The "Lobster Fever" has gone viral, sparking a global installation craze and causing the number of AI Agents to skyrocket overnight.
Open-source Agents, epitomized by OpenClaw, are evolving into autonomous "digital blue-collar workers" capable of scheduling and executing complex tasks. The architectural synergy between Agents and Skills has forged a perfect partnership, unlocking the full productivity potential of foundational models.
While this system-level execution capability and flexible skill ecosystem are rapidly driving Agent adoption in production environments, a "security black hole" is quietly forming.
Projects like the aforementioned "Lobster" have been flagged as an "absolute security nightmare." From the moment of their release, numerous instances were found exposed to the public internet, with API keys left completely unprotected. Misconfigured permissions mean these "little lobsters" operate like "clueless children who know all the family secrets yet are sent out to run errands alone."
Consequently, several leading global enterprises have already banned employees from running OpenClaw on corporate devices.
The relentless pursuit of efficiency makes technological iteration inevitable. The explosion in Agent numbers is now a reality. The pressing question remains: How do we securely delegate authority to Agents?
How can enterprises build a comprehensive defense management system that unleashes potential while managing a growing fleet of thousands of Agents annually? AI Agents urgently require a unified defense system under a brand-new security framework.
Breaking away from traditional security paradigms, Alibaba Cloud is proud to unveil the Agent Security Center—an innovative solution built from the ground up with an Agent-centric, AI-native security philosophy.
Enterprises typically manage two categories of AI Agent assets: internally developed agents and third-party agents. While assessing the security risks of these assets, organizations need a unified perspective that balances both commonalities and differences. Simultaneously, to reduce management complexity, a holistic, end-to-end view is essential.
