If Block Mode is disabled, the Breach Detection page can detect risk events but cannot block them.
To re-enable Block Mode, click Quick Blocking in the Actions column. After you confirm the operation, Cloud Firewall automatically enables the firewall switch, resets IPS rules, and applies the default IPS configuration for the threat engine.
Quick Blocking does not control individual events. Enabling or disabling Quick Blocking toggles the intrusion prevention feature for the entire Cloud Firewall.
References
IPS Configuration -- Set the running mode of the threat engine and configure threat intelligence, basic protection, intelligent defense, and virtual patches to more accurately identify and block intrusion threats. For more information, see IPS Configuration.
Intrusion prevention system (IPS) -- Detect and block malicious traffic in real time, including malicious attacks, vulnerability exploits, brute-force attacks, worms, mining programs, backdoor trojans, and DoS attacks. For more information, see IPS overview and IPS.
Vulnerability Prevention -- Cloud Firewall syncs vulnerabilities detected by Security Center that are exploited by network attacks and provides defense against them. For more information, see Vulnerability Prevention.