By default, Cloud Firewall allows all traffic through the Internet firewall until you create at least one access control policy. Create outbound and inbound policies to control which traffic can flow between your Internet-facing assets and the Internet.
Prerequisites
Before you begin, ensure that:
The Internet firewall is enabled for your Internet-facing assets. For more information, see Enable the Internet firewall. For the full list of asset types that Cloud Firewall can protect, see Protection scope.
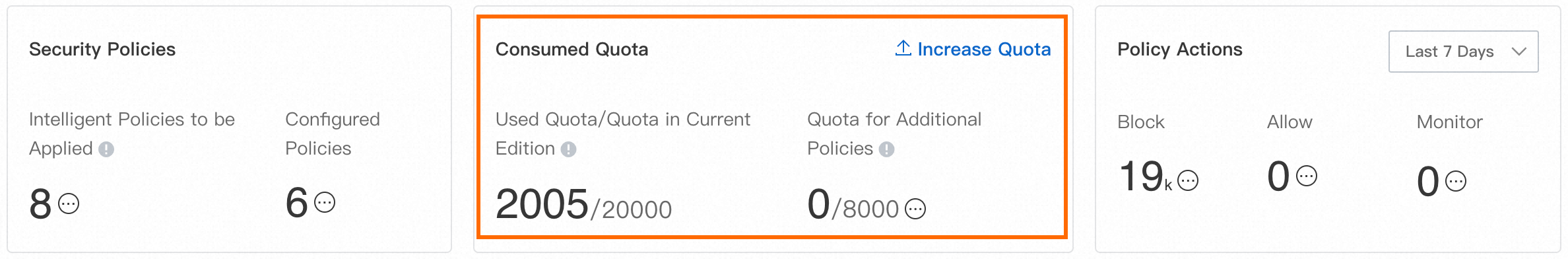
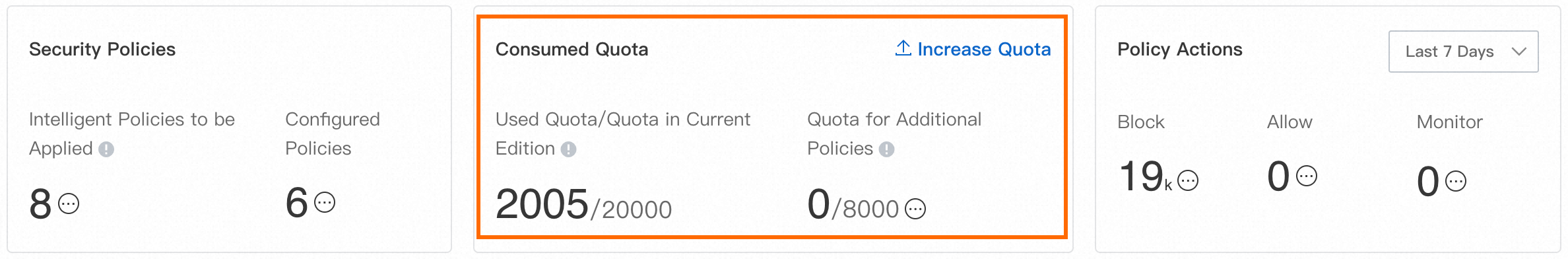
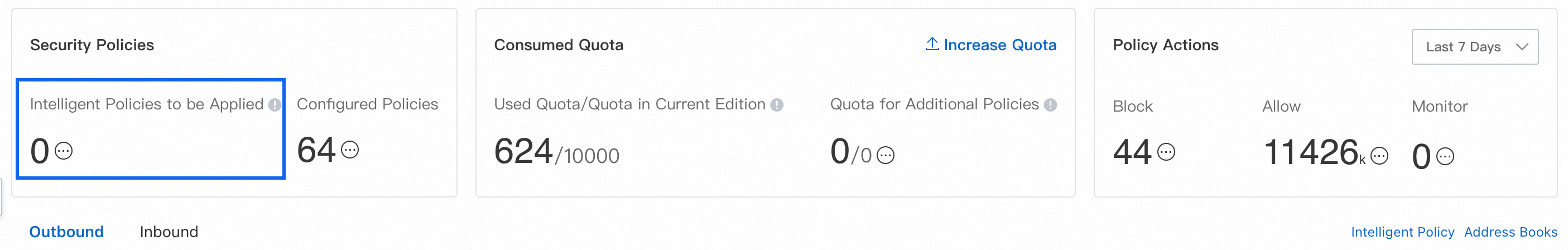
Your policy quota is sufficient. Check current quota usage on the Protection Configuration > Access Control > Internet Border page. For details on quota calculation, see Overview of access control policies. If the remaining quota is insufficient, click Increase Quota to increase the value of Quota for Additional Policy. For more information, see Purchase Cloud Firewall.
