As open-source agents like OpenClaw reshape security boundaries with sweeping momentum, the long-standing contradictions within traditional Security Operations Centers (SOCs)—characterized by alert fatigue, operational complexity, lack of global visibility, and a shortage of professional security personnel—are further intensifying.
In the face of fragmented boundaries and security blind spots brought by the "Lobster Craze," alongside an expanding AI attack surface, the traditional security operations model—plagued by slow log correlation and difficult full-chain traceability—is bound to be superseded by a new, AI-driven next-generation paradigm. This evolution will not merely manifest as countering AI-based attacks at AI speed or providing assistant-level alert interpretation; rather, it will advance into a form of digital productivity for security operations capable of autonomous execution.
Alibaba Cloud has officially unveiled the new Agentic SOC, ushering in a new era of autonomous security operations.
By integrating over a decade of accumulated cloud-native security expertise with cutting-edge AI-native design philosophies, the platform delivers four core capabilities: omni-domain risk perception at the environmental layer, model-driven deep reasoning, autonomous collaborative investigation by Agents, and closed-loop full-chain traceability.
AI Agents are capable of highly autonomous global task orchestration, automatically executing log analysis and path restoration. Through an intelligent loop of "Perception—Decision—Execution," Alibaba Cloud Agentic SOC achieves a paradigm shift in security operations, transitioning from "human-reliant rule monitoring" to "autonomous collaboration."
Agentic SOC is not merely a superposition of features; it delivers a completely new security operations experience.
Built upon Large Language Models (LLMs) and an Agent Cluster architecture, Agentic SOC boasts superior capabilities in semantic understanding, context correlation, and task orchestration. Centered around specific incidents, the system can autonomously orchestrate a chain of tools—including querying, analysis, correlation, and judgment—to execute complex workflows. These range from log analysis, root cause tracing, and path restoration to impact assessment and the generation of remediation suggestions.
Furthermore, Agentic SOC is deeply integrated with Alibaba Cloud's native omni-domain security data. By adopting a "Skills + Memory" AI-Native architecture, it significantly enhances the efficiency, accuracy, and scalability of threat response, truly achieving millisecond-level reaction times.
Designed for complex multi-cloud and heterogeneous security environments, Agentic SOC has established full-link native telemetry collection capabilities spanning from IaaS and PaaS to SaaS. It supports the unified ingestion of logs from a wide range of cloud services—including ECS, containers, SLB (Server Load Balancer), and databases—and performs unified modeling across key security domains such as identity, endpoint, network, application, cloud infrastructure, and data security.
Furthermore, the platform supports nearly 100 types of log sources, including third-party cloud providers like AWS and Azure, as well as mainstream security vendors like Palo Alto and Fortinet. This extensive compatibility continuously enhances unified collection, comprehension, and operational capabilities across multi-cloud and third-party scenarios.
Leveraging the powerful generalized reasoning capabilities of Qwen3.5 as the "Strategic Brain," the system drives threat assessment, attack chain reasoning, and decision-making in complex scenarios. Simultaneously, a security-specific large model, fine-tuned from Qwen3.5-35B, acts as the "Tactical Expert," responsible for log semantic parsing, ATT&CK technique identification, and real-time alert classification to achieve millisecond-level precision.
This architecture perfectly fuses the "breadth" of general cognition with the "depth" of vertical domain expertise. While significantly reducing computing costs, it ensures that every security decision possesses both the sharp intuition of a large model and the best practices of a security expert. Consequently, AI-driven security event discovery efficiency has increased by 8x, and security alert coverage has improved by 2x.
Powered by a Skills + Memory AI-Native architecture, the system automatically memorizes attack patterns, IoC (Indicators of Compromise) signatures, and response strategies. When known threats reappear, it directly retrieves historical experience to achieve rapid closed-loop resolution.
Investigation workflows are encapsulated as reusable capability units via Skills. These are not only ready-to-use out of the box but also support customization to fit specific business scenarios. By continuously aggregating massive anonymized attack-defense experience from the cloud, the platform becomes increasingly knowledgeable about your business environment and more aligned with operational habits the more it is used.
