Security Center connects to your AWS account to monitor and protect your AWS assets using Host protection, Cloud Security Posture Management (CSPM), and Agentless Detection. CSPM discovers and manages security risks in your cloud assets through automated risk checks, baseline scans, and attack path analysis. It identifies security vulnerabilities such as cloud product configuration errors and server configuration defects, and provides remediation suggestions to address them.
How Security Center accesses your AWS account: Security Center does not store your long-term root user credentials. It uses your root user AccessKey pair only for the initial authorization step, during which it automatically creates a dedicated IAM user (prefixed with AlibabaSasSubAccount_) with limited permissions. All subsequent access uses this IAM user. After initial authorization, delete the root user AccessKey pair immediately.
Choose an onboarding plan
Two plans are available:
| Quick configuration | Manual configuration | |
|---|---|---|
| Authorization account type | Root user AccessKey pair (initial authorization only) | IAM user with least privilege access |
| Supported features | Host | Host, CSPM, Agentless Detection (Outside Chinese Mainland only) |
| Configuration complexity | Simple | Medium |
When to use each plan:
Use Quick configuration if you only need to monitor AWS EC2 hosts and want to get started quickly.
Use Manual configuration if you need CSPM, Agentless Detection, or want to follow the principle of least privilege from the start.
Plan 1: Quick configuration (host assets only)
Prerequisites
Before you begin, confirm that you have:
An AWS account with root user access
A Security Center account with sufficient permissions to configure multi-cloud assets
Step 1: Create root user credentials in AWS
The root user's AccessKey pair is used only for the initial authorization. Security Center uses it to automatically create a dedicated IAM user (prefixed with AlibabaSasSubAccount_) in your AWS account. After authorization succeeds, immediately delete this root user AccessKey pair to reduce security risks.
Log in to the AWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM console as the root user and click My Security Credentials on the dashboard.
ImportantOnly the root user can access Security Credentials.
On the My Security Credentials page, click Create access key and configure the following settings:
Use case: Select a use case that matches your scenario. If none apply, select Other.
Set description tag (optional): Enter a tag to identify this key. Tags can be up to 256 characters and can contain letters, digits, spaces, and these special characters:
_ . : / = + - @.
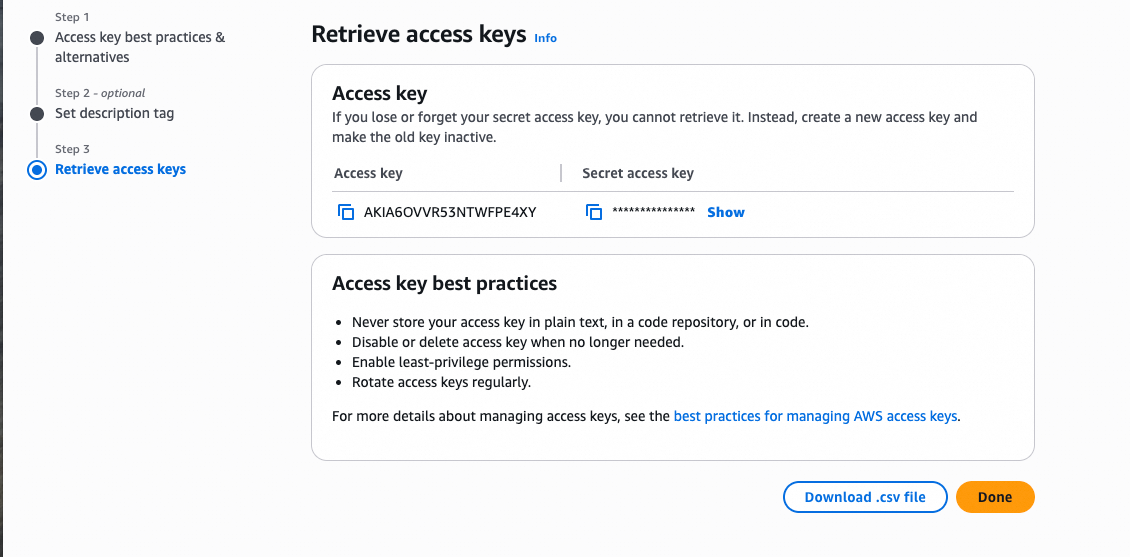
On the Retrieve access key page, copy and save the Access key (Access Key ID) and Secret access key.
Click Download .csv file to save the AccessKey pair to your computer.
