When an enterprise uses multiple Alibaba Cloud accounts across different departments, a unified data protection strategy is needed for centralized management. The cross-account backup feature allows a designated management account to centrally back up and restore data from the cloud resources of other accounts. This isolates source data from backup data at the account level, enabling centralized data protection that meets compliance and auditing requirements. This approach also reduces overall O&M costs and improves efficiency because the management account handles all backup operations. This eliminates the need for users in other accounts to learn the backup system.
How it works
Cloud Backup supports two authorization methods to add an account to be backed up for cross-account backup: one based on Resource Directory and the other on RAM role assumption. The following table describes the working principles and use cases of the two methods.
Add an account by using Resource Directory: Use this method if the management account and the account to be backed up are in the same Resource Directory. The management account must be the management account of the Resource Directory or a delegated administrator account for the Cloud Backup service. The management account can centrally manage member accounts to back up their cloud resources through a simple, visual process. This method is ideal for unified backup scenarios in enterprises that have a multi-account architecture built on Resource Directory. It is also suitable for industries like finance and government that require strong compliance and centralized control.
Add an account via RAM role assumption: Create a RAM role in the account to be backed up and grant permissions to the management account. This allows Cloud Backup to temporarily assume the RAM role in the account to be backed up by using the
AliyunServiceRoleForHbrCrossAccountBackupservice-linked role. This grants Cloud Backup the permissions to access the resources to be backed up. This method is suitable for scenarios where Resource Directory is not used or where temporary authorization through Resource Access Management (RAM) is required for cross-account backup.
Both methods allow the management account to provide unified data protection for the accounts to be backed up. You can use a unified backup policy to back up data from multiple accounts and restore the data to any managed account on demand. Backup jobs and backup data are managed within the management account. The accounts to be backed up do not need to enable or operate the Cloud Backup service. Only the management account can use or delete the backup data, thereby achieving data isolation at the account level.

In a cross-account backup scenario, the management account and the managed accounts to be backed up can perform the following operations:
Resource type | Management account actions | Managed account actions |
ECS instance |
|
|
Other resource types |
|
|
Limitations
You can use the cross-account backup feature for ECS instance backup, ECS file backup, NAS backup, OSS backup, Tablestore backup, ECS database backup, and SAP HANA backup scenarios. For an ECS instance, you can restore backup points only to the account of the source ECS instance. Cross-account restoration is not supported. For specific supported scenarios, refer to the prompts in the Cloud Backup console.
The backup points of an ECS instance belong to the management account, but the generated ECS snapshots are stored in the account to be backed up. Snapshot fees are charged to the account to be backed up. For more information, see Billing.
Cross-account backup does not affect backup performance, data deduplication efficiency, or network transmission speed.
When you configure cross-account backup by using Resource Directory, the management account must be the management account of the Resource Directory or a delegated administrator account for the Cloud Backup service. You can add a maximum of three delegated administrator accounts for the Cloud Backup service.
For information about the supported regions, see Features by region.
Prerequisites
Prepare a management account and at least one account to be backed up.
To configure cross-account backup by using Resource Directory, the management account and the account to be backed up must be in the same Resource Directory. For more information, see Enable a Resource Directory and Invite an Alibaba Cloud account to join a Resource Directory.
Decide whether to configure cross-account backup by using Resource Directory or RAM role assumption based on your business requirements.
Add an account by using Resource Directory
(Optional) Step 1: Set a delegated administrator account
If you use the management account of your Resource Directory as the management account, skip this step.
To use a member account of a Resource Directory as the management account, you must set this account as a delegated administrator account for the Cloud Backup service. For more information, see Manage delegated administrator accounts.
Use the management account of your Resource Directory to log on to the Resource Management console.
In the left-side navigation pane, choose .
On the Trusted Service page, find Cloud Backup and click Manage in the Actions column.
In the Delegated Administrator Account section, click Add.
In the Add Delegated Administrator Account panel, select the desired management account.
Click OK.
After the account is added, Cloud Backup appears in the list of trusted services when you log on to the Resource Management console as the delegated administrator account.
Step 2: Add the member account
Use the management account to log on to the log on to the Cloud Backup console.
In the left-side navigation pane, choose .
On the Cross-account backup page, switch to the region that contains the resources of the account to be backed up.
Click Add an account to be backed up.
In the Add an account to be backed up panel, configure the following parameters and click OK.
