By Cheng Tan
If you are running an AI Agent in a production environment, you may face such a dilemma:
"I want the Agent to use GitHub, but I don't want to give it my PAT" — a leaked token could lead to an attack on the repository.
"I need the Worker to call the internal API, but those keys are too sensitive" — API keys for billing systems, databases, payment gateways... giving them to the Agent poses too much risk.
"Different Workers need different permissions, but managing them is a nightmare" — Should the front-end Worker have access to the production database? Probably not. But how to enforce that?
In version 1.0.6, we introduced a comprehensive solution: Enterprise-level MCP Server management based on Higress AI Gateway + mcporter.
MCP (Model Context Protocol) is an open standard for exposing APIs as tools that AI Agents can discover and call. It can be understood as "OpenAPI for AI Agents" — you don't need to explain each API endpoint to the Agent manually; you only need to define the MCP tool once, and any MCP-compatible Agent can use it immediately.
The beauty of MCP lies in its separation of tool definition and credential management. The schema of the tool explains "what this API does and what parameters it needs", but does not say "this is the API key". This separation is the foundation of enterprise-level secure deployments.
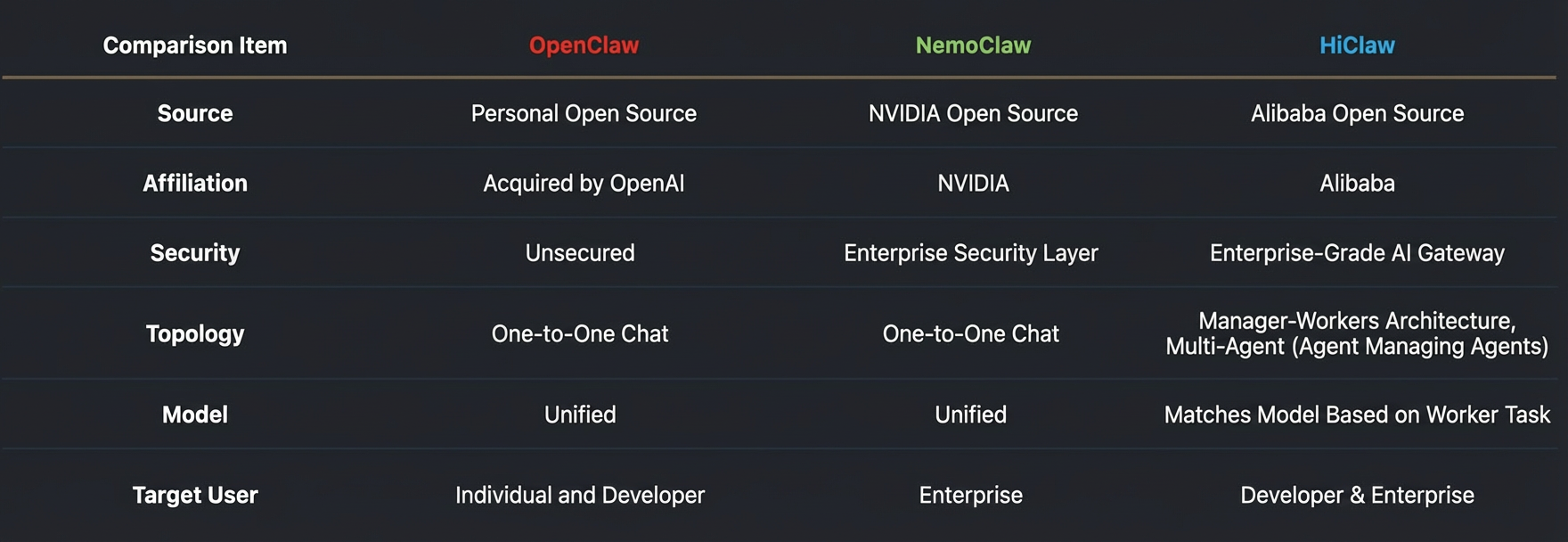
Before delving into the integration with HiClaw, let's introduce mcporter — a powerful MCP toolkit developed by Peter Steinberger (the author of OpenClaw).
mcporter is a TypeScript runtime, CLI, and code generation toolkit. Core capabilities include:
mcporter call server.tool key=value
# List all configured MCP servers
mcporter list
# View tools and full parameter schema for a specific server
mcporter list github --schema
# Invoke a tool
mcporter call github.search_repositories query="hiclaw" limit=5In HiClaw 1.0.6, both the Manager and Worker interact with the MCP server via mcporter — but with key security enhancements provided by Higress AI Gateway.
