Tair (Redis OSS-compatible) instances sit at the data layer, close to your application services, and handle a high volume of requests. Each instance type has a maximum bandwidth limit. When traffic consistently exceeds that limit, application performance degrades.
This page walks you through identifying the cause of high traffic and resolving it.
Step 1: Check traffic usage
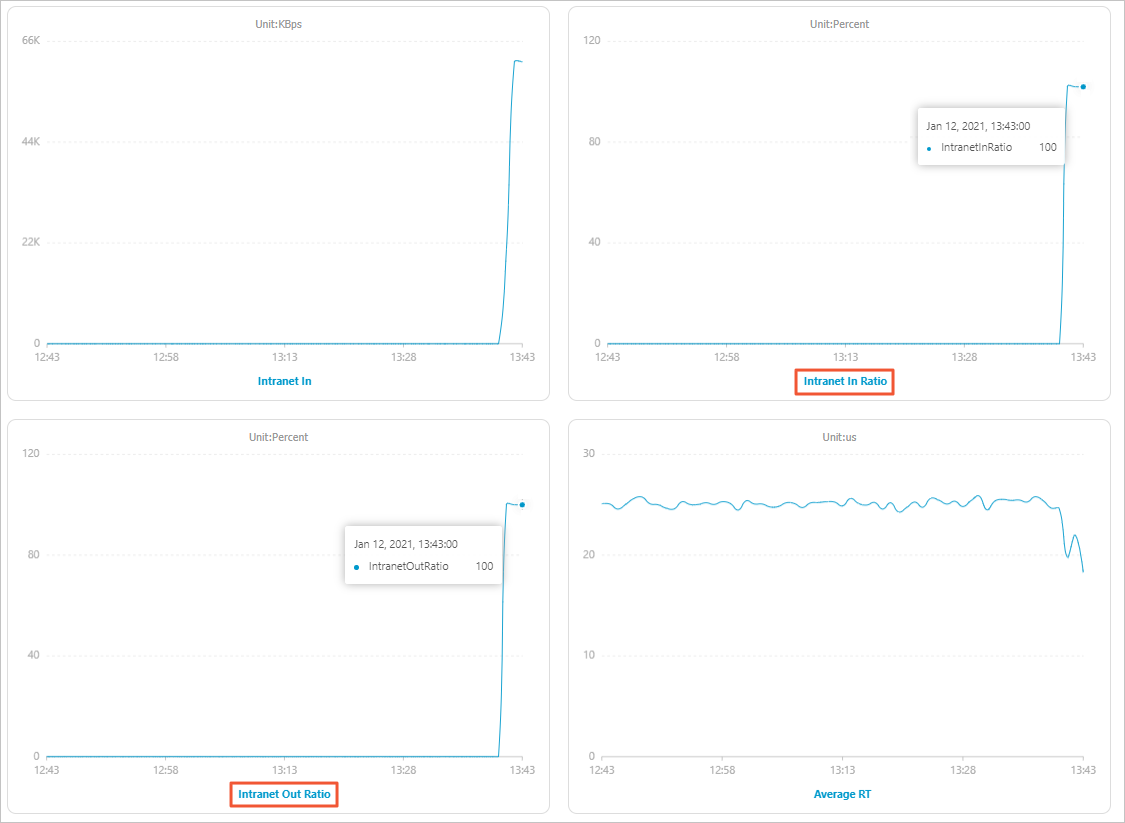
Query the traffic usage of the instance for the time period when you suspect the issue occurred. Focus on two metrics:
If either metric averages 80% or higher consistently, the instance is approaching its bandwidth limit and you should investigate. In severe cases — such as the example below — both metrics spike to 100%.
Figure 1. Traffic usage example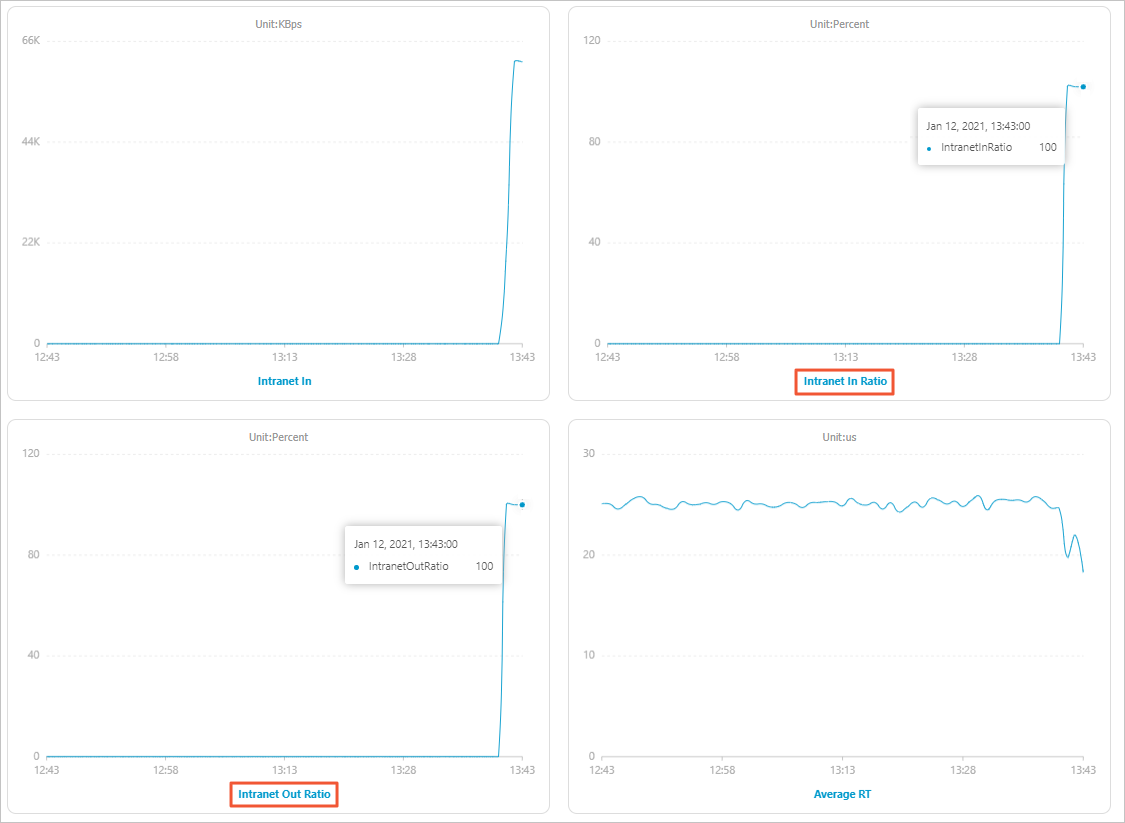
If you already know when the spike occurred, skip this step and go directly to Step 2: Identify the cause.