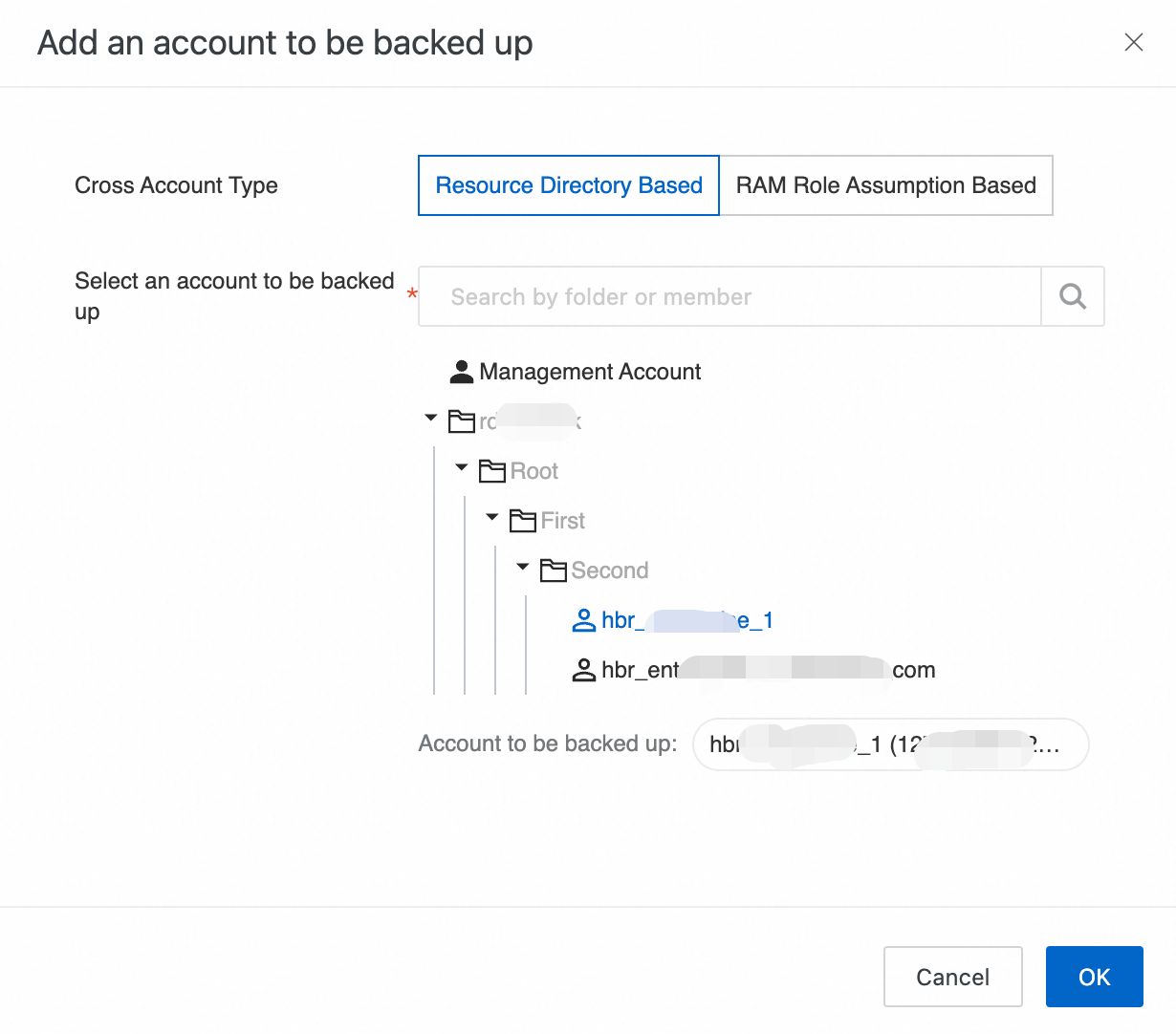
Parameter
Description
Cross-account type
Select Resource Directory-based.
Select an account to be backed up
Select an account to be backed up from the Resource Directory.
You can select only one member account at a time. You can enter a keyword to quickly find the member account.
NoteFor accounts that are in a Resource Directory, we recommend that you configure cross-account backup by using Resource Directory. You can also configure cross-account backup by using RAM role assumption. For more information, see Add an account via RAM role assumption.
