Data Security Center (DSC) provides data leak detection as a value-added service for Detection and Response. This document describes how to view risk event details and disposition methods.
Prerequisites
You have purchased Data Security Center and ensured sufficient Detection and Response quota (available through separate purchase of value-added services or default quota with Enterprise Edition). If the Detection and Response service is not activated or the quota is insufficient, you can upgrade your instance.
You have completed asset authorization.
Risk event and disposition overview
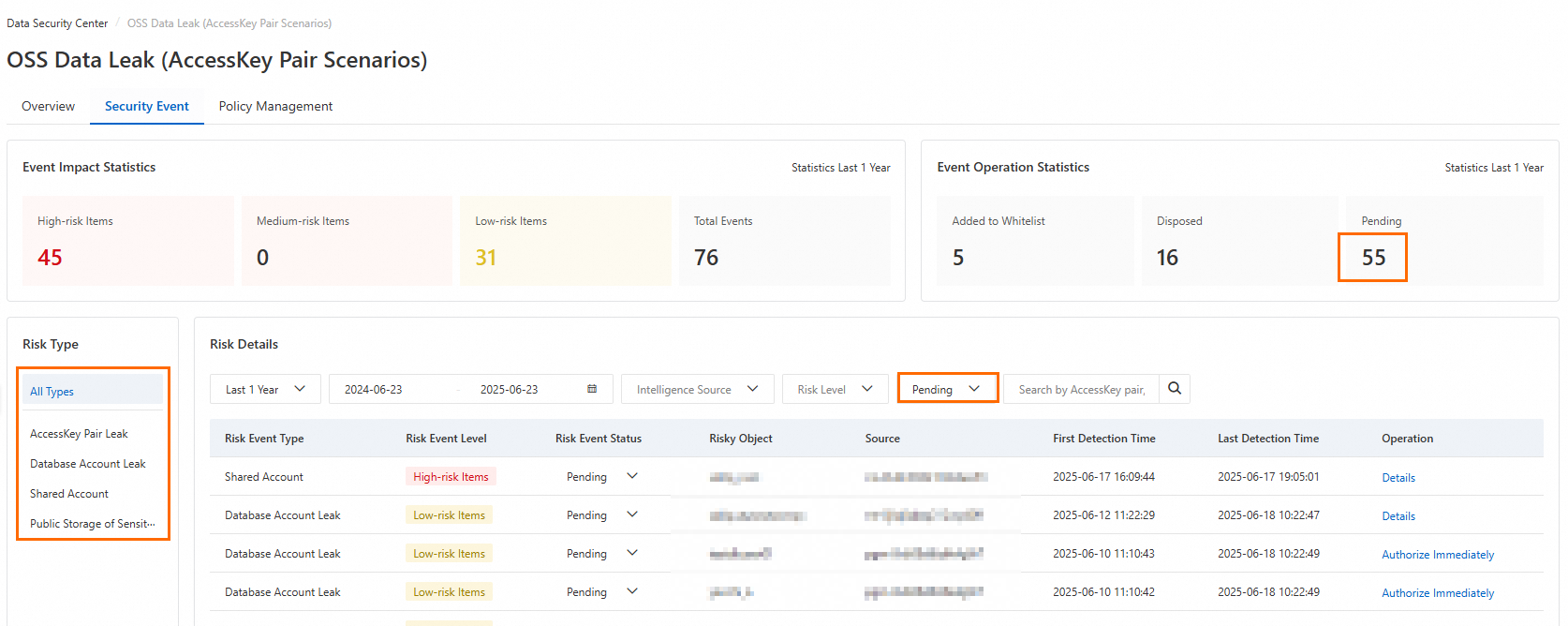
View the number of risk events at each risk level and event operation statistics.
Log on to the Data Security Center console.
In the navigation pane on the left, choose .
On the Security Event tab, view the recent Event Impact Statistics and Event Operation Statistics, along with the detected Risk Details.
Event Impact Statistics: Displays the Total Events, High-risk Items, Medium-risk Items, and Low-risk Items risk events detected in the past year. You can click the number under each risk level to filter the Risk Details list below by risk event level.
Event Operation Statistics: Displays the disposition status of risk events detected in the past year, including Added to Whitelist, Disposed, and Pending events.