Before understanding the MCP integration architecture of HiClaw, it is necessary to clarify the relationship between MCP and SKILLS.
HiClaw supports skills.sh for an open SKILLS marketplace and provides support for a Nacos enterprise-built SKILLS marketplace. SKILLS are iterative capability packages aimed at practical scenarios:
MCP is not meant to replace SKILLS, but rather to act as a complement within the SKILLS ecosystem, enabling the rapid conversion of existing APIs into standard tools usable by Agents. The core value of MCP lies in:
With CLI tools like mcporter, HiClaw achieves the reorganization and orchestration of MCP tools, forming iteratively optimized SKILLS:
MCP Tools (Atomic Capabilities)
│
▼ mcporter Orchestration
│
SKILL (Scenario-based Capability Packs)
│
▼ Real-world Execution
│
Iterate & Optimize SKILLsThe best practices for both are:
This complementary relationship achieves the effect of SKILL + MCP being greater than the sum of their parts: enterprises can enjoy the rich capabilities of the open SKILLS marketplace while achieving secure, granular permission control over internal APIs through the MCP gateway.
When you want to add a new API tool for a Worker, the complete process is as follows:
┌─────────────────────────────────────────────────────────────────────────────┐
│ YOU (Human) │
│ │
│ "Add a stock index API: GET https://api.finance.com/v1/index?symbol={symbol}"│
│ "Authenticate via X-API-Key header, here is my key: sk_xxx" │
└────────────────────────────────────┬────────────────────────────────────────┘
│
▼
┌─────────────────────────────────────────────────────────────────────────────┐
│ MANAGER CLAW │
│ │
│ 1. Generate MCP Server YAML configuration based on your description │
│ 2. Run setup-mcp-server.sh stock-index "sk_xxx" --yaml-file /tmp/stock.yaml│
│ 3. Validate with mcporter: mcporter call stock-index.get_index symbol=000001.SH│
│ 4. Notify Worker: "New MCP server 'stock-index' is ready" │
└────────────────────────────────────┬────────────────────────────────────────┘
│
▼
┌─────────────────────────────────────────────────────────────────────────────┐
│ HIGRESS AI GATEWAY │
│ │
│ ┌─────────────────────────────────────────────────────────────────────┐ │
│ │ MCP Server: stock-index-mcp-server │ │
│ │ ├─ Real credentials: sk_xxx (stored securely, never exposed) │ │
│ │ ├─ Tools: get_index(symbol: string) -> stock index data │ │
│ │ └─ Authorized consumers: manager, worker-alice, worker-bob │ │
│ └─────────────────────────────────────────────────────────────────────┘ │
│ │
│ Issue temporary consumer token to Worker │
│ Token can only call authorized MCP servers │
│ Real API key never leaves the gateway │
└────────────────────────────────────┬────────────────────────────────────────┘
│
▼
┌─────────────────────────────────────────────────────────────────────────────┐
│ WORKER CLAW │
│ │
│ 1. Receive notification from Manager │
│ 2. Pull latest mcporter configuration from MinIO │
│ 3. Discover tools: mcporter list stock-index --schema │
│ 4. Test tools: mcporter call stock-index.get_index symbol=000001.SH │
│ 5. Generate SKILL.md based on understanding │
│ 6. Use this tool in subsequent tasks! │
│ │
│ ┌─────────────────────────────────────────────────────────────────────┐ │
│ │ Worker's Perspective: │ │
│ │ ├─ Has: Consumer token (like a "work ID badge") │ │
│ │ ├─ Can: Call stock-index.get_index through the gateway │ │
│ │ └─ Cannot: See the real API key sk_xxx │ │
│ └─────────────────────────────────────────────────────────────────────┘ │
└─────────────────────────────────────────────────────────────────────────────┘As shown in the following figure, you can also directly upload Swagger files for the Manager to analyze
Once the configuration is complete, the Manager can view the tool list under the MCP Server in the Higress console and carry out further permission management
Through the console, you can:
Permission Management Guidelines:
stock-index MCP Server)stock-index.get_index, but cannot call stock-index.update_index)HiClaw 1.0.6 implements security isolation at the MCP Server level based on the open source version, which can meet the permission control needs of most enterprises.
