If you need to control traffic between your assets and specific geographic regions, you can configure an access control policy for the Internet firewall and specify the source or destination type as a region. For example, you can allow access only from a specific region or block access from another. This topic demonstrates how to configure a policy that blocks all traffic from international regions for a business that serves users only in Chinese mainland.
Scenario
In the scenario shown in the following figure, you have an ECS instance with the EIP 47.100.XX.XX. Because your business serves users only in Chinese mainland, you need to configure a policy to block all traffic from international regions.
Prerequisites
You have purchased Cloud Firewall and enabled Internet firewall protection. For more information, see Purchase Cloud Firewall and Internet firewall.
Procedure
Log on to the Cloud Firewall console.
In the navigation pane on the left, choose .
On the Inbound tab, click Create Policy. In the Create Inbound Policy panel, click the Create Policy tab and configure the policy with the following parameters.
Parameter
Description
Example value
Source Type
The source of the network traffic. Select a source type and enter its address.
Location
Source
All Geographical Regions Outside China
Destination Type
The destination of the network traffic. Select a destination type and enter its address.
IP
Destination
Enter the public IP address of the ECS instance,
47.100.XX.XX/32.Protocol Type
The transport layer protocol. Valid values are TCP, UDP, ICMP, and ANY. If you are unsure which protocol to use, select ANY.
ANY
Port Type
The type and number of the destination port.
Port
Port
Enter
0/0to apply the policy to all ports.Application
The application type associated with the traffic.
ANY
Action
The action to apply to matching traffic.
Allow: allows the traffic.
Deny: blocks the traffic and does not send a notification.
Monitor: In this mode, traffic is allowed by default. You can filter and observe this traffic using the relevant fields in traffic logs. After a period of observation, you can change the action to Allow or Deny as needed.
Deny
Priority
The priority of the policy. The default is Lowest.
Highest
Policy Validity Period
Set the validity period for the policy. The policy can match traffic only within the validity period.
Always
Status
Specifies whether the policy is enabled upon creation. You can enable disabled policies later from the policy list.
Enable
Next steps
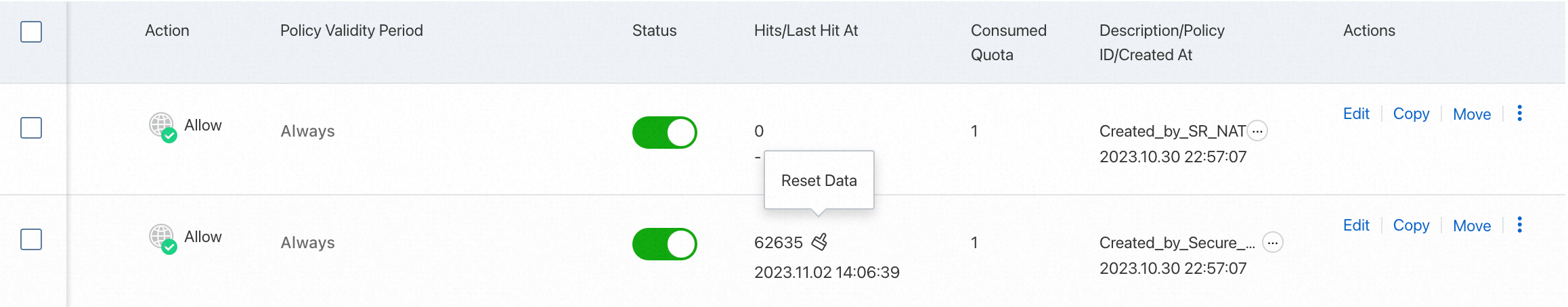
After your service has been running for a period of time, you can view the hit count and last hit time of access control policies in the Hits / Last Hit At column of the access control policy list.
Click the hit count to view the traffic logs on the Traffic Logs page. For more information, see Log audit.
Related documentation
For detailed instructions on how to configure access control policies for the Internet firewall, see Configure Internet firewall access control policies.
For more information about access control policy configuration principles, see Access control policy configuration examples.
For answers to common questions about access control policies, see FAQ about access control policies.