After running cloud service configuration checks, review failed check items in the Security Center console and apply the provided remediation steps. Fixing risky configurations improves the security, performance, and reliability of your cloud environment.
Prerequisites
Before you begin, ensure that you have:
Access to the Security Center console
The required permissions to modify cloud service configurations
View check results
Log on to the Security Center console. In the top navigation bar, select the region of the assets you want to manage: China or Outside China.
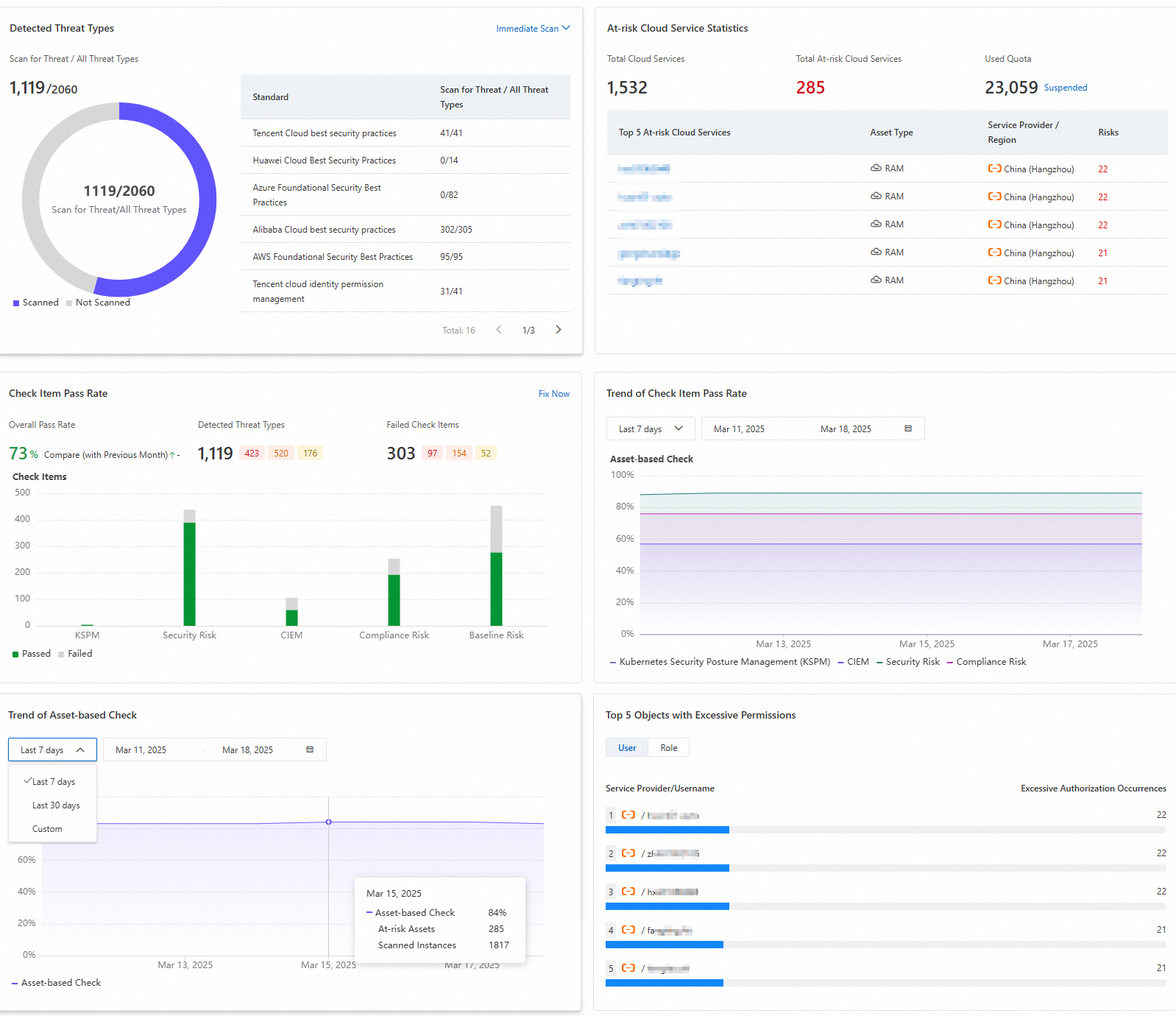
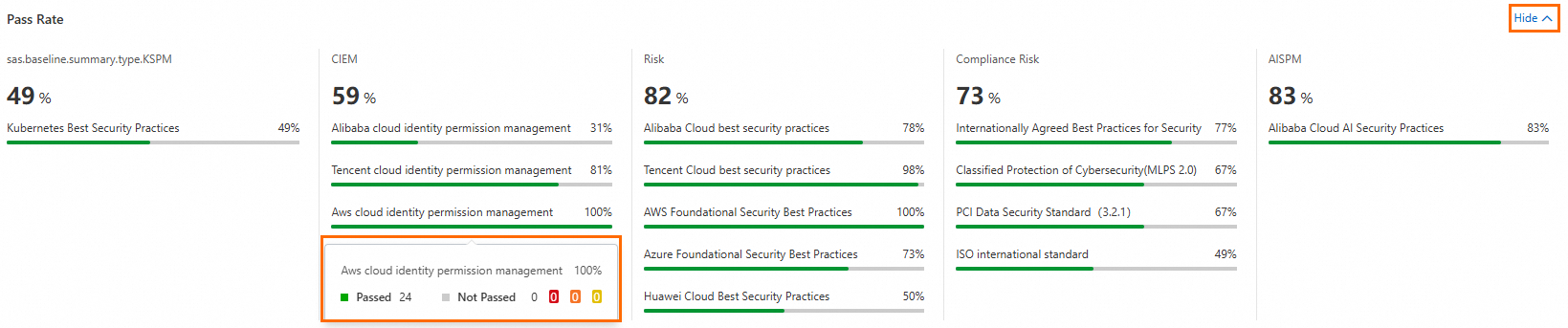
(Optional) Go to Risk Governance > CSPM > Risk Overview for a high-level picture of your configuration risks. Select a cloud provider to filter assets, or leave it blank to view all. The risk overview includes: In the At-risk Cloud Service Statistics area, the pay-as-you-go mode displays Used Quota and the subscription mode displays Remaining Quota. Click Scale Out to purchase additional quota.
Detected Threat Types
At-risk Cloud Service Statistics
Check Item Pass Rate
Trend of Check Item Pass Rate
Trend of Asset-based Check
Top 5 Objects with Excessive Permissions
Go to Risk Governance > CSPM > Cloud Service Configuration Risk to review specific check items.
At the top of the page, hover over the Check Item Pass Rate line to see the counts of high-risk (red), medium-risk (orange), low-risk (yellow), and failed (gray) check items. > Important: High-risk items pose major threats to your assets. Address them as soon as possible.
Find the risk items to address.
 Alternatively, click Fix Now in the Check Item Pass Rate area on the Risk Overview tab to go directly to the Cloud Service Configuration Risk tab filtered to items that support one-click fixing.
Alternatively, click Fix Now in the Check Item Pass Rate area on the Risk Overview tab to go directly to the Cloud Service Configuration Risk tab filtered to items that support one-click fixing.In the All Check Items list on the left, click a check item type to see its associated risks in the list on the right.
Use the filter options above the list to narrow results by risk level, status, check item name, or check item type. For example, filter by one-click fix support to see which items Security Center can fix automatically.
