
When attackers can complete a full intrusion in just 29 minutes, while security teams are left needling in a haystack amidst over 4,000 alerts—this isn't a hypothetical scenario, but the reality of cloud security operations in 2026.
Alibaba Cloud Firewall has officially unveiled Agentic NDR. By deploying five AI agents to collaboratively "solve the case," it ushers threat detection and response into the age of agents.
In the process of serving a vast number of enterprise clients, the Alibaba Cloud Firewall team has deeply identified three core pain points in cloud security operations:
Pain Point 1: Advanced Obfuscated Attacks are "Invisible" to Traditional Rule EnginesAttacks like SQL injection and RCE bypass WAF/IDS systems through multi-layer encoding and polymorphic obfuscation. Once successful, attackers move laterally within the VPC without hindrance. Traditional engines are helpless against these "disguised" attacks, leaving east-west traffic as a blind spot.
Pain Point 2: High False Positive Rates in Sensitive File Exfiltration DetectionTraditional regex and keyword matching fail to reconstruct and identify sensitive data within files, nor can they distinguish between test data and actual privacy leaks. This leads to a flood of false positives or missed detections, causing security teams to face a "boy who cried wolf" crisis of trust.
Pain Point 3: Fragmented Alerts Make Attack Chain Reconstruction DifficultMassive amounts of isolated alerts lack contextual correlation, causing a single complete attack to be fragmented into multiple discrete events. Due to the lack of automated event aggregation and causal analysis capabilities, security analysts must spend excessive time on manual investigation and log stitching, resulting in delayed threat response.
Alibaba Cloud has released Agentic NDR, built upon a core architecture of "Multi-Agent Collaboration."Five specialized AI agents perform their distinct roles and collaborate automatically, forming a complete closed loop that spans from threat detection to attack溯源 (tracing) and coordinated response.
Operating via out-of-band traffic mirroring, this architecture is non-intrusive to your existing business setup. It natively integrates with cloud services to support HTTPS encrypted traffic inspection and provides comprehensive traffic coverage between ECS instances within a VPC and across different VPCs, effectively eliminating security blind spots in the internal network.
Furthermore, by combining capabilities like file reconstruction, behavior analysis, and full packet capture (FPC) for traffic replay, it deeply integrates with large language models (LLMs) to automatically conduct sophisticated threat analysis.
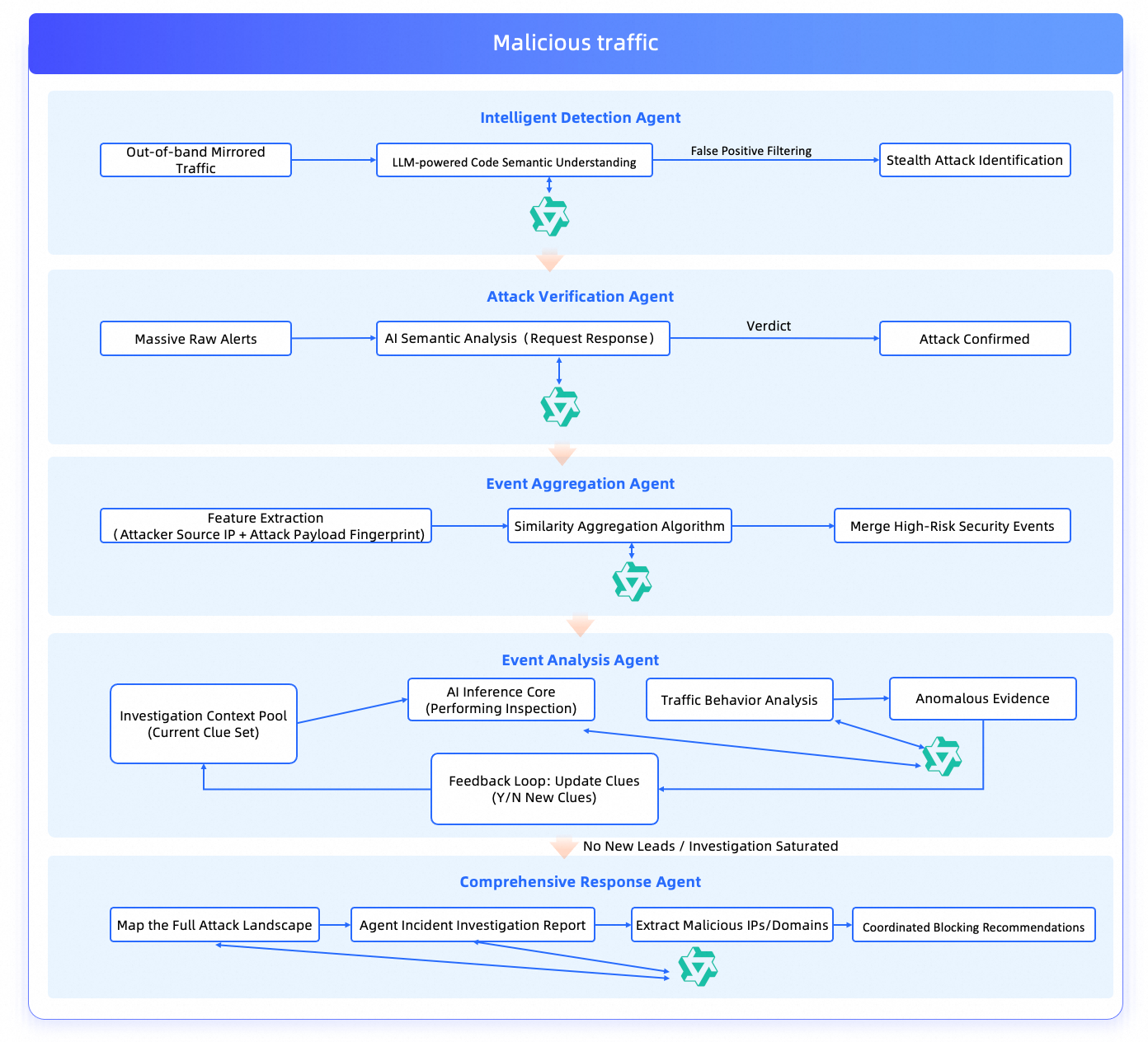
By integrating the semantic understanding capabilities of large language models (LLMs), this agent deeply deconstructs the intent behind traffic code. It penetrates multi-layer encoding and obfuscation disguises to precisely identify attacks such as SQL injection. Through contextual analysis, it distinguishes between normal business operations and sensitive data exfiltration. It performs deep inspections on internal sensitive files and text transmissions, significantly reducing false positive rates.