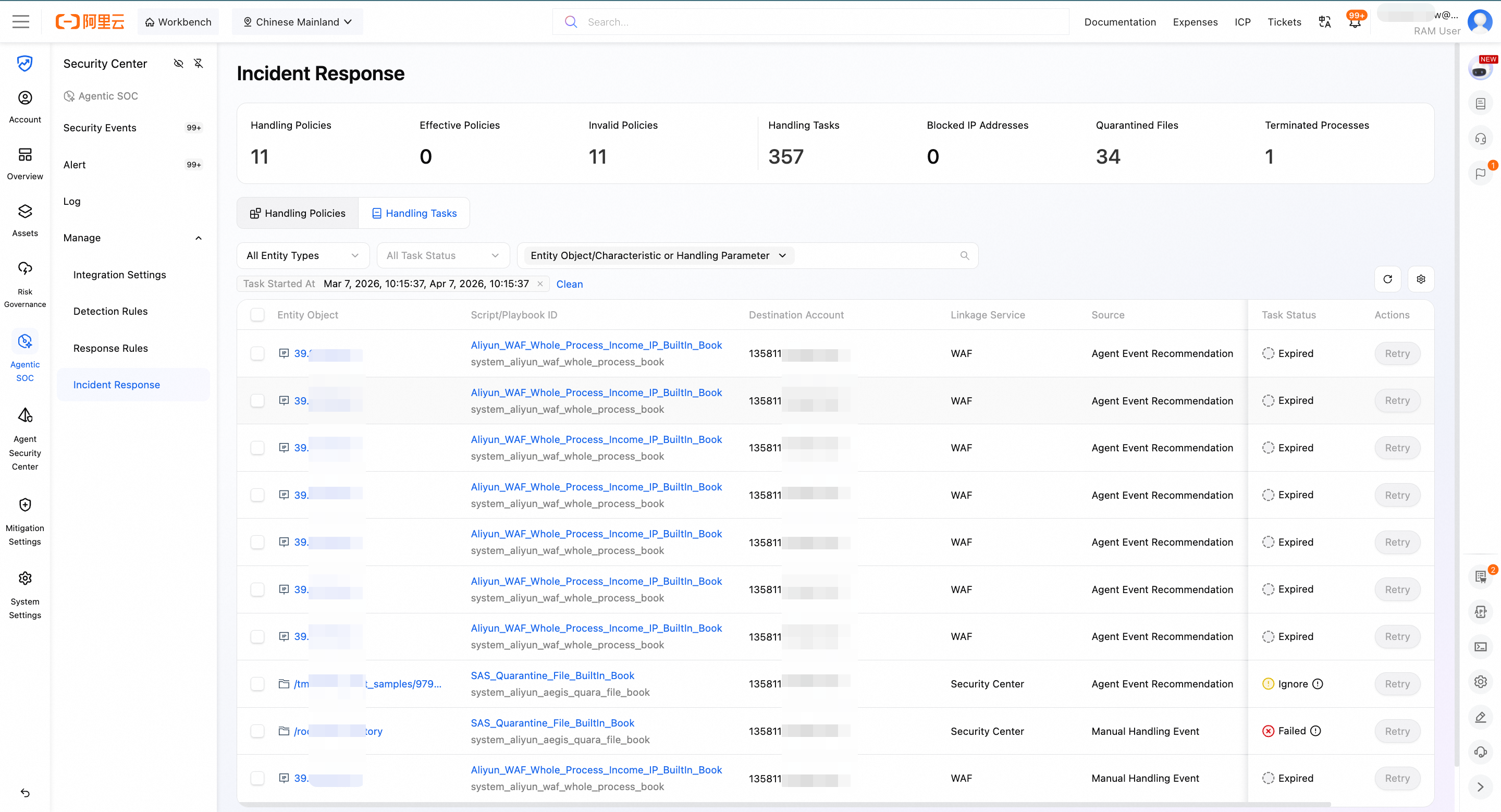
Once a threat is detected, there is no need to manually log in to multiple consoles for individual operations. Directly connecting to products from multi-cloud providers like Alibaba Cloud, Tencent Cloud, and Huawei Cloud, as well as various security vendors, the system allows for one-click execution of remediation actions such as file isolation, host snapshots, and IP blocking.