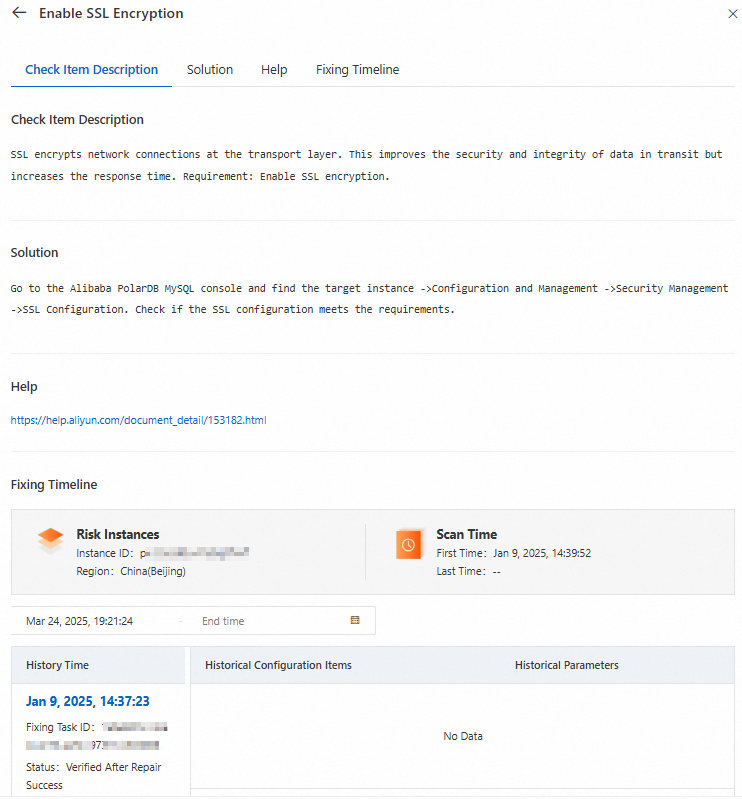
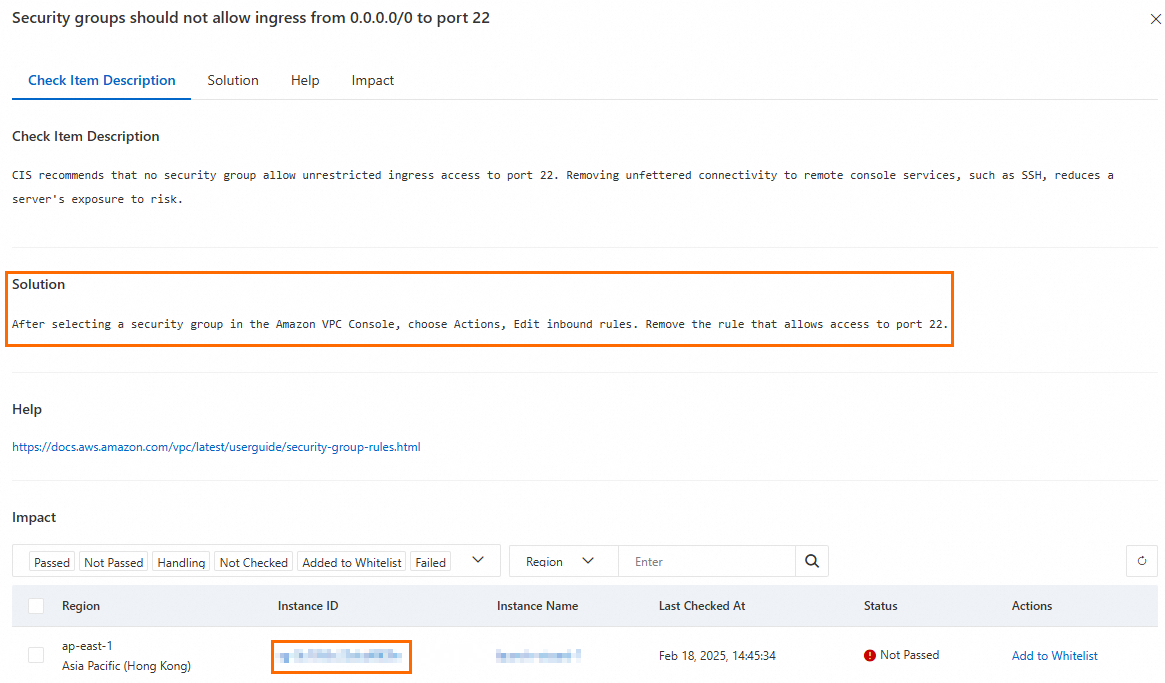
In the Actions column of a risk item, click Details to open the check item details panel. The panel contains four sections:
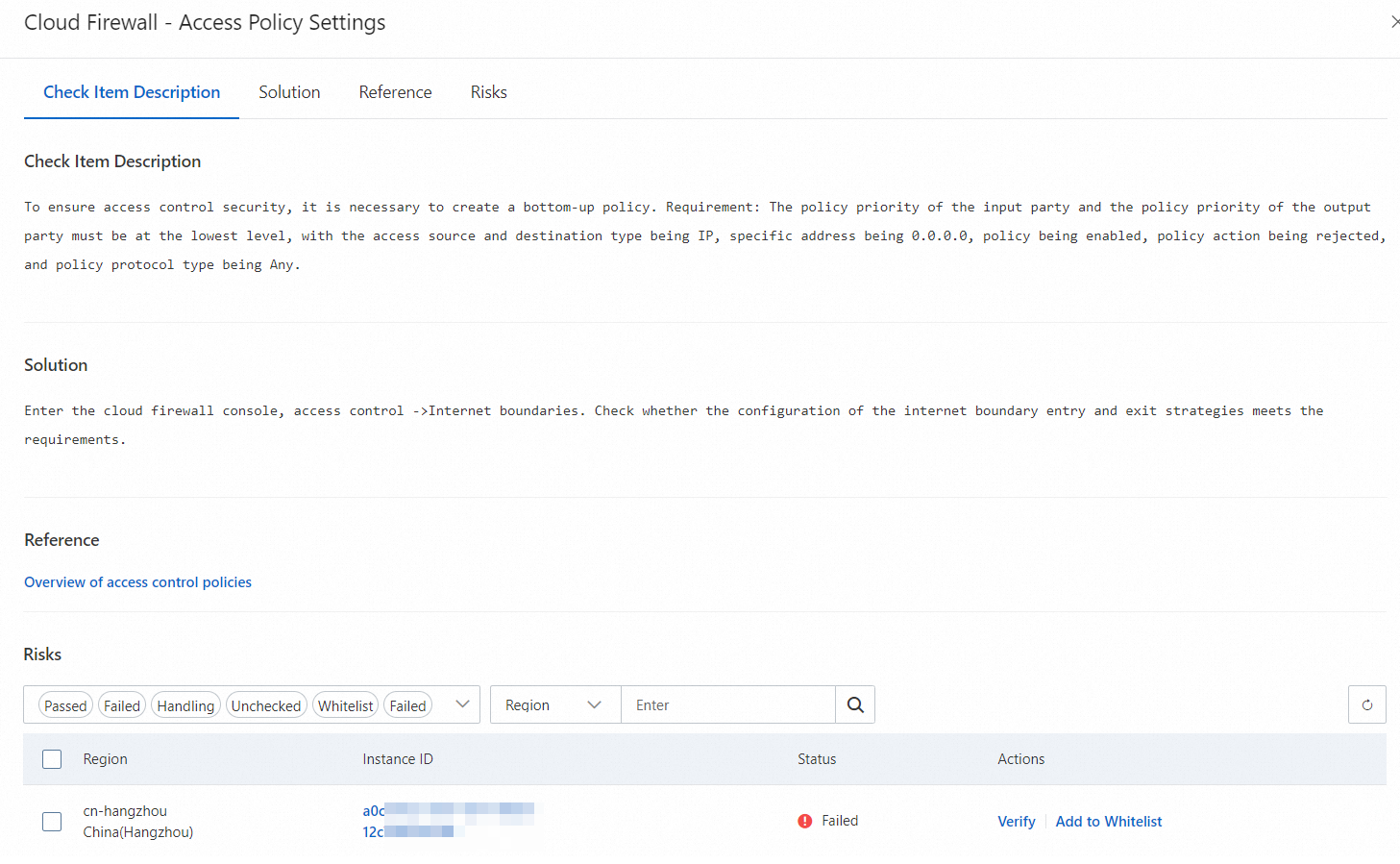
Check Item Description — what the check item evaluates and why it matters
Solution — step-by-step remediation guidance
Help — additional reference information
Impact — the cloud service instances affected by this risk
Fix risky configurations
In the Impact area of the check item details panel, you can see all instances with configuration risks. For each instance, choose to fix the risk or add it to the whitelist.
Fix with one-click fix
Security Center supports one-click fixes for over 100 check items. To check whether a check item supports one-click fixing, look for a Fix button in the Actions column of an instance with a Not Passed status. If no Fix button appears, the check item does not support one-click fixing — follow the manual remediation steps in the Solution section instead.