To address this, the Alibaba Cloud Agent Security Center introduces a comprehensive protection framework covering the full lifecycle of Agents, spanning both the Development Phase (Buildtime) and the Operational Phase (Runtime).
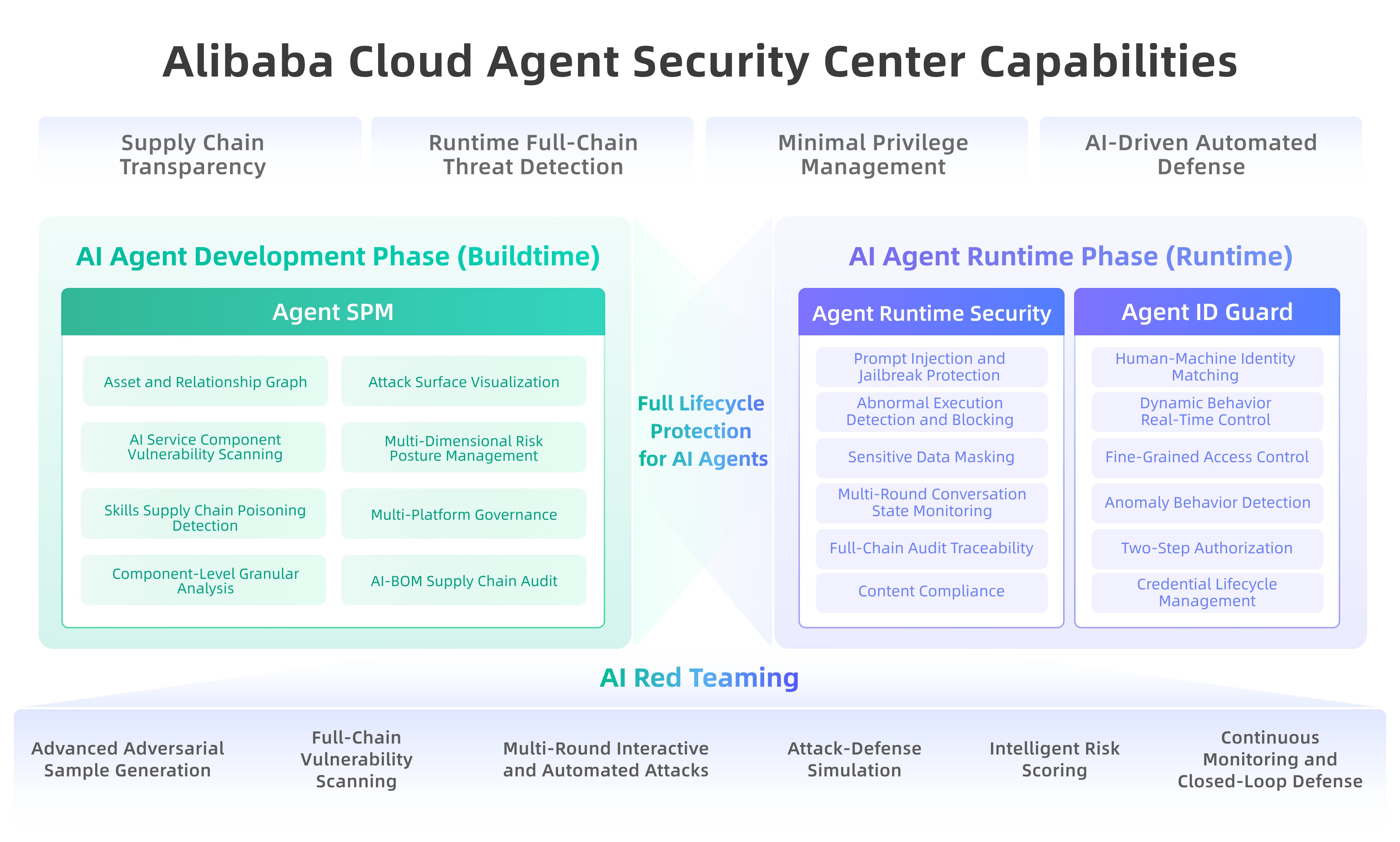
When working with open-source Agent frameworks, we face three primary security risks across the full lifecycle:
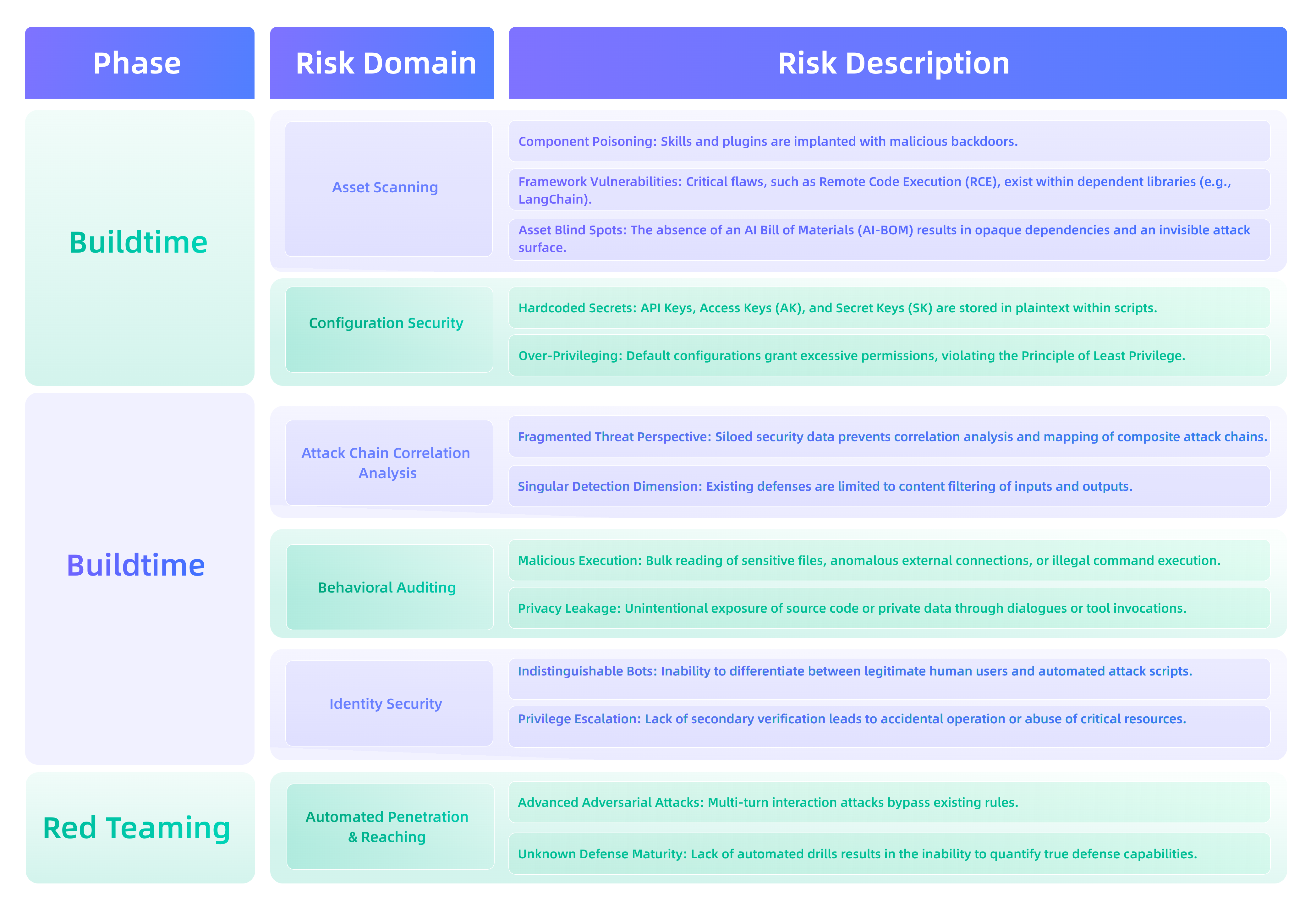
Correspondingly, the defense team must possess four core capabilities to address these technical risks:
To effectively manage both internally developed and third-party AI Agent applications, the platform must automatically discover Agent assets and identify usage patterns, including adaptation to various protocols (such as specific functional ports of LLMs).
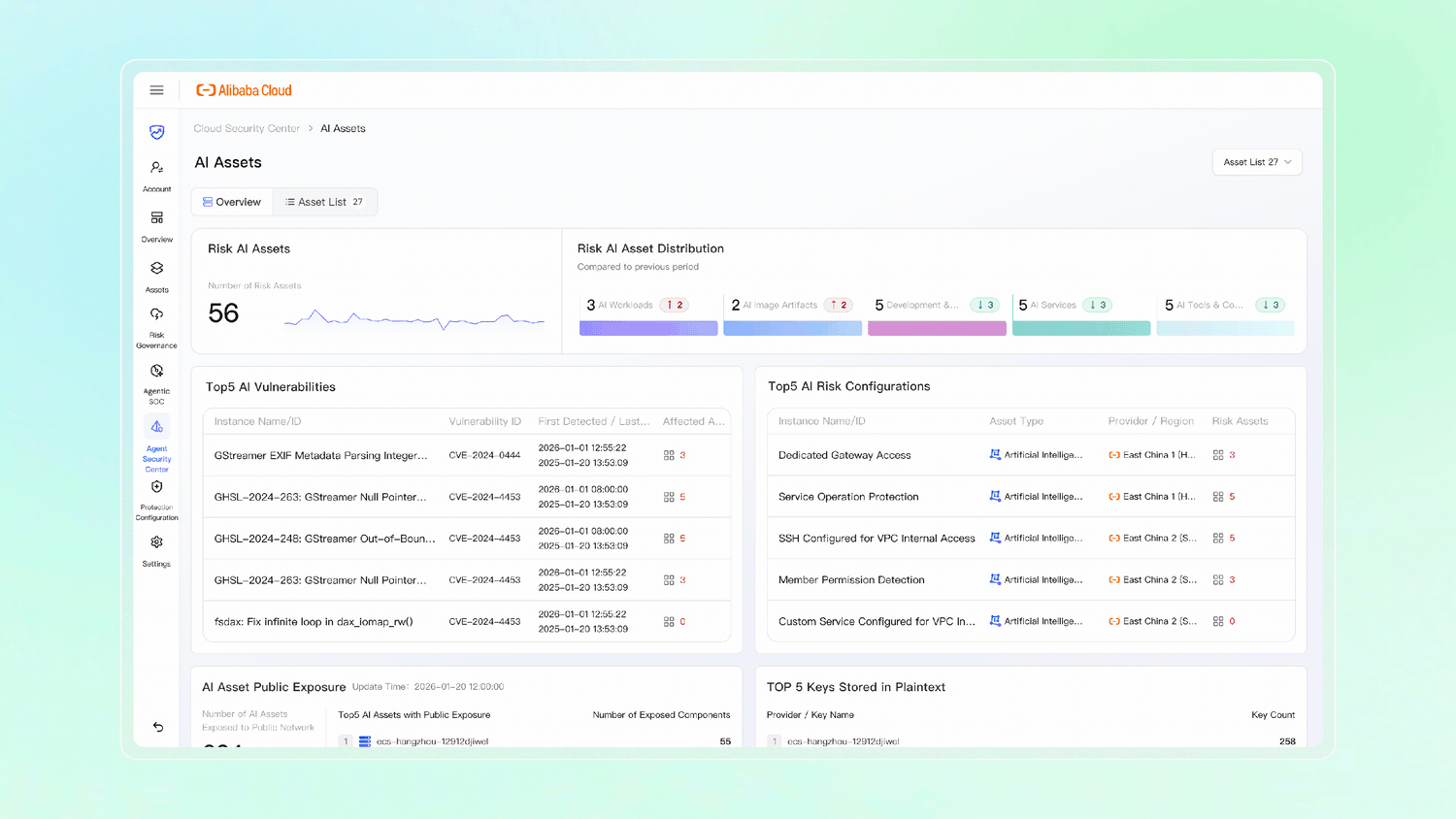
The Agent Security Center achieves comprehensive visibility into enterprise AI infrastructure through deep integration with ECS, Lightweight Servers, ACK (Container Service), and five major AI platform-level assets: Bailian, PAI, AgentRun, Dify, and AgentKit. Focusing on asset transparency and source-level governance, the platform leverages Agent Security Posture Management (ASPM) to automatically connect with mainstream development platforms like Bailian and Dify. It goes beyond simple Agent identification to deeply parse core components such as Skills and MCP protocols, constructing a complete asset lineage graph.
By combining AI-BOM (Bill of Materials) supply chain audits with specialized Skills poisoning detection, the system clearly displays third-party dependencies and rapidly locates hidden backdoors. Simultaneously, it utilizes agentless scanning to identify vulnerabilities within frameworks like OpenClaw and LangChain, ensuring full clarity regarding asset inventory and security posture.
Agent identity security faces unprecedented challenges. Within enterprises, the number of Agents vastly outnumbers human employees, and their identities are highly dynamic—constantly shifting due to delegation and task switching. Traditional, human-centric identity systems are simply unable to adapt.