Step 2: Complete onboarding in Security Center
Go to the AWS asset provisioning page. The recommended path is: Alternatively, on any of the following pages, find the
 icon in the Multi-cloud Service Access section and click Provision or Grant:
icon in the Multi-cloud Service Access section and click Provision or Grant:Assets > Host
Risk Governance > CSPM > Cloud Service Configuration Risk
Agentic SOC > Service Integration
Protection Configuration > Host Protection > Agentless Detection (switch the region to Outside Chinese Mainland first)
Log in to the Security Center consoleSecurity Center console.Log on to the Security Center console.Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner of the console, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
On the Multi-cloud Configuration Management > Multi-cloud Assets tab, click Grant Permission and select AWS.
In the Add Assets Outside Cloud panel, select Quick Configuration, select the features to provision, and click Next.
On the Submit AccessKey Pair page, enter the credentials you created in step 1:
Access Key ID and Secret Access Key: Enter the root user credentials.
Provisioning Region: Select an available AWS region. Security Center uses this region to verify asset accessibility.
Domain: Select China if you use an AWS China proxy. Otherwise, select International.
Click Next. Security Center automatically verifies the credentials and permissions.
If verification fails, see Credential and permission verification failed after I entered the AccessKey pair.
Configure the synchronization policy:
Select region: Select the AWS regions containing the assets to onboard. > Note: Asset data is stored in the data center that corresponds to the region selected in the upper-left corner of the Security Center console: Chinese Mainland (data centers in the Chinese mainland) or Outside Chinese Mainland (data center in Singapore).
Region Management: Selected by default. When enabled, assets in new AWS regions added to your account are automatically synchronized.
Host Asset Synchronization Frequency: Set the interval for automatically synchronizing AWS EC2 host assets. Set to Off to disable.
AK Service Status Check: Set the interval for Security Center to check the validity of the AWS account AccessKey pair. Set to Off to disable.
Click Synchronize Assets. Security Center automatically synchronizes EC2 host assets from your AWS account.
ImportantSecurity Center automatically creates an IAM user in AWS (prefixed with
AlibabaSasSubAccount_). Do not delete or disable this IAM user or its AccessKey pair. Doing so interrupts asset provisioning and security monitoring.
Step 3: Delete the root user AccessKey pair
After the assets are provisioned, immediately delete the root user AccessKey pair used for initial authorization.
Log in to the AWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM console as the root user and click My Security Credentials on the dashboard.
In the Access keys section, locate the AccessKey pair used for this authorization. In the Actions column, click Delete and confirm.
Plan 2: Manual configuration
This plan creates an IAM user with least privilege access in AWS and supports all features: Host, CSPM, and Agentless Detection.
Prerequisites
Before you begin, confirm that you have:
An AWS account with IAM administrative access
A Security Center account with sufficient permissions to configure multi-cloud assets
(For Agentless Detection) Familiarity with AWS CloudTrail, S3, and SQS — you will need to create a log delivery pipeline in AWS before onboarding
Step 1: Create an IAM user with least privilege access in AWS
Create a dedicated IAM user for Security Center integration and retrieve its AccessKey pair.
For detailed steps on creating IAM users and adding permissions, see the AWS documentation on creating users and adding permissions.
Log in to the AWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM console. In the left navigation pane, click Users and then click Create user.
Specify the user details:
User name: Enter an identifiable name, such as
aliyun-security-center-user.Provide user access to the AWS Management Console: Do not select this option. This user is for API access only.
Set the user permissions:
Select Attach policies directly.
Attach the policies that correspond to the features you plan to use:
Feature AWS policy Notes Host AmazonEC2ReadOnlyAccess,IAMReadOnlyAccess— CSPM ReadOnlyAccessFor log-based risk detection, also complete the audit log configuration in Configure AWS audit logs for CSPM Agentless Detection Custom policy (must create manually) Requires a CloudTrail → S3 → SQS log delivery pipeline. See Create a custom policy for Agentless Detection 
Review the user details and permission policies, then click Create user.
Create and save the IAM user AccessKey pair:
In the Users list, click the username to open the details page.
On the Summary tab, click Create access key and configure:
Use case: Select a use case for your scenario. If none apply, select Other.
Set description tag (optional): Enter a tag such as
for-aliyun-sasc.
Click Create access key. On the Retrieve access key page, copy and save the Access key and Secret access key.
Step 2: Complete onboarding in Security Center
Log in to the Security Center consoleSecurity Center console. In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland. On the Multi-cloud Configuration Management > Multi-cloud Assets tab, click Grant Permission and select AWS.