Risk Details: Displays risk events by risk type (All Types, AccessKey Pair Leak, Database Account Leak, Shared Account, Public Storage of Sensitive Information, etc.).
NoteYou can click the statistics numbers or corresponding Risk Event Type to filter the Risk Details list by condition.
View risk event details and disposition
DSC categorizes detected risk events into 4 basic types. If you have enabled detection for the corresponding risk type, you can view detailed event information and take appropriate actions in the risk details area after a risk event occurs.
AccessKey pair leaks
Detects active AccessKey pair leaks through intelligence sources such as GitHub, public plaintext storage, private plaintext storage, threat intelligence, and custom intelligence. You can view details of AccessKey access to buckets and take recommended actions such as integrating with KMS for AccessKey rotation or whitelisting. For storage media, you can delete corresponding files or whitelist them.
In the Risk Event Type area, click AccessKey Pair Leak.
In the Operation column of the target risk event, click Details.
ImportantTo view detailed information about risk events, you must first complete asset authorization.
On the Details page, view the detailed information about the risk event and take disposition actions.
AccessKey information
View information such as AccessKey ID, Account of AccessKey Pair, AccessKey Pair Status, First Detection Time, Latest Detection Time, and Intelligence Source.

Click Handle.
In the Manage AccessKey Pair panel, perform Disable or Rotate operations.
Disable: Redirects to the Resource Access Management (RAM) console to disable the AccessKey for the current primary account and its RAM users. For more information, see Disable an AccessKey pair of a RAM user.
Rotate:
KMS Integrated: After clicking Confirm, KMS will perform rotation, delete the existing AccessKey pair, and create a new one.
WarningThis operation cannot be undone once executed. Please proceed with caution.
KMS Not Integrated: Redirects to the Key Management Service console to host your AccessKey credentials in KMS. If you have not activated KMS, you must first purchase and enable a KMS instance.
AccessKey leak details
View AccessKey leak information from the following intelligence sources. You can process or whitelist risk events based on different intelligence sources.
GitHub Leak Amount: AccessKey information contained in public source code on the GitHub platform.
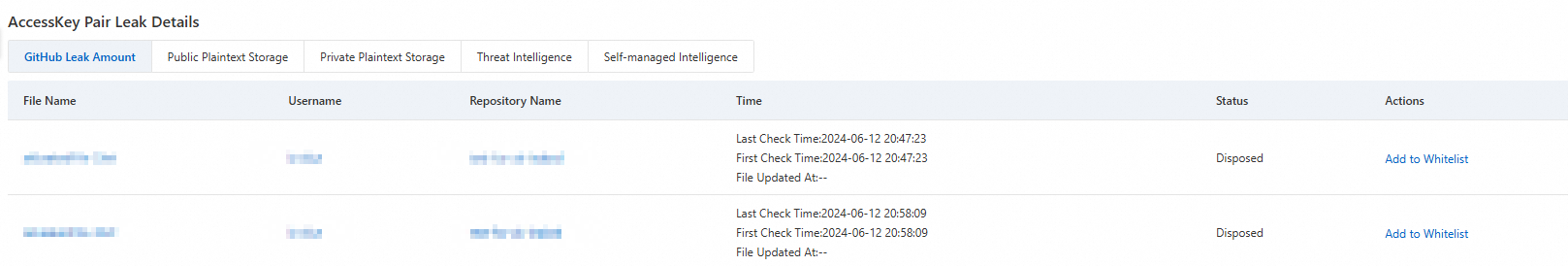
Click File Name, Username, or Repository Name to jump to the GitHub platform to view related information.
Click Add to Whitelist in the Actions column to whitelist the target file. This file will not generate AccessKey leak risk events in the future.
Public Plaintext Storage/Private Plaintext Storage: Detects AccessKey information stored in plaintext in public/private files in authorized OSS buckets.
