The Outbound Connection page shows the Internet access activity of your service assets — where they connect, how much traffic they generate, and which connections look suspicious. Use this page to spot unusual outbound traffic, investigate at-risk assets, and block access to malicious destinations.
Prerequisites
Before you begin, ensure that you have:
The Internet firewall enabled. For more information, see Internet firewall
How it works
The Outbound Connection page has two main views:
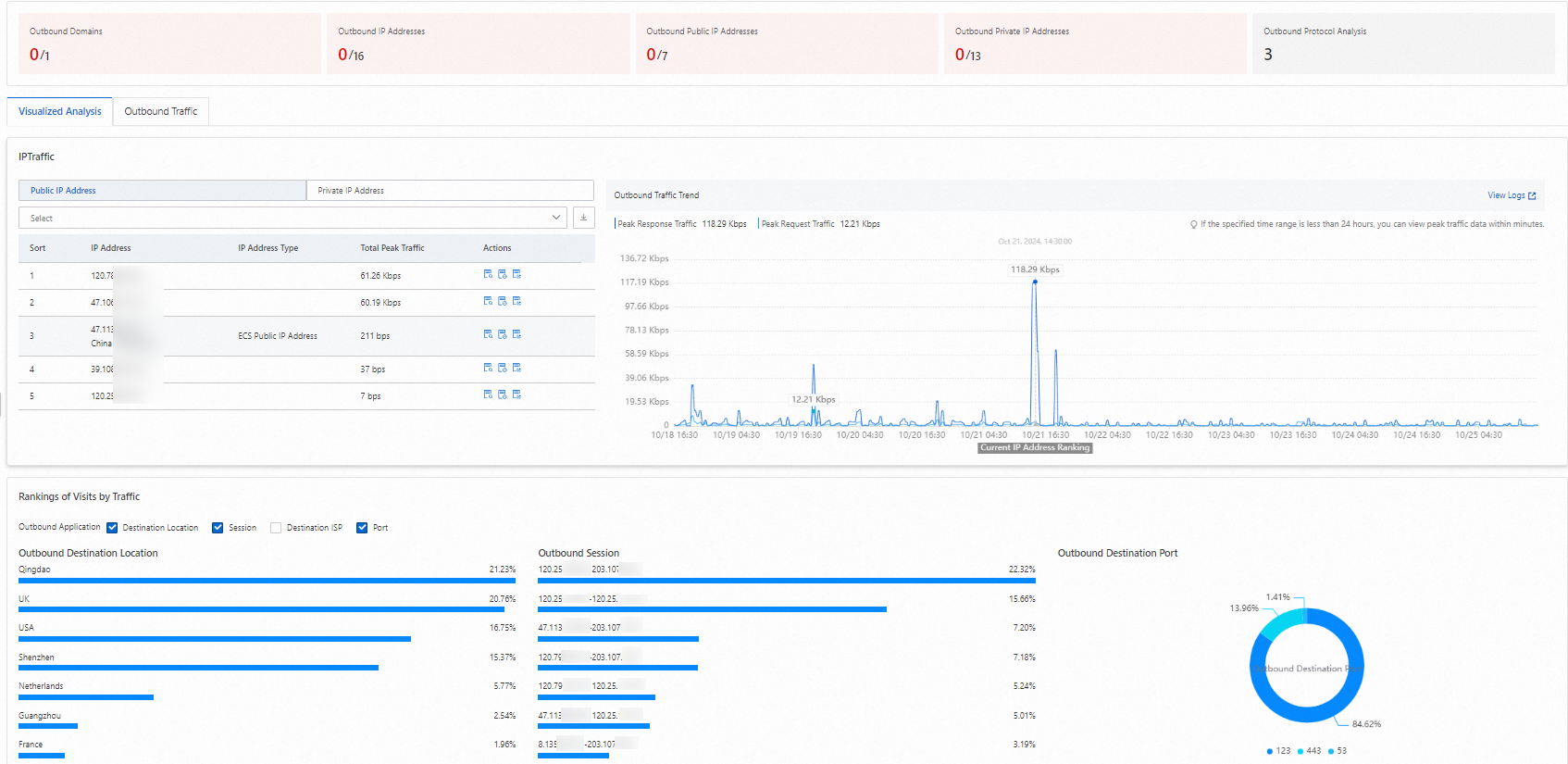
Visualized Analysis — real-time traffic charts showing peak traffic, IP-level trends, and top outbound destinations. Use this view to get an at-a-glance picture of your outbound traffic volume and distribution.
Outbound Traffic — tabular data organized by domain name, destination IP, asset IP, and protocol. Use this view to investigate specific assets or destinations and take action on at-risk entries.
