OpenYurt, the industry's first non-intrusive cloud-native edge computing platform, has recently released v1.2.0. It continues to focus on Kubernetes features such as non-intrusiveness, full collaboration between cloud edge and end, and cross-network domain communication. OpenYurt also deeply builds the continuous delivery and efficient operation and maintenance management capabilities of OpenYurt and Kubernetes to realize massive edge computing services.
Kubernetes, as the most fundamental project in cloud-native computing, has gained wide recognition from developers and enterprises, and has triggered enthusiasm for participation. OpenYurt extends cloud-native technology to edge scenarios, which are complex and diverse, posing challenges for most developers to use and participate in the OpenYurt project. Among these challenges, the installation and deployment of OpenYurt has become a difficult problem for cloud-native practitioners, community participants, and developers.
OpenYurt v1.2.0 further optimizes the installation process of OpenYurt without modifying the configurations of native Kubernetes. It implements a cloud-native edge computing platform based on Kubernetes and OpenYurt, allowing for the management of edge devices and computing power in a cloud-native manner.
In the version of OpenYurt v1.2.0, the installation and deployment process has been optimized.The original ten-step process has been reduced to five steps, as shown in the figure. The numerous special configuration processes for native Kubernetes components in the original process have been streamlined. In the latest version, there is no need to adjust the configuration of native Kubernetes components.
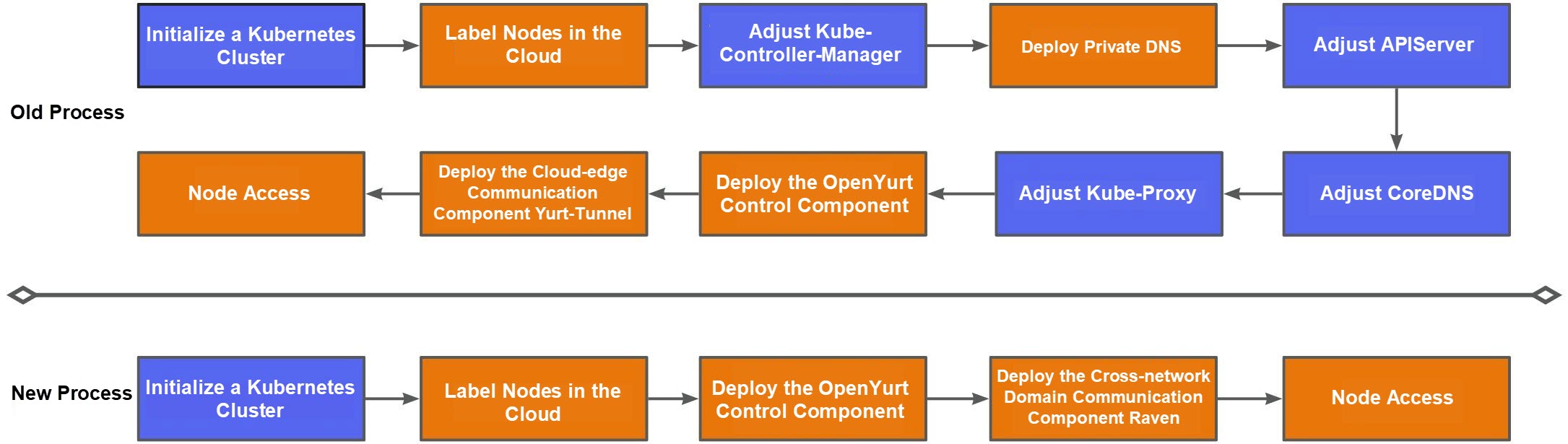
The new installation and deployment steps are as follows.
For more information about how to deploy OpenYurt, see Installation.
