Query and analyze firewall traffic logs in real time to monitor network activity, detect anomalies, and investigate security incidents.
Prerequisites
Before you begin, make sure that:
Traffic from your assets is being collected. For more information, see access management.
Enable log delivery
Cloud Firewall collects two types of logs. Enable both before running queries:
Alert logs: Records traffic that matches access control and attack prevention policies. Use these logs to investigate policy hits and security events.
Protocol logs: Records all network session metadata, regardless of policy match. Use these logs for traffic analysis and anomaly detection.
To enable log delivery:
Log on to the Agentic NDR console.
In the navigation pane, select Logs.
In the upper-right corner of the Log Analysis page, click Log Settings.
In the Log Settings panel, go to the Log Delivery tab.
In the Basic Settings section, note the Region for Log Delivery and log retention period. To change either setting, go to the Cloud Firewall console. For more information, see Modify log storage configurations.
Under Log Delivery, turn on both Alert Logs and Protocol Log.
Configure filter rules and delivery fields
Use filter rules to control which protocol logs are delivered, and delivery fields to select which log attributes to include.
In the upper-right corner of the Log Analysis page, click Log Settings.
Configure each tab as needed:
Custom filter rules
Filter rules determine which protocol log streams are delivered.
Create a rule: On the Custom Filter Rules tab, click Create Rule. In the Protocol Log Filter Rule panel, set the Filter Logic and Stream Information, then click OK.
When multiple filter rules apply, note the following priority behavior:
Multiple rules in the same whitelist or blacklist are combined with
ORlogic.Blacklist rules take priority over whitelist rules. If a conflict occurs, the blacklist rule applies.
Edit a rule: In the Actions column of the target rule, click Edit. Modify the settings in the Protocol Log Filter Rule panel and click OK.
Delete a rule: In the Actions column of the target rule, click Delete, then confirm.
Deleting a filter rule means logs that previously matched it will no longer be filtered.
Custom delivery fields
On the Custom Delivery Fields tab, select the fields to include in delivered logs, then click OK.
Query logs
When you open the Log Analysis page, a default query runs automatically and results appear immediately.
Write a query
Enter statements in the search box using the format:
query statement | analytic statementQuery statements find and filter log data. Use a query statement alone to search logs, or combine it with an analytic statement to compute statistics.
Supported content: keywords, numeric values, numeric ranges, and wildcards (
*).A space or bare
*returns all logs with no filter applied.For full syntax, see Query syntax and features.
Analytic statements aggregate and transform query results — for example, summing traffic bytes, counting events, or calculating year-over-year (YoY) and month-over-month (MoM) comparisons. An analytic statement must follow a query statement after the | separator. For syntax, see Aggregate functions.
To build queries interactively without writing SQL, click the ![]() icon to the right of the search box. This opens Data Explorer, a visual query builder. For more information, see High-Performance and Fully Accurate Query and Analysis (Dedicated SQL Edition).
icon to the right of the search box. This opens Data Explorer, a visual query builder. For more information, see High-Performance and Fully Accurate Query and Analysis (Dedicated SQL Edition).
Full-text search
Full-text search matches keywords across all log fields.
Wrap a keyword in double quotation marks to match it exactly:
"error"Separate keywords with a space or
andto require all terms:www.aliyun.com passorwww.aliyun.com and passUse parentheses with
orfor alternatives:www.aliyun.com and (pass or tcp)Append
*as a suffix wildcard:www.aliyun.com and tcp_*
Wildcards are supported only as a suffix. For example, tcp_* is valid, but *_not_establish is not.
Field-specific search
Field-specific search targets individual log fields.
Basic format:
field:valueNumeric comparison:
field >= valueCombine fields:
src_ip: 192.XX.XX.22 and dst_ip: 192.XX.XX.54Check whether a field is present:
cloud_instance_id: *Check whether a field is absent:
not cloud_instance_id: *
Field-specific search can be combined with full-text search in the same query. For the list of indexed fields, see Fields that support indexing.