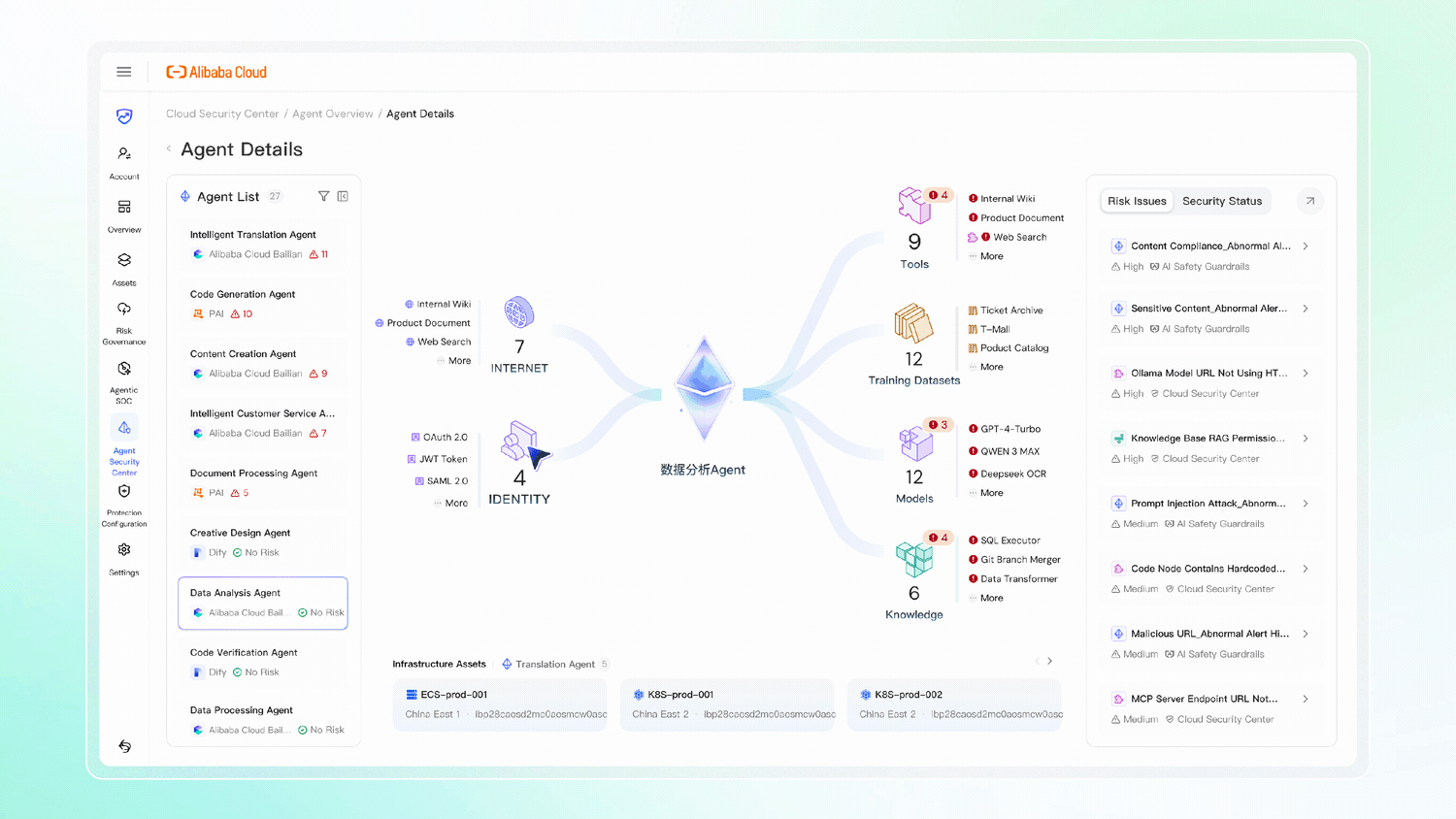
As Agent identities and credentials become scattered across disparate systems, there is an urgent need for a unified, centralized management platform. This system must achieve global consistency in managing identities, permissions, and secrets, while also identifying and mitigating data leakage risks at the API and protocol levels.
Focusing on dynamic defense and identity control, Agent ID Guard enforces strict identity governance. By orchestrating human-machine identity alignment, enforcing granular access control, and mandating secondary authorization at critical nodes, it prevents privilege abuse and credential leakage, effectively guarding the final line of defense.
In the AI era, the core differentiation in protection strategies lies in native integration. It is essential to secure the input and output of foundational models and Agents, conduct adversarial testing and model scanning, and strengthen the inherent defense capabilities of Agent assets and runtime security detection through native AI guardrails.