Agentic SOC also supports custom playbooks and threat intelligence integration. By automating the entire workflow from discovery to closed-loop resolution, it compresses response times from hours to minutes.
Covering the entire security operations lifecycle—from log ingestion, threat detection, and incident investigation to response and post-mortem analysis—Agentic SOC fully encompasses the core workflows of a human security team.
Powered by the Qwen Large Language Model, the Agent Team consists of five intelligent agent clusters: Log Standardization, Threat Detection, Incident Investigation, Incident Response, and Report Generation. These clusters achieve seamless end-to-end collaboration, constructing a truly autonomous closed loop.
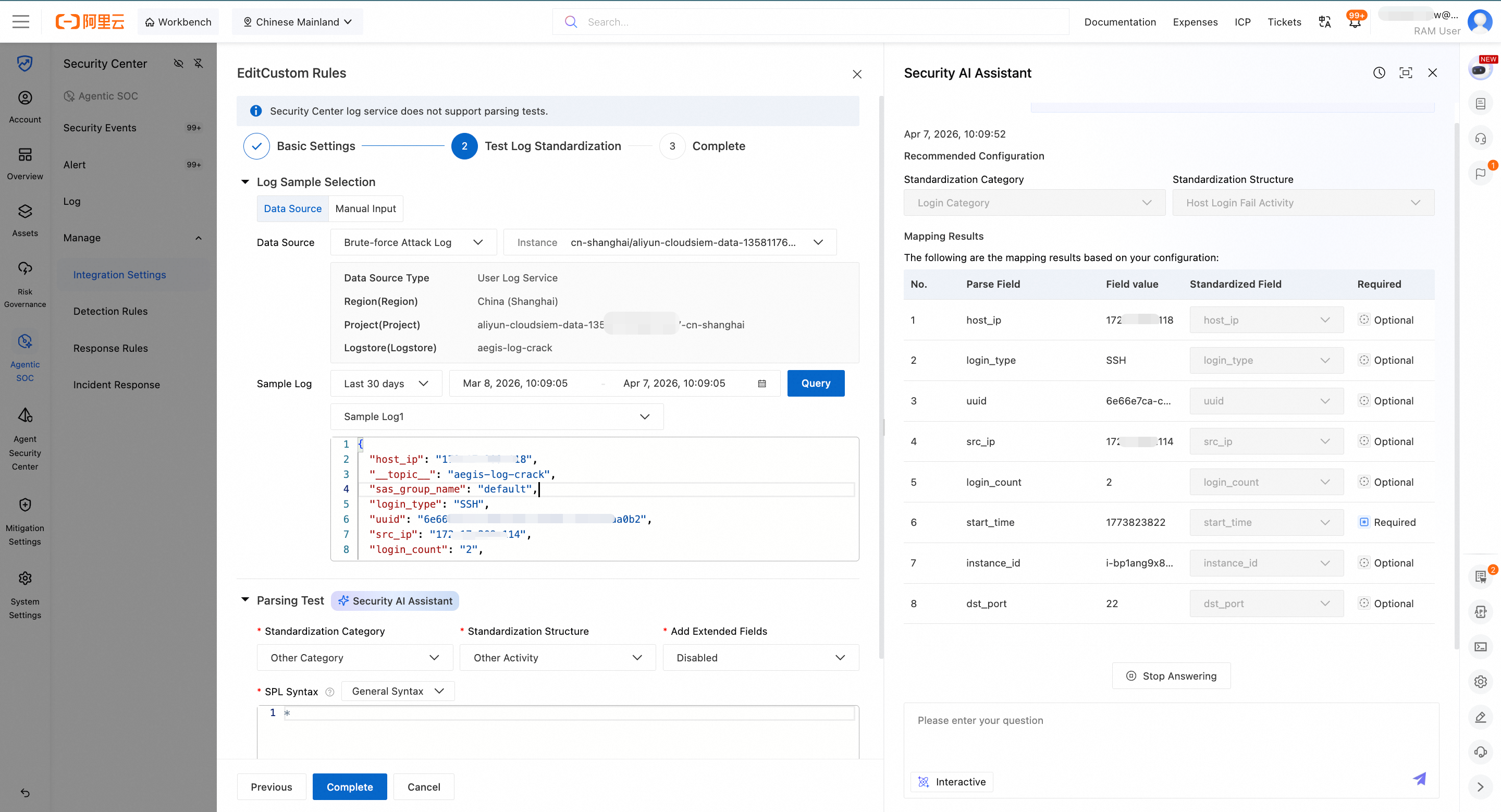
The Log Standardization Agent leverages semantic recognition technology to automatically parse and map multi-source heterogeneous logs into a unified security model, generating SPL (Search Processing Language) syntax with a single click. This significantly lowers the learning curve for users and accelerates the efficiency of log onboarding.