Tip: Set up alert rules on Intranet In Ratio and Intranet Out Ratio at 80% to get notified before traffic reaches the limit. See Alert settings. Acting at 80% gives you time to investigate before service is affected.
Step 2: Identify the cause
Three common causes can drive high traffic on a Tair (Redis OSS-compatible) instance.
Before you start: Temporarily adjust the instance bandwidth to reduce the immediate impact on your services while you work through the root cause.
Check each cause in order.
Large keys and hot keys
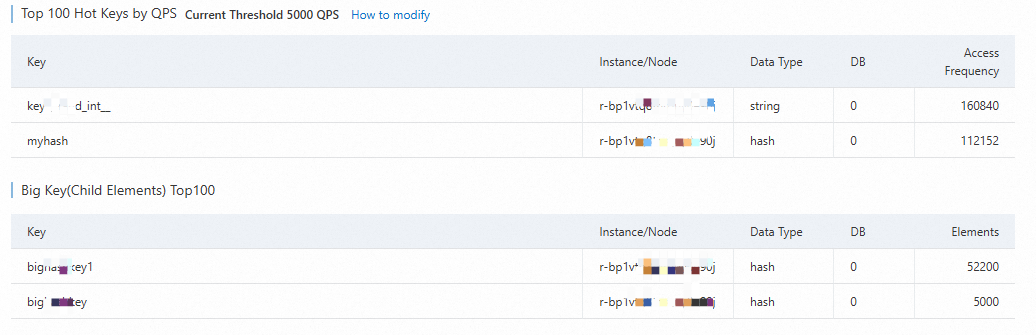
Use the Top Key Statistics feature to identify large keys or hot keys on the instance. The feature displays key details directly in the console.
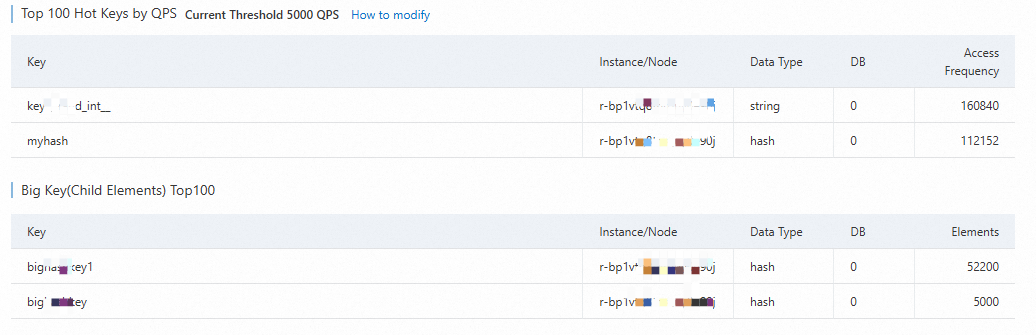
These two key types cause traffic problems in different ways:
| Key type | How it causes high traffic | Resolution |
|---|
| Large key | Each access transfers a large payload, which can saturate bandwidth and cause traffic spikes. | Split by business logic (e.g., user ID or time range), reduce access frequency, or delete keys that are no longer needed. See Large keys and hot keys. |
| Hot key | High-frequency access to the same key generates a continuous stream of small requests that accumulate into sustained traffic elevation. | Split by business logic, or use the Proxy Query Cache feature to cache hot keys at the proxy layer. |
Slow requests
Use the Slow Requests feature to check for recently executed slow requests.
Slow requests can block subsequent commands and cause traffic spikes.
If slow requests are present, disable high-risk commands such as KEYS and HGETALL in your production environment.
Service traffic growth
If traffic stays high after addressing large keys, hot keys, and slow requests, the cause is likely natural growth in service traffic. Consider the following options:
| Option | When to use | How to proceed |
|---|
| Upgrade instance memory | Traffic has grown beyond the current bandwidth tier | Move to an instance type with more memory. Before committing, purchase a pay-as-you-go instance to test whether the target type meets your workload requirements, then release it after testing. |
| Upgrade instance architecture | Traffic volume requires horizontal scaling | Switch to a cluster or read/write splitting architecture to distribute traffic across multiple nodes. See Change instance configurations. |
| Handle periodic peaks | Traffic spikes are predictable (e.g., a peak at 22:00 every night) | Use Bandwidth Auto Scaling or Scheduled Bandwidth Upgrade instead of permanently upgrading. |