Agentic SOC is a built-in threat detection and response module in Security Center. It provides unified log analysis, automated incident response, and out-of-the-box threat detection rules. Charges are based on log ingestion traffic volume and log storage capacity.
Billing options
Agentic SOC supports two billing methods. Choose based on how predictable your log volume is.
| Billing methodUSD 100 per 1,000 GB per month | Best for | How it works |
|---|---|---|
| Subscription | Stable, predictable workloads with known log volumes | Pay upfront for fixed daily ingestion traffic and storage capacity. Minimum: 100 GB/day ingestion, 1,000 GB storage. |
| Pay-as-you-go | Variable traffic or when you cannot estimate usage in advance | Billed daily based on actual ingestion and usage. Minimum billing unit: 1 GB. |
You can mix billing methods across dimensions. For example, subscribe for log ingestion traffic and activate Log Management on pay-as-you-go.
If you have already purchased log ingestion traffic using subscription, you cannot activate Agentic SOC on pay-as-you-go.
Billing dimensions
Agentic SOC charges across up to four dimensions, depending on which services you activate.
Log ingestion traffic
The daily volume of logs ingested into Agentic SOC for analysis, measured in GB/day.
Subscription pricing (tiered):
| Daily traffic (X) | Price |
|---|---|
| X = 100 GB | USD 0.45/GB/day |
| 200 GB ≤ X < 9,999,999,999 GB | USD 0.42/GB/day |
Minimum purchase: 100 GB/day. Step size: 100 GB/day.
X=100 GB: USD 0.45/GB/day.
200 GB =< X < 9,999,999,999 GB: USD 0.42/GB/day.
Pay-as-you-go pricing (tiered cumulative):
| Traffic tier | Price | Daily fee formula (Y = daily GB) |
|---|---|---|
| 1–10 GB/day | USD 2.20/GB | 2.2 × Y |
| 11–50 GB/day | USD 1.6/GB | 2.2 × 10 + 1.6 × (Y − 10) |
| 51–100 GB/day | USD 1.4/GB | 2.2 × 10 + 1.6 × 40 + 1.4 × (Y − 50) |
| > 100 GB/day | USD 1.2/GB | 2.2 × 10 + 1.6 × 40 + 1.4 × 50 + 1.2 × (Y − 100) |
Estimate your required ingestion traffic using one of these methods:
Based on Simple Log Service (SLS) capacity:
Log ingestion traffic (GB/day) = Log storage capacity / TTLWhere log storage capacity is the storage used by the log sources you plan to ingest, and TTL is the log retention period.
Based on Events Per Second (EPS):
Log ingestion traffic (GB/day) = EPS × 86400 × SIZE / (1024 × 1024)Where EPS is the number of raw log events per second, and SIZE is the average log entry size (typically 3 KB–7 KB).
End-to-end cost example:
An environment generating 200 EPS with an average log size of 5 KB:
Daily traffic = 200 × 86400 × 5 / (1024 × 1024) ≈ 82 GB/day| Billing method | Calculation | Daily cost |
|---|---|---|
| Pay-as-you-go | 2.2 × 10 + 1.6 × 40 + 1.4 × (82 − 50) | USD 130.80 |
| Subscription (100 GB/day tier) | 100 × USD 0.45 | USD 45.00 |
For this environment, subscription at the 100 GB/day minimum provides significantly lower daily costs than pay-as-you-go.
Log storage capacity
The amount of storage Agentic SOC uses to retain logs, measured in GB.
Subscription pricing: USD 100 per 1,000 GB per month. Minimum purchase: 1,000 GB. Step size: 1,000 GB.
Sizing guidance: Allocate 120 GB per managed server, or use three times the storage capacity currently used by Security Center log analysis.
Intelligent usage analysis
Required only when you activate Security Operations Agent. This dimension measures the AI analysis quota consumed by alert triage, incident investigation, traceability, attribution, and security report generation.
Subscription pricing: USD 9.6 per 100 GB/day. Minimum: 100 GB/day. The purchase quantity does not support auto-filling and must match your log ingestion traffic purchase amount.
Pay-as-you-go pricing: USD 0.144 per GB per day.
Usage resets at midnight daily. After exceeding the limit, the system automatically applies rate limiting.