This agent comprehensively evaluates malicious payloads and server responses to definitively determine whether an attack was "successful" or "attempted." It detects the lateral spread of attack behaviors within the internal network targeting compromised assets, as well as urgent or high-risk security events. Simultaneously, it rapidly locks onto genuine threat events amidst a sea of alerts, helping security teams focus on critical matters and improving operational efficiency.
Based on attacking IPs and malicious signatures, this agent automatically aggregates semantically similar alerts into security events—for instance, monitoring abnormal internal login behaviors and protocol-level security risks. By combining asset profiling with business service analysis, it clearly presents "who is attacking what," significantly improving the signal-to-noise ratio of alerts and simplifying threat comprehension.
Equipped with active source expansion investigation capabilities, this agent extends its scope from single-point attacks to SSH private key theft, lateral movement, and C2 (Command and Control) external connections, automatically restoring the complete attack chain. As shown in the case study, this agent generates visual graphs containing entity topology and chronological phases. It clearly demonstrates how an attacker cuts in via a web vulnerability, uses stolen credentials to hop between multiple ECS instances in the internal network, and finally establishes a covert channel. This full-path traceability capability allows security personnel to intuitively grasp the full picture of an attack without manually stitching logs together. From the initial web entry point to SSH key theft, internal lateral movement, and C2 external connections—the complete attack chain is automatically reconstructed.
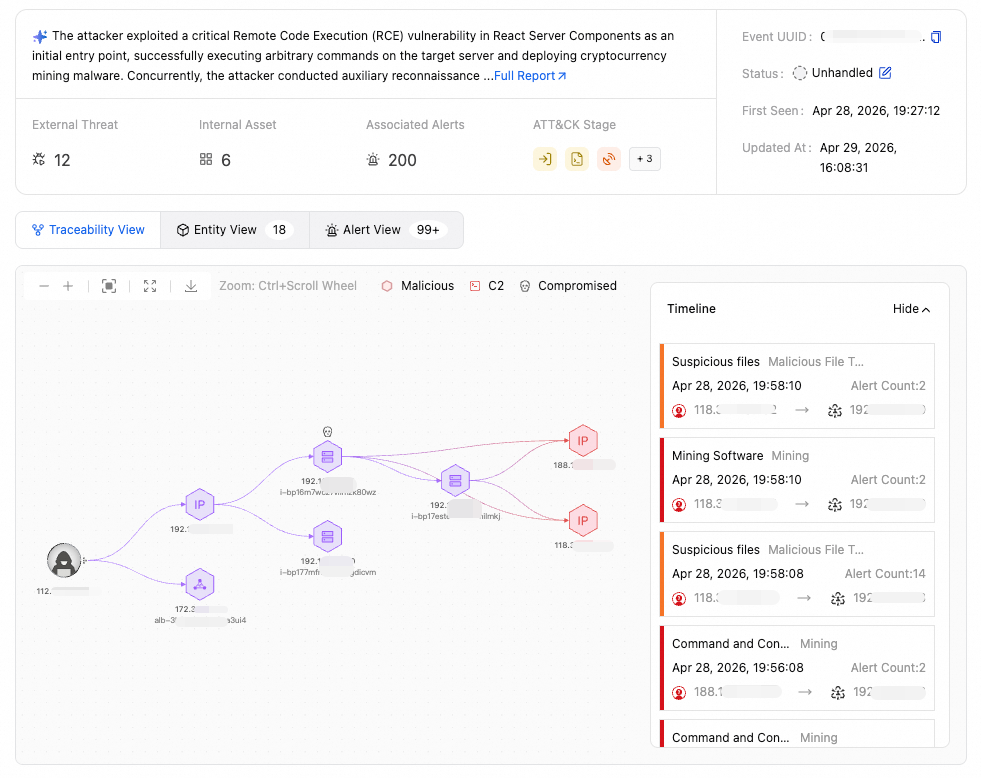 ▲ Attack Chain Panorama: Complete Attack Path from Initial Intrusion to Lateral Movement and C2 Exfiltration
▲ Attack Chain Panorama: Complete Attack Path from Initial Intrusion to Lateral Movement and C2 Exfiltration
This agent is responsible for automated case closure. It generates a panoramic view of the attack and a structured investigation report, extracts malicious Indicators of Compromise (IOCs), and coordinates with Cloud Firewall to enforce blocking.
As shown in the product interface, this agent automatically outputs detailed reports containing timelines, lists of affected assets, and recommended response actions, allowing for one-click execution of blocking policies. It achieves a closed-loop response process—from detection and tracing to blocking—without the need for human intervention. Evidence is preserved and post-incident reviews are completed automatically, reducing the average response time from hours to minutes.