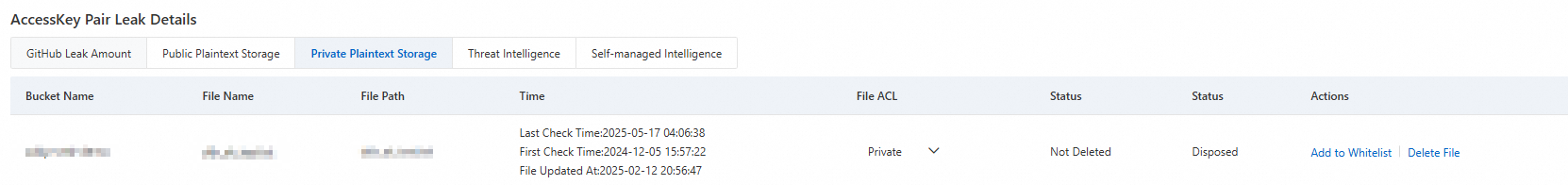
Modify ACL: Click the dropdown button in the File ACL column to modify the ACL of the corresponding file.
Delete: Click Delete File in the Actions column to delete the file from the corresponding bucket.
Add to allowlist: In the Actions column, click Add to Whitelist to add the target file to the allowlist. The file will no longer generate AccessKey pair leak threat events.
Threat Intelligence/Self-managed Intelligence: For AccessKey leak events from threat intelligence or custom intelligence, you can whitelist related threat sources or intelligence entry users.
NoteAfter a file is deleted, the Status will automatically update to Deleted on T+1 day, and the Status will update to Disposed.
After a file is whitelisted, the Status will automatically update to Added to Whitelist on T+1 day.
AccessKey bucket access details
For leaked AccessKeys accessing buckets, you can not only view specific file access lists but also configure bucket access permissions and set POP gateway interception policies to effectively protect data security.
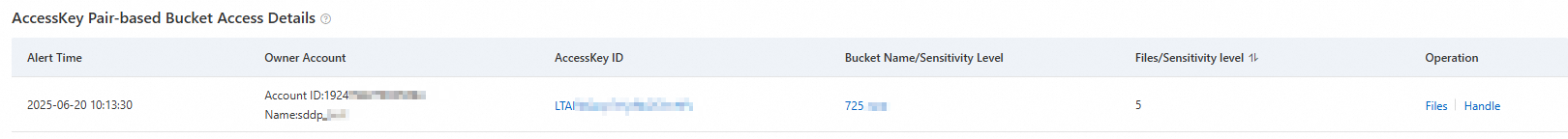
Threat Tracing: Click the target AccessKey ID or Bucket Name/Sensitivity Level to view the visualization path of AccessKey and bucket access behavior.
View Files: Click Files in the Actions column to view information about accessed files. You can also directly modify the file ACL.
Handle: Click Handle in the Actions column to configure bucket access permissions and set POP gateway interception policies.
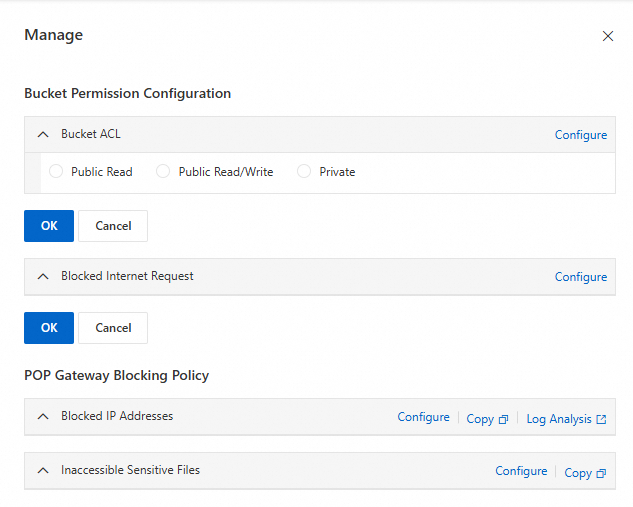
Bucket Permission Configuration: Click Configure to set up Bucket ACL and public network request interception, then click OK.
POP Gateway Blocking Policy: Click Configure to jump to the Resource Access Management (RAM) console to create policies that restrict IP access and sensitive file access permissions. For more information, see Create a custom policy.
Database credential leaks
By detecting credential information (including connection addresses, port numbers, accounts, and passwords) for ApsaraDB RDS or PolarDB in authorized OSS Buckets, this feature identifies and gathers statistics on database instances, including self-managed instances and instances from threat intelligence. It also tracks risky behaviors that involve using these accounts to access the corresponding database instances and generates risk events. For the affected accounts, you can integrate with KMS to perform operations such as credential rotation or adding the accounts to an allowlist. For the storage medium, you can delete the corresponding file or add it to an allowlist.