Common query examples
The following queries cover the most common investigation scenarios. All examples use the log_type, direction, and rule ID fields to scope results precisely.
Traffic volume
Measure total inbound traffic and packet count from the Internet to a specific asset range:
log_type:internet_log and direction:"in" and dst_ip:1.2.*.* | select sum(in_packet_bytes) as flow, sum(in_packet_count) as packetFind the top 10 NAT Gateway traffic flows, grouped by source IP, destination IP, and port:
log_type:nat_firewall_log | select src_ip, dst_ip, dst_port, sum(in_packet_bytes) as in_bytes, sum(out_packet_bytes) as out_bytes, sum(total_packet_bytes) as total_bytes group by src_ip, dst_ip, dst_port order by total_bytes desc limit 10Access control
Find inbound Internet traffic that matched an access control policy:
log_type:internet_log and direction:"in" and not acl_rule_id:00000000-0000-0000-0000-000000000000A value of 0 for not acl_rule_id indicates a match for the access control policy, while any other value indicates no match.
Find the top 10 blocked outbound destinations — internal-to-Internet traffic dropped by an access control policy:
log_type:internet_log and direction:out and not acl_rule_id:00000000-0000-0000-0000-000000000000 and rule_result:drop | select dst_ip, dst_port, count(*) as cnt group by dst_ip, dst_port order by cnt desc limit 10Find the top 10 source IPs, destination IPs, and applications for outbound HTTPS sessions with destination port 443, more than three packets (completed TCP three-way handshake), and no domain name detected:
log_type:internet_log and direction:out and dst_port:443 and total_packet_count>3 and domain:""| select array_agg(distinct src_ip) as srcip, array_agg(distinct dst_ip) as dstip, slice(split(dst_ip,'.' ,4),1,3) as dstip_c, app_name, COUNT(1) as cnt GROUP by dstip_c,app_name order by cnt desc limit 10This query filters for sessions on port 443 with more than three packets (completed TCP three-way handshake) and no detected domain name, then groups results by destination IP segment and application.
Attack prevention
Find inbound Internet traffic that matched an attack prevention (IPS) policy:
log_type:internet_log and direction:"in" and not ips_rule_id:00000000-0000-0000-0000-000000000000If the value of not ips_rule_id is 0, an attack prevention policy is matched. Otherwise, no attack prevention policy is matched.
View outbound traffic that matched an IPS policy, with full details including IP addresses, ports, application, domain, and rule result:
log_type:internet_log and direction:out and not ips_rule_id:00000000-0000-0000-0000-000000000000 | select src_ip, dst_ip, dst_port,app_name, domain,ips_rule_id, ips_rule_name, rule_resultClick Query/Analysis to run the query. For more information about viewing results, see View query and analysis results.
Analyze query results
Results appear in the histogram and Raw Logs tab.
Histogram
The histogram shows log volume distributed over time.
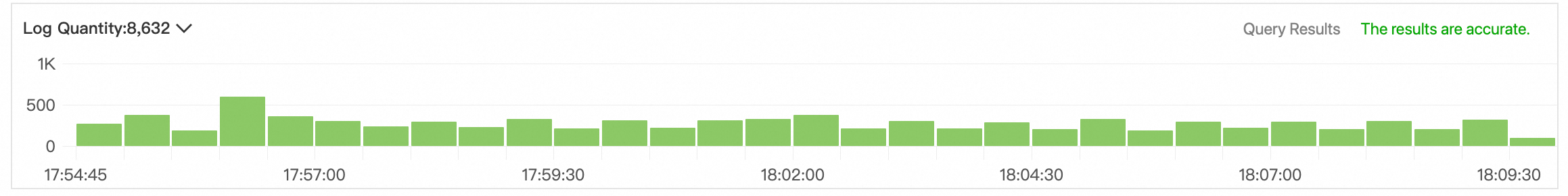
Hover over a green bar to see the time range and log count for that interval.