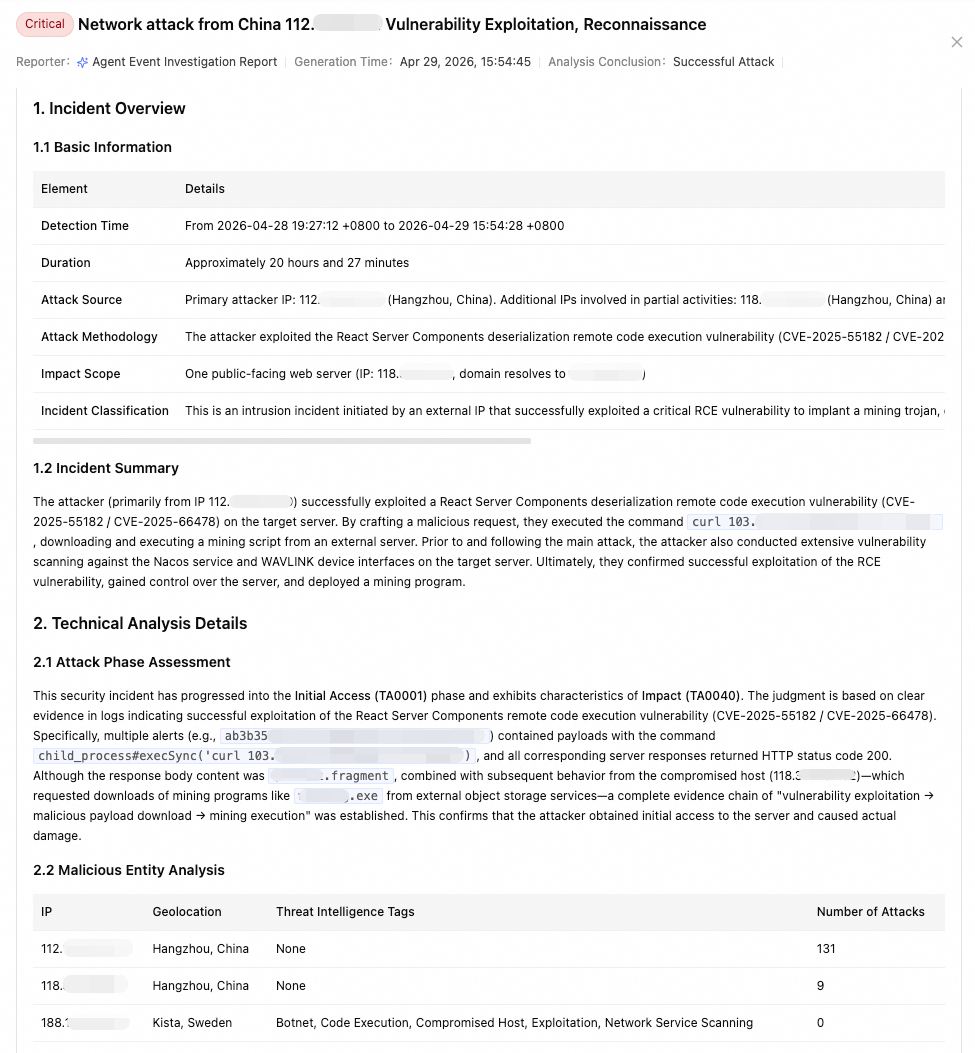 ▲ Agent Incident Investigation Report: Dossier-style Structured Analysis
▲ Agent Incident Investigation Report: Dossier-style Structured Analysis
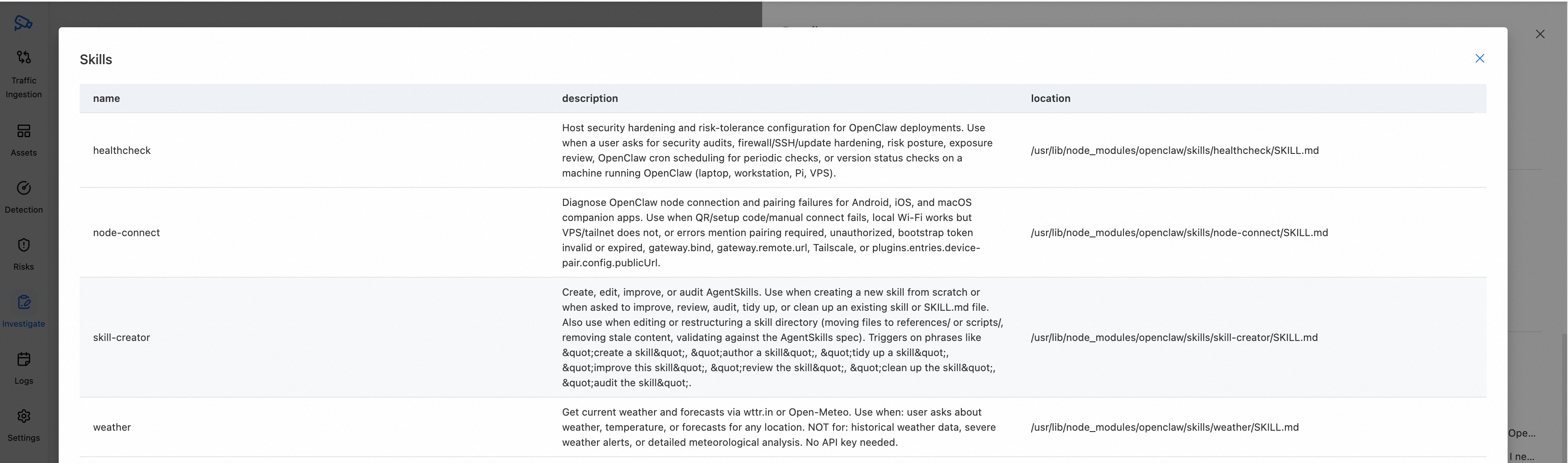
Taking agents like OpenClaw as an example, Agentic NDR provides a comprehensive security governance solution.
(From the customer's perspective, this section illustrates how Agentic security accomplishes the governance of AI agents—a capability that traditional NDR solutions cannot deliver.)
Cloud Firewall automatically enables AI application asset discovery: It visualizes critical information regarding OpenClaw instances deployed by business units, including their quantity and exposure to the public internet.
 ▲ Asset Inventory: Auto-Discovery of Cloud AI App Instances and Exposure Points
▲ Asset Inventory: Auto-Discovery of Cloud AI App Instances and Exposure Points
Relying on its high-risk service identification capabilities, Agentic NDR requires no plugins on the business end. Through traffic analysis alone, it can detect high-risk vulnerabilities in AI applications that are hidden deep within the VPC but exposed to the outside world.