A risk event is only detected and identified as a database credential leak when a bucket file contains the database's credentials, connection address, and port number information simultaneously.
In the Risk Event Type area, click Database Account Leak.
In the Operation column of the target risk event, click Details.
ImportantTo view detailed information about risk events, you must first complete asset authorization.
On the Details page, view the detailed information about the risk event and take disposition actions.
Database information
View information such as Database Account, Database Instance, First Detection Time, Latest Detection Time, and Intelligence Source.

Click Handle.
In the Manage Account panel, perform Delete or Rotate operations.
Delete: Delete the account and password of the current database instance.
WarningThis operation cannot be undone once executed. Please proceed with caution.
Rotate:
KMS Integrated: After clicking Confirm, the database credentials will be rotated, deleting and recreating new database credentials.
WarningThis operation cannot be undone once executed. Please proceed with caution.
KMS Not Integrated: Redirects to the Key Management Service console to host your database credentials in KMS. If you have not activated KMS, you must first purchase and enable a KMS instance.
Credential leak details
View credential leak information from the following intelligence sources. You can process or whitelist risk events based on different intelligence sources.
Public Plaintext Storage/Private Plaintext Storage: Detects database-related information stored in plaintext in public/private files in authorized OSS buckets.
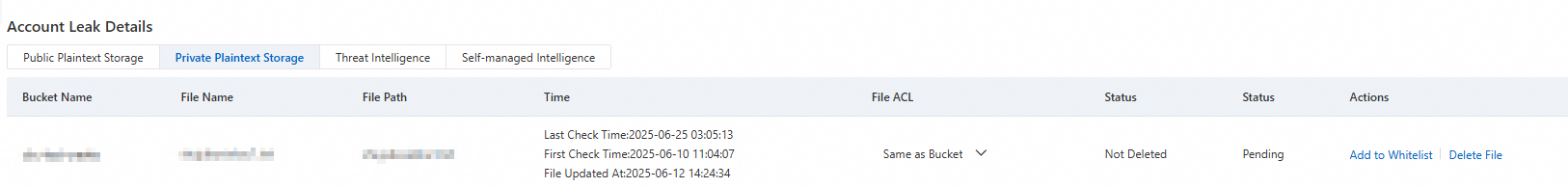
Modify ACL: Click the dropdown button in the File ACL column to modify the ACL of the corresponding file.
Delete: Click Delete File in the Actions column to delete the file from the corresponding bucket.
Whitelist: Click Add to Whitelist in the Actions column to whitelist the target file. This file will not generate database credential leak risk events in the future.
Threat Intelligence/Self-managed Intelligence: For database leak events from threat intelligence or custom intelligence, you can whitelist related threat sources or intelligence entry users.
NoteAfter a file is deleted, the Status will automatically update to Deleted on T+1 day, and the Status will update to Disposed.
After a file is whitelisted, the Status will automatically update to Added to Whitelist on T+1 day.
Database access details
In addition to viewing the database name, access frequency, access time, and sensitive data classification and grading results accessed by the account, you can also view detailed database information (including database tables and sensitive information) and revoke the account's access and modification permissions to the database.
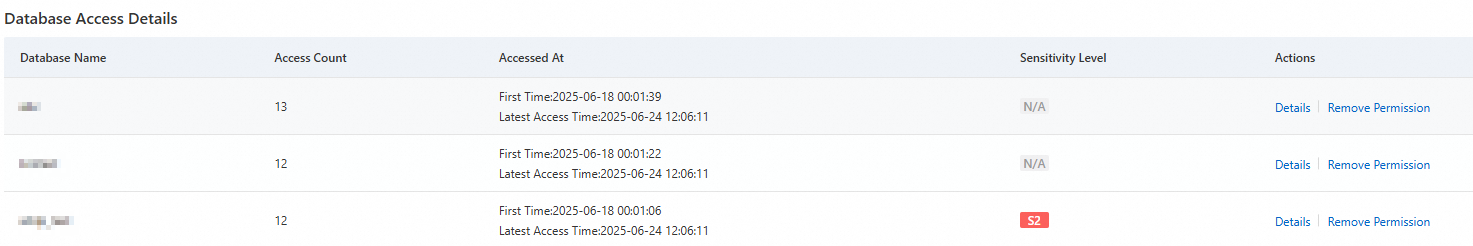
Details: Click Details in the Actions column of the target database to view detailed database table information.