Core Security Principle: Workers never see the real credentials.
Even if the Worker is fully compromised, the attacker can only obtain a consumer token:
Let’s walk through a real scene. You have an internal billing API and want the Worker to query customer data.
In your Matrix room, tell the Manager:
You: I want to add a billing API as an MCP tool.
Endpoint: GET https://billing.internal.company.com/api/v1/customers/{customer_id}
Auth: Bearer token in the Authorization header
Here is the token: Bearer eyJhbGciOiJSUzI1NiIs...The Manager will:
1. Generate the YAML configuration:
server:
name: billing-mcp-server
config:
accessToken: "" # Manager replaces this with your actual token
tools:
- name: get_customer
description: "Retrieve customer details by ID"
args:
- name: customer_id
description: "Customer ID (e.g., CUST-12345)"
type: string
required: true
requestTemplate:
url: "https://billing.internal.company.com/api/v1/customers/{{.args.customer_id}}"
method: GET
headers:
- key: Authorization
value: "Bearer {{.config.accessToken}}"2. Deploy to Higress MCP Gateway:
setup-mcp-server.sh billing "eyJhbGciOiJSUzI1NiIs..." --yaml-file /tmp/mcp-billing.yaml3. Validate with mcporter:
mcporter list billing --schema
mcporter call billing.get_customer customer_id=CUST-123454. Notify relevant Workers:
Manager: @alice @bob New MCP server `billing` is now configured with the `get_customer` tool.
Please use the file-sync skill to pull the updated configuration, then use the
mcporter skill to discover and learn the new tool.Worker Alice:
# Pull the updated configuration from MinIO
hiclaw-sync
# Discover the new tool
mcporter list billing --schema
# Test the tool
mcporter call billing.get_customer customer_id=CUST-12345
# Generate a SKILL for future reference
mkdir -p ~/skills/billing-operations
# ... Write SKILL.md, including tool documentationThen, when you assign tasks:
You: @alice Check if customer CUST-12345 has any overdue bills.
Alice: Let me query the billing system...
mcporter call billing.get_customer customer_id=CUST-12345
Customer: Acme Corp
Status: Active
Overdue: Yes, $4,500 since January 15th
The customer does indeed have an overdue bill.Alice never saw the real API token. She only used a consumer token to call through the gateway.
If you have existing Swagger or OpenAPI format API documentation? Even easier.
You: Here is our product catalog API Swagger documentation:
https://docs.internal.company.com/swagger.json
Authenticated via X-API-Key header. Key: prod_cat_xxx
Manager: I will convert the Swagger documentation into MCP tools...
Found 12 endpoints, creating 12 MCP tools...
Deploying to Higress as the `product-catalog` MCP server.
Testing the first tool... ✓
Testing the second tool... ✓
All tools verified.
@warehouse-team New MCP server `product-catalog` is ready, containing 12 tools.The Manager can read the Swagger/OpenAPI documentation and automatically generate the corresponding MCP server configuration.
Even simpler — just paste the curl command:
You: Add this API call as a tool:
curl -X GET "https://api.shipping.com/v1/track?tracking_id=ABC123" \
-H "X-API-Key: ship_xxx"
Manager: Creating MCP server `shipping` with tool `track_package`...
