The log ingestion policy of Agentic SOC needs to be bound with standardized ingestion rules. The standardized rules use SPL syntax and datasets of Simple Log Service to parse logs.
Standardized rule sources
Standardized ingestion rules use SPL syntax to map incoming logs to datasets, extract key field information from logs, and provide data support for subsequent log parsing rules to generate alert information.
Rule source | Description | Supported operations |
Predefined |
| View |
Custom |
|
|
Operations on standardized rules
Prerequisites
You have purchased and activated Agentic SOC. For specific operations, see Purchase and activate Agentic SOC.
Create custom standardized rules
Log on to the Security Center console. In the upper-left corner of the console, select the region where your assets to be protected are located: China or Outside China.
In the navigation pane on the left, choose . On the Standardized Rule tab, click Create Custom Rule in the upper-left corner.
You can refer to the following information to complete the basic configuration.
Parameter
Description
Rule Name
User-defined
Service Provider
Predefined vendors: Alibaba Cloud, Fortinet, Chaitin Tech, Microsoft, Sangfor, Tencent Cloud, Huawei Cloud, Hillstone Networks, Knownsec, Microsoft Cloud, and others.
User-defined manufacturers: For how to create manufacturers, see Step 1: Add a product.
Product
Automatically pulls all products under the manufacturer, such as Alibaba Cloud Security Center, Fortinet Firewall, etc. For products supported by Agentic SOC, see Integration Center.
Standardization Category or Structure
Standardization Classification: Network Log, Host Log, Security Log, Audit Log, Snapshot Log, Logon Log, Other Log.
Standardization Structure:
A standardization classification contains multiple standardization structures.
A standardization structure corresponds to a set of standardized fields and a dataset (StoreView). A dataset can be mapped to multiple standardization structures.
NoteFor how to view the dataset and standardized fields corresponding to the standardization classification/structure, see Dataset description.
Remarks
You can add feature descriptions to the current standardized rule to facilitate quick search and improve readability.
Set SPL syntax and perform log standardization testing.
Select data source: Select the data source that the custom rule needs to analyze.
Fill in SPL syntax.
You can use predefined rules and existing custom rules as templates. You can view the SPL syntax corresponding to these rules on the details page.
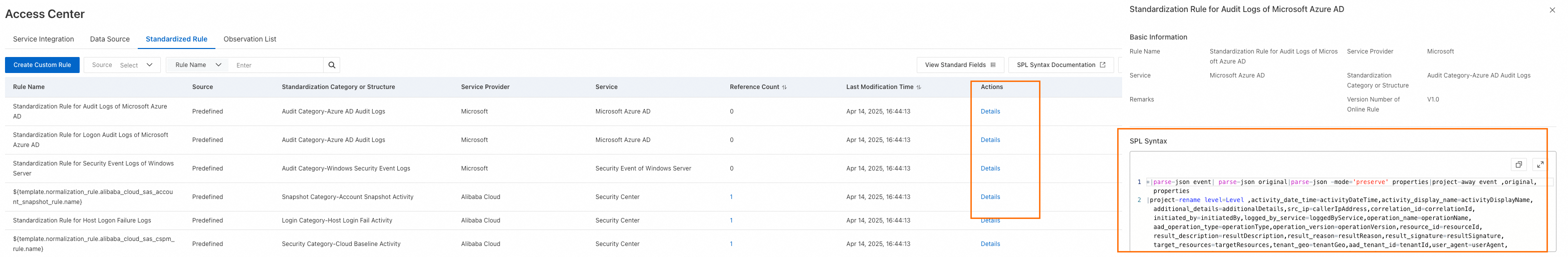
You can also refer to the SPL syntax documentation to write your own custom syntax.
Perform standardization testing.
WarningIf the current data source has no data, the SPL syntax will not be able to parse logs and return results, which will prevent you from selecting test data and completing the standardization test.
Click the
 button, select a test data, and click Parse and Test.
