RDS Supabase is a managed Supabase service provided by ApsaraDB RDS for PostgreSQL. You can use this service to quickly build backend services on ApsaraDB RDS for PostgreSQL for various scenarios, such as minimum viable product (MVP) validation, AI application development, and software-as-a-service (SaaS) platforms.
Features
What is Supabase?
Supabase is an open source Backend as a Service (BaaS) platform that provides developers with features similar to Firebase. Supabase is fully open source and supports self-hosting. Built on PostgreSQL, the platform provides core backend services, including a database, authentication, object storage, and real-time data synchronization, making it ideal for developers who need to quickly build application backends.
Supabase provides a complete set of backend features required to build applications. You can use the entire suite or select only the components you need.
The core capabilities of Supabase include Database, Authentication and Authorization, Object Storage, Edge Functions, Realtime, Vector, and Artificial Intelligence (AI).
Core capabilities of RDS Supabase
Built on the core of open source Supabase, RDS Supabase provides the main Supabase features and is optimized for the cloud-native infrastructure of ApsaraDB RDS for PostgreSQL.
Database
Provides standard PostgreSQL capabilities and additional Plugins. It also supports proprietary ApsaraDB RDS for PostgreSQL Plugins. For example, you can build AI applications by using Supabase with the rds_ai Plugin.
Supports auto-generated Data APIs, including CRUD, RESTful, and GraphQL APIs.
Authentication
Provides a complete user management system that supports multiple authentication methods and can be used as a standalone feature.
Object Storage
The Object Storage service can directly connect to the RDS cold storage service, which is built on Alibaba Cloud Object Storage Service (OSS).
Fully compatible with the Alibaba Cloud OSS protocol, allowing seamless integration of applications with Alibaba Cloud OSS.
Supports advanced features such as resumable uploads and storage compression.
Realtime
Synchronizes data changes in real time across all connected clients.
Stores and synchronizes the online status of all users across all clients.
Supports channel subscription and broadcast functions.
Vector and AI
Vector service
Uses the built-in rds_pgvector Plugin to store, index, and access Embeddings.
Stores vector data and transactional data in the same database to simplify applications and improve performance.
API integration
Easily connects to any Large Language Model (LLM) or Embeddings API, including Hugging Face and SageMaker.
AI assistant
Provides built-in Bailian tokens, so you can use Qwen for LLM services directly.
Use cases
Minimum viable product (MVP)
Helps entrepreneurs and independent developers quickly release a viable version of their application to accelerate time-to-market.
After prototyping is complete, you can quickly generate backend services by simply configuring the table structure.
You can quickly integrate Supabase features such as authentication and message subscription to significantly improve product development efficiency.
AI application development
The combination of RDS Supabase and PostgreSQL provides a one-stop solution for AI application development.
ApsaraDB RDS for PostgreSQL provides multi-modal data storage and retrieval capabilities based on rds_pgvector.
RDS Supabase provides API endpoints for the application.
You can use the rds_ai Plugin to quickly integrate model services from Bailian and Platform for AI (PAI).
SaaS platforms
With RDS Supabase, you can help business teams rapidly develop internal platforms. This helps enterprises monitor project data in real time, collaboratively manage content assets, and improve cross-departmental collaboration.
Prerequisites
To use this feature as a RAM user, you must grant the user the following permissions. For information about how to grant permissions, see Grant permissions to a RAM user.
AliyunRDSAIReadOnlyAccess or AliyunRDSAIFullAccess: Permissions to read or manage AI application development in ApsaraDB RDS.
AliyunVPCFullAccess: Permissions to manage a Virtual Private Cloud (VPC).
AliyunRDSFullAccess: Permissions to manage ApsaraDB RDS.
AliyunRAMReadOnlyAccess: Read-only permissions for Resource Access Management (RAM), granting permission to view user, group, and authorization information.
Billing
ApsaraDB RDS for PostgreSQL instance fees
When you create an RDS Supabase project, you must create an ApsaraDB RDS for PostgreSQL instance within the project. You are charged for the RDS instance specifications and storage space. The billing method is the same as that for the RDS Supabase project.
Internet NAT Gateway and EIP fees
When you create an RDS Supabase project and enable the public NAT feature, you are charged on a Pay-as-you-go basis for the Internet NAT Gateway and Elastic IP Address (EIP).
The General-purpose Supabase service platform is free of charge. You are only charged for RDS PostgreSQL instance fees, Internet NAT Gateway fees, and EIP fees on a pay-as-you-go basis.
Limitations
Only PostgreSQL 17 and later major versions are supported.
Do not delete or modify the databases and associated accounts that are automatically created by the RDS Supabase project, as doing so will make the project unavailable.
Create an RDS Supabase project
Go to the RDS console homepage, and in the left navigation bar, click AI Application Development.
After you select a region at the top, on the RDS Supabase page, click Create Project.
In the panel that appears, configure the RDS Supabase parameters.
Parameter
Description
RDS Supabase Project Name
Enter a name for the RDS Supabase project.
Region
The region where the RDS Supabase project resides.
Public NAT
Enable the Internet NAT Gateway. You must enable this service when you need to use an external custom model that is accessed over the internet in the RAG Agent.