If you want to match multiple IP addresses, domain names, or ports as a group, create an address book first. For more information, see Manage address books.
Create a policy
Cloud Firewall offers three ways to create policies:
Create a custom policy: Build a policy from scratch based on your requirements.
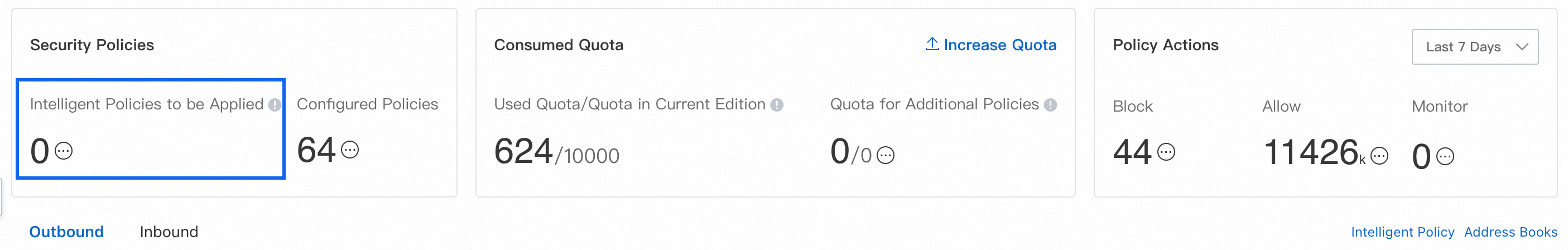
Apply a recommended intelligent policy: Cloud Firewall analyzes traffic from the previous 30 days and recommends policies based on identified risks. Review and apply recommendations that fit your environment.
Apply a recommended common policy: Use pre-built policies for common security scenarios.
Important Allow access only to the ports where your services are actively running on public IP addresses, and deny access to all other ports. This reduces your Internet exposure.
To allow trusted sources and block everything else, create a high-priority Allow policy for the trusted sources first, then create a low-priority Deny policy that matches all sources.
Recommended policies (both intelligent and common) must be explicitly applied — they do not take effect automatically.
Create a custom policy
Custom policies let you define exact match conditions for outbound or inbound traffic.
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Protection Configuration > Access Control > Internet Border.
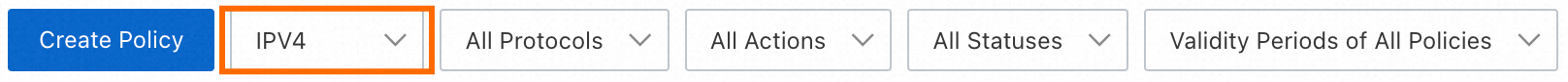
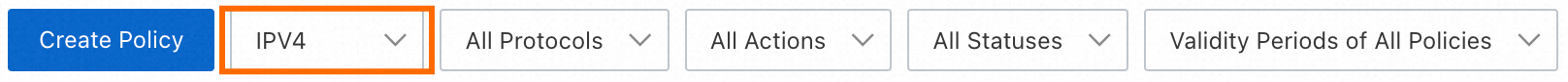
On the Outbound or Inbound tab, select IPV4 or IPV6 from the drop-down list, then click Create Policy. By default, the policy applies to IPv4 addresses.