To open the page, log on to the Cloud Firewall console and choose Traffic Analysis > Outbound Connection in the left navigation pane.
Visualized Analysis
The Visualized Analysis tab displays peak traffic, IP-level trend charts, and top outbound traffic statistics in real time.
In the upper-right corner of the Outbound Connection page, select a time range and click Visualized Analysis.
Review the data displayed on the tab.
The tab shows the following data:
| Data | Description | Actions |
|---|---|---|
| IP Traffic | Public IP Address (traffic redirected by the Internet firewall): peak total response traffic for all public IP addresses — such as ECS instance public IPs or NAT elastic IP addresses (EIPs) — sorted by response traffic in descending order. Private IP Address (traffic redirected by NAT firewalls): peak total response traffic for ECS instance private IP addresses. The virtual private clouds (VPCs) where the ECS instances reside must be associated with a NAT Gateway. Results are sorted by response traffic in descending order. | Use the search box to filter by public or private IP address. Click Public IP Address or Private IP Address to switch all charts — IP Traffic Trend, Top IP Traffic, and Top 10 Outbound Traffic — to show data for that asset type. In the Actions column: click View Logs to open Log Audit and view traffic logs for the IP; click View outreach details to open the Outbound Details tab for that IP; click View Trends to display the peak traffic trend for the IP in the chart. Click the  icon to export traffic data for public and private IP addresses. icon to export traffic data for public and private IP addresses. |
| Top 10 Outbound Traffic | Top 10 destination regions, destination carriers, session percentages, and ports for outbound traffic. | None. |
To view Internet firewall traffic logs, click View Logs in the upper-right corner of the list to open the Log Audit page and select the Traffic Logs tab.
View outbound connection data
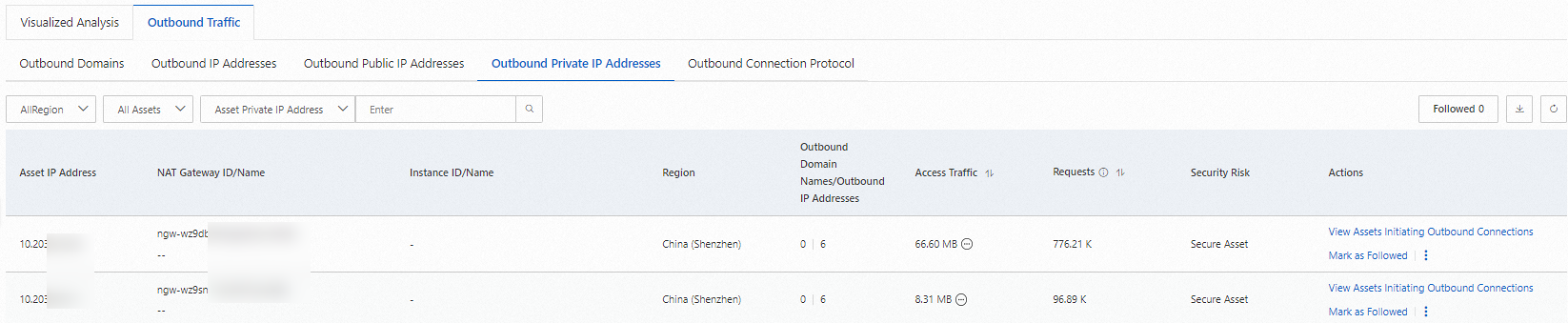
The Outbound Traffic tab organizes outbound data into five sub-tabs — Outbound Domains, Outbound IP Addresses, Outbound Public IP Addresses, Outbound Private IP Addresses, and Outbound Connection Protocol — so you can investigate from whichever angle fits your current task. The statistics area at the top gives you an immediate count of at-risk entries across all categories.
In the upper-right corner of the Outbound Connection page, select a time range.
Review the statistics area and the Outbound Traffic tab.

On the Outbound Traffic tab, specify a custom query to search traffic data within a 7-day range.