Typically, a professional SIEM operations engineer's workflow involves manually searching for sample log field descriptions, understanding the SIEM security model structure, learning SPL syntax, and continuously debugging to optimize the syntax over multiple rounds. The Log Standardization Agent compresses this process from 5–7 working days to less than half a day, improving log onboarding efficiency by 90%.
In the realm of threat detection, taking the "Malicious Web Traffic Backtracking Agent" as an example: when a host-side anomaly is detected—such as a high-risk Remote Code Execution (RCE) alert—the Threat Detection Agent is triggered. It then traces the web attack entry point by analyzing network-side WAF flow logs.
Based on the payloads found in the logs, the Agent performs feature extraction, cross-domain retrieval, correlation confirmation, and payload restoration. By seamlessly integrating host-side anomalies with network-side attack payloads for cross-analysis, the system achieves a cross-domain closed loop and delivers precise intrusion analysis.
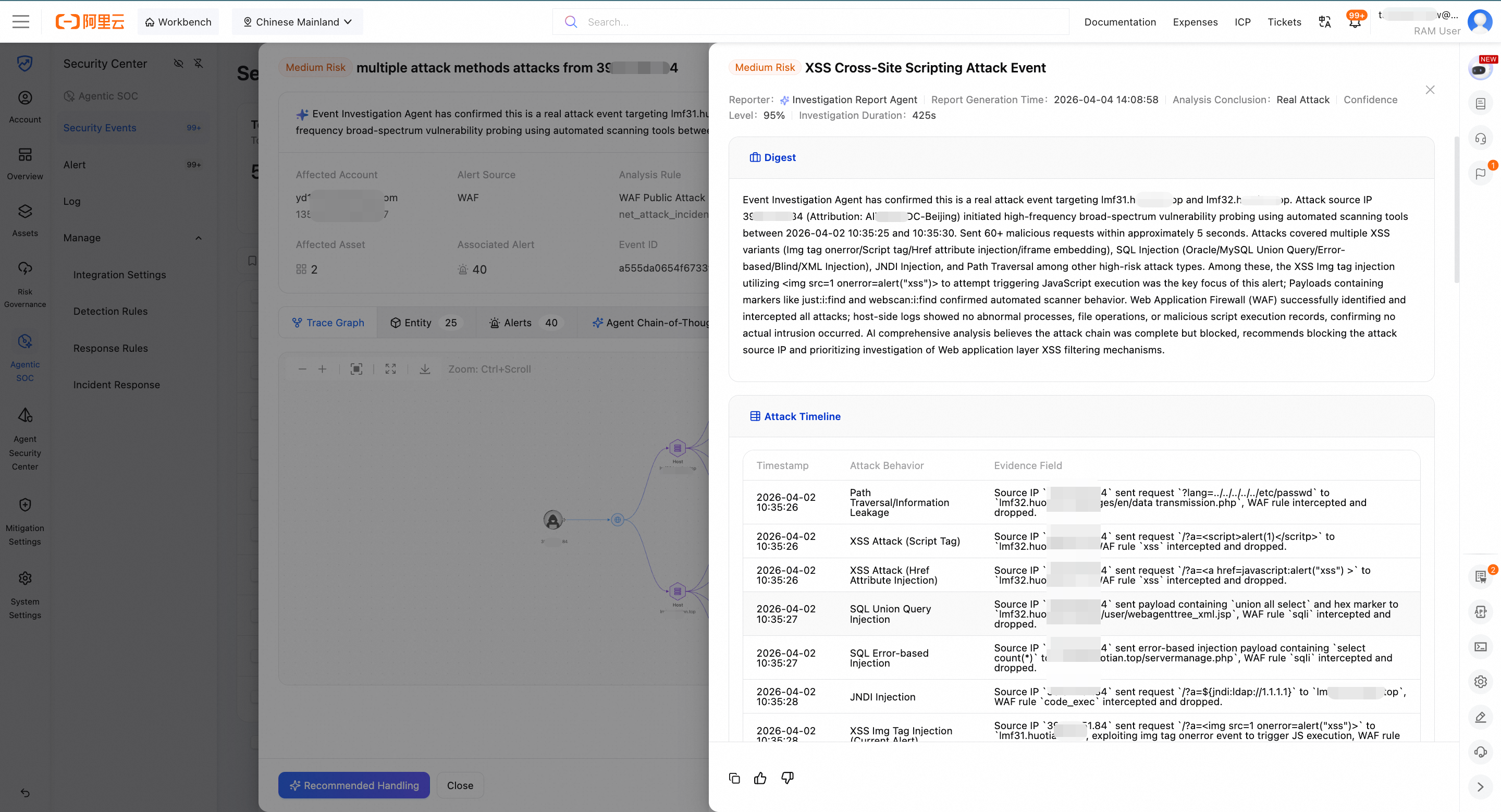
Powered by the Alibaba Cloud Security Knowledge Graph and the Qwen series of Large Language Models, the Incident Investigation Agent integrates the ReAct (Reasoning and Acting) architecture to build an intelligent investigation hub. Taking alerts as clues, the Agent autonomously executes a "Think-Plan-Act" loop. It automatically reconstructs attack paths and timelines, assesses the impact scope, and structurally outputs provenance graphs, remediation suggestions, and the Agent's Chain of Thought (CoT).