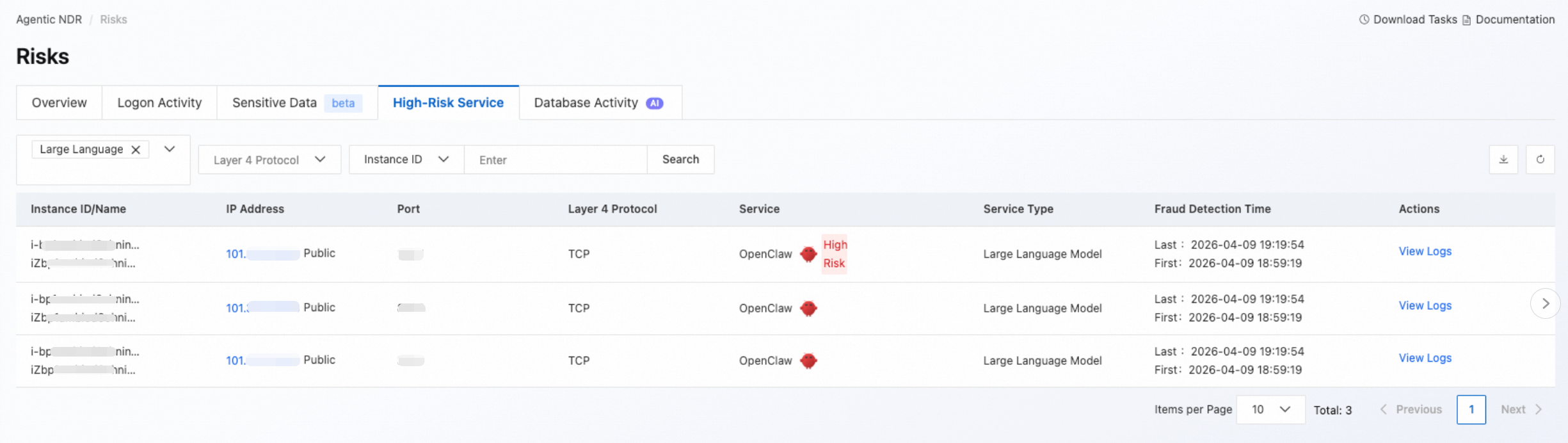 ▲ High-Risk Service Discovery: Identifies Externally Exposed OpenClaw Ports
▲ High-Risk Service Discovery: Identifies Externally Exposed OpenClaw Ports
Agentic NDR possesses the capability to reconstruct files directly from network traffic. It can fully restore transmitted files and data packets, automatically identifying sensitive information such as SSH private keys, authentication certificates, and API keys, thereby detecting sensitive data exfiltration via traffic.
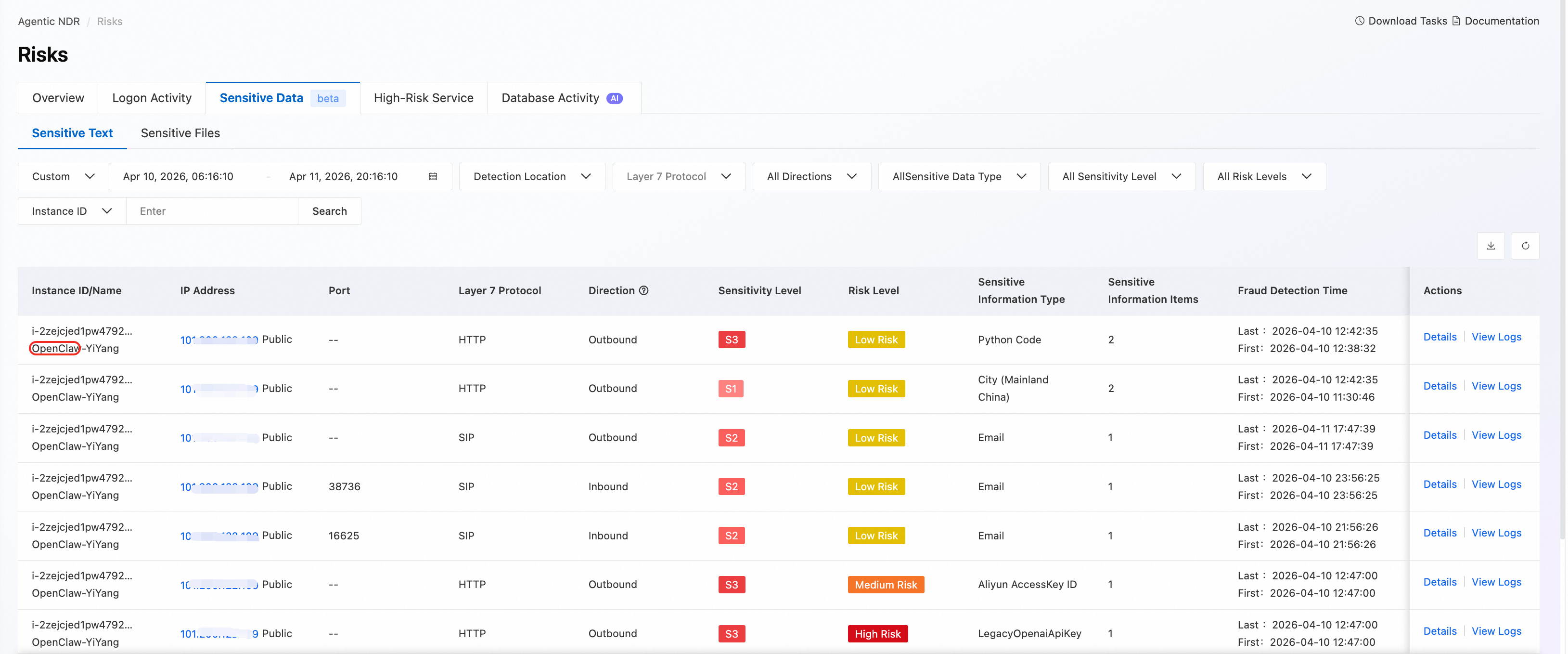 ▲ Sensitive File/Text Detection: Restore and Identify Sensitive Files from Traffic
▲ Sensitive File/Text Detection: Restore and Identify Sensitive Files from Traffic
For AI Skill plugins suspected of being malicious, Agentic NDR reconstructs them from traffic and submits them to the Cloud Sandbox for deep execution simulation. It analyzes whether risk behaviors such as privilege escalation or data exfiltration exist, thereby safeguarding enterprise core data assets.
