You can use the Internet firewall to apply fine-grained controls to traffic between your public assets and the Internet. This helps reduce your Internet attack surface and mitigate security risks. You can enable the Internet firewall with a single click without changing your network topology. Protection takes effect in seconds, providing immediate traffic visualization, attack prevention, access control, and log auditing.
Features
How it works
After you enable the Internet firewall for a public asset, Cloud Firewall filters all inbound and outbound traffic. It uses deep packet inspection (DPI), intrusion prevention (IPS) rules, threat intelligence, virtual patching, and access control policies to determine whether to allow the traffic. This effectively blocks unauthorized access and secures traffic between your public assets and the Internet.
Protected public assets (inbound and outbound): Includes IPv4 and IPv6 assets such as ECS, EIP (including L2 EIP), load balancers, Bastionhost, NAT Gateway, HAVIP, and GA EIP.
The following figure shows an example of a protection scenario for the Internet firewall:

Impact on your services
Creating, enabling, and disabling an Internet firewall does not require changes to your current network topology and does not affect your services. You can enable or disable protection for your resources in seconds with a single click. Enable the Internet firewall during off-peak hours.
Protection specifications
Starting October 15, 2025, Cloud Firewall will release Billing Method 2.0. New customers will use Billing Method 2.0 by default. Existing customers will continue to use Billing Method 1.0. The protection specifications for the Internet firewall differ between the two billing methods.
Billing Method 2.0
Protection specification | Description | Cloud Firewall subscription (Premium, Enterprise, and Ultimate Editions) | Cloud Firewall pay-as-you-go |
Number of firewall instances | The number of regions that can be protected. Each protected region corresponds to one Internet firewall instance. | This depends on the number of instances and the bandwidth you purchase. For the number of instances and bandwidth provided by different editions, see Subscription 2.0. If the quota is insufficient, upgrade the specifications. For more information, see View the protection status of assets. | Billing is based on the actual number of firewall instances and the total processed traffic. The maximum supported peak bandwidth is 10 Gbps. To request a higher specification, contact your business manager or architect. For more information about billing, see Pay-as-you-go 2.0. |
Public traffic processing capacity | The peak of the total internet traffic processed by the firewall. Billing is based on the sum of outbound and inbound internet traffic bandwidth. |
Billing Method 1.0
