The Vulnerability Prevention page lists vulnerabilities exploitable over the network that are automatically detected by Security Center and synced to Cloud Firewall. This feature helps you defend against attacks that target these vulnerabilities. You can manually enable Cloud Firewall and its intrusion prevention system (IPS) rules to block exploits and protect your assets from intrusion. This topic describes the types of vulnerabilities that Cloud Firewall can detect and explains how to configure vulnerability prevention.
Supported vulnerability types
Cloud Firewall syncs only vulnerabilities that are detected by network scans. For a list of supported vulnerability types, see the console.
Cloud Firewall displays vulnerability prevention data only for assets with detected vulnerabilities or a history of attacks.
Cloud Firewall syncs some types of vulnerabilities detected by Security Center and displays them on the Vulnerability Prevention page. If a protected asset is at risk of a vulnerability, Cloud Firewall can analyze exploit attempts in attack traffic and take protective action.
If you use the Enterprise Edition or Ultimate Edition of Cloud Firewall, you can view the vulnerabilities that Cloud Firewall can defend against in the section. For more information, see IPS Configuration.
Limitations
The vulnerability prevention feature is available only in the pay-as-you-go and subscription editions of Cloud Firewall.
The vulnerability prevention feature supports automatic vulnerability detection but does not support manual detection.
NoteTo perform a manual real-time vulnerability scan, go to the Vulnerability Fix page in the Security Center console. For more information, see Scan for vulnerabilities.
For Server Load Balancer (SLB) instances in a classic network, only blocking based on threat intelligence is supported.
The intrusion prevention system (IPS) module of Cloud Firewall cannot parse traffic encrypted with Transport Layer Security (TLS) or Secure Sockets Layer (SSL). Therefore, this traffic cannot be detected or protected.
Prerequisites
On the page, set Threat Engine Mode to Block Mode.
If you do not set the Threat Engine Mode to Block Mode, on the Vulnerability Prevention page, the protection status for all vulnerabilities is Alert Only. This means that Cloud Firewall only logs and generates alerts for detected vulnerabilities and does not block them. For more information about the threat engine mode, see Threat Engine Mode.
Procedure
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose .
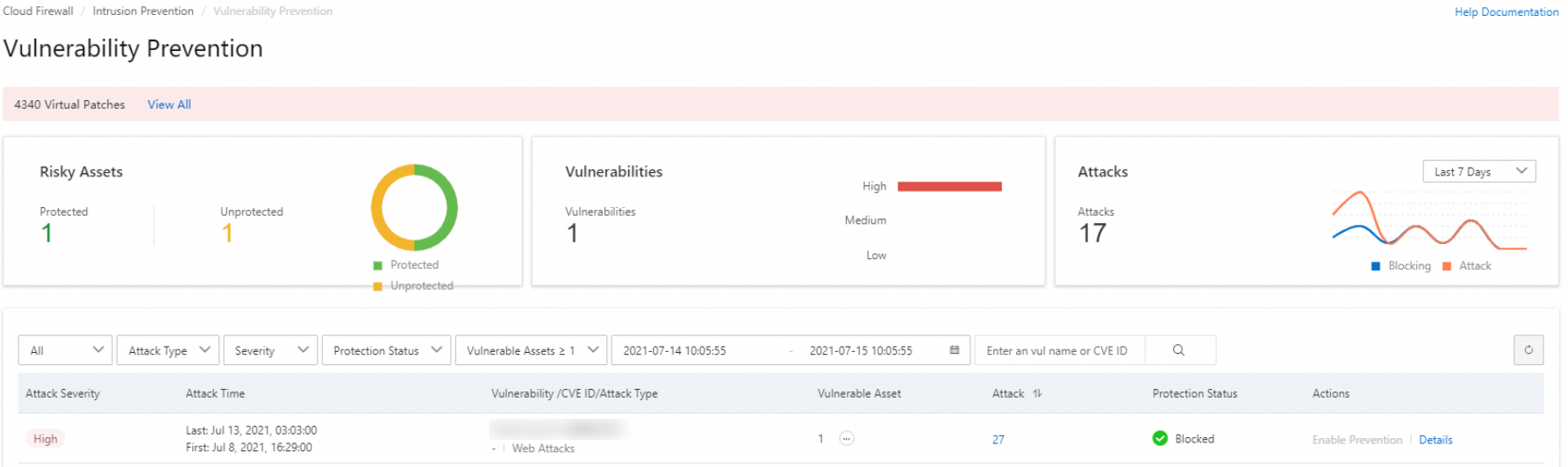
On the Vulnerability Prevention page, review detected vulnerability attacks on your assets.