The AI Guardrails establish a dynamic defense architecture centered on "Runtime Behavior," specifically targeting critical threats such as indirect prompt injection, identity spoofing, data exfiltration, privilege escalation, and tool poisoning.
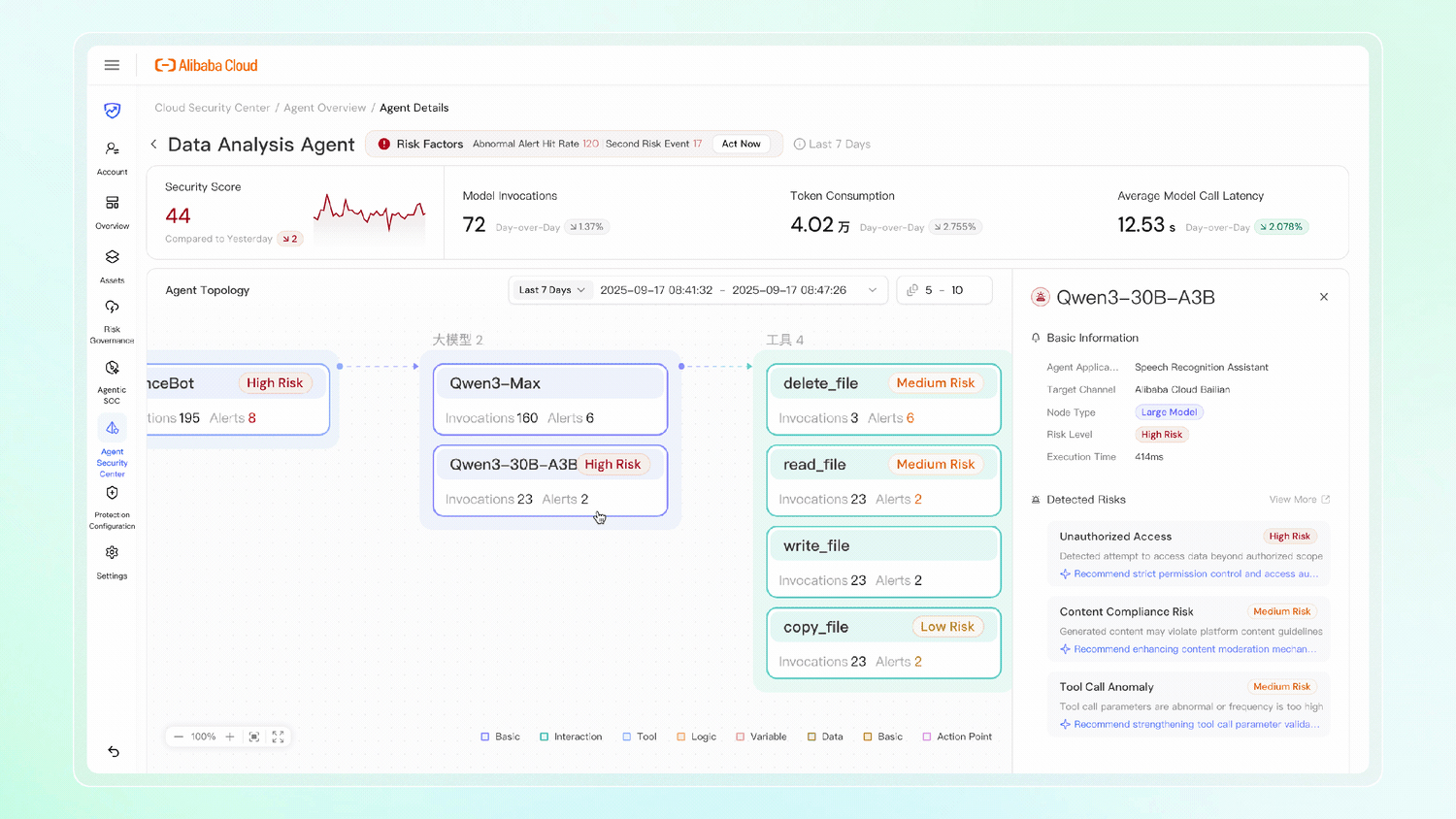
This system achieves closed-loop alarm management through "intelligent tagging and event interpretation." By leveraging AI to generate chain-of-thought event summaries, it automatically deduces risk pathways and pinpoints root causes. Furthermore, it provides panoramic topology maps and node-based timelines, intuitively visualizing the end-to-end invocation chain and risk distribution across "AI Applications → Foundational Models → Tools," while supporting drill-down auditing.