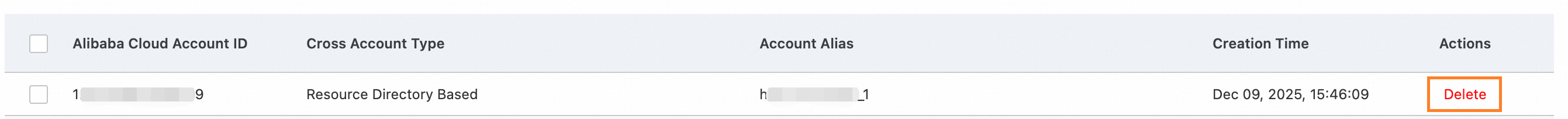
After the account is added, it appears in the account list.
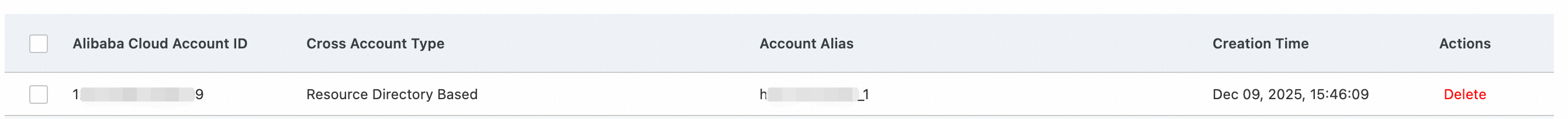 When an account is managed for the first time, Cloud Backup automatically creates the
When an account is managed for the first time, Cloud Backup automatically creates the AliyunServiceRoleForHbrRdservice-linked role:Role name:
AliyunServiceRoleForHbrRdAccess policy:
AliyunServiceRolePolicyForHbrRdPermission description: Allows Cloud Backup to access the resources of other authorized accounts for cross-account backup and restore operations.
The following actions affect cross-account authorization and can cause cross-account backup jobs to fail. Proceed with caution.
Delete the account to be backed up from the cross-account backup list of the management account.
The management account is no longer the management account of the Resource Directory or the delegated administrator account for the Cloud Backup service.
The account to be backed up is removed from the Resource Directory that is managed by the management account.
Delete the
AliyunServiceRoleForHbrRdservice-linked role in the account to be backed up.
Existing backups are not affected. If you want to cancel cross-account backup, see Cancel cross-account backup.
Add an account via RAM role assumption
Step 1: Create a service-linked role
The management account requires the AliyunServiceRoleForHbrCrossAccountBackup service-linked role.
Role name:
AliyunServiceRoleForHbrCrossAccountBackupAccess policy:
AliyunServiceRolePolicyForHbrCrossAccountBackupPermission description: Allows the backup service to access the resources of other authorized accounts for cross-account backup and restore operations.
You need to perform this operation only once when you use the feature for the first time. If you have already granted the authorization, proceed to Step 2.
Use the management account to log on to the Cloud Backup console.
In the left navigation bar, select Backup > Cross-Account Backup.
On the Cross-Account Backup page, switch to the region that contains the resources you want to back up.
Click Add Account to Be Backed Up, and in the Add Account to Be Backed Up panel, set Cross-account Type to Based on RAM role assumption.
In the Cloud Backup Authorization dialog box, click Authorize.
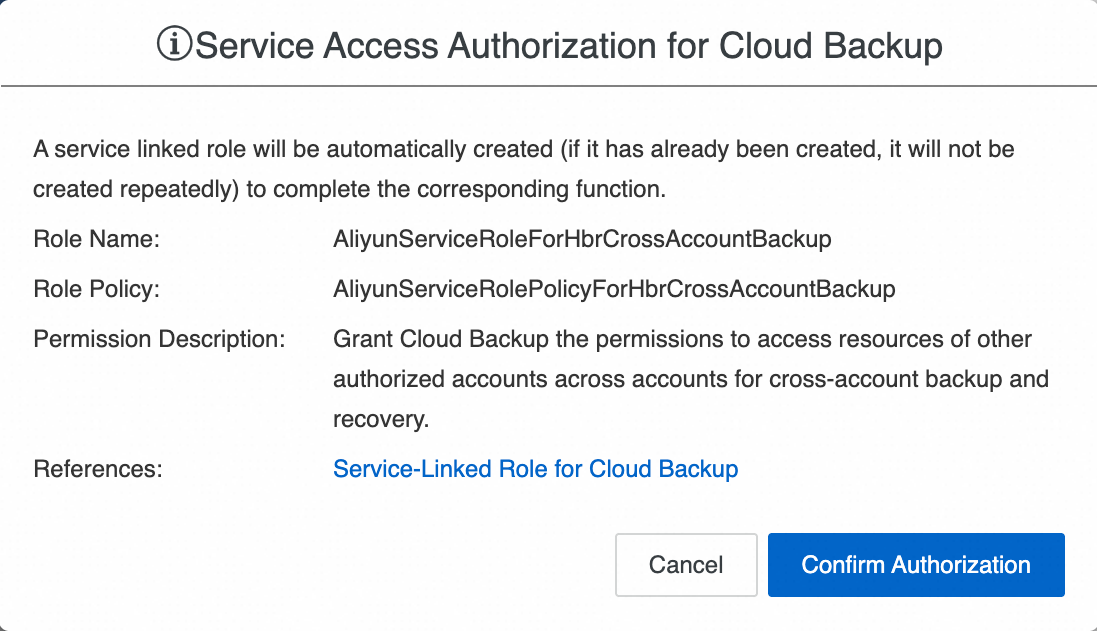 For more information, see Cloud Backup service-linked role.
