The Detection and Response value-added service in Data Security Center (DSC) detects data leaks across your cloud assets, traces access events, and lets you feed in your own intelligence for continuous monitoring. This topic covers how to read the risk overview, authorize assets for detection, and add self-managed intelligence.
Prerequisites
Before you begin, make sure that you have:
Purchased DSC and a Detection and Response quota. The quota is available as a standalone value-added service or included by default with the Enterprise Edition. If you have not activated the service or your quota is insufficient, upgrade your instance
An instance in a region that supports the Detection and Response feature. For supported regions, see Supported regions
View the data leak overview
The Overview page summarizes data leak events from the past year across four areas: statistics by source, asset authorization status, top risk objects, and risk trends.
Log on to the Data Security Center console.
In the left navigation pane, choose Data Detection and Response > Data Leak.
On the Overview page, review the statistics and take action as needed.

The page is divided into four areas:
| Area | Description | Available actions |
|---|---|---|
| ① AccessKey leak and account password leak statistics | Shows two counts: Full Data Leak and Unhandled Leaks. Within each count, Total AccessKey pair Leaks and Total Database Leaks are broken down by detection channel: GitHub Leak Amount, Public Plaintext Storage, Private Plaintext Storage, Threat Intelligence, and Self-managed Intelligence. | Click |
| ② Asset authorization statistics | Displays the capacity and usage of your purchased OSS protection volume and database instances. | Click Authorize Immediately to open the Asset Authorization Configuration panel. |
| ③ Top 5 risk objects | Lists the five assets with the highest number of risk events, along with their risk levels. | Click a risk object name to see all risk events for that asset on the Security Event page. |
| ④ Risk trend | A line chart showing total alert volume and the breakdown by risk level (important, medium, low) over time. | Filter by Last 1 Day, Last 7 Days, Last 15 Days, Last 30 Days, or Custom. |
Authorize assets for detection
DSC detects data leak risks in OSS buckets and database instances only after you authorize them. Complete authorization before adding self-managed intelligence or viewing risk event details.
Log on to the Data Security Center console.
In the left navigation pane, choose Data Detection and Response > Data Leak.
On the Overview tab, in the Storage Authorization Statistics or Database Authorization Statistics section, click Authorize Immediately.

In the Asset Authorization Configuration panel, select the target assets on the Not authorized tab and complete the Authorization.

Only RDS and PolarDB database instances are supported for authorization. If the asset you want to authorize is not listed, click Asset synchronization and retry after the sync completes.
After authorization, DSC starts detecting risk events for the authorized assets.
Add self-managed intelligence
By default, DSC only generates risk events for AccessKeys or database accounts it has confirmed as leaked through automated detection channels (such as GitHub scans or bucket file scans). If you already know or suspect that specific credentials are compromised, add them as self-managed intelligence. DSC then continuously tracks access behaviors associated with those credentials against your authorized assets and alerts you in real time.
You can view and manage all entries in the Intelligence Management panel at any time.
Self-managed intelligence covers two types: AccessKey leak intelligence and account password leak intelligence.
Add AccessKey leak intelligence
When no AccessKey leak is detected in GitHub or authorized bucket files, DSC does not generate risk events for that AccessKey—even if it accesses authorized buckets. To monitor access behaviors for a specific AccessKey regardless of automated detection results, add it manually.
In the AccessKey Leak (Past Year) section, click Add Intelligence.

In the Intelligence Management panel, click Add Intelligence.
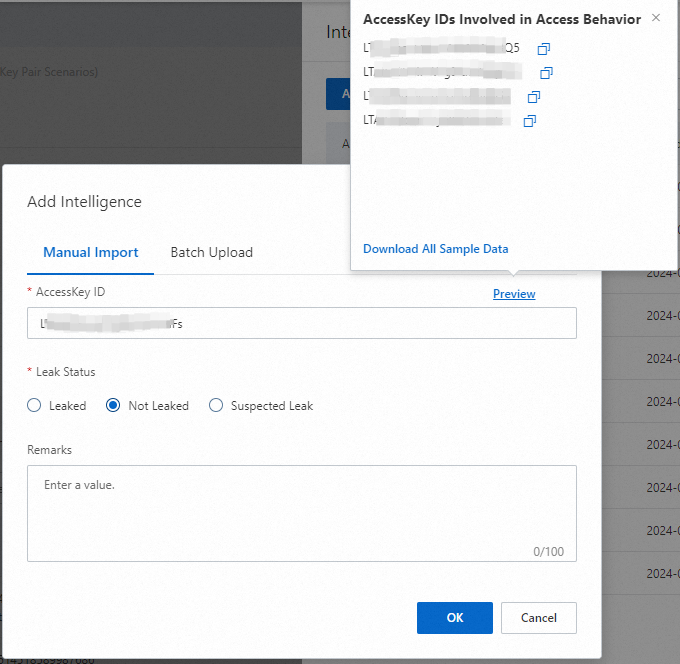
Add AccessKey pairs using one of the following methods: Option 1: Manual import (single entry) On the Manual Import tab, enter the AccessKey ID, select the Leak Status (Leaked, Not Leaked, or Suspected Leak), enter any Remarks, and click OK. Option 2: Batch upload
On the Batch Upload tab, click Download Template to get the .xlsx template file. If you have authorized a target bucket and at least one detection has run, DSC pre-populates the template with detected AccessKey data, as shown below.

Fill in the required columns: AccessKeyId (the AccessKey ID), Status (the leak status: Leaked, Not Leaked, or Suspected Leak), and Comment (remarks). Save the file.
On the Batch Upload tab, click View Local File or the upload
 icon to import the saved .xlsx file.
icon to import the saved .xlsx file.Click OK.
If you have authorized a target bucket and at least one detection has run after authorization, DSC records the AccessKey IDs that accessed the bucket and generates sample data. Click Preview to copy these AccessKey details for input.

After adding the intelligence, view and manage it in the Intelligence Management panel. To remove an entry, click Delete.
Add account password leak intelligence
For database instances with confirmed, suspected, or potential leak risks—or instances whose access activity you need to monitor—add them to self-managed intelligence. DSC continuously tracks access activities and provides real-time alerts.
Complete database instance authorization before adding it to self-managed intelligence. See Authorize assets for detection.
In the Account Leak (Past Year) section, click Add Intelligence.

In the Intelligence Management panel, click Add Intelligence.
In the Add Intelligence dialog box, configure the following parameters and click OK.
| Parameter | Description |
|---|---|
| Asset type | Specify the OS of the host to add. Only RDS and PolarDB are supported. |
| Database instance | The authorized database instance to monitor. |
| Database account | The account for the selected database instance. |
| Leak status | The leak status: Leaked, Not Leaked, or Suspected Leak. |
| Remarks | An optional description. |
After adding the intelligence, view and manage it in the Intelligence Management panel. To remove an entry, click Delete.
What's next
View risk event details and handle detected risks in Risk details and handling.