For other entry points, see step 2 in Plan 1.
In the Add Assets Outside Cloud panel, select Manual Configuration, select the features to provision, and click Next:
Host: Automatically discovers and synchronizes AWS EC2 host assets.
CSPM: Scans AWS cloud product configurations for configuration risks.
Agentless Detection (Outside Chinese Mainland only): Scans AWS assets for vulnerabilities and risks.
On the Submit AccessKey Pair page, enter the IAM user credentials:
IAM user Access Key ID and IAM user Secret Access Key: Enter the credentials created in step 1.
Provisioning Region: Select an available AWS region. Security Center uses this region to verify asset accessibility.
Domain: Select China if you use an AWS China proxy. Otherwise, select International.
Click Next. Security Center automatically verifies the credentials and permissions.
If verification fails, see Credential and permission verification failed after I entered the AccessKey pair.
(Optional) Configure audit logs for CSPM: If you want to use the log audit feature of CSPM, complete the following. Otherwise, click Skip.
AWS Region: Enter the ID of the region where the SQS queue is located. For region IDs, see AWS region IDs.
SQS Queue Name: Enter the name of the SQS queue you created.
ImportantComplete the required configurations in the AWS console before proceeding. See Configure AWS audit logs for CSPM.
Configure the synchronization policy on the Policy Configuration page:
Select region: Select the AWS regions containing the assets to onboard. > Note: Asset data is stored in the data center that corresponds to the region selected in the upper-left corner of the console: Chinese Mainland (data centers in the Chinese mainland) or Outside Chinese Mainland (data center in Singapore).
Region Management: Selected by default. When enabled, assets in new AWS regions added to your account are automatically synchronized.
Host Asset Synchronization Frequency: Set the interval for synchronizing AWS EC2 host assets. Set to Off to disable. (Required only if provisioning Host.)
Cloud Service Synchronization Frequency: Set the interval for synchronizing AWS cloud product configurations. Set to Off to disable. (Required only if provisioning CSPM.)
AK Service Status Check: Set the interval for Security Center to check the validity of the AWS account AccessKey pair. Set to Off to disable.
Click Synchronize Assets. Security Center synchronizes the data from your AWS account.
Manage provisioned assets
Host assets
Go to Assets > Host. In the multi-cloud asset provisioning section, click the ![]() icon to view provisioned AWS hosts. For more information, see Host assets.
icon to view provisioned AWS hosts. For more information, see Host assets.
To protect your AWS EC2 hosts:
Install the client: Install the Security Center client on each AWS host. When running the installation command, set Service Provider to AWS. See Install the client.
Upgrade to a paid edition: The Free edition provides basic detection only. To get antivirus, vulnerability remediation, and intrusion prevention, attach a paid edition (Anti-virus edition or higher) to your AWS hosts. See Manage security authorizations for hosts and containers.
Cloud Security Posture Management (CSPM)
Go to Assets > Cloud Product. In the left pane under All Alibaba Cloud Services, click AWS to view your provisioned assets. For more information, see Viewing cloud product information.
Run a configuration risk check: See Configure and run a cloud platform configuration risk check policy.
Handle risk items: See View and handle failed cloud platform configuration risk check items.
Agentless Detection
Go to Protection Configuration > Host Protection > Agentless Detection. Switch the region to Outside Chinese Mainland. In the Add Multi-cloud Asset area, click the ![]() icon to view imported AWS assets. After the assets are imported, you can use the Agentless Detection feature to scan AWS hosts for vulnerabilities and baselines. For more information, see Agentless Detection.
icon to view imported AWS assets. After the assets are imported, you can use the Agentless Detection feature to scan AWS hosts for vulnerabilities and baselines. For more information, see Agentless Detection.
Advanced configuration
Create a custom policy for Agentless Detection
For more information, see the AWS documentation on creating a user and adding permissions.
Log in to the AWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM console. On the Policies page, click Create Policy.