For more information, see Cloud Backup service-linked role.
Step 2: Create a RAM role
Use the account to be backed up to log on to the RAM console.
In the left-side navigation pane, choose .
On the Roles page, click Create Role.
On the Create Role page, set Principal Type to Cloud Account. Then, set Principal Name to Other Account, enter the ID of the management account, and click OK.
 Note
NoteGo to the Security Settings page to view your Alibaba Cloud account ID.
In the Create Role dialog box, enter a RAM role name, such as
hbrcrossrole, and click OK.
Step 3: Grant permissions to the RAM role
After you create a RAM role, you must attach a system policy or a custom policy to the role. On the Precise Permission page, RAM provides two system policies. Select one of the policies.
AdministratorAccess: Grants the permissions to manage all cloud resources of the destination account.AliyunHBRRolePolicy: (Recommended) Grants the system permissions required by Cloud Backup.The
AliyunHBRRolePolicysystem policy includes the following permissions:{ "Version": "1", "Statement": [ { "Action": [ "nas:DescribeFileSystems", "nas:CreateMountTargetSpecial", "nas:DeleteMountTargetSpecial", "nas:DescribeMountTargets", "nas:DescribeAccessGroups" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "ecs:RunCommand", "ecs:CreateCommand", "ecs:InvokeCommand", "ecs:DeleteCommand", "ecs:DescribeCommands", "ecs:StopInvocation", "ecs:DescribeInvocationResults", "ecs:DescribeCloudAssistantStatus", "ecs:DescribeInstances", "ecs:DescribeInstanceRamRole", "ecs:DescribeInvocations", "ecs:CreateSnapshotGroup", "ecs:DescribeSnapshotGroups", "ecs:DeleteSnapshotGroup", "ecs:CopySnapshot" ], "Resource": "*", "Effect": "Allow" }, { "Action": "bssapi:QueryAvailableInstances", "Resource": "*", "Effect": "Allow" }, { "Action": [ "ecs:AttachInstanceRamRole", "ecs:DetachInstanceRamRole" ], "Resource": [ "acs:ecs:*:*:instance/*", "acs:ram:*:*:role/aliyunecsaccessinghbrrole" ], "Effect": "Allow" }, { "Action": [ "ram:PassRole", "ram:GetRole", "ram:GetPolicy", "ram:ListPoliciesForRole" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "hcs-sgw:DescribeGateways" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "oss:ListBuckets", "oss:GetBucketInventory", "oss:ListObjects", "oss:HeadBucket", "oss:GetBucket", "oss:GetBucketAcl", "oss:GetBucketLocation", "oss:GetBucketInfo", "oss:PutObject", "oss:CopyObject", "oss:GetObject", "oss:AppendObject", "oss:GetObjectMeta", "oss:PutObjectACL", "oss:GetObjectACL", "oss:PutObjectTagging", "oss:GetObjectTagging", "oss:InitiateMultipartUpload", "oss:UploadPart", "oss:UploadPartCopy", "oss:CompleteMultipartUpload", "oss:AbortMultipartUpload", "oss:ListMultipartUploads", "oss:ListParts" ], "Resource": "*", "Effect": "Allow" }, { "Effect": "Allow", "Action": [ "ots:ListInstance", "ots:GetInstance", "ots:ListTable", "ots:CreateTable", "ots:UpdateTable", "ots:DescribeTable", "ots:BatchWriteRow", "ots:CreateTunnel", "ots:DeleteTunnel", "ots:ListTunnel", "ots:DescribeTunnel", "ots:ConsumeTunnel", "ots:GetRange", "ots:ListStream", "ots:DescribeStream", "ots:CreateIndex", "ots:CreateSearchIndex", "ots:DescribeSearchIndex", "ots:ListSearchIndex" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "cms:QueryMetricList" ], "Resource": "*" }, { "Action": [ "ecs:DescribeSecurityGroups", "ecs:DescribeImages", "ecs:CreateImage", "ecs:DeleteImage", "ecs:DescribeSnapshots", "ecs:CreateSnapshot", "ecs:DeleteSnapshot", "ecs:DescribeSnapshotLinks", "ecs:DescribeAvailableResource", "ecs:ModifyInstanceAttribute", "ecs:CreateInstance", "ecs:DeleteInstance", "ecs:AllocatePublicIpAddress", "ecs:CreateDisk", "ecs:DescribeDisks", "ecs:AttachDisk", "ecs:DetachDisk", "ecs:DeleteDisk", "ecs:ResetDisk", "ecs:StartInstance", "ecs:StopInstance", "ecs:ReplaceSystemDisk", "ecs:ModifyResourceMeta" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "vpc:DescribeVpcs", "vpc:DescribeVSwitches" ], "Resource": "*", "Effect": "Allow" }, { "Action": [ "kms:ListKeys", "kms:ListAliases" ], "Resource": "*", "Effect": "Allow" } ] }
The following steps show how to attach the AliyunHBRRolePolicy policy to the hbrcrossrole RAM role.
Use the account to be backed up to log on to the RAM console.
In the left-side navigation pane, choose .
Find the hbrcrossrole RAM role and go to its details page.
On the Permissions tab, click Precise Permission.
In the Precise Permission dialog box, set Permission Type to System Policy, enter AliyunHBRRolePolicy in the Policy Name field, and then click OK.
A success message appears. Click Close.
Modify the trust policy of the RAM role.
On the role details page, click the Trust Policy tab.
Click Edit Trust Policy.
Click the JSON tab and copy the following code to the code editor. Replace management-account-id with the ID of the management account.
This policy grants the management account permission to obtain a temporary token through Cloud Backup to operate on the resources of the account to be backed up.
NoteYou can go to the Security Settings page to view your Alibaba Cloud account ID.
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "RAM": [ "acs:ram::management-account-id:role/AliyunServiceRoleForHbrCrossAccountBackup" ] } } ], "Version": "1" }Click OK.
Step 4: Add the managed account
Use the management account to log on to the Cloud Backup console.
In the left navigation bar, select Backup > Cross-Account Backup.
On the Cross-Account Backup page, switch to the region that contains the resources you want to back up.
ImportantThe management account must add the account to be backed up in the same region as the ECS files, NAS file systems, OSS buckets, Tablestore tables, ECS databases, or ECS instances to be backed up. Otherwise, Cloud Backup cannot find the resources, causing backup plans to be misconfigured or backup jobs to fail.
Click Add an account to be backed up. In the Add an account to be backed up panel, select RAM role assumption-based for Cross-account type, configure the following parameters, and then click OK.