● With an end-to-end autonomous assessment coverage rate of up to 80%, the system significantly reduces manual intervention, allowing security teams to bid farewell to alert fatigue:
● Drastically Reduce Costs: Users only need to verify event details, saving hundreds of man-days in operational costs per year.
● Focus on High-Value Decisions: Teams can focus on deep hunting for advanced threats (such as APTs and 0-days).
● Strategic Shift: Security operations shift from "firefighting" to "strategic defense," entering the era of autonomous driving.
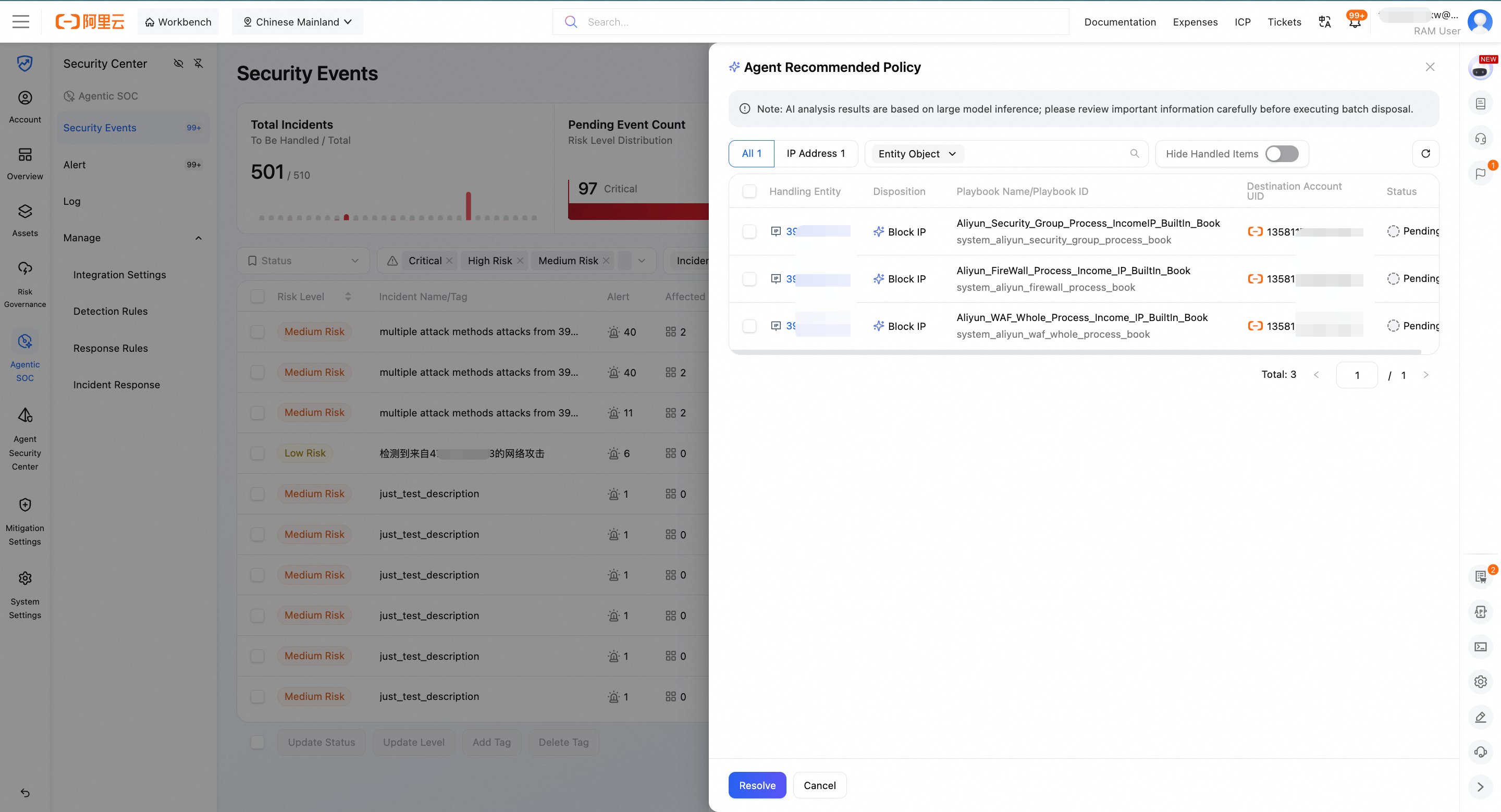
The autonomous execution of security operations in Agentic SOC is strictly governed by human supervision. From the perspective of an incident response expert, the Incident Response Agent comprehensively analyzes the impact based on investigation results and provides prudent remediation suggestions. These are embedded within a human-in-the-loop review process; once confirmed, actions are automatically executed. The system supports batch task distribution, provides complete audit logs, and allows for reversal operations.
● Comprehensive Coverage: Supports remediation capabilities for 6 types of entities including IPs, files, and processes, covering 99% of malicious entities across the network.
● High Precision: Based on investigation conclusions, the Incident Response Agent performs a secondary verification analysis. When a judgment is successfully made, the accuracy rate for identifying malicious entities reaches 99%.
● Rapid Response: The Mean Time to Respond (MTTR) for network-wide incidents is accelerated from 90 minutes to 30 minutes.
The Incident Investigation Report Agent automates the output of technical investigation reports in minutes. It provides a comprehensive post-mortem analysis including professional event characterization and summaries, attack chains and timelines, impact assessments, root cause analysis, remediation suggestions, and IoC (Indicators of Compromise) evidence, fully reproducing the security incident.
Global attack chain report generation takes only minutes, saving human engineers hours or even days by eliminating the need for repetitive, tedious evidence collection. Furthermore, it ensures no investigative evidence is overlooked and standardizes report output quality, supporting one-click copying in Markdown format.
Alibaba Cloud Security Operations Agent liberates hundreds of man-days of operational costs annually for customers, realizing the vision of "Autonomous Driving for Security Operations" and truly upgrading AI from a mere auxiliary tool into digital productivity.