Double-click a green bar to drill down to a finer time granularity. The Raw Logs tab updates to show results for that time range.
Raw logs
The Raw Logs tab shows query results in raw or table format.
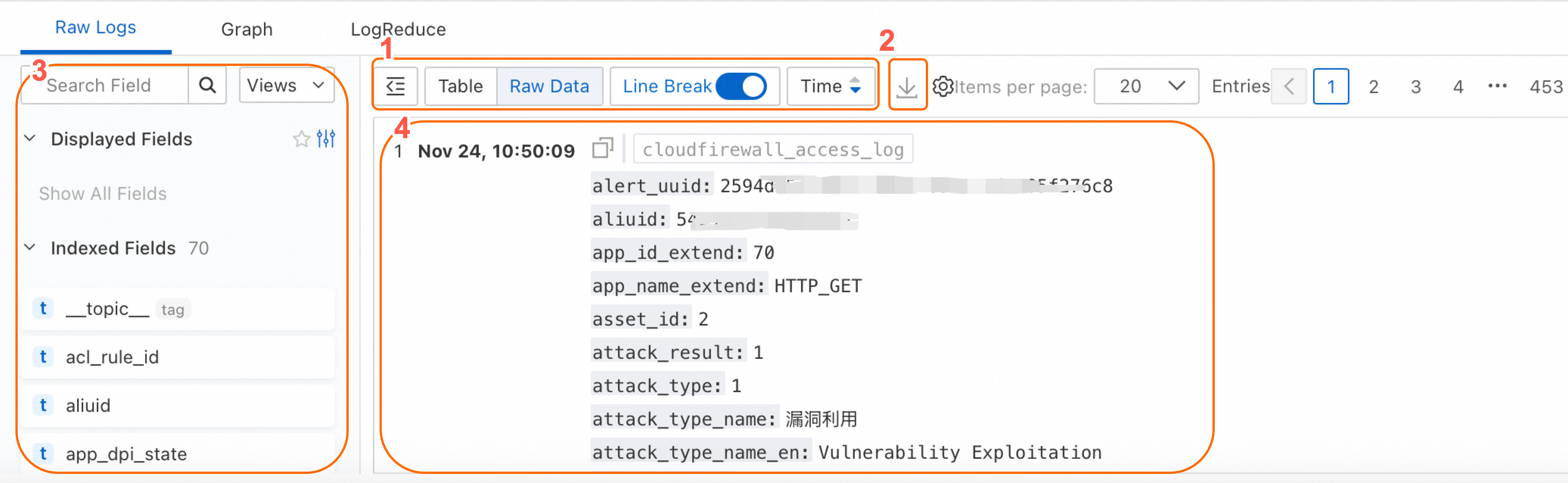
| Number | Description |
|---|---|
| ① | Switch the log display format, sort order, and other display settings. |
| ② | Click the |
| ③ | Shows Display Fields, Indexed Fields, and system fields. Click the add icon next to an indexed field to show it in the log detail panel. Click the remove icon next to a display field to hide it. If no fields are added to Display Fields, the default fields appear. Click the chart icon next to a field to view its Basic Distribution and Statistics. For more information, see Field settings. |