In the Policy Editor section, select JSON and paste the following policy:
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "ec2:DeleteSubnet", "ec2:DeleteVpcEndpoints", "ec2:DeleteInternetGateway", "ec2:TerminateInstances", "ec2:StopInstances", "ec2:DeleteSecurityGroup", "ec2:DeleteVpc" ], "Resource": "*", "Condition": { "StringLike": { "ec2:ResourceTag/Name": "alibaba-cloud-security-scan*" } } }, { "Effect": "Allow", "Action": [ "ec2:DeleteSnapshot" ], "Resource": "*", "Condition": { "StringLike": { "ec2:ResourceTag/Name": "SAS_Agentless*" } } }, { "Effect": "Allow", "Action": [ "ec2:CopySnapshot", "ec2:AuthorizeSecurityGroupIngress", "ec2:DescribeInstances", "ec2:CreateImage", "ec2:CreateVpc", "ec2:AttachInternetGateway", "ec2:CopyImage", "ec2:ModifyImageAttribute", "ec2:DescribeSnapshots", "ec2:ModifySubnetAttribute", "ec2:DescribeInternetGateways", "ec2:ModifySnapshotAttribute", "ec2:DescribeInstanceTypeOfferings", "ec2:DescribeAvailabilityZones", "ec2:CreateInternetGateway", "ec2:CreateSecurityGroup", "ec2:DescribeVolumes", "ec2:CreateSnapshot", "ec2:AuthorizeSecurityGroupEgress", "ec2:RunInstances", "ec2:DetachInternetGateway", "ec2:DescribeSecurityGroups", "ec2:DescribeImages", "ec2:CreateVpcEndpoint", "ec2:CreateSnapshots", "ec2:DescribeVpcs", "ec2:DescribeImageAttribute", "ec2:DescribeVpcEndpoints", "ec2:CreateSubnet", "ec2:DescribeSubnets", "ec2:ModifyVpcEndpoint", "ec2:CreateTags", "ec2:DescribeRouteTables", "ec2:CreateRoute", "ec2:DescribeRegions", "kms:Decrypt", "kms:DescribeKey", "kms:CreateGrant", "kms:ListGrants", "kms:RevokeGrant", "kms:GenerateDataKey", "kms:ReEncrypt*", "iam:GetUser" ], "Resource": "*" } ] }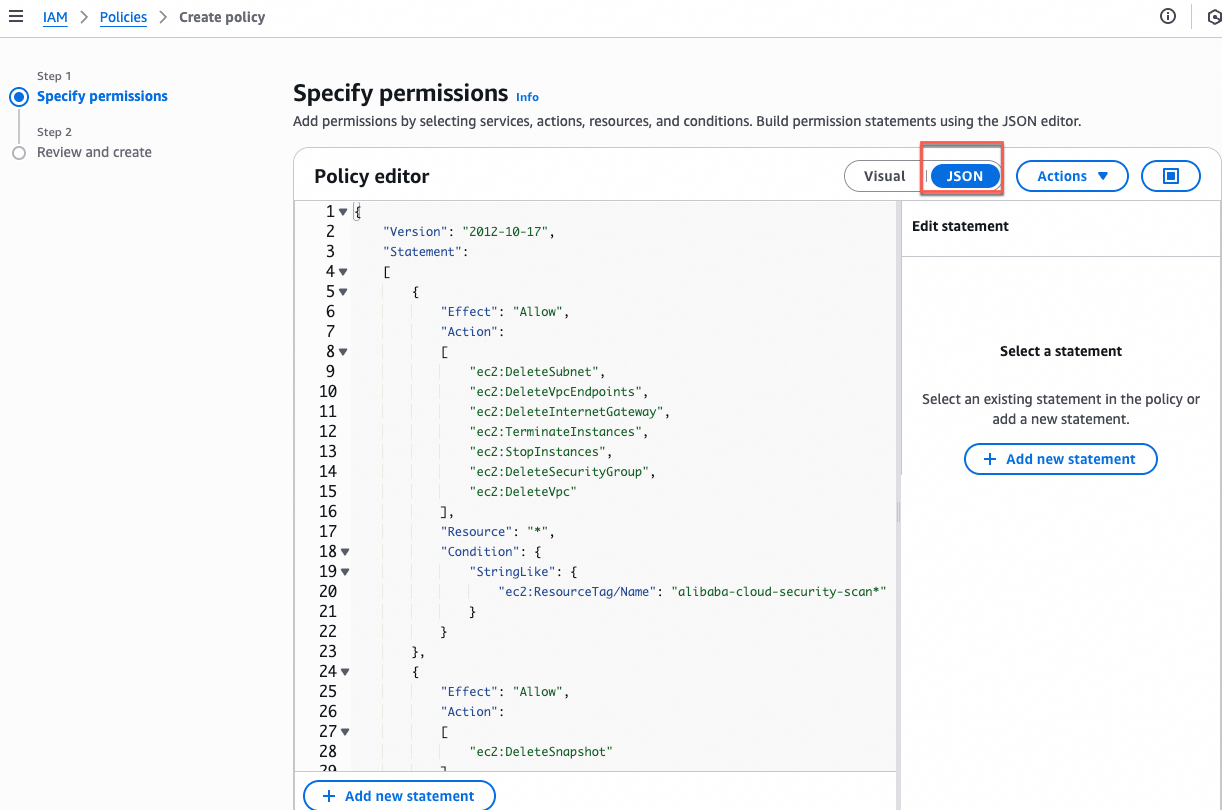
Click Next, enter a policy name such as
AliyunSASC-AgentlessScan-Policy, and click Create Policy.Attach this policy to the IAM user. See Set user permissions in step 1 of Plan 2.