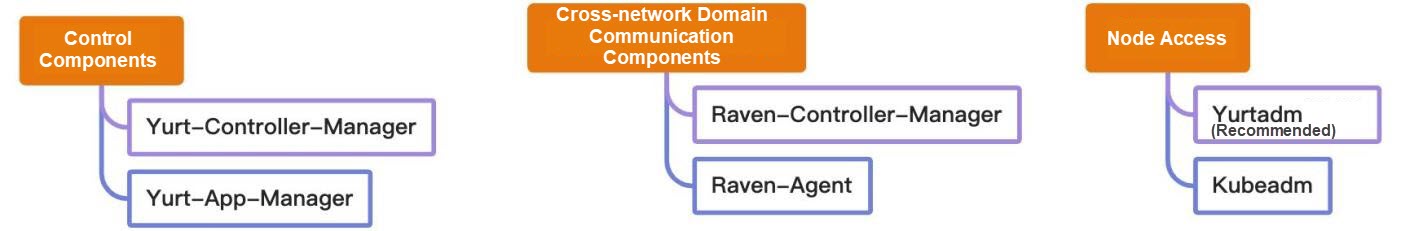
The features of Raven in v1.2 have been further improved. The deployment process for monitoring Prometheus and MetricsServer is the same as the installation and deployment process for native Kubernetes clusters. Yurt-Tunnel and CoreDNS no longer depend on special configurations. However, compared to native Kubernetes, there is a difference in the way data is transmitted. As shown in the figure, monitoring metric data from the cloud to the gateway or a separate edge node is communicated through the VPN tunnel built by Raven. Monitoring data of common nodes is forwarded to the gateway node and transmitted to the observation and monitoring component of the cloud through the VPN tunnel.
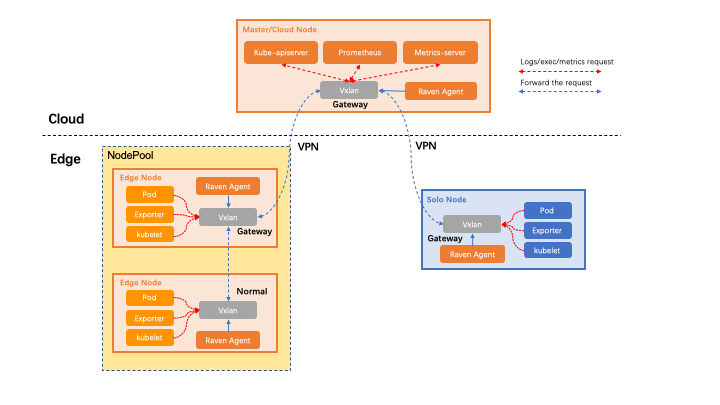
Despite the differences in data transmission methods, the installation and deployment of Prometheus still maintain the simplicity of native Kubernetes. For instance, kubelet metrics are collected through 10255 read-only ports, and you can directly add the configuration to obtain these metrics. By modifying the label rule to collect information from 10255 read-only ports through the HTTP protocol, the installation and deployment of Prometheus can be completed.
- job_name: 'kubelet'
kubernetes_sd_configs:
- role: node
scheme: https
tls_config:
ca_file: /var/run/secrets/kubernetes.io/serviceaccount/ca.crt
insecure_skip_verify: true
authorization:
credentials_file: /var/run/secrets/kubernetes.io/serviceaccount/token
relabel_configs:
- action: labelmap
regex: __meta_kubernetes_node_label_(.+)
- source_labels: [__address__]
action: replace
target_label: __address__
regex: ([^:;]+):(\d+)
replacement: ${1}:10255
- source_labels: [__scheme__]
action: replace
target_label: __scheme__
regex: https
replacement: httpNacos 2.2.2: Optimize Startup Experience and Authentication Tips
Distributed End-to-End Tracing Analysis of Message Queue for Apache RocketMQ x OpenTelemetry

707 posts | 57 followers
FollowAlibaba Cloud Native Community - May 4, 2023
Alibaba Developer - March 30, 2022
Alibaba Cloud Native Community - August 17, 2022
Alibaba Cloud Native Community - May 4, 2023
Alibaba Cloud Native Community - July 17, 2023
Alibaba Cloud Native Community - January 9, 2023

707 posts | 57 followers
Follow Cloud-Native Applications Management Solution
Cloud-Native Applications Management Solution
Accelerate and secure the development, deployment, and management of containerized applications cost-effectively.
Learn More Super Computing Cluster
Super Computing Cluster
Super Computing Service provides ultimate computing performance and parallel computing cluster services for high-performance computing through high-speed RDMA network and heterogeneous accelerators such as GPU.
Learn More ApsaraDB for MyBase
ApsaraDB for MyBase
ApsaraDB Dedicated Cluster provided by Alibaba Cloud is a dedicated service for managing databases on the cloud.
Learn More Container Service for Kubernetes
Container Service for Kubernetes
Alibaba Cloud Container Service for Kubernetes is a fully managed cloud container management service that supports native Kubernetes and integrates with other Alibaba Cloud products.
Learn MoreMore Posts by Alibaba Cloud Native Community
Dikky Ryan Pratama July 1, 2023 at 3:49 pm
awesome!