In the Create Outbound Policy or Create Inbound Policy panel, click the Create Policy tab.
Configure the policy parameters and click OK.
Outbound policy parameters
Outbound policies control traffic from your Internet-facing assets to the Internet.
You can use the following address type combinations for source and destination:
IP address or IP address book (IPv4 or IPv6)
Domain name or domain name address book (outbound destination only)
Region (outbound destination only)
| Parameter | Description |
|---|
| Source type | The initiator of the traffic. Select a type and specify the address accordingly.<br>- IP: Enter CIDR blocks in standard format (for example, 192.168.0.0/16). Separate multiple CIDR blocks with commas. You can enter up to 2,000 CIDR blocks. If you enter multiple CIDR blocks, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing IP address book (IPv4 or IPv6). For more information, see Manage address books. |
| Source | The source IP address or address book. |
| Destination type | The receiver of the traffic. Select a type and specify the address accordingly.<br>- IP: Enter CIDR blocks in standard format (for example, 192.168.0.0/16). Separate multiple CIDR blocks with commas. You can enter up to 2,000 CIDR blocks. If you enter multiple CIDR blocks, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing IP address book (IPv4 or IPv6). For more information, see Manage address books.<br>- Domain Name: Select a domain name resolution mode:<br> - FQDN-based Dynamic Resolution (Extract Host or SNI Field in Packets): Use for HTTP, HTTPS, SMTP, SMTPS, SSL, POPS, and IMAPS traffic.<br> - DNS-based Dynamic Resolution: Use for protocols other than HTTP, HTTPS, SMTP, SMTPS, SSL, POPS, and IMAPS. Does not support wildcard domain names or address books containing wildcard domain names.<br> - FQDN-based And DNS-based Dynamic Resolution: Use for HTTP, HTTPS, SMTP, SMTPS, SSL, POPS, and IMAPS traffic when some or all traffic does not include HOST or SNI fields. Requires strict mode to be enabled for ACL Engine Management. Does not support wildcard domain names or address books containing wildcard domain names.<br>- Region: Select one or more regions inside or outside China where the destination address is located. |
| Purpose | The destination address or address book. |
| Protocol type | The transport-layer protocol. Options: TCP, UDP, ICMP, ANY. Select ANY if you are unsure. |
| Port type | The destination port configuration.<br>- Port: Enter port ranges in port/port format (for example, 22/22 or 80/88). Separate multiple ranges with commas. You can enter up to 2,000 port ranges. If you enter multiple ranges, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing port address book. For more information, see Manage address books. |
| Port | The destination port or address book. |
| Application | The Layer 7 application type. Available options depend on the protocol and destination type.<br>- Protocol type = TCP:<br> - Destination type IP, Address Book (IP), or Region: All application types are available.<br> - Destination type Domain Name or Address Book (domain names):<br>  - FQDN-based Dynamic Resolution: HTTP, HTTPS, SMTP, SMTPS, SSL, POPS, IMAPS only.<br>  - DNS-based Dynamic Resolution: All application types.<br>  - FQDN-based And DNS-based Dynamic Resolution: HTTP, HTTPS, SMTP, SMTPS, SSL, POPS, IMAPS only.<br>- Protocol type = UDP: ANY or DNS only.<br>- Protocol type = ICMP or ANY: ANY only.<br>
Note Cloud Firewall identifies applications based on packet characteristics, not port numbers. If identification fails, the packet is allowed. To block unknown-application traffic, enable strict mode for the Internet firewall. For more information, see Access control engine modes. |
| Action | What happens to matched traffic.<br>- Allow: Allows the traffic.<br>- Deny: Blocks the traffic without sending a notification.<br>- Monitor: Allows the traffic and monitors it. You can filter and monitor the traffic in traffic logs. After monitoring for a period of time, you can change the action to Allow or Deny based on your requirements. |
| Description | A note that helps you identify the policy's purpose later. |
| Priority | When the policy takes effect relative to others. New policies default to Lowest priority and are added to the end of the policy list. A smaller priority number means higher precedence.<br>- Highest: The policy is evaluated first.<br>- Lowest: The policy is evaluated last. |
| Policy validity period | The time window during which the policy is active.<br>- Always: The policy is always active.<br>- Single Time Range: Active once during a specified time range.<br>- Recurrence Cycle: Active during a recurring time window. Specify the time range and days.<br> |
| Status | Whether to enable the policy immediately. If you skip this when creating the policy, enable it later from the policy list. |
Inbound policy parameters
Inbound policies control traffic from the Internet to your Internet-facing assets.
