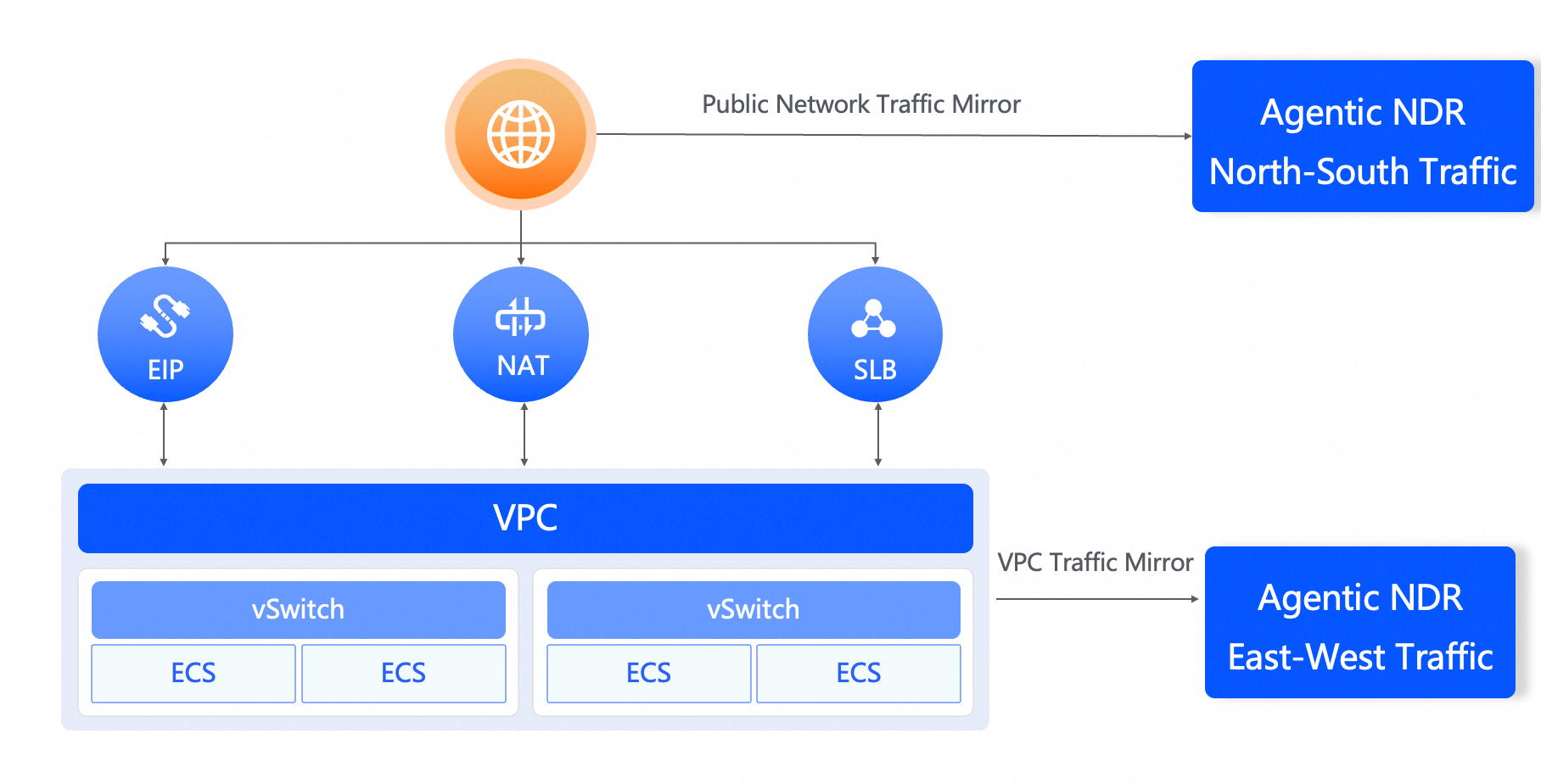
Agentic NDR is a cloud-native Network Detection and Response (NDR) product for the public cloud. Using out-of-band traffic mirroring, it detects and responds to advanced network threats through traffic filtering, full traffic retention, threat correlation, and threat analysis—serving as the final line of defense for your cloud assets.