Configure AWS audit logs for CSPM
This section walks through the four-step pipeline required to enable log-based CSPM risk detection: CloudTrail collects management events, stores them in an S3 bucket, and delivers event notifications to an SQS queue. Security Center reads from that queue to perform log audits.
Step 1: Create a CloudTrail trail
A CloudTrail trail records all management operations on cloud resources in a specified region. For more information, see the AWS documentation on creating a trail.
Log in to the AWS CloudTrail console. In the region selector in the upper-right corner, select the AWS region to monitor. On the dashboard or in the left navigation pane, select Trails and click Create Trail.
On the Choose Trail Attributes page, configure the following settings and click Next:
Trail name: Enter a descriptive name such as
aliyun-sasc-audit-trail.Storage Location: > Important: Record the bucket name for later use.
Create New S3 Bucket: Enter a globally unique bucket name in all lowercase letters.
Use Existing S3 Bucket: In the Trail Log Bucket Name field, click Browse and select the target bucket.
Log File SSE-KMS Encryption: Clear this check box. Use the default SSE-S3 encryption (not SSE-KMS).
On the Choose Log Events page, configure: Click Next.
Event Type: Management events.
API Activity: Read, Write.
On the Review and Create page, review the configuration and click Create Trail.
Step 2: Create an SQS message queue
This queue receives log file event notifications from the S3 bucket. For more information, see the AWS documentation on creating a message queue.
Log in to the AWS SQS consoleAWS SQS console, select the region, and click Create queue.
WarningThe queue region must be the same as the region where you created the CloudTrail trail.
Configure the queue:
Type: Standard.
Name: Enter an identifiable name such as
aliyun-sasc-log-queue. > Important: This name is used to generate the queue's unique ARN and for access policy configuration. Enter it exactly as intended.
Configure the access policy:
In the Access policy panel, select Advanced. > Important: Record the Account ID and Queue ARN from the default policy for the next steps.
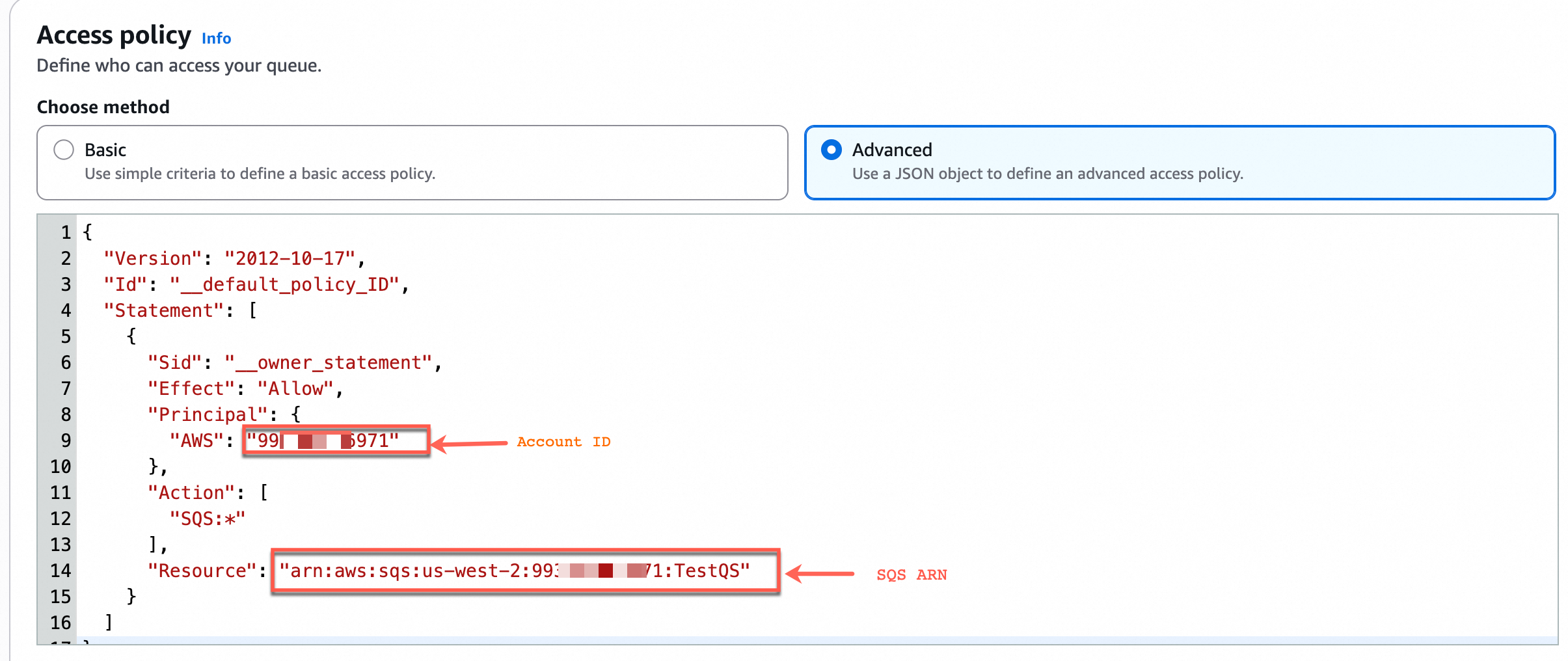
Replace all existing content in the policy editor with the following JSON template:
{ "Version": "2012-10-17", "Id": "__default_policy_ID", "Statement": [ { "Sid": "__owner_statement", "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::${Account ID}:root" }, "Action": "SQS:*", "Resource": "${SQS ARN}" }, { "Sid": "example-statement-ID", "Effect": "Allow", "Principal": { "Service": "s3.amazonaws.com" }, "Action": [ "SQS:SendMessage" ], "Resource": "${SQS ARN}", "Condition": { "ArnLike": { "aws:SourceArn": "arn:aws:s3:*:*:${S3 bucket name}" } } } ] }Replace the placeholders in the template:
Placeholder
How to get the value
Example
${Account ID}The Account ID recorded in the previous step
99********1${SQS ARN}The Queue ARN recorded in the previous step
arn:aws:sqs:ap-northeast-1:123******012:aliyun-sasc-log-queue${S3 bucket name}The name of the S3 bucket set when creating the CloudTrail trail. Find it in the AWS S3 console on the bucket details page.
aws-cloudtrail-logs-123******12-abcdef
Scroll to the bottom of the page and click Create queue.
Step 3: Create an S3 event notification
Configure the S3 bucket to send a notification to the SQS queue whenever a new log file is generated. For more information, see the AWS documentation on Amazon S3 Event Notifications.
Log in to the AWS S3 consoleAWS S3 console and select the region.
WarningThe region must be the same as the region where you created the CloudTrail trail.
On the General purpose buckets tab, click the S3 bucket you specified when creating the CloudTrail trail to open its details page.
On the Properties tab, in the Event notifications section, click Create event notification and configure:
Event types: Select Put.
Destination: Select SQS Queue and specify the queue created in step 2.
Click Save changes.
Step 4: Grant the IAM user permission to read from the SQS queue
Log in to the AWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM consoleAWS IAM console. On the Policies page, click Create Policy and configure:
Service: SQS.
Effect: Allow.
Read: GetQueueUrl, ReceiveMessage.
Write: ReceiveMessage.
Resources: Click Add ARNs and enter the Queue ARN. > Note: Find the Queue ARN in the AWS SQS consoleAWS SQS console on the queue details page.
Attach the policy to the IAM user. See Set user permissions in step 1 of Plan 2.
FAQ
Some of my provisioned AWS resources are not visible in Security Center. What should I do?
Check whether you selected the AWS region where the resource is located in the provisioning configuration. If the region is correct, wait for synchronization to complete — there may be a delay after initial provisioning or configuration changes.
Credential and permission verification failed after I entered the AccessKey pair. What should I do?
The most common causes:
Insufficient permissions: The IAM user may not have the required policies attached. Go to the AWS console and add the missing permission policies. See Set user permissions.
Wrong account type (Quick configuration only): Quick configuration requires a root user AccessKey pair. If you used an IAM user key, log in to AWS as the root user and create a new AccessKey pair. See Step 1: Create root user credentials in AWS.
Region not available: The selected region may not be accessible. Switch to another available region or change the domain setting, then resubmit.