For incorrect sensitive column identification results, click Column details to correct the sensitive data identification results.
Remove Permission: Click Remove Permission in the Actions column of the target database. Then click OK.
This will delete all access/modification permissions of the current account to the database.
Mixed use of human and machine accounts
Analyzes the operation behavior of an account through historical logs, determines if there is human use of machine accounts, and generates risk events for mixed use of human and machine accounts.
Machine accounts are primarily used for communication needs between software, programs, scripts, or services, typically used by programs at runtime rather than for direct human user operations. For example:
The account accessed/used objects/tools that have not appeared in history, including databases, SQL statements, client IPs, client tools, etc.
The database account's current operation frequency is low, which can be performed by humans. This behavior may not have caused data leakage, but it exposes vulnerabilities in account management. In the future, the "human-machine separation" principle should be clearly defined, with human and machine accounts managed and used separately.
In the Risk Event Type area, click Shared Account.
In the Operation column of the target risk event, click Details.
ImportantTo view detailed information about risk events, you must first complete asset authorization.
On the Details page, view the detailed information about the risk event and take disposition actions.
Account information
View information such as Access Account, Instance, First Detection Time, Latest Detection Time, and Intelligence Source.

Click Handle.
In the Manage Account panel, perform Delete or Rotate operations.
Delete: Delete the account and password of the current database instance.
WarningThis operation cannot be undone once executed. Please proceed with caution.
Rotate:
KMS Integrated: After clicking Confirm, the database credentials will be rotated, deleting and recreating new database credentials.
WarningThis operation cannot be undone once executed. Please proceed with caution.
KMS Not Integrated: Redirects to the Key Management Service console to host your database credentials in KMS. If you have not activated KMS, you must first purchase and enable a KMS instance.
Detailed abnormal statements
View detailed information about executed operation statements, including database name, table name, access time, access IP, access client, operation type, operation statement, and returned rows.
Public storage of sensitive information
When the system detects more than 1,000 files with sensitivity level S3 or higher in an authorized and public OSS bucket, it will generate an alert. It is recommended that you modify the bucket status or delete/modify the ACL (Access Control List) of sensitive files.
In the Risk Event Type area, click Public Storage of Sensitive Information.
In the Operation column of the target risk event, click Details.
ImportantTo view detailed information about risk events, you must first complete asset authorization.
On the Details page, view the detailed information about the risk event and take disposition actions.
Bucket information
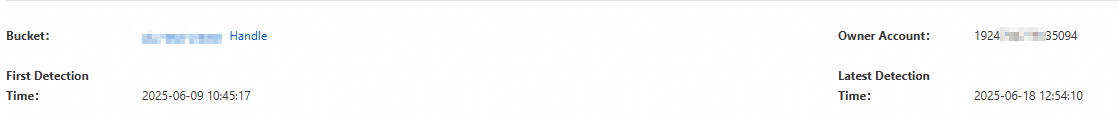
View information such as Bucket Name, Owner Account, First Detection Time, and Latest Detection Time.
Click Handle.
Configure bucket access permissions and set POP gateway interception policies.
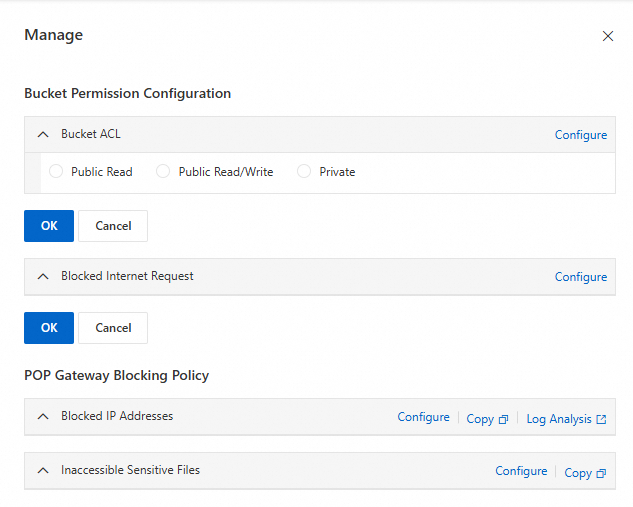
Bucket Permission Configuration: Click Configure to set up Bucket ACL and public network request interception, then click OK.