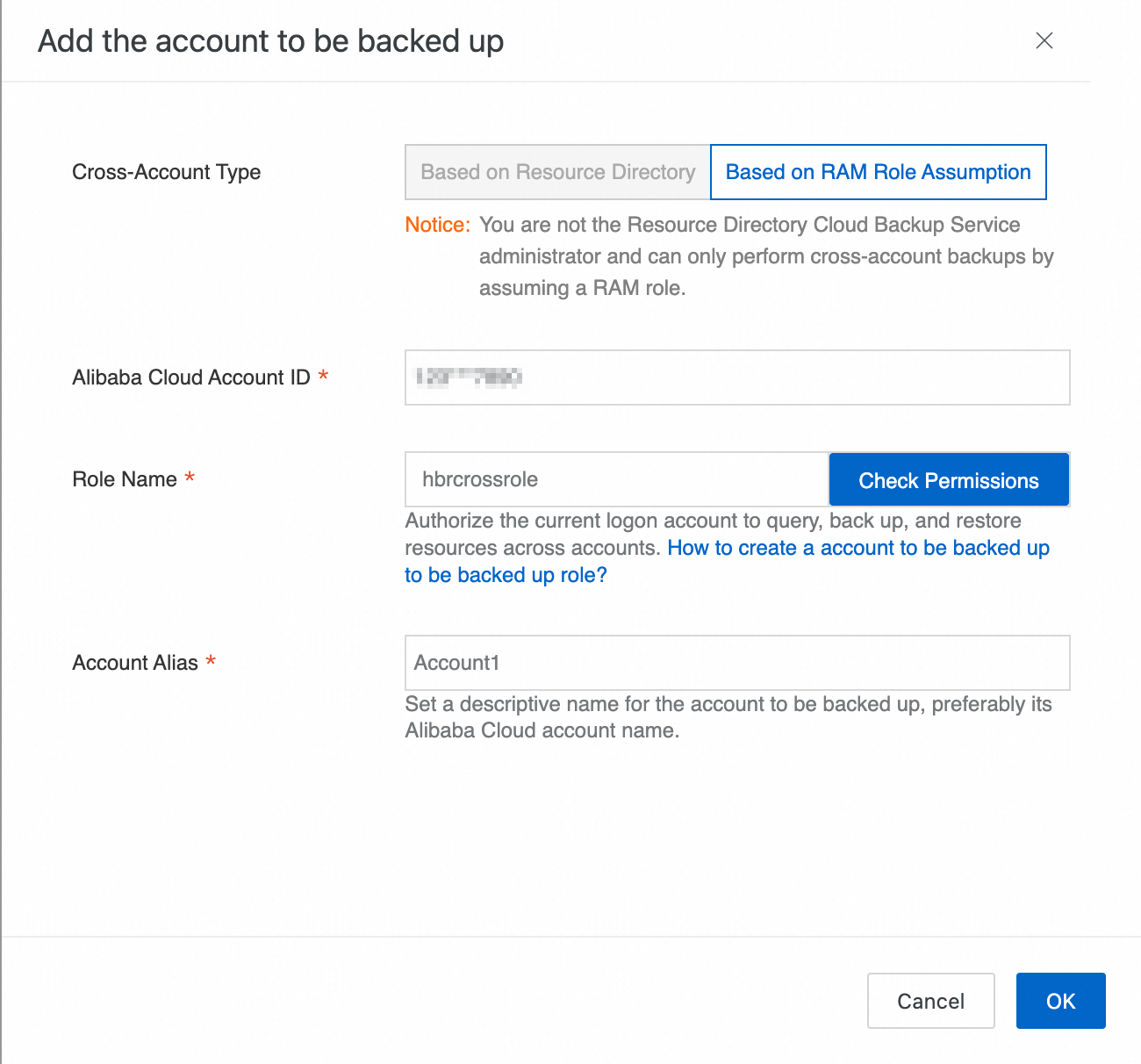
Parameter
Description
Cross-account type
Select RAM role assumption-based. If your accounts are managed by using Resource Directory, we recommend that you see Add an account by using Resource Directory.
Alibaba Cloud Account ID
Enter the Alibaba Cloud account ID. In this case, enter the ID of the account to be backed up.
NoteYou can go to the Security Settings page to view your Alibaba Cloud account ID.
Role Name
Enter the name of the RAM role that you created in the account to be backed up, such as
hbrcrossrole.ImportantClick Check Permissions to verify that the authorization is correctly configured. If an error is reported, check your configuration and try again. If the check is successful, the following message appears: You are authorized to access the resources of this role.
Account Alias
Specify an alias for the account to be backed up to facilitate identification. We recommend that you use the name of the Alibaba Cloud account to be backed up.
After the account is added, it appears in the account list.
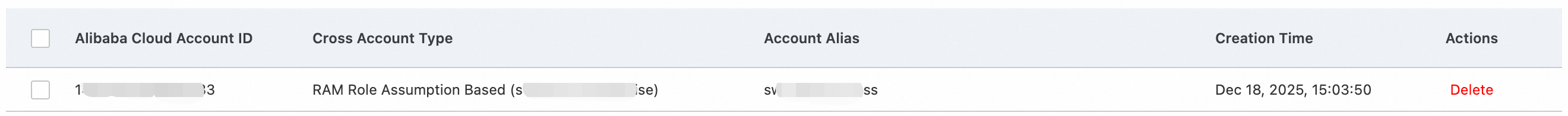
The following actions affect cross-account authorization and can cause cross-account backup jobs to fail. Proceed with caution:
Delete the account to be backed up from the cross-account backup list of the management account.