button, select a test data, and click Parse and Test.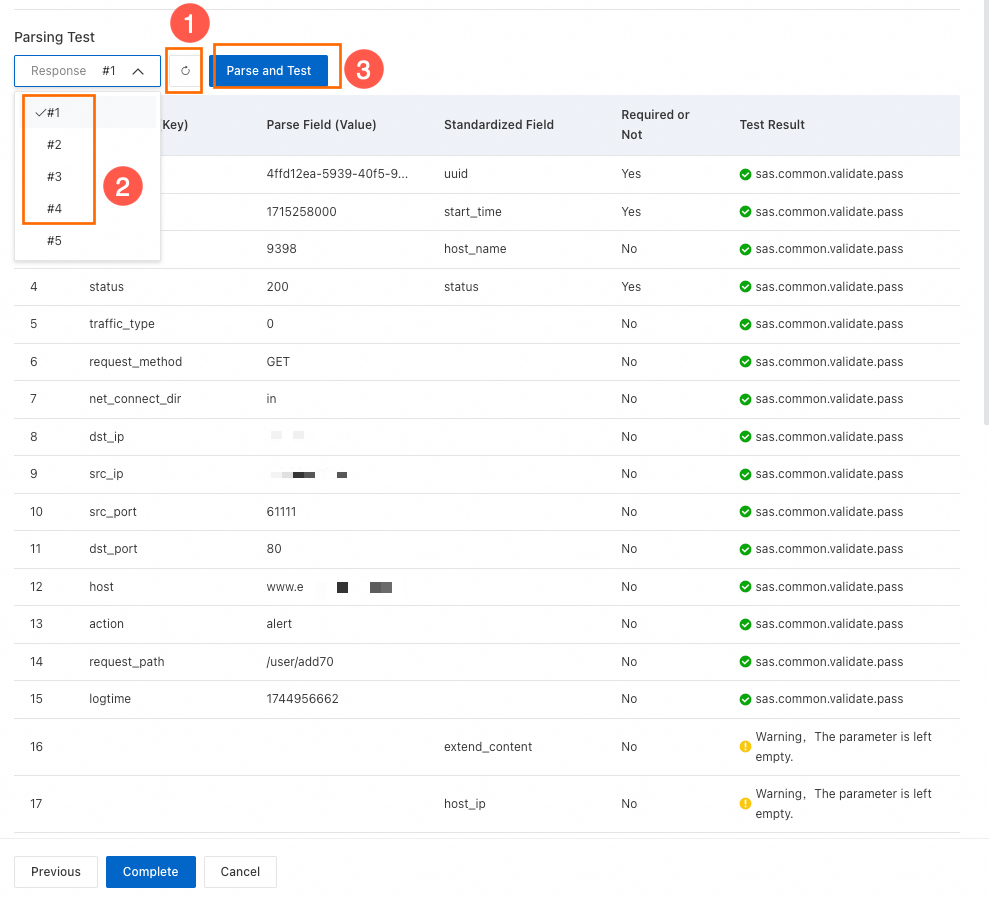
After the test is passed, click Complete in the lower-left corner.
Modify standardized rules
Only custom rules support modification.
Log on to the Security Center console. In the upper-left corner of the console, select the region where your assets to be protected are located: China or Outside China.
In the navigation pane on the left, choose .
Find the rule you want to modify and click the Edit button in the Actions column.
Modify the relevant content on the edit page. The configuration items that can be modified are as follows:
Basic settings: rule name, remarks.
SPL syntax: After modifying the SPL syntax, you still need to perform log standardization testing. For specific operations, see Set SPL syntax and perform log standardization testing.
Delete standardized rules
Predefined rules cannot be deleted.
Standardized rules that have been bound to access policies cannot be deleted.
Log on to the Security Center console. In the upper-left corner of the console, select the region where your assets to be protected are located: China or Outside China.
In the navigation pane on the left, choose .
Find the rule you want to delete and click the Delete button in the Actions column.
Dataset description
Dataset Storeview is a virtual resource created based on Logstore, used to manage and save the relationships between multiple Logstores. Through datasets (Storeview), you can perform unified queries on logs in different Logstores, but datasets (Storeview) do not support modification operations on logs.
Description of the relationship between standardized rules and datasets
Standardized rules need to configure Standardization Category or Structure. Each standardization classification contains multiple standardization structures, and each structure corresponds to a storage dataset (StoreView) and a set of standardized fields. A dataset (StoreView) is also mapped to multiple standardization structures. The relationship can be referred to in the following figure:

Impact on product integration
During product integration, Agentic SOC parses product logs according to SPL syntax based on the data standard fields in the dataset, then matches threat detection rules, and finally identifies security risks. In addition, datasets will have the following configuration restrictions on access policies:
If a dataset (StoreView) has already been bound to 5 access policies in scan query mode, the standardization method for new policies can only be "Real-time Consumption" and does not support "Scan Query". For an explanation of standardization methods, see Product logs.
