Out-of-the-box server configurations are rarely secure. Unnecessary open ports, weak passwords, and missing patches each create an entry point that attackers can exploit — often automatically, at scale. Cloud Firewall's intrusion prevention system (IPS), Basic Protection, and Virtual Patching work together to close these gaps before they become incidents.
Common attack vectors
Modern attacks exploit two categories of weakness:
Improper system configurations
| Weakness | Risk |
|---|---|
| Unnecessary open ports | Expands the attack surface |
| Weak passwords | Vulnerable to brute-force attacks |
| Missing security policies | Leaves the system with no baseline defense |
Unpatched vulnerabilities
| Weakness | Risk |
|---|---|
| Command execution vulnerability | Allows arbitrary remote code execution |
| DoS vulnerability | Disrupts normal service requests |
| Data breach vulnerability | Exposes sensitive or confidential data |
Real-world cases
The following CVEs show how unpatched vulnerabilities lead to serious compromise.
Case 1: RCE in Samba (CVE-2017-7494)
Samba implements the Server Message Block (SMB) protocol on Linux and UNIX, enabling file and printer sharing. This vulnerability lets a client upload a library file to a writable shared directory and force the server to load and execute it.
Affected versions: Samba 4.4.14, 4.5.10, and 4.6.4 on Linux and UNIX.
| Impact | Description |
|---|---|
| Command execution | Remote code execution compromises the server and causes data breaches |
| Service disruption | SambaCry, a worm that exploits this CVE, mines cryptocurrency on compromised servers, consuming compute resources and degrading service availability |
Case 2: RCE in Windows SMB server (CVE-2017-0143)
The SMB server is a protocol component installed by default on Windows. This vulnerability allows an attacker to send specially crafted packets to an SMBv1 server and execute code remotely.
Affected versions: Windows Server 2008 SP2, 2008 R2 SP1, 2012 Gold, 2012 R2, and 2016.
| Impact | Description |
|---|---|
| Command execution | Remote code execution compromises the server and causes data breaches |
| Data loss | WannaCry and similar worms exploit this CVE to encrypt files, causing data loss and breaches |
How Cloud Firewall protects against these threats
The Alibaba Cloud security team continuously tracks system vulnerabilities and translates that research into prevention rules. Cloud Firewall provides layered protection across three threat categories:
| Threat | Protection mechanism |
|---|---|
| Brute-force attacks | Threat intelligence detects network-wide attack patterns and blocks scans and intrusion attempts proactively |
| OS vulnerabilities (including Samba RCE, SMB RCE) | Virtual Patching shields systems from high-risk OS vulnerabilities |
| Other intrusions (reverse shells, system file tampering) | Basic Protection detects and blocks these attacks in real time |
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account with access to Cloud Firewall console
Cloud Firewall activated and protecting your assets
Enable intrusion prevention
Step 1: Set the threat engine to Block mode
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Prevention Configuration > IPS Configuration.
Click the Internet Border tab.
For Threat Engine Mode, select a Block mode level.
Step 2: Turn on Basic Protection
On the Basic Protection tab, turn on Basic Protection.

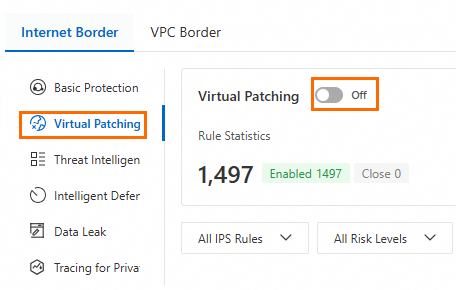
Step 3: Turn on Virtual Patching
On the Virtual Patching tab, turn on Virtual Patching.
With all three controls enabled, Cloud Firewall defends against brute-force attacks, known OS vulnerabilities, and active intrusion attempts across your internet-facing assets.