Protection specification | Description | Cloud Firewall subscription (Premium, Enterprise, and Ultimate Editions) | Cloud Firewall pay-as-you-go |
Number of protectable public IP addresses | The number of public IP addresses for which you can enable the Internet firewall. | This depends on the number of protectable public IP addresses you purchase and the peak of the total processable traffic. If the quota is insufficient, you can upgrade the specifications. Different Cloud Firewall editions have different public IP address quotas. For more information, see Subscription 1.0. Note If your service traffic exceeds the purchased Cloud Firewall traffic processing specifications, the product Service Level Agreement (SLA) cannot be guaranteed. This may trigger downgrade rules, such as the failure of security features (ACL, IPS, and log auditing), disabling the firewall for top assets that exceed the quota, rate limiting, and packet loss. If your service traffic is at risk of exceeding the quota, see Post-paid elastic bandwidth for subscription instances. | Billing is based on the actual number of public IP addresses with protection enabled and the peak of the total processed traffic. There is no quota limit. For more information about billing, see Pay-as-you-go 1.0. |
Public traffic processing capacity | The peak of the total processed internet traffic. Billing is based on the higher value between the outbound and inbound internet traffic bandwidth. |

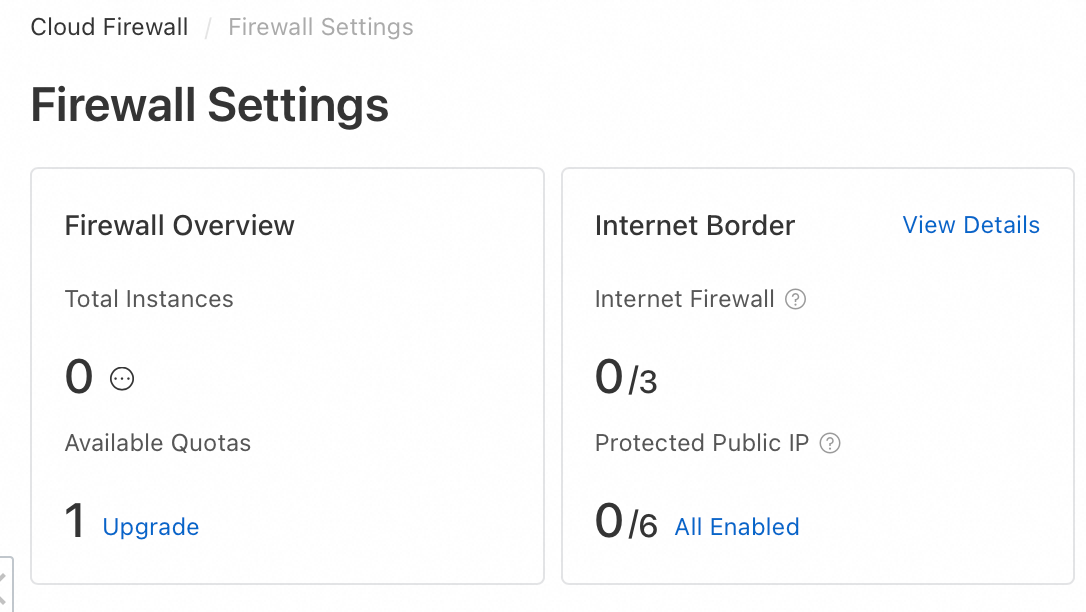
Asset protection status
Enable the Internet firewall
Enable protection for assets manually
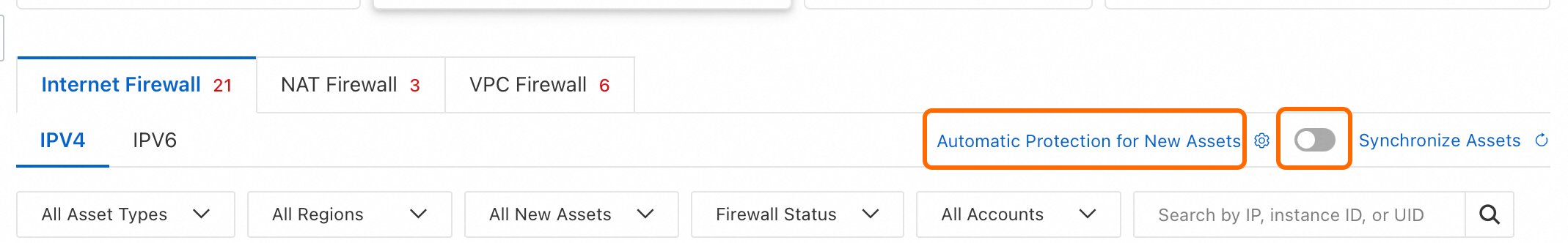
If Automatic Protection for New Assets is not enabled, you can manually enable Internet firewall protection for public assets.
Log on to the Cloud Firewall console.
In the left navigation pane, click Firewall.
On the Internet Firewall tab, click the IPv4 or IPv6 tab to manually enable protection for public assets.
If the asset you want to protect is not in the public asset list, click Synchronize Assets in the upper-right corner of the list. This synchronizes asset information from your current Alibaba Cloud account and its member accounts. Asset synchronization takes about 1 to 2 minutes.
Enable protection for a single asset: Find the public asset you want to protect in the list and click Enable Protection in the Actions column.
Enable protection for multiple assets: Select multiple public assets in the list and click Enable Protection below the list.
Enable automatic protection for new assets
After you enable Automatic Protection for New Assets, Cloud Firewall automatically enables Internet firewall protection for any new public assets added to your current Alibaba Cloud account and its member accounts.
Log on to the Cloud Firewall console.
In the left navigation pane, click Firewall.