ImportantIf you have already configured an Internet NAT Gateway for the vSwitch in the RDS Supabase project network, do not enable this option. You can check whether an Internet NAT Gateway is enabled for the corresponding vSwitch in the NAT Gateway console.
If you enable the Internet NAT Gateway, this action automatically binds an EIP and incurs fees for both the NAT Gateway and the EIP.
VPC
Select the Virtual Private Cloud (VPC) for the RDS Supabase project.
If you have an existing VPC that meets your network planning needs, you can select it directly.
If you do not have a suitable VPC, you can use the default VPC and vSwitch. For more information, see VPCs and vSwitches.
If the default VPC and vSwitch do not meet your requirements, create a VPC and vSwitch first. For more information about how to create a VPC and a vSwitch, see VPCs and vSwitches.
Primary Availability Zone and Network
Select the primary zone and vSwitch.
Supabase Type
Currently, only the General Purpose type is supported.
Dashboard username
Dashboard Password
Set the password for the default user supabase.
RAG Agent
Enables RAG Agent.
The RAG Agent includes some built-in models. If you use external custom models that require public internet access, you must enable Public NAT for the Agent.
Billing Method
Supports Subscription and Pay-as-you-go.
Engine
For RDS PostgreSQL in an RDS Supabase project, the only supported engine version is PostgreSQL 17.
SLR Authorization
Authorization is required only on your first use and is free of charge. Click Go to Authorize to authorize the service-linked roles (AliyunServiceRoleForRds and AliyunServiceRoleForRdsPgsqlOnEcs).
Product Family
Select the edition of the ApsaraDB RDS for PostgreSQL instance in the RDS Supabase project.
Basic Edition: Single-node read-only instances that are highly cost-effective and suitable for learning or testing. Fault recovery and restarts take a long time.
High-availability Edition: This edition includes a primary node and a secondary node to provide High Availability (HA) for read-only instances. It is suitable for production environments and recommended for more than 80% of user scenarios.
Instance Category
Select the instance category of the ApsaraDB RDS for PostgreSQL instance in the RDS Supabase project.
General Purpose: Features dedicated memory and I/O, and shared CPU and storage. It offers high cost-effectiveness at a low price.
Dedicated: Provides dedicated memory, I/O, CPU, and storage for superior and stable performance.
NoteThe Basic Edition does not support the Dedicated instance category.
Specifications
Select the instance type of the ApsaraDB RDS for PostgreSQL instance in the RDS Supabase project.
NoteFor supported instance types, see the options available on the console. For more information about instance types, see ApsaraDB RDS for PostgreSQL instance types.
Bucket
Set the storage space for the ApsaraDB RDS for PostgreSQL instance in the RDS Supabase project.
Database password
Set the database password for the ApsaraDB RDS for PostgreSQL instance in the RDS Supabase project.
After you confirm the configuration, click Buy Now.
After the creation is complete, you can view the created projects in the RDS Supabase list.
Log in to the Supabase Dashboard
Go to the RDS console, and in the left-side navigation pane, click AI Application Development.
After you select a region at the top, click the Project ID of the target project in the RDS Supabase list to go to the RDS Supabase details page.
On the Basic Information page, in the IP Address Whitelist section, click Add Whitelist Group to add the IP address of the target client to the IP address whitelist.
NoteIf you have previously configured an IP address whitelist, you can directly click Public Endpoint to go to the Supabase login page.
Click Public Endpoint in the Network Information section to open the Supabase login page.
For more information about how to use Supabase, see Getting Started | Supabase Docs.
NoteIf you log in from an ECS instance in the same VPC as your RDS Supabase project, use the internal connection address.
Click View Details in the Actions column to view the detailed information of the instance on the Basic Information page.
Delete an RDS Supabase project
Go to the RDS console homepage, and in the left navigation bar, click AI Application Development.
After selecting a region at the top, in the RDS Supabase list, click Delete next to the target project.
In the dialog box that appears, click OK.
ImportantDeleting an RDS Supabase project does not automatically delete the ApsaraDB RDS for PostgreSQL instance or the Internet NAT Gateway created with the project. You need to manually release the instance, and delete the Internet NAT Gateway and the EIP.
FAQ
Related documentation and APIs
RDS Supabase SDK User Guide: Describes how to obtain the Supabase URL and Supabase key, and how to use the RDS Supabase SDK in various programming languages.
Related APIs: For APIs related to RDS Supabase, see Supabase API Reference.
Appendix: Get the service API key
Method 1: Using an API call (DescribeInstanceAuthInfo - Query the authentication information of an RDS AI application instance)
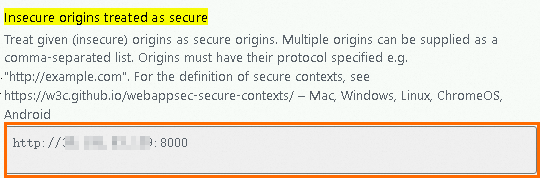
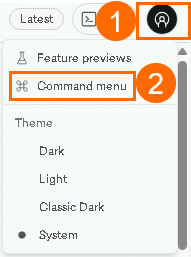
 icon in the upper-right corner, and select Command menu.
icon in the upper-right corner, and select Command menu.