The Vulnerability Prevention page displays detection results from the last day, 7 days, or month.
Hover over the
 icon in the Vulnerable Assets column to view the IP addresses of the vulnerable assets.
icon in the Vulnerable Assets column to view the IP addresses of the vulnerable assets.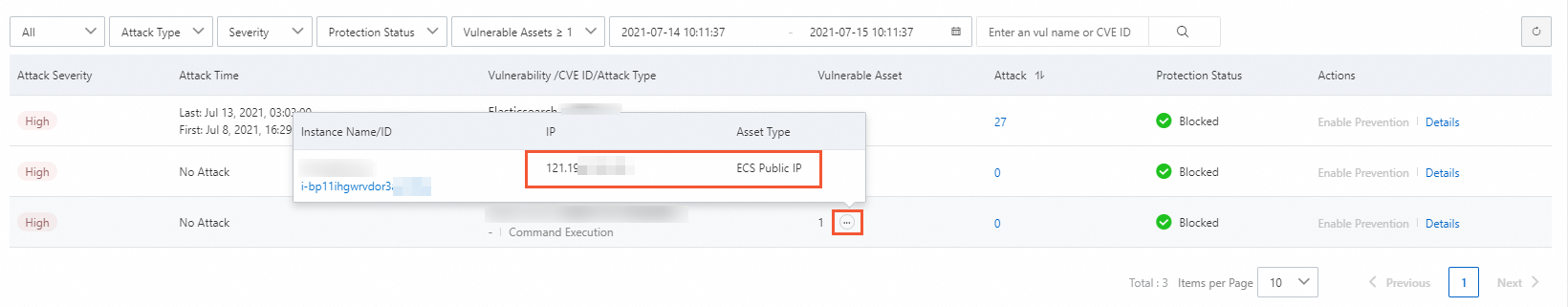
Attack Count: The number of attacks on your assets that exploit this vulnerability.
Protection Status: The action Cloud Firewall takes against exploits of this vulnerability.
Blocked: Cloud Firewall blocked attacks that exploited this vulnerability.
Alert Only: Cloud Firewall detects exploits of the vulnerability and reports alerts but does not block them.
Partial Protection: Only some of the affected ECS instances are protected by Cloud Firewall.
Details: Click Details to open the Vulnerability and Protection Details page and view detailed information about the vulnerability, including its name, risk level, CVE ID, and affected assets.
On the Vulnerability Prevention page, locate a vulnerability with the Alert Only status and click Enable Protection in the Actions column.
Enabling protection has two effects. If Cloud Firewall is not enabled for the server that has the vulnerability, clicking Enable Protection automatically enables the Internet Border Firewall for the server. If Cloud Firewall is already enabled for the server, clicking Enable Protection enables Block Mode for the Threat Engine Mode on the IPS Configuration page. The vulnerability status may take 1 to 2 minutes to update. Please wait.
NoteAfter you enable vulnerability prevention, existing access control policies continue to take effect on the newly protected assets. Ensure that traffic to their public service ports is allowed on the Inbound tab of the Internet Border Firewall page.
Related topics
The Prevention Configuration feature lets you set the threat engine's operating mode and configure threat intelligence, basic protection, intelligent defense, and virtual patching to more accurately identify and block intrusion risks. For more information, see IPS Configuration.
The intrusion prevention (IPS) capability can detect and block malicious traffic in real time, including hacker attacks, exploits, brute-force attacks, worms, mining programs, backdoors, trojans, and DoS attacks, and protect your cloud-based information systems and network architecture. For more information, see IPS capability overview and Intrusion prevention.