Delete the
AliyunServiceRoleForHbrCrossAccountBackupservice-linked role in the management account.Delete the RAM role that is used for cross-account backup in the account to be backed up.
The necessary permissions are not granted to the RAM role that is used for cross-account backup in the account to be backed up.
Existing backups are not affected. If you want to cancel cross-account backup, see Cancel cross-account backup.
Configure cross-account backup
After you add an account to be backed up, log on to the console as the management account and switch to the account to be backed up from the account list. Then, you can configure cross-account backup for the resources of the account to be backed up.
Use your management account to log on to the log on to the Cloud Backup console.
In the top navigation bar, select the region where the resources to be backed up are located.
Click Logon Account and select the added account to be backed up.
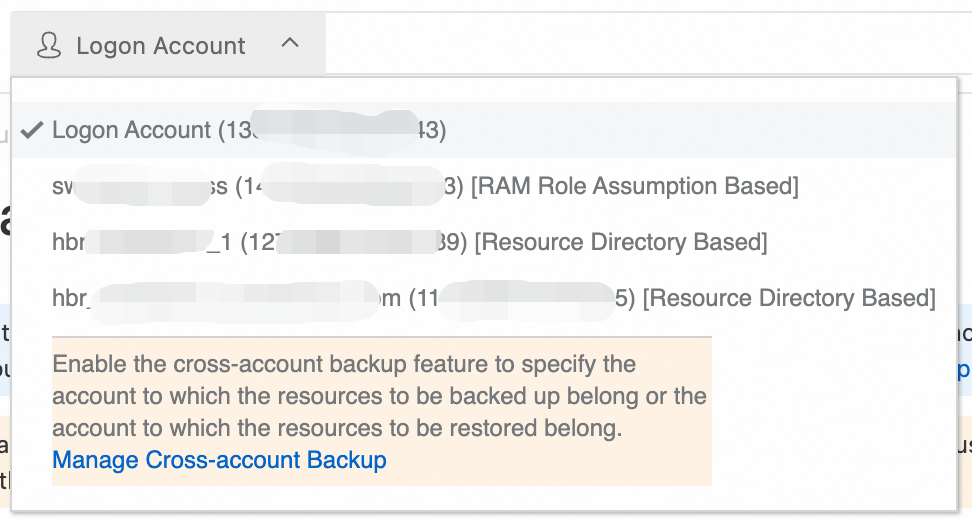
In the left-side navigation pane, select a backup feature to perform a cross-account backup.
ImportantECS file backup, ECS instance backup, NAS backup, OSS backup, Tablestore backup, ECS database backup, and SAP HANA backup support cross-account backup. When you restore an ECS instance from a cross-account backup, you can restore it only to the original Alibaba Cloud account. For specific supported scenarios, refer to the information provided in the Cloud Backup console.
For example, to back up an ECS file, first switch from the current account to the account that contains the target ECS instance. Then, select the ECS instance from the instance list. Create a backup policy or select an existing one and bind it to the ECS instance to configure the backup plan. After the backup job is complete, the ECS file data of the account to be backed up is backed up to the backup vault of the management account.
ImportantA backup vault can store backup data from different accounts at the same time. A backup policy can be bound to data sources from different accounts at the same time to achieve unified data protection for various types of resources across multiple accounts. Before you configure a cross-account backup plan, make sure that all the prerequisites are met.
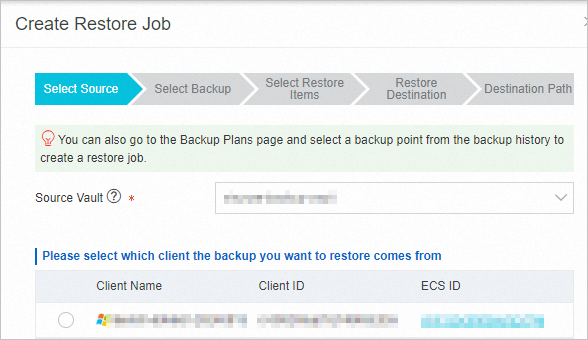
Cross-account restore
The backup vault of the management account stores the backup data of the management account and the accounts to be backed up. You can restore data from any historical backup point in the backup vault to the management account or any account to be backed up. This section describes how to restore data to an account to be backed up.