Enable Automatic Protection for New Assets: On the Internet Firewall tab, turn on the switch to the right of Automatic Protection for New Assets.
Select asset types for automatic protection: Click Automatic Protection for New Assets. In the dialog box that appears, select the new assets to be automatically protected by asset type and region. Then, click Save.
Next steps
After you enable the Internet firewall, you can configure access control policies and view access logs for public assets to better manage traffic between your public assets and the Internet.
Configure access control policies
If you have not configured any access control policies, Cloud Firewall allows traffic by default. You can create access control policies for the Internet firewall to apply fine-grained control over traffic between your public assets and the Internet.
On the page, locate the target asset. In the Actions column, click Configure Policy and configure either an outbound or inbound access control policy for the public asset. For more information, see Configure access control policies for the Internet firewall.
Query audit logs
On the page, on the tab, set filter conditions to view access logs for traffic between your public assets and the Internet. For more information, see Log auditing.
View traffic analysis
On the page, view traffic data for assets that actively access the Internet. This includes outbound abnormal traffic tracing, destination Internet addresses, and outbound connections from public and private assets. This information helps you identify suspicious assets and ensure service security. For more information, see Outbound connections.
On the page, view data about Internet access to your service assets. This includes inbound abnormal traffic tracing, open public IP addresses, open ports, open applications, and the number of public IP addresses for cloud products. This information helps you identify suspicious assets and ensure service security. For more information, see Internet exposure.
View attack prevention data
On the page, locate the target asset. In the Actions column, click View Attacks and choose to view attack prevention data for outbound or inbound traffic of the public asset. For more information, see Intrusion prevention.
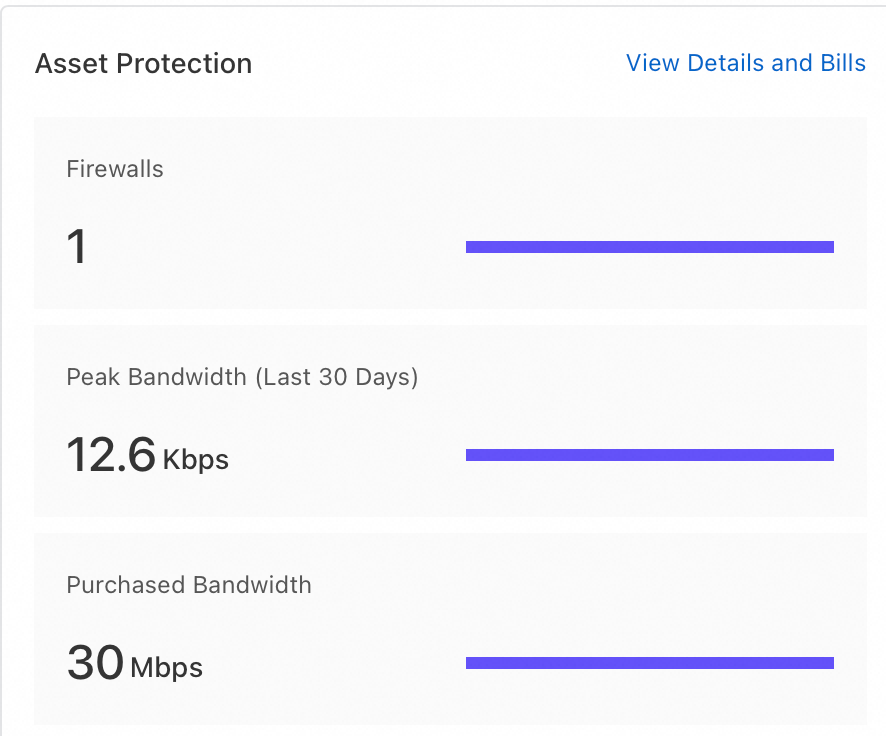
View public traffic processing status
In the left navigation pane, click Overview. Then, on the Overview page in the Asset Protection area, view the number of firewall instances, purchased traffic, and recent peak bandwidth.