You can use the following address type combinations for source and destination:
Source: IP address, IP address book, or region
Destination: IP address or IP address book
| Parameter | Description |
|---|
| Source type | The initiator of the traffic. Select a type and specify the address accordingly.<br>- IP: Enter CIDR blocks in standard format (for example, 192.168.0.0/16). Separate multiple CIDR blocks with commas. You can enter up to 2,000 CIDR blocks. If you enter multiple CIDR blocks, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing address book. For more information, see Manage address books.<br>- Region: Select one or more regions inside or outside China where the source address is located. |
| Source | The source IP address, address book, or region. |
| Destination type | The receiver of the traffic. Select a type and specify the address accordingly.<br>- IP: Enter CIDR blocks in standard format (for example, 192.168.0.0/16). Separate multiple CIDR blocks with commas. You can enter up to 2,000 CIDR blocks. If you enter multiple CIDR blocks, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing IP address book. For more information, see Manage address books. |
| Destination | The destination IP address or address book. |
| Protocol type | The transport-layer protocol. Options: TCP, UDP, ICMP, ANY. Select ANY if you are unsure. |
| Port type | The destination port configuration.<br>- Port: Enter port ranges in port/port format (for example, 22/22 or 80/88). Separate multiple ranges with commas. You can enter up to 2,000 port ranges. If you enter multiple ranges, Cloud Firewall automatically creates an address book and prompts you to name it when you save the policy.<br>- Address Book: Select an existing port address book. For more information, see Manage address books. |
| Port | The destination port or address book. |
| Application | The Layer 7 application type. Available options depend on the protocol type.<br>- Protocol type = TCP: All application types are available (for example, HTTP, HTTPS, SMTP, SMTPS, SSL, FTP).<br>- Protocol type = UDP: ANY or DNS only.<br>- Protocol type = ICMP or ANY: ANY only.<br>
Note Cloud Firewall identifies applications based on packet characteristics, not port numbers. If identification fails, the packet is allowed. To block unknown-application traffic, enable strict mode for the Internet firewall. For more information, see Access control engine modes. |
| Action | What happens to matched traffic.<br>- Allow: Allows the traffic.<br>- Deny: Blocks the traffic without sending a notification.<br>- Monitor: Allows the traffic and monitors it. You can filter and monitor the traffic in traffic logs. After monitoring for a period of time, you can change the action to Allow or Deny based on your requirements. |
| Description | A note that helps you identify the policy's purpose later. |
| Priority | When the policy takes effect relative to others. New policies default to Lowest priority and are added to the end of the policy list. A smaller priority number means higher precedence.<br>- Highest: The policy is evaluated first.<br>- Lowest: The policy is evaluated last. |
| Policy validity period | The time window during which the policy is active.<br>- Always: The policy is always active.<br>- Single Time Range: Active once during a specified time range.<br>- Recurrence Cycle: Active during a recurring time window. Specify the time range and days.<br> |
| Status | Whether to enable the policy immediately. If you skip this when creating the policy, enable it later from the policy list. |
Apply recommended intelligent policies
Cloud Firewall analyzes your traffic from the previous 30 days and generates intelligent policy recommendations based on identified risks. Both outbound and inbound recommendations may be generated.