Switch to the destination account to which you want to restore the backup data.
Create a restore job. The procedure to create a restore job is the same as that for each data source.
Restore an ECS database (Restore a MySQL database, Restore an Oracle database, and Restore an SQL Server database)
Best practices
Cross-account type selection: Choose a suitable cross-account configuration method based on your enterprise account architecture. For multi-account scenarios that are not in a Resource Directory or for cross-enterprise collaboration, we recommend that you configure cross-account backup by using RAM role assumption. For enterprise multi-account architectures that are in a Resource Directory, we recommend that you configure cross-account backup by using Resource Directory to facilitate unified control and permission management.
Least privilege configuration: Use the
AliyunHBRRolePolicysystem policy instead ofAdministratorAccessto prevent security risks from excessive permissions. Grant only the minimum permissions that are required for backup and restore operations. We recommend that you periodically review cross-account backup permissions and promptly revoke permissions that are no longer needed.Region planning: Add cross-account configurations based on the regions where the resources to be backed up are located to ensure backup performance and data transmission efficiency. Prioritize configuring cross-account backup in regions with a high concentration of resources.
Cost control: The cross-account backup feature is free of charge. For more information about other fees, see Billing. Plan your backup policies and retention periods to control storage costs.
Cancel cross-account backup
After canceling cross-account backup, the management account can no longer back up data from the account to be backed up. Evaluate the impacts before you proceed.
If the management account only adds an account to be backed up but does not perform backup or restore operations, no fees are incurred.
After canceling cross-account backup, existing backups are retained in the backup vaults of the management account and can be restored to the current account or other managed accounts. This data continues to occupy storage, and Cloud Backup continues to charge storage fees. If you want to stop billing, see How do I stop being billed for Cloud Backup? Note that you cannot restore data from deleted backups.
Switch to the account to be backed up. For each relevant data source, delete backup plans, uninstall backup clients (if any), unregister instances, and delete backup vaults. For more information, see How do I stop being billed for Cloud Backup?.
Switch to the management account, and on the Cross-account Backup page in the Cloud Backup console, delete the account to be backed up.
If you configured cross-account backup by using Resource Directory, delete the
AliyunServiceRoleForHbrRdservice-linked role in the account to be backed up.Use the account to be backed up to log on to the RAM console.
In the left-side navigation pane, choose .
Find the
AliyunServiceRoleForHbrRdservice-linked role. In the Actions column, click Delete Role and confirm the deletion.
If you configured cross-account backup by using RAM role assumption, delete the RAM role that you created in the account to be backed up.
Use the account to be backed up to log on to the RAM console.
In the left-side navigation pane, choose .
Find the RAM role that you created, such as
hbrcrossrole. In the Actions column, click Delete Role and confirm the deletion.
Billing
Using the cross-account backup feature provided by Cloud Backup is free of charge. However, fees are incurred for backup and recovery. For a detailed description, see the following table. For more information, see Billing methods and billable items.
Managed account resources | Management account charges | Managed account charges |
ECS instance |
|
|
ECS file |
| Fees for resources such as disks that are used after a restore from a backup point |
NAS |
|
|
OSS |
|
|
Tablestore |
|
|
ECS database |
| Fees for resources such as disks that are used after a restore from a backup point |
SAP HANA |
| Fees for resources such as disks that are used after a restore from a backup point |
FAQ
Is cross-account backup free?
The cross-account backup feature is free of charge. However, costs incurred during backup and restore operations are charged to the management account. Snapshot service fees for ECS instance backups and OSS request fees are charged to the account to be backed up. For more information, see Billing.
Cross-account vault replication vs. cross-account backup
Cross-account replication for backup vaults: The source account runs a backup job and generates backup data. The source account then copies the data from its backup vault to another Alibaba Cloud account. As a result, both accounts store a copy of the backup data. This achieves data redundancy and allows the data to be used across accounts.
Cross-account backup: The management account applies backup policies to the accounts to be backed up. The backup data from these accounts is centrally stored in the backup vaults of the management account. The management account can use the backup data to perform on-demand restore operations. This achieves unified management of backup data. The accounts to be backed up cannot view or manage their backed up data.
Both methods support account-level data isolation for accounts inside and outside a Resource Directory, making them widely used for enterprise data security and compliance. Choose the appropriate method. You can also combine the two methods to achieve both unified management and redundancy of backup data.