View datasets
Common datasets are as follows:
Standardization classification | Standardization structure | Dataset name |
Network Log | 5-tuple Log | network_activity |
DNS Log | ||
HTTP Log | ||
Host Log | Process Network Connection Log | process_activity |
Process File Write Log | ||
Process Startup Log | ||
Process DNS Request Log | ||
Security Log | API Security Risk Log | risk_activity |
Cloud Service Baseline Log | ||
Host Baseline Log | ||
Cloud Platform Operation Alert Log | alert_activity | |
API Security Alert Log | ||
Endpoint Detection and Response Alert Log | ||
Firewall Alert Log | ||
Host Network Alert Log | ||
Alert logs of WAF | ||
Other Alert Log | ||
Crawler Alert Log | ||
Vulnerability Log | vulnerability_activity | |
Audit Log | Bastionhost Audit Log | audit_activity |
NoSQL Database Audit Log | ||
Cloud Platform Operation Audit Log | ||
Audit logs of Kubernetes resources | ||
Windows Security Event Log | ||
API Gateway Audit Log | ||
SQL Database Audit Log | ||
Object Storage Service Audit Log | ||
Azure Active Directory Audit Log | ||
Azure Active Directory Logon Log | ||
Snapshot Log | Account Snapshot | account_activity |
Process Startup Snapshot | process_activity | |