Warning Review each recommended policy carefully before applying it. Understand what it does and how it may affect your services.
Ignoring a recommended intelligent policy is permanent — it cannot be restored.
Check whether recommendations are available
Go to the Internet Border page to see whether Cloud Firewall has generated any recommendations.
In the left-side navigation pane, choose Protection Configuration > Access Control > Internet Border.
Open the Recommended Intelligent Policy page using either method:
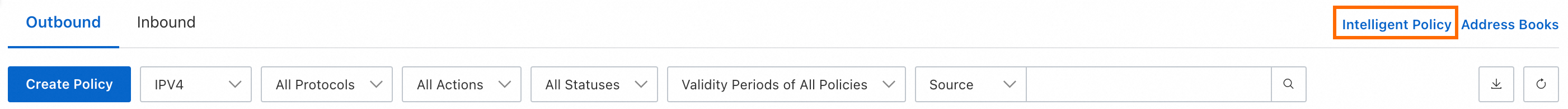
In the upper-right corner above the policy list, click Intelligent Policy. In the panel that opens, click the Outbound or Inbound tab. 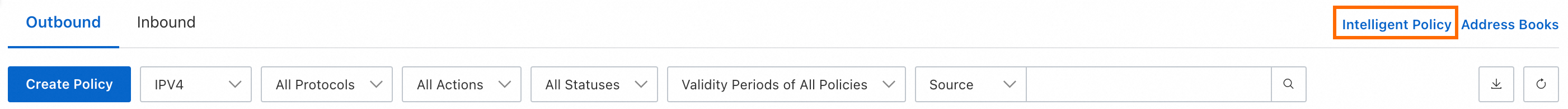
On the Outbound or Inbound tab, click Create Policy. In the panel that opens, click the Recommended Intelligent Policy tab.
Review the recommendations. To apply a single policy, click Apply Policy. To apply multiple policies at once, select them and click Batch Dispatch.
Apply recommended common policies
Cloud Firewall provides pre-built policies for common security scenarios. Apply them if they match your requirements.
Warning Review each recommended policy carefully before applying it. Understand what it does and how it may affect your services.
Ignoring a recommended common policy is permanent — it cannot be restored. If you ignore all common policies, the Recommended Common Policy tab no longer appears.
In the left-side navigation pane, choose Protection Configuration > Access Control > Internet Border.
On the Outbound or Inbound tab, click Create Policy. In the panel that opens, click the Recommended Common Policy tab.
Review the policies. To apply one, click Quick Apply.
Configure the ACL engine mode
The access control list (ACL) engine determines how Cloud Firewall handles traffic whose application type or domain name cannot be identified.
| Mode | Behavior |
|---|
| Loose Mode (default) | Unknown traffic is allowed. Use this mode to avoid unintended disruptions. |
| Strict Mode | Unknown traffic is matched against all configured policies. If a Deny policy matches, the traffic is blocked. Use this mode to enforce stricter control over unidentified traffic. |
To configure the engine mode, go to Protection Configuration > Access Control > Internet Border and click ACL Engine Mode in the upper-right corner of the policy list. You can set the default mode for new assets, change the mode for a single asset, or change the mode for multiple assets at once.


Set the default mode for new assets
In the Access Control Engine Management - Internet Border panel, the Engine Management section shows the mode applied to new assets automatically (listed under Add ACL Engine Mode).
To change it, click Modify.
Change the mode for a single asset
In the Access Control Engine Management - Internet Border panel, the ACL Engine Mode column shows the current mode for each asset.
To change it, click Modification.