Agentic NDR positioning
What Agentic NDR detects
Agentic NDR is built for threats that evade conventional security tools:
Advanced Persistent Threats (APTs) — multi-stage attacks that spread indicators across multiple packets over time
Sensitive data exposure — AccessKey IDs, AccessKey Secrets, data transmitted in plaintext, weak passwords, and personal identity information leaking from your assets
Successful intrusions — confirmed by inspecting both request and response traffic, not just inbound probes
Stealthy malware activity — behaviors that match no single signature rule but are surfaced by correlating signals across multiple detection engines
Internet-exposed blind spots — assets with high-risk ports or weak passwords discovered through full-traffic visibility
How it works
Agentic NDR mirrors full bidirectional traffic out-of-band, leaving your workloads untouched. The mirrored traffic flows through a pipeline of detection engines that run asynchronously:
Traffic collection — Raw packets are captured via out-of-band traffic mirroring without affecting production traffic.
Bidirectional threat detection — Both request and response packets are analyzed. Inspecting response packets confirms whether an attack succeeded, reducing false positives from probes that never landed.
Multi-engine correlation — Signature rules, threat intelligence, file sandboxing, behavioral analysis, and exposure analysis run in parallel. When one engine flags an event, the others cross-check it. This catches stealthy activity that bypasses any single engine.
Selective packet retention — Only traffic from attack windows that trigger alerts is retained. Traffic that poses no risk is discarded, keeping storage costs low.
Protocol log delivery — Protocol logs from protected assets are collected, indexed, analyzed, and delivered within seconds for search, analysis, and compliance reporting.
Feature overview
| Feature | What it does | Technical highlights |
|---|---|---|
| Asset and risk management | Identifies business services and surfaces internet-exposed blind spots | Covers web, database, email, file management, and remote control; detects high-risk ports, weak passwords, and sensitive data exposure |
| Automatic retention of attack packets | Retains raw traffic from alert-triggering windows; discards all other traffic | Minimizes storage costs; enables online payload analysis for post-incident forensics on APTs |
| Bidirectional and asynchronous full-traffic threat detection | Analyzes both request and response packets to confirm attack success | Eliminates false positives from one-way inspection; detects multi-packet indicators too weak to trigger single-packet rules |
| Correlated analysis across multiple detection engines | Runs signature rules, threat intelligence, file sandboxing, behavioral analysis, and exposure analysis in parallel | Cross-checks evidence across engines; surfaces stealthy activity that bypasses static rules or matches only low-severity rules |
| Search, filter, and deliver protocol logs | Collects, indexes, analyzes, and delivers protocol logs within seconds | Supports MLPS compliance and traffic audit requirements |
Asset and risk management
Agentic NDR automatically identifies the business services running on your cloud assets across a wide range of categories: web, database, email, file management, and remote control. Full-traffic visibility surfaces internet-exposed blind spots and assets with high-risk ports or weak passwords. Targeted, scenario-based remediation covers sensitive data exposure including AccessKey IDs, AccessKey Secrets, data transmitted in plaintext, weak passwords, and personal identity information.
Automatic retention of attack packets
Raw traffic from any attack window that triggers an alert is retained automatically—traffic that poses no risk is not. This selective retention minimizes both manual effort and storage costs. The retained packets are available for online payload analysis, letting O&M engineers trace incidents and analyze attack patterns directly in the console. This capability is particularly suited to high-security scenarios such as critical event protection and adversarial engagements, where post-incident forensics on APTs is essential.
Bidirectional and asynchronous full-traffic threat detection
Agentic NDR mirrors full bidirectional traffic and performs asynchronous threat detection on both directions. Analyzing response packets confirms whether an attack was successful, rather than flagging every probe as an incident. For attacks where indicators are spread across multiple packets—too weak in any single packet to trigger a rule—correlating signals across the full traffic stream makes detection possible. This approach covers the blind spots left by inspecting only inbound traffic.
Correlated analysis across multiple detection engines
Multiple detection engines run simultaneously: signature rules, threat intelligence, file sandboxing, behavioral analysis, and exposure analysis. When a traffic flow matches an Intrusion Detection System (IDS) rule, the service automatically cross-checks it with threat intelligence, behavioral analysis, and file reconstruction. This correlation of evidence improves alert accuracy. Stealthy activities that bypass static rule detection or match only low-severity rules are surfaced when other engines pick up the signal.
Search, filter, and deliver protocol logs
Protocol logs from protected assets are collected in real time, searched, analyzed, and delivered within seconds. This gives you continuous visibility into network activity and supports MLPS compliance and traffic audit requirements.