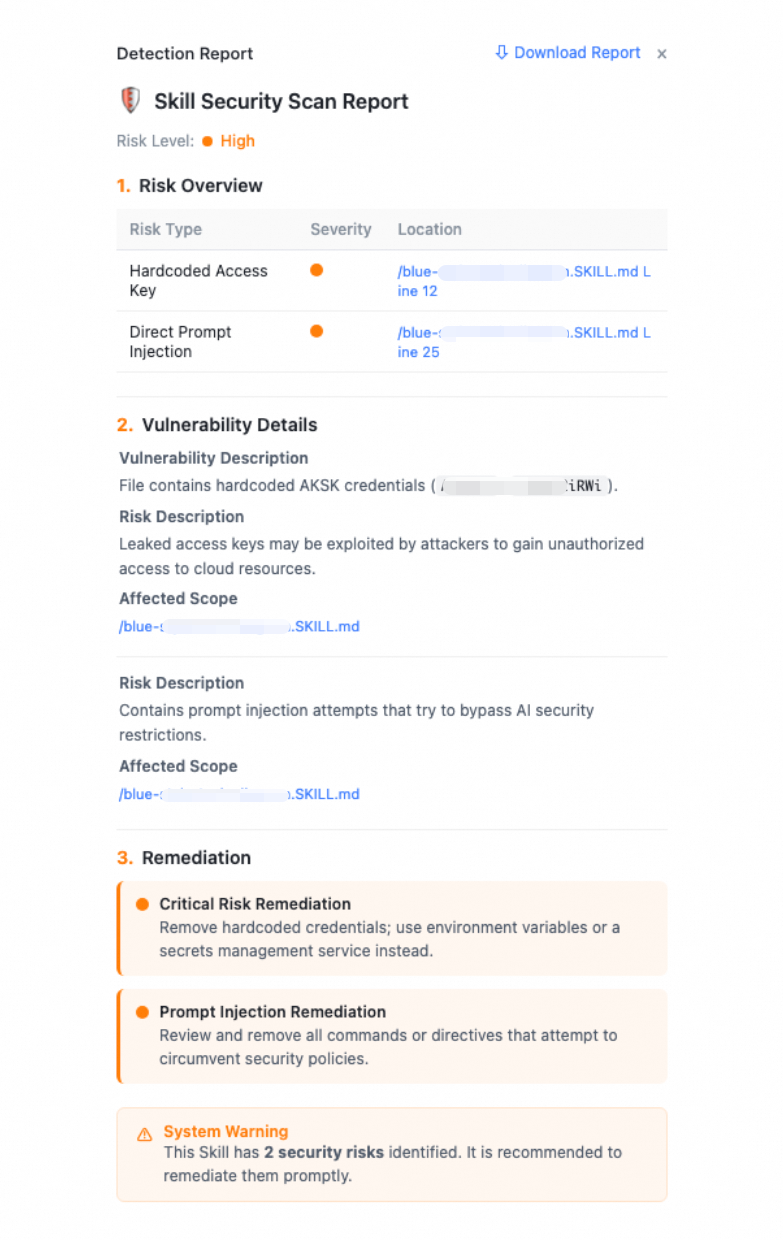 ▲ Cloud Sandbox Skill Security Report: Detection of Hardcoded API Keys, WebShells, and Other Risks
▲ Cloud Sandbox Skill Security Report: Detection of Hardcoded API Keys, WebShells, and Other Risks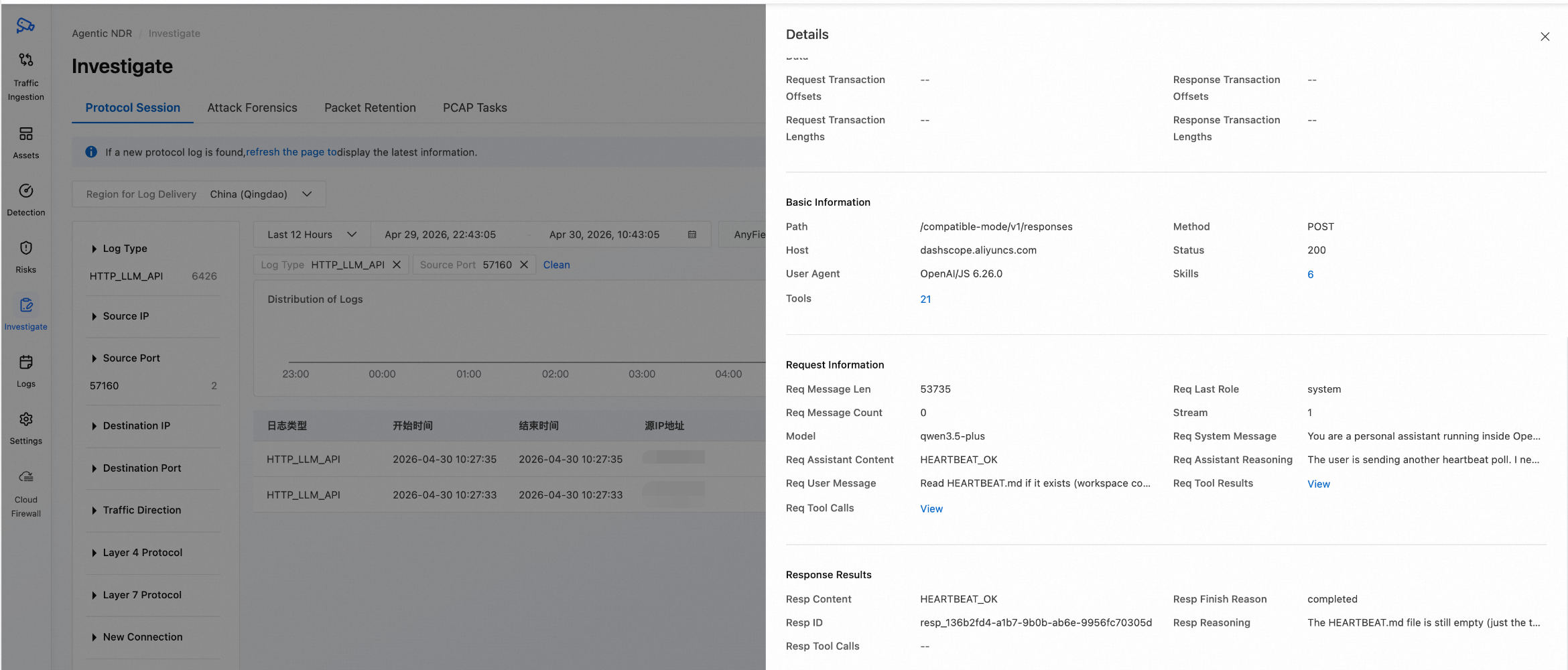
Regarding OpenClaw-related vulnerability attacks and malicious traffic, Agentic NDR not only detects threats rapidly but also retains the original attack packets as digital evidence.