Prior to its official launch, Alibaba Cloud Agentic SOC has already been validated in real-world security operations scenarios across multiple top-tier global customers, earning recognition for its capabilities and efficiency across multiple dimensions.
This subsidiary of a global top-10 cosmetics giant manages a hybrid cloud infrastructure via multiple vendors, making the coordination of security operations and technical risk management extremely challenging. Specifically, their traditional SOC suffered from单一 log sources and a lack of deep analysis for massive alerts, leading to high false-positive rates and severe "alert fatigue" for the operations team.
After adopting Alibaba Cloud Agentic SOC, the company achieved unified security event operations across multi-cloud and hybrid cloud environments. Beyond native Alibaba Cloud products, they integrated 20+ additional product types and over 50 log sources, eliminating data silos and enabling true 7×24 real-time detection and response.
Outcome: The MSS managed security team now focuses on complex event assessment and customizing detection rules/playbooks, while the client's security department maintains comprehensive control over operations quality. With clear responsibility boundaries and doubled efficiency, the Mean Time to Respond (MTTR) was reduced from 6+ hours to under 2 hours.
This SME in the overseas new energy sector lacks a dedicated security team, with security duties handled by general IT staff. They previously suffered from crypto-mining malware植入 following brute-force attacks exploiting weak passwords. Traditional manual response was lagging and difficult to trace due to a lack of specialized skills.
By deploying Alibaba Cloud Agentic SOC's multi-Agent collaboration solution, the Incident Investigation Agentautonomously completed 66% of real attack assessments and path restoration. The solution supports one-click batch containment and integrates with Cloud Firewall to shift from passive response to active interception of SSH brute-force attacks.
Outcome: The solution successfully compressed the MTTR from several days to under 30 minutes, improving emergency response efficiency by 99%. Agentic SOC effectively filled the gap of a dedicated security engineer, helping the SME break through security capability bottlenecks at less than 20% of the cost of overseas manpower, achieving efficient, intelligent security operations.
This new energy vehicle (NEV) enterprise expanding globally has only one security operations staff member. Facing rapid business growth and a complex multi-cloud + hybrid cloud architecture, the expanding attack surface led to a surge in alerts and sharp compliance pressures.
Using Alibaba Cloud Agentic SOC's multi-Agent collaboration solution, the enterprise achieved unified access and management of 8 security products across Alibaba Cloud, Huawei Cloud, and third-party devices, building a standardized operations foundation for their multi-cloud environment. Relying on the autonomous assessment and automation capabilities of the Security Operations Agent, they successfully intelligently aggregated millions of daily raw alerts into approximately 90,000 security events.
Outcome: The company achieved a 99.5% automated disposal rate, increased the security event closed-loop rate from 60% to 99%, and reduced the false-negative rate by 85%. This solved the challenge of "one person doing the work of a team," ensuring security standards and compliance amidst rapid business growth.
Agentic SOC lets machines handle the complexity, allowing humans to focus on strategy—making security move as fast as thought.
Alibaba Cloud Launches Agentic API Security: The Data Defense Line for API Calls
23 posts | 1 followers
FollowAlibaba Cloud Community - September 27, 2025
Alibaba Cloud Community - August 22, 2025
Alibaba Cloud Community - May 20, 2026
Alibaba Cloud Community - January 11, 2023
Alibaba Cloud Community - April 3, 2026
Alibaba Cloud Community - April 2, 2026
23 posts | 1 followers
Follow Qwen
Qwen
Full-range, open-source, multimodal, and multi-functional
Learn More Alibaba Cloud Model Studio
Alibaba Cloud Model Studio
A one-stop generative AI platform to build intelligent applications that understand your business, based on Qwen model series such as Qwen-Max and other popular models
Learn More Alibaba Cloud for Generative AI
Alibaba Cloud for Generative AI
Accelerate innovation with generative AI to create new business success
Learn More AgentBay
AgentBay
Multimodal cloud-based operating environment and expert agent platform, supporting automation and remote control across browsers, desktops, mobile devices, and code.
Learn MoreMore Posts by CloudSecurity