Deployment and testing complete. @logistics-team can now use `track_package`.One unique feature of HiClaw 1.0.6 is that Workers not only use MCP tools — they write documentation for them.
When a Worker first encounters a new MCP server, it will:
mcporter list --schema
mcporter call commandsThis SKILL becomes the Worker’s permanent reference for that MCP server. Over time, the more the Worker uses the tools, the more they can improve the SKILL based on practical experience:
It’s like having an AI writing its own documentation — and continuously improving it.
Let’s clarify what Workers can and cannot do:
✅ Call any authorized MCP server
✅ Use tools through Higress AI Gateway
✅ Generate and improve SKILL documentation
✅ Work autonomously within authorized scope
❌ See real API keys, tokens, or credentials
❌ Call unauthorized MCP servers
❌ Extract credentials from the gateway
❌ Share credentials with other Workers
This is the zero trust principle for credentials: Agents operate on a need-to-know basis, while they never need to know the real credentials.
This release completes the roadmap planning for "Universal MCP Service Support":
✅ Pre-configured MCP Connectors: GitHub, as well as any custom service via YAML configuration
✅ Custom MCP Integration: Access any HTTP API, documented via Swagger/curl/YAML
✅ Fine-grained Permission Control: Manager authorizes Workers by MCP server
Any MCP-compatible tool can now be safely exposed to Workers, with zero credential leakage.
Version 1.0.6 also introduced universally available slash commands — usable in DMs or group chats:
/reset — Fixes a stuck or misconfigured Claw
You: @alice /reset
Alice: Context cleared. Ready for new tasks.Applicable for:
/stop — Interrupt long-running tasks
You: @bob /stop
Bob: Task interrupted. Here is what I was working on:
- Analyzed 45% of the codebase
- Found 3 potential issues
- Haven't started the fixes yet
Why did you interrupt me? Do you want me to change direction?Applicable for:
/model — Quickly switch the current session model
You:@manager /model qwen3.5-plus
manager:Model set to qwen3.5-plus (hiclaw-gateway/qwen3.5-plus).Applicable for:
The design principles for file synchronization have been unified: "Writers push and notify, receivers pull on demand"; pulling every 5 minutes serves as a backup. The Manager adds on-demand mc mirror pulls during task/project completion processes to ensure that Workers read the latest results.
Already using HiClaw? Upgrade to the latest version:
bash <(curl -sSL https://higress.ai/hiclaw/install.sh)New to HiClaw? Get started with one command:
# macOS / Linux
bash <(curl -sSL https://higress.ai/hiclaw/install.sh)
# Windows (PowerShell 7+)
Set-ExecutionPolicy Bypass -Scope Process -Force; $wc=New-Object Net.WebClient; iex $wc.DownloadString('https://higress.ai/hiclaw/install.ps1')After installation, open Element Web at http://127.0.0.1:18088 and tell your Manager to add some MCP tools!
We are continuously improving HiClaw. Coming soon:
Join our community: Discord | DingTalk

706 posts | 57 followers
FollowAlibaba Cloud Native Community - April 22, 2026
Alibaba Cloud Native Community - April 3, 2026
Alibaba Cloud Native Community - April 10, 2026
Alibaba Cloud Native Community - March 25, 2026
Alibaba Cloud Native Community - March 5, 2026
Alibaba Cloud Native Community - April 30, 2026

706 posts | 57 followers
Follow Container Compute Service (ACS)
Container Compute Service (ACS)
A cloud computing service that provides container compute resources that comply with the container specifications of Kubernetes
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn More API Gateway
API Gateway
API Gateway provides you with high-performance and high-availability API hosting services to deploy and release your APIs on Alibaba Cloud products.
Learn More AgentBay
AgentBay
Multimodal cloud-based operating environment and expert agent platform, supporting automation and remote control across browsers, desktops, mobile devices, and code.
Learn MoreMore Posts by Alibaba Cloud Native Community