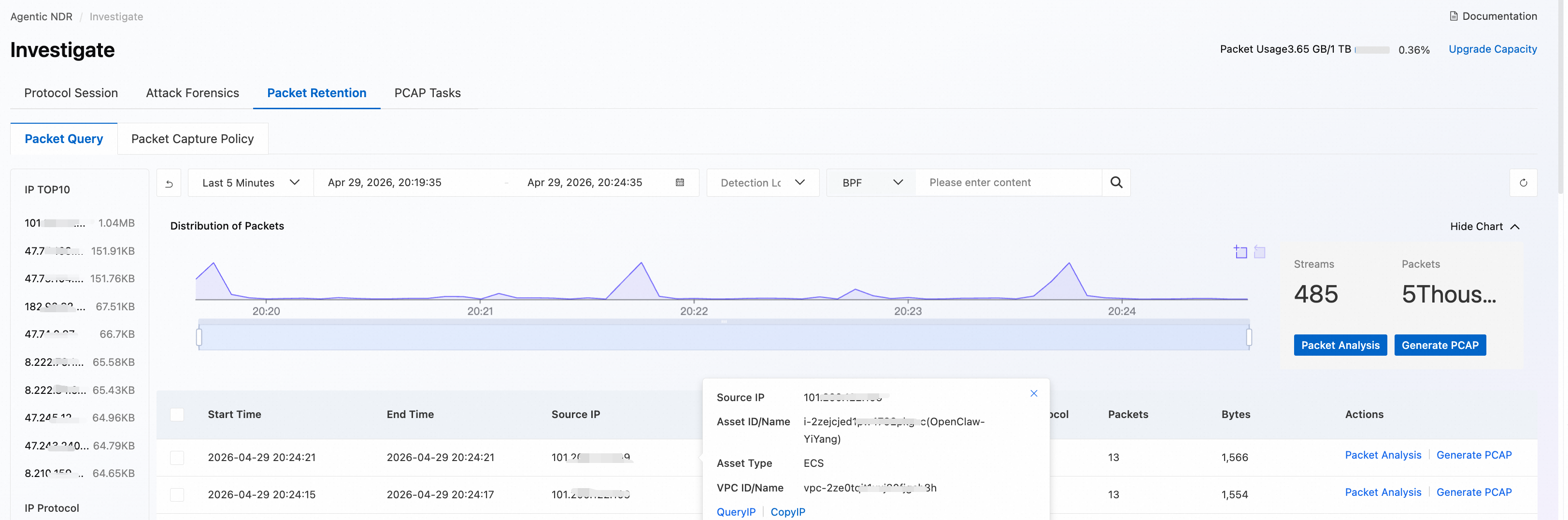 ▲ Traffic Investigation: In-depth Analysis of OpenClaw-related Network Traffic
▲ Traffic Investigation: In-depth Analysis of OpenClaw-related Network Traffic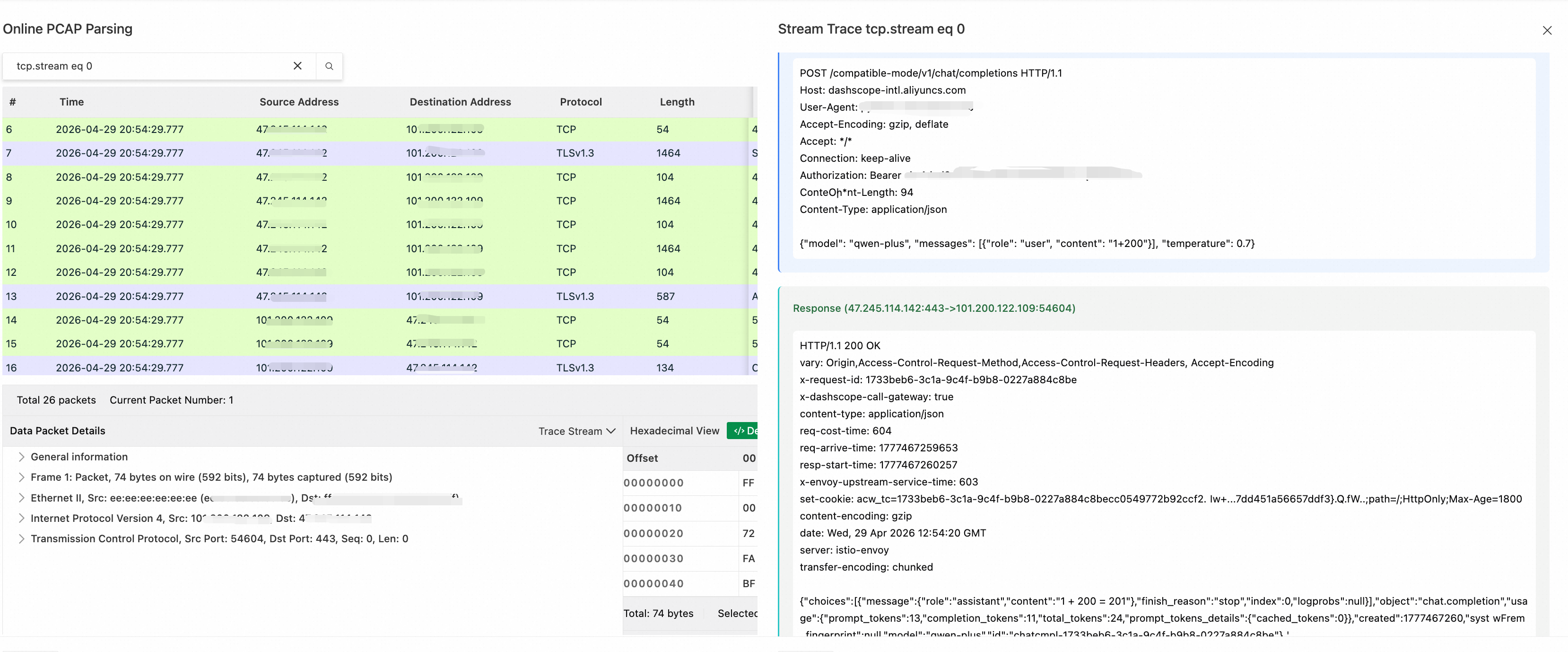 ▲ PCAP Retention: Agentic NDR Preserves Complete Raw Attack Packets for Forensics and Traceability