POP Gateway Blocking Policy: Click Configure to jump to the Resource Access Management (RAM) console to create policies that restrict IP access and sensitive file access permissions. For more information, see Create a custom policy.
Sensitive file list
View details of detected sensitive files, including sensitive data information and file access path tracing information, and modify file ACLs.
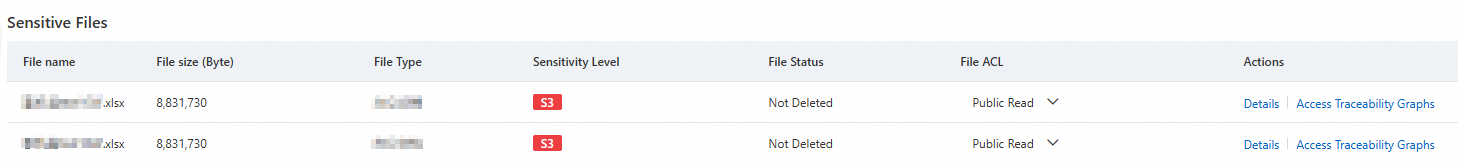
Details: Click Details to view details of sensitive information contained in the file.
Threat Source Tracing: Click Threat Source Tracing to view the visualization path of file access behavior.
Other operations
Risk event policy configuration
DSC categorizes detected risk events into 4 basic types. You need to enable the status for each type and configure the corresponding risk level.
In the navigation pane on the left, choose .
On the Policy Management tab, enable the risk event status for the corresponding risk event type, and then configure the risk event level according to your requirements.
ImportantRisk event status is enabled by default, and the Shared Account event type has a default risk level of Medium-risk Items, while other types have a default risk level of High-risk Items.
After a risk event is disabled, no new alert events will be generated, but existing events will not be affected.
After adjusting the risk event level, the risk level of existing events will be updated synchronously.
After configuration is complete, click Save.
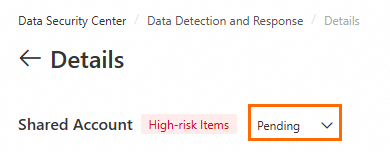
Modify event disposition status
You can modify the risk event status (such as whitelisted, processed, pending, etc.).
You can modify the event status in the Risk Details list on the Security Event tab.
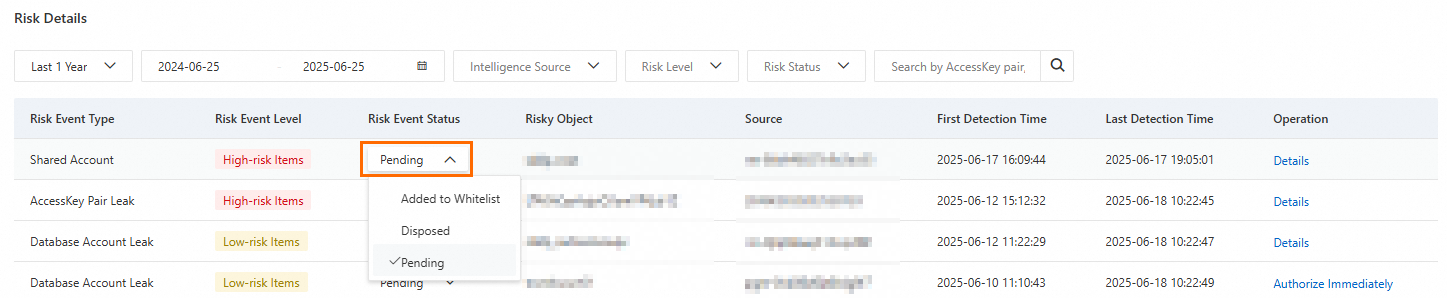
Or modify the event status on the Details page of the target risk event.