| ④ | Shows individual log entries. For field descriptions, see Log fields. Click the copy icon to copy a log entry. Click the SLS Copilot icon to summarize information, find errors, or perform other analysis tasks on the log content. Click any field value in a log entry to access contextual actions: open a Logstore, run a quick query, navigate to a dashboard, or open a custom HTTP link. For more information, see Event configuration. 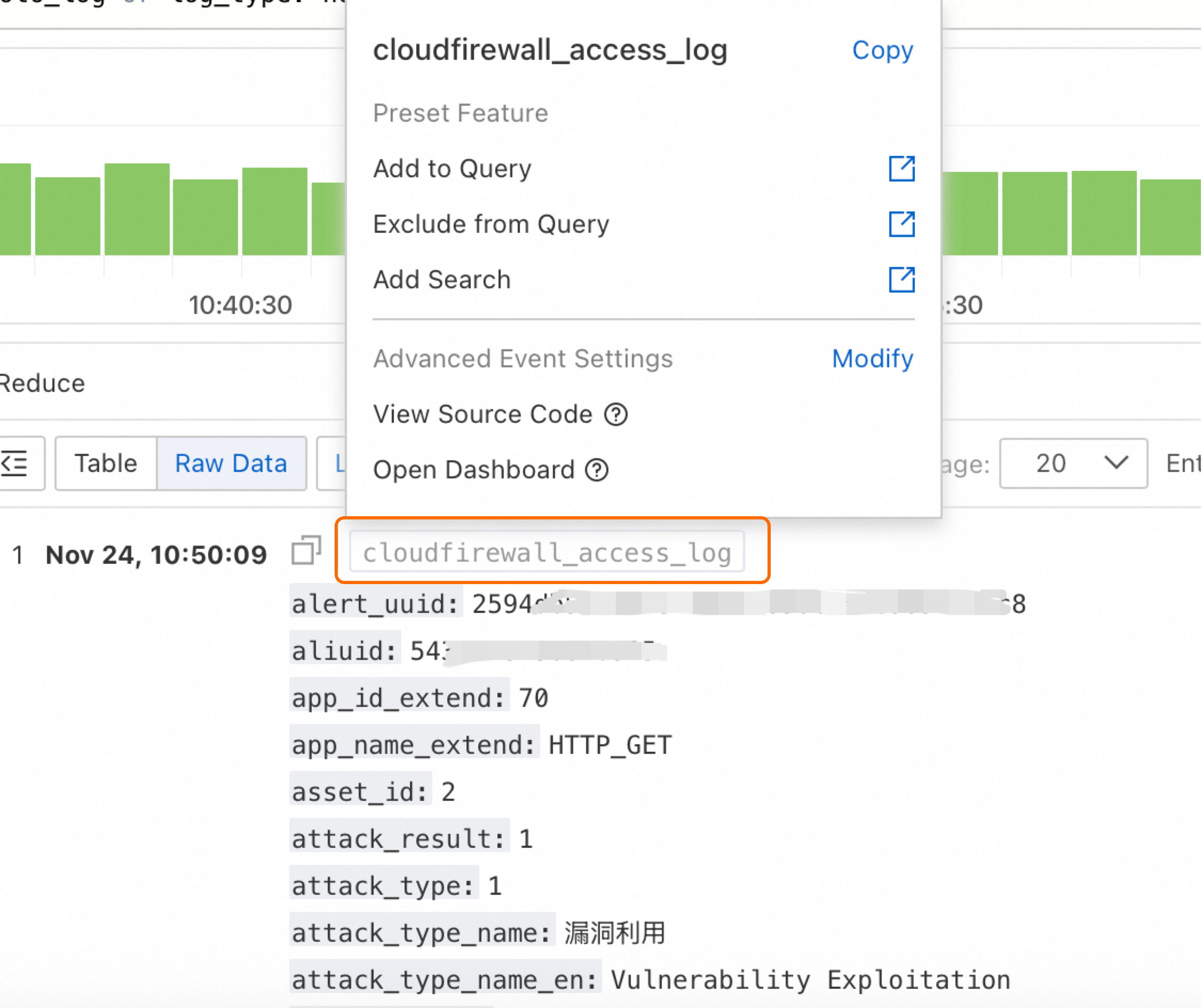 |
What's next
Log fields — field names, types, and descriptions for Cloud Firewall logs.
Export logs — download query results to your local machine.
Create an OSS shipping task (New) — ship logs to an OSS bucket for long-term storage and offline analysis.