Network Connection Snapshot | ||
Logon Log | Cloud Platform Logon Log | login_activity |
Host Logon Failure Log | ||
Host Logon Log |
If you want to view more dataset information, you can refer to the following steps.
Log on to the Security Center console. In the upper-left corner of the console, select the region where your assets to be protected are located: China or Outside China.
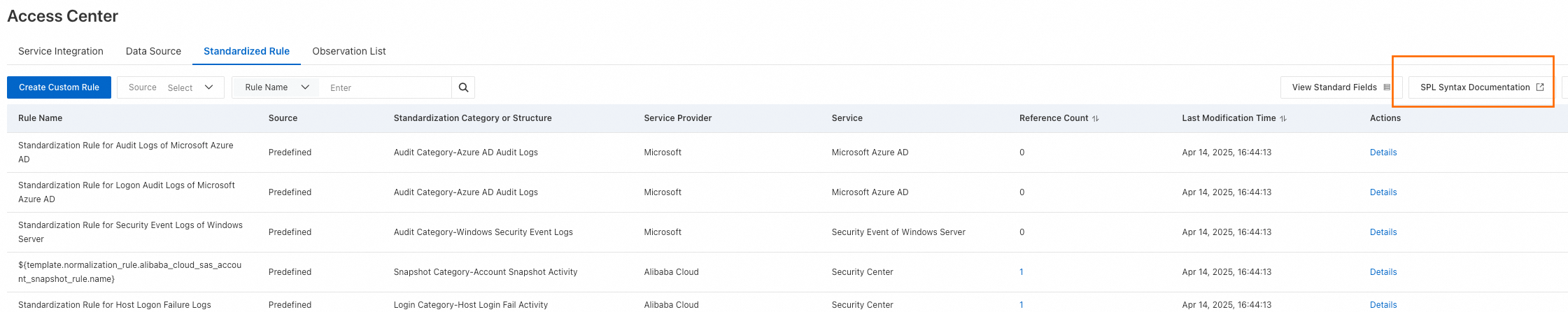
In the navigation pane on the left, choose . On the Standardized Rule tab, click View Standard Fields in the upper-left corner.
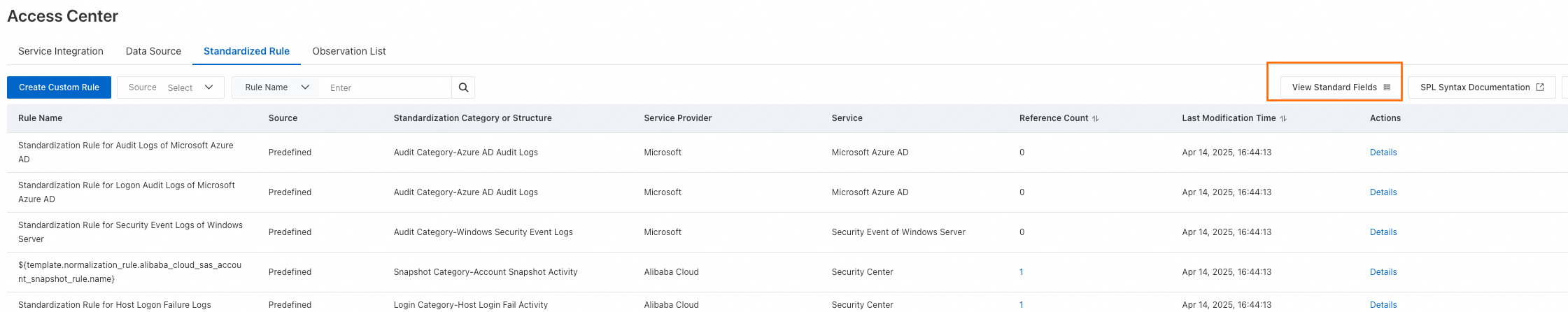
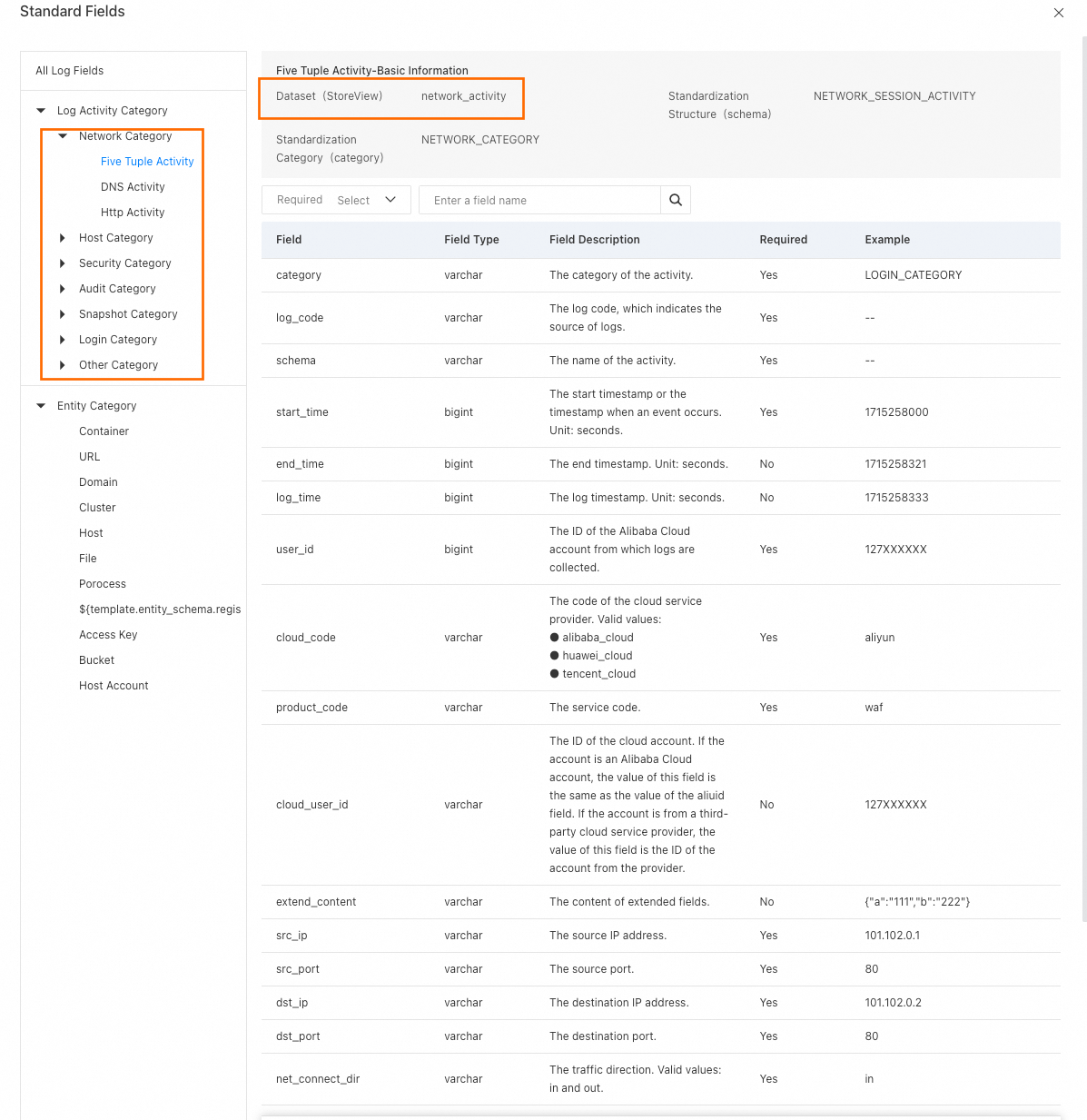
In the standardized field list, the Log Activity Category list items on the left are the standardization classifications supported by Agentic SOC, and the list root nodes are the standardization structures. On the right, you can view the Dataset (StoreView) name and the list of standardized fields.
References
To bind standardized rules, see Product integration.
To know which products are supported by default standardized rules, see Integration Center.
To learn more about Agentic SOC 2.0 architecture information, see Agentic SOC 2.0.
If you encounter problems during operation, see FAQ for solutions.