Through the integration of these three core functional modules—Asset Management, Identity Governance, and Runtime Detection—the system realizes full-chain threat detection. It establishes a dynamic, full-lifecycle security framework for AI Agents, driving the evolution from isolated point defenses to unified control, and from static rules to behavioral intelligence.
Automated Red Teaming is designed to bypass built-in model safeguards, continuously validating and assessing defense effectiveness.
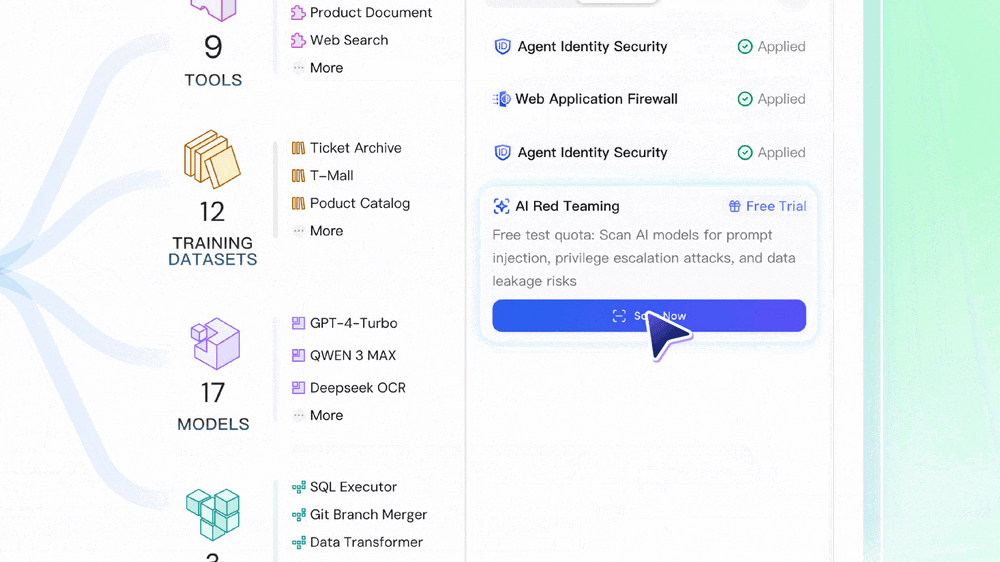
By simulating real-world hacker perspectives through advanced adversarial sample generation, automated multi-turn attack orchestration, and intelligent risk scoring, we enable the evolution from passive defense to active immunity, establishing a robust security foundation for your enterprise agents.
Four core capabilities seamlessly integrated into the Alibaba Cloud Agent Security Center from an Agent-first perspective!
The Agent Security Center inherits Alibaba Cloud's cloud-native security philosophy and best practices accumulated over a decade. It deeply integrates atomic security capabilities into foundational models and the Agent platform, unifying cloud products, platforms, permissions, and interfaces. Guided by an AI-native approach, it achieves a closed loop of end-to-end security—from Agent awareness to risk traceability.
● Agentless Zero-Touch Discovery: Leveraging agentless scanning technology for workloads such as ECS, the system supports second-level classification and identification of 200+ AI/Agent tools/components and 150+ services. This non-intrusive approach requires no plugin installation, eliminating business interference while accurately extracting directory structures and associated scripts, thereby resolving pain points related to high resource consumption.