Change the mode for multiple assets
In the Access Control Engine Management - Internet Border panel, select the assets you want to update and click Batch Modify below the list.
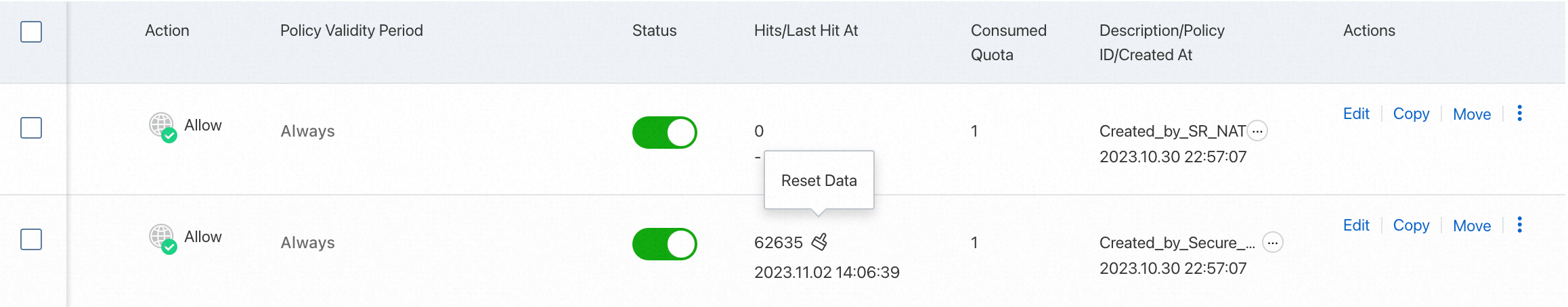
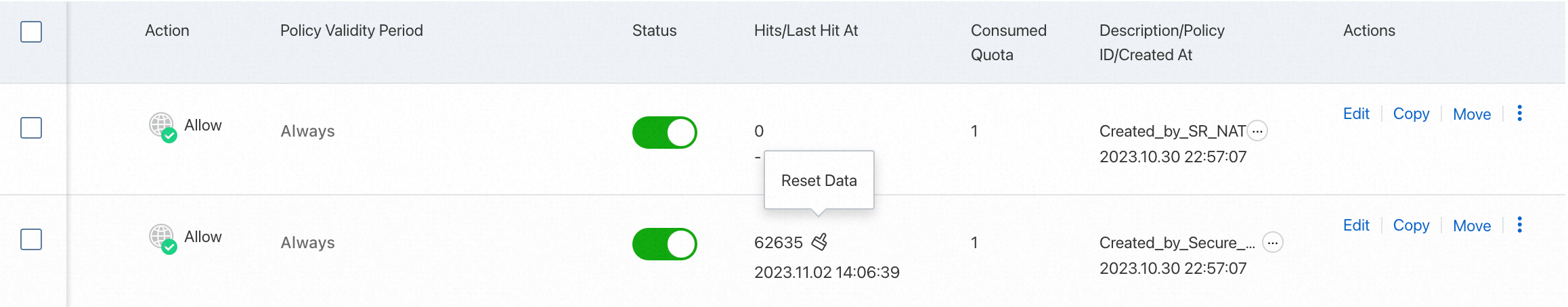
View policy hits
After your policies run for a while, check the Hits and Last Hit At columns in the policy list to see how many times each policy was matched and when.
Click the hit count to go to the Traffic Logs page and inspect the matching traffic. For more information, see Log Audit.
What to do next
After creating a custom policy, find it in the policy list. Use the Actions column to Edit, Delete, or Copy it. You can also download the full policy list, delete multiple policies at once, or click Move to adjust a policy's priority.
Priority values range from 1 to the total number of existing policies. A lower number means higher priority. When you change a policy's priority, the priorities of lower-ranked policies shift down accordingly.
Important Deleting a policy removes all traffic control that it was enforcing. Proceed with caution.