Self-managed databases on Elastic Compute Service (ECS) instances are frequent targets for brute-force attacks, vulnerability exploits, malicious command execution, and data theft. Cloud Firewall's intrusion prevention system (IPS) defends against all four threat categories from a single configuration page, without requiring changes to your database or application code.
Supported databases
Cloud Firewall IPS protects self-managed databases deployed on ECS instances. The following database types are supported:
MySQL
Microsoft SQL Server
Redis
PostgreSQL
Memcache
MongoDB
Oracle
How Cloud Firewall protects databases
Each threat category maps to a specific IPS protection mechanism:
| Threat | Protection mechanism | Behavior |
|---|---|---|
| Brute-force attacks | Threat Intelligence | Automatically blocks IPs associated with network-wide attacks and malicious scanning |
| Database application vulnerabilities (Common Vulnerabilities and Exposures (CVE), denial-of-service (DoS), data breaches) | Virtual Patching | Automatically blocks traffic identified as vulnerability exploits |
| Malicious command execution and file reading/writing (stored procedures, user-defined functions (UDFs), webshell writing) | Basic Protection (Basic Rules) | Blocks malicious operations in real time |
| Data theft and breaches | Basic Protection (high-risk SQL blocking) | Automatically blocks high-risk SQL operations in real time |
Enable database protection
Enable IPS for database defense
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Prevention Configuration > IPS Configuration.
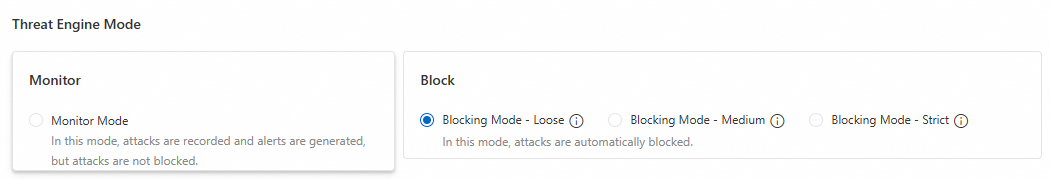
On the Internet Border tab, go to the Threat Engine Mode section and set Block Mode to Blocking Mode - Loose.
In the Threat Intelligence section, turn on Threat Intelligence.
In the Basic Protection section, turn on Basic Rules.
In the Virtual Patching section, turn on Virtual Patching.
All three protections are now active. Cloud Firewall begins inspecting database traffic immediately — no restart or database reconfiguration required.
For detailed configuration options, see IPS configuration.
What's next
Review security events regularly to identify recurring attack sources and tighten access control rules.
For databases exposed to the internet, restrict access to known IP ranges using security group rules to reduce the attack surface before threats reach the IPS layer.