● Enterprise-Wide Asset Management: Precisely identifies 150+ AI services and 180+ core components, automating the construction of the AI-BOM (Bill of Materials) to ensure complete transparency and visibility of supply chain assets.
● Asset Lineage & Dependency Analysis: Penetrates the invocation hierarchy of Agent assets and components to automatically map dependency relationships. This eradicates hidden "shadow" assets, achieving 100% asset coverage.
● Deep Risk Governance: Integrates 17 Agent configuration risk detection models and a rule library of 2,500+ specialized vulnerabilities. It governs supply chain risks from configuration compliance to code-level vulnerabilities, ensuring AI applications remain secure and controllable.
● Establishing a "Behavior-Content-Identity" Full-Chain Closed Loop: Breaking down data silos by correlating threats across the complete attack chain. By integrating input/output control with identity credential verification, it accurately blocks composite attacks, ensuring the Agent's execution is fully trustworthy and controllable from start to finish.
● Multi-Engine Collaborative Detection: Covers five core capabilities: content safety, prompt injection attacks, sensitive data leakage, malicious URL detection, and full-chain Agent risk detection. It identifies 30+ categories of granular risks in real-time (including jailbreaking, prompt injection, malicious operations, identity bypass, and data poisoning), constructing a seamless security defense for comprehensive risk coverage and efficient interception.
● Fine-Grained Identity & Access Control: Powered by Agent ID Guard, it enforces granular authorization checks on Agent access requests during runtime. This prevents privilege escalation, credential abuse, and loss of control over high-risk operations. It supports seamless integration with 10+ enterprise identity sources, covers dozens of Agent deployment environments (such as on-premise, multi-cloud, and IDC servers/containers), and manages fine-grained permissions for hundreds of common applications.
● Proactive Risk Validation: Conducts continuous, proactive risk validation from Buildtime (development) to Runtime (operations). This breaks the single-point perspective, unifying the discovery and governance of security risks that span the entire lifecycle.
● AI-Driven Intent Recognition: Introduces large model capabilities to perform semantic analysis based on natural language descriptions and logical orchestration. This deeply identifies concealed malicious intents and potential violations that traditional rules cannot detect, endowing the security defense with "cognitive" ability.
● Systematic Adversarial Confrontation: Conducts continuous, automated AI Red Teaming exercises against foundational models and Agents. It supports automated attack testing against 12 types of prompt injection techniques (including role-play jailbreaking, DAN jailbreaking, prompt leakage, obfuscation, and token smuggling) and utilizes 300+ high-quality attack samples, demonstrating a 50%+ success rate in attacking models like DeepSeek.
The true potential of open-source Agents lies not in the fragmentation of isolated deployments, but in the strength of a visible, controllable, and intelligent ecosystem. The Alibaba Cloud Agent Security Center provides the deep transparency required to make every line of code and dependency fully traceable, safely unleashing the full productivity of your AI initiatives.
The Agent Security Center is now available in public beta. Visit the console to start your free trial today.
https://yundun.console.alibabacloud.com/?&p=sas#/agentAsset/overview/cn-hangzhou
Alibaba Cloud's New Launch: Agent ID Guard, Who Will Manage the Identity Security of These "Claws"?
22 posts | 1 followers
FollowCloudSecurity - January 30, 2026
Alibaba Cloud Native Community - October 11, 2025
Justin See - March 20, 2026
Alibaba Cloud Native Community - September 29, 2025
CloudSecurity - April 15, 2026
CloudSecurity - April 9, 2026
22 posts | 1 followers
Follow AgentBay
AgentBay
Multimodal cloud-based operating environment and expert agent platform, supporting automation and remote control across browsers, desktops, mobile devices, and code.
Learn More Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn More Alibaba Cloud for Generative AI
Alibaba Cloud for Generative AI
Accelerate innovation with generative AI to create new business success
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn MoreMore Posts by CloudSecurity