Number of managed instances
Required only when you activate Security Operations Agent. This is the count of instances managed for cross-instance security operations and automated response. Instances include Elastic Compute Service (ECS), Web Application Firewall (WAF), Application Load Balancer (ALB), cross-cloud products, and on-premises security products. Each instance is counted only once—duplicate entries are automatically removed.
Subscription pricing: USD 1.434 per instance per month. Minimum: 10 instances/month. Step size: 10 instances/month.
Pay-as-you-go pricing: USD 2.15 per instance per month.
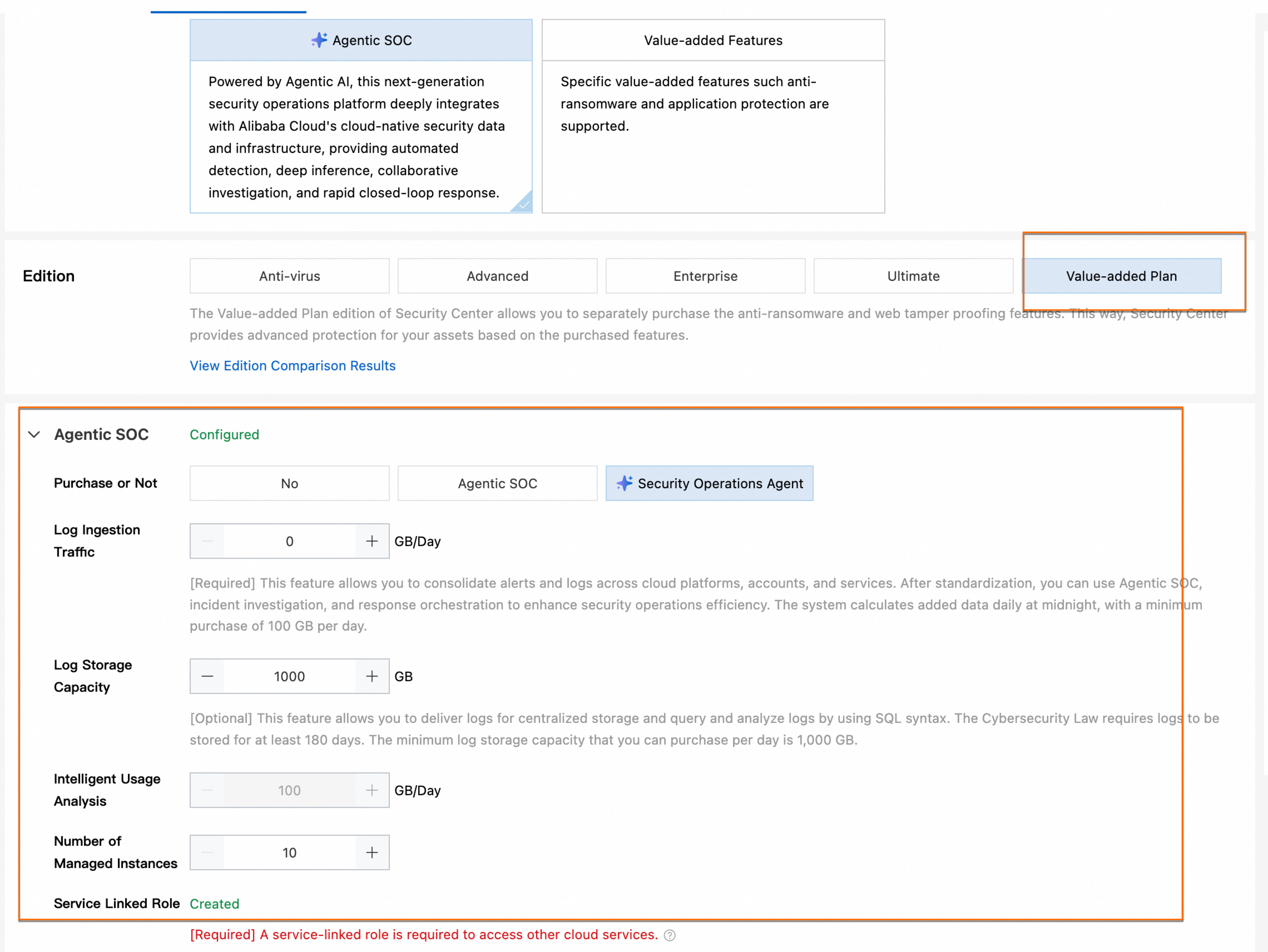
Activate using subscription
Before you begin
You have logged on to the Security Center console with an account that has permissions to purchase Security Center services.