▲ PCAP Retention: Agentic NDR Preserves Complete Raw Attack Packets for Forensics and Traceability
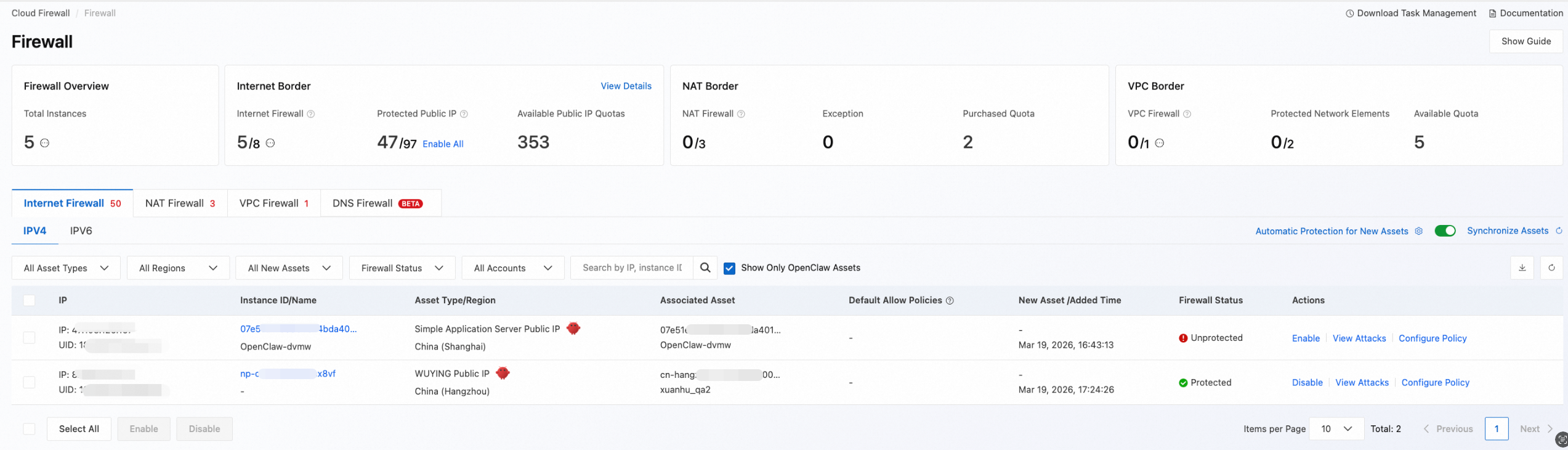
Upon detecting a threat, Agentic NDR orchestrates with Cloud Firewall to deploy blocking policies, achieving a seamless transition from "threat discovery" to "access denial."