The statistics area and the Outbound Traffic tab show the following data:
| Data | Description | Actions |
|---|---|---|
| Outbound Domains | Number of at-risk domain names and total domain names that your assets access on the Internet. | Click the Outbound Domains area to open the Outbound Traffic > Outbound Domains tab. On detected at-risk domain names, you can: click Configure Access Control Policy to set an outbound access control policy on the Internet firewall (see Configure an access control policy for the Internet firewall); click View Intelligence Profile to see threat intelligence data for the domain name; click a domain name to view details — on the Outbound Public IP Addresses and Outbound Private IP Addresses tabs, review the ECS instances that made outbound connections, then click View Logs to see traffic logs; click *.example.com are not supported and still generate alerts if added); click Whitelist in the upper-right corner to open the Whitelist panel and remove entries; click |
| Outbound IP Addresses | Number of at-risk destination IP addresses and total destination IP addresses that your assets access on the Internet. | Click the Outbound IP Addresses area to open the Outbound Traffic > Outbound IP Addresses tab. The same actions apply as for Outbound Domains. |
| Outbound Public IP Addresses | Number of at-risk assets and total assets that initiate outbound connections using public IP addresses such as EIPs. | Click the Outbound Public IP Addresses area to open the Outbound Traffic > Outbound Public IP Addresses tab. Click Mark as Followed to flag an entry; click Followed to unfollow; click View Logs to open traffic logs on the Log Audit page. |
| Outbound Private IP Addresses | Number of at-risk private assets and total private assets that initiate outbound connections through a NAT Gateway. | Click the Outbound Private IP Addresses area to open the Outbound Traffic > Outbound Private IP Addresses tab. The same actions apply as for Outbound Public IP Addresses. |
| Outbound Connection Protocol | Number and percentage of unidentified protocols and all protocols used when your assets access the Internet through application protocols. Supported protocols include HTTPS, HTTP, MQTT, DNS, Redis, MySQL, Zabbix, RTP, SSH, and MongoDB. | Click the Outbound Protocol Analysis area to open the Outbound Traffic > Outbound Connection Protocol tab. Click View Logs to open traffic logs on the Log Audit page. |
View the intelligence profile of an outbound domain name or destination IP address
On the Outbound Domains or Outbound IP Addresses tab, click View Intelligence Profile to see detailed threat intelligence data for a domain name or destination IP address. Use this data to verify whether the intelligence tags assigned to that destination are accurate.
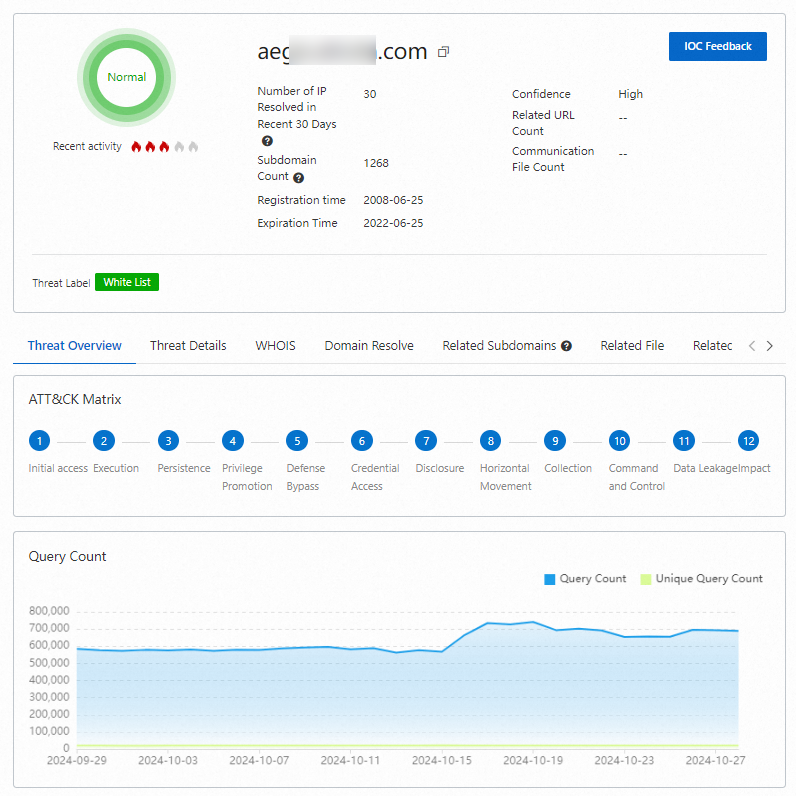
If a tag is inaccurate, click IOC Feedback to report the issue.
Export outbound connection data
On the Outbound Domains tab, click the ![]() icon in the upper-right corner of the list to download outbound data — including domain names, destination IP addresses, public assets, private assets, and connection protocols — in CSV format.
icon in the upper-right corner of the list to download outbound data — including domain names, destination IP addresses, public assets, private assets, and connection protocols — in CSV format.
What's next
To review the billing limits for Protected Internet Traffic, see Subscription 2.0 and Pay-as-you-go 2.0.
To view inbound traffic from the Internet to your assets, see Internet Exposure.
What do I do if my service traffic exceeds the bandwidth supported by Cloud Firewall?
What do the intelligence tags on the Outbound Connection page mean?