You have estimated your required log ingestion traffic and storage capacity. See Billing dimensions.
Activation steps
In the left navigation pane, choose Detection and Response > Agentic SOC.
Click Activate Subscription. On the Quick Purchase tab, Billing Method defaults to Subscription.
Click Create Service-linked Role to authorize Agentic SOC to access your other cloud services. Skip this step if the role already exists.
NoteSecurity Center automatically creates the service-linked role
AliyunServiceRoleForSasCloudSiem. For details, see Service-linked roles for Security Center.Select the services to activate:
Agentic SOC: Unified log collection from multicloud environments, multiple accounts, and products such as WAF, Cloud Firewall, and virtual private cloud (VPC). Provides a closed-loop process for detecting, responding to, and handling security alerts and events. Meets MLPS 2.0 log audit requirements.
Security Operations Agent (optional): An advanced AI-powered service built on Agentic SOC. Uses Agentic AI as its core engine and integrates with Alibaba Cloud's native security data and infrastructure. Autonomously analyzes security events for rapid response.
Set the quantity for each service:
Agentic SOC: Set Log Ingestion Traffic and Log Storage Capacity independently based on your needs.
Security Operations Agent: Also set Intelligent Usage Analysis and Number of Managed Instances. The Intelligent Usage Analysis quantity must match your log ingestion traffic amount.
Choose whether to enable Access Policy:
Enabled: After activation, the system automatically ingests logs from Security Center, WAF, Cloud Firewall, and ActionTrail under your current Alibaba Cloud account. See Recommended log ingestion policy for the full data source list.
Disabled: No predefined ingestion settings are applied. After purchase, manually select log sources via Product ingestion.
Review the Security Center Related Agreements, then click Order Now.
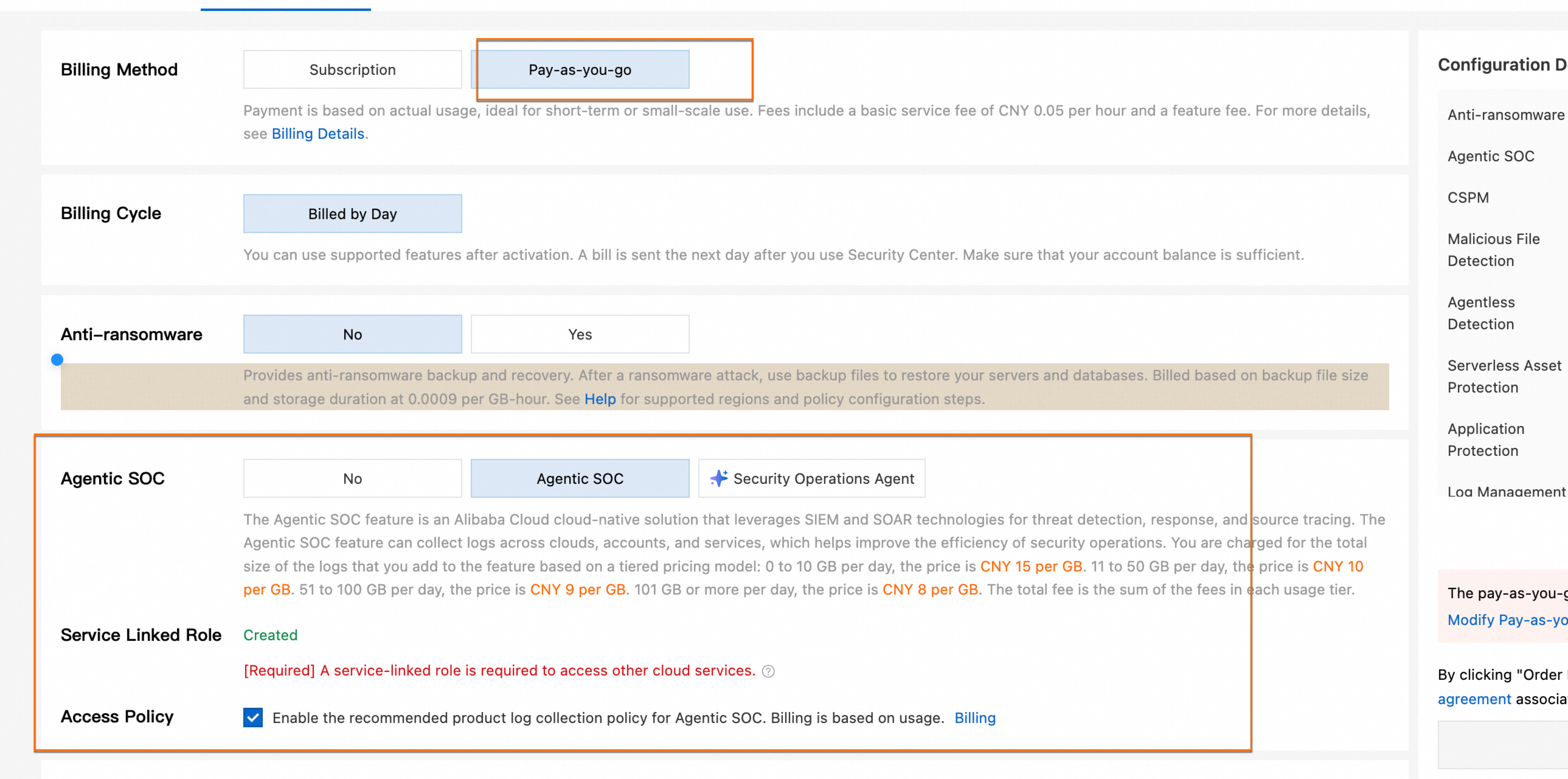
Activate using pay-as-you-go
Before you begin
You have logged on to the Security Center console with an account that has permissions to purchase Security Center services.
You have not already purchased log ingestion traffic using the subscription billing method.
Activation steps
In the left navigation pane, choose Detection and Response > Agentic SOC.
Click Activate Pay-as-you-go and select the services to activate (Agentic SOC and optionally Security Operations Agent).
Review the billing rule descriptions. Billing varies by activated service:
Agentic SOC: Billed daily based on actual log ingestion traffic using tiered cumulative pricing. Minimum billing unit: 1 GB (traffic under 1 GB is billed as 1 GB).
Security Operations Agent: In addition to the log ingestion traffic fee, also billed for Intelligent Usage Analysis and Number of Managed Instances.
Choose whether to enable One-click Ingestion:
Enabled: After activation, the system automatically ingests logs from Security Center, WAF, Cloud Firewall, and ActionTrail. Security Center generates a bill the next day based on your actual log ingestion volume.
ImportantEnabling one-click ingestion starts automatic log ingestion immediately. Review the Recommended log ingestion policy to understand what data sources are ingested before enabling.
Disabled: Manually select log sources after activation via Product ingestion.
Click Activate and Authorize.
NoteSecurity Center automatically creates the service-linked role
AliyunServiceRoleForSasCloudSiem. For details, see Service-linked roles for Security Center.
Features available after activation
The features you can access depend on your billing method and which dimensions you purchased.
Subscription
| Feature | Log ingestion only | Log storage only | Log ingestion + storage |
|---|---|---|---|
| Dashboard | Not supported | Not supported | Not supported |
| Security Events | Supported | Not supported | Supported |
| Alert | Supported (Custom Alert Analysis requires Log Management pay-as-you-go) | Not supported | Supported |
| Incident Response | Supported | Not supported | Supported |
| Response Rules | Supported | Not supported | Supported |
| Log Management | Standardized logs: Supported (scan query only); Security Center logs: Not supported | Security Center logs: Supported; Standardized logs: Not supported | Supported |
| Detection Rules | Predefined: Supported; Custom: Supported (scan query only) | Not supported | Supported |
| Integration Settings / Service Integration | Supported | Not supported | Supported |
If you also activate the pay-as-you-go Log Management feature, all Log Management and Detection Rule capabilities are fully supported.
Pay-as-you-go
| Feature | Status |
|---|---|
| Dashboard | Not supported |
| Security Events | Supported |
| Alert | Supported |
| Incident Response | Supported |
| Response Rules | Supported |
| Log Management | Standardized logs: Supported (scan query only); Security Center logs: Not supported |
| Detection Rules | Predefined: Supported; Custom: Supported (scan query only) |
| Integration Settings / Service Integration | Supported |
If you also activate the pay-as-you-go Log Management feature, all Log Management and Detection Rule capabilities are fully supported.