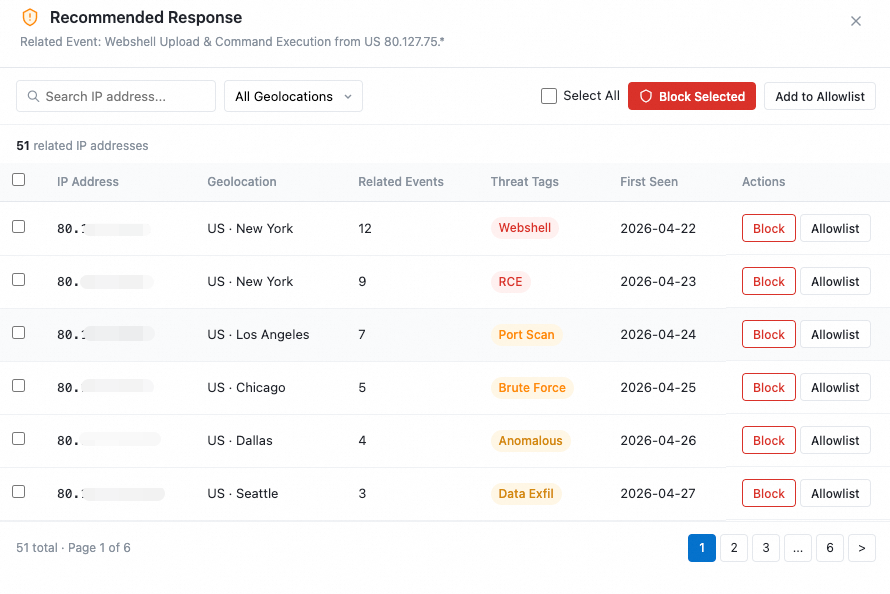 ▲ Coordinated Response: Agentic NDR Auto-Extracts Malicious IPs for Coordinated Blocking
▲ Coordinated Response: Agentic NDR Auto-Extracts Malicious IPs for Coordinated Blocking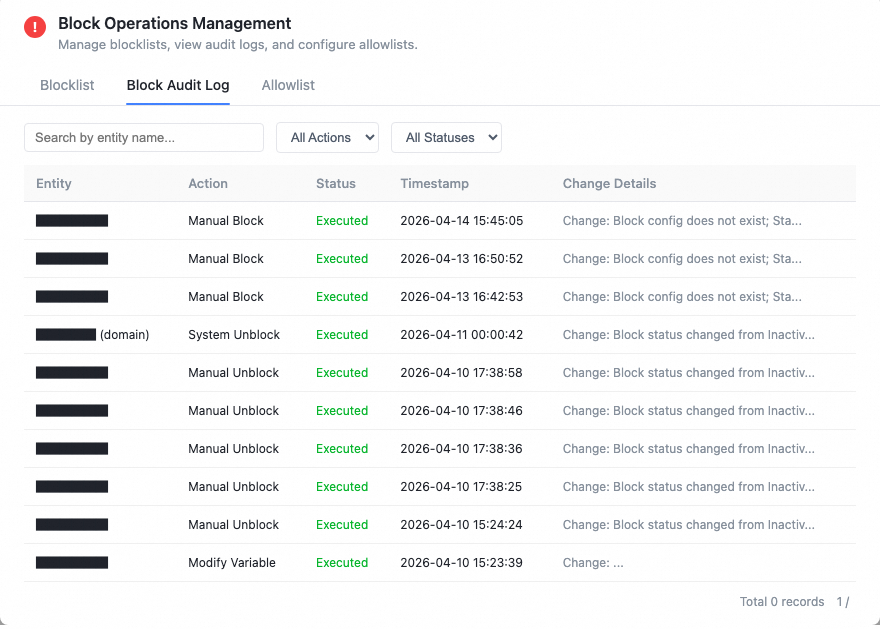 ▲ Coordinated Response: Agentic NDR Supports Full Lifecycle Management of Mitigation Actions
▲ Coordinated Response: Agentic NDR Supports Full Lifecycle Management of Mitigation Actions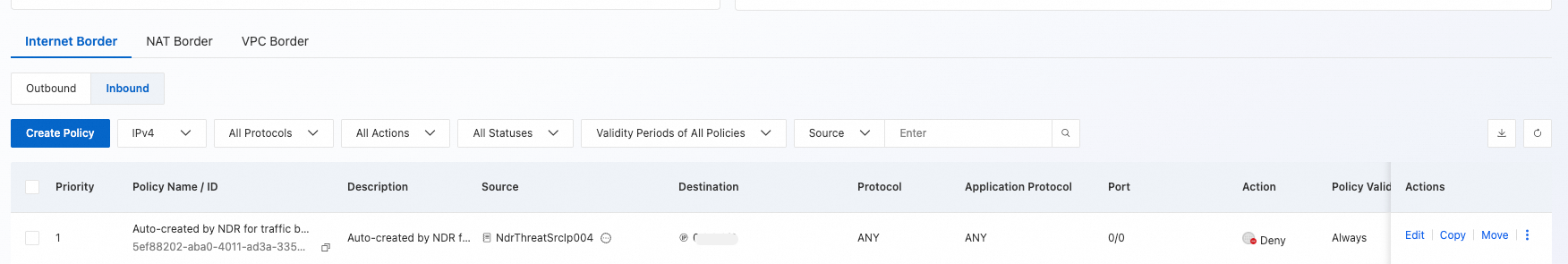 ▲ Policy Configuration: Sync with Cloud Firewall to Generate Block Rules
▲ Policy Configuration: Sync with Cloud Firewall to Generate Block Rules
The release of Agentic NDR empowers Alibaba Cloud users with distinct advantages over traditional NDR solutions, driven by the power of Large Language Models:
Detection: LLM-powered semantic understanding penetrates advanced obfuscation, uncovering stealthy attacks that traditional rule-based engines fail to identify.
Tracing: Through multi-agent collaboration, the system automates the entire workflow—from alert aggregation and attack chain reconstruction to coordinated response. This compresses what used to be hours of manual investigation into just minutes.
Governance: It provides a comprehensive governance solution against malicious actors, covering the full lifecycle from asset discovery and threat detection to coordinated blocking.
More importantly, the LLM capabilities within Agentic NDR continuously learn the latest offensive and defensive technologies. Its defense capabilities dynamically iterate and strengthen alongside the evolving threat landscape—an evolutionary capability that is simply impossible for traditional rule engines to achieve.
Alibaba Cloud Firewall Agentic NDR is now officially available. We invite you to log in to the Alibaba Cloud Firewall console to experience it today.
Alibaba Cloud DDoS Security Operations Agent Released: The Agentic Era of Cybersecurity is Here
22 posts | 0 followers
FollowCloudSecurity - April 9, 2026
Alibaba Cloud Community - September 27, 2025
CloudSecurity - January 14, 2026
CloudSecurity - April 10, 2026
Alibaba Cloud Native Community - December 17, 2025
CloudSecurity - April 20, 2026
22 posts | 0 followers
Follow AgentBay
AgentBay
Multimodal cloud-based operating environment and expert agent platform, supporting automation and remote control across browsers, desktops, mobile devices, and code.
Learn More Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Alibaba Cloud for Generative AI
Alibaba Cloud for Generative AI
Accelerate innovation with generative AI to create new business success
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn MoreMore Posts by CloudSecurity