Ingest product logs
After activating Agentic SOC, ingest product logs to enable cross-resource alerting and unified log analysis. For instructions, see Product ingestion.
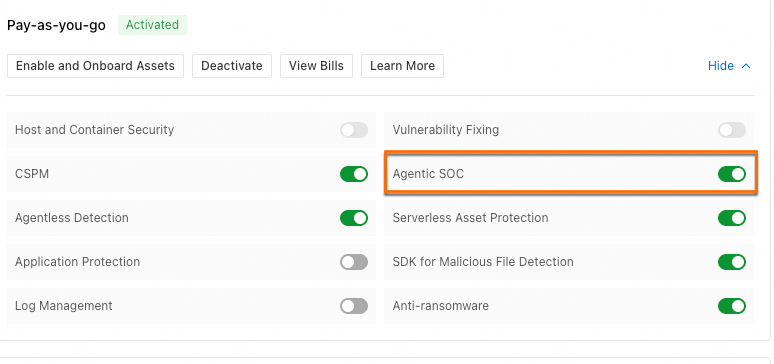
Cancel or disable Agentic SOC
Subscription
On the Overview page, in the Subscription section, click Change > Downgrade. On the Order Downgrade tab, in the Agentic SOC section, set Purchase or Not to No.
The exact refund amount is shown on the downgrade page. For details, see Refund disbursement. For full downgrade instructions, see Downgrade.
Pay-as-you-go
On the Overview page, in the Pay-as-you-go section, turn off the switch for Agentic SOC or Log Management.
No new charges accrue after you disable the service. Except for user-delivered logs, all data and configurations—including security alerts, security events, and ingestion settings—are deleted after 15 days.
After you turn off the Log Management switch, log delivery stops and the corresponding Logstore is deleted. Deleted log data cannot be recovered. Proceed with caution.
Appendix
Other purchase entry points
You can also purchase Agentic SOC on the Security Center purchase page or on the console Overview page. For Security Center edition selection and other service purchases, see Purchase Security Center.
Subscription
Pay-as-you-go
Security Center purchase page
Overview page
Recommended log ingestion policy
When you enable Access Policy (subscription) or One-click Ingestion (pay-as-you-go), Agentic SOC automatically ingests logs from the following sources under your current Alibaba Cloud account—no manual configuration required.
If your Security Center edition is Free Edition or you have only purchased value-added services, ActionTrail event logs are not ingested.
| # | Product | Data source | Standardization method | Security capabilities |
|---|---|---|---|---|
| 1 | Security Center | DNS request logs | Scan query | Predefined analysis rules, predefined playbooks |
| 2 | Security Center | Baseline logs | Scan query | Incident investigation and traceability, predefined playbooks |
| 3 | Security Center | Login flow logs | Scan query | Custom analysis rules, incident investigation and traceability, predefined playbooks |
| 4 | Security Center | Network connectivity logs | Scan query | Predefined analysis rules, predefined playbooks |
| 5 | Security Center | Process startup logs | Scan query | Predefined analysis rules, custom analysis rules, incident investigation and traceability, predefined playbooks |
| 6 | Security Center | Security alert logs | Real-time consumption | Predefined playbooks |
| 7 | Security Center | Vulnerability logs | Scan query | Incident investigation and traceability, predefined playbooks |
| 8 | Web Application Firewall | WAF alert logs | Real-time consumption | Predefined analysis rules, custom analysis rules, predefined playbooks |
| 9 | Web Application Firewall | WAF full, block, and block-and-observe logs | Real-time consumption | Predefined analysis rules, custom analysis rules, incident investigation and traceability, predefined playbooks |
| 10 | Cloud Firewall | Cloud Firewall alert logs | Real-time consumption | Predefined analysis rules, custom analysis rules, predefined playbooks |
| 11 | ActionTrail | ActionTrail event logs | Real-time consumption | Custom analysis rules, incident investigation and traceability |
What's next
To understand Agentic SOC architecture and version differences, see Agentic SOC version comparison.
To ingest logs from additional products after activation, see Agentic SOC product ingestion.
To learn about Security Center editions and other service purchases, see Purchase Security Center.