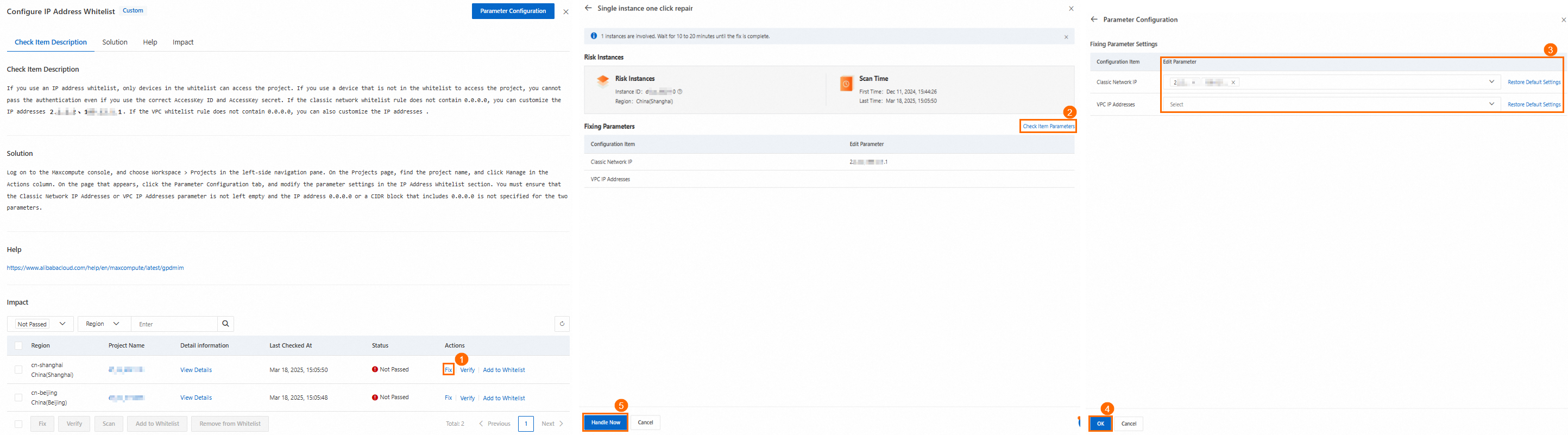
To fix an instance:
In the Actions column of the target instance, click Fix.
In the fix panel, review the risky instance information, scan time, and fix parameters.
If you need to adjust parameters before fixing, click Check Item Parameters, set Edit Parameter in the Parameter Configuration panel, and click OK.
Click Fix Now.
If your account lacks authorization to modify another account's configurations, click Authorize in the dialog that appears.
If there is no notice about rollback restrictions, you can click Rollback later to restore the previous configuration.
If prompted after the fix, restart the instance.
To fix multiple instances at once, select the risk items for multiple instances and click Fix at the bottom of the risk list.
Fix in the cloud service console
Click the at-risk instance ID, account ID, or policy name to navigate to the console of the affected cloud service and apply fixes manually.
Whitelist risks
After adding a risk item to the whitelist, Cloud Security Posture Management (CSPM) stops reporting that risk and excludes it from the total risk count. Only whitelist items you have confirmed pose no threat to your environment.
Use the whitelist to exempt a risk item when the detected configuration is intentional or acceptable for your environment. If a risk can be fixed, fix it instead of whitelisting it.
To whitelist a risk item, click Add to Whitelist in the Impact area of the check item details panel for the corresponding instance.

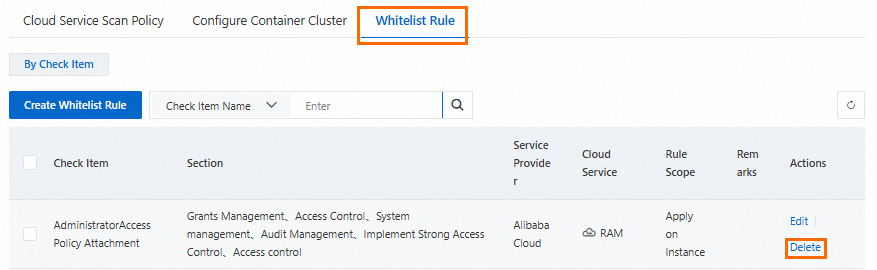
To view all whitelisted check items, go to Policy Management > Whitelist Rule. To remove an item from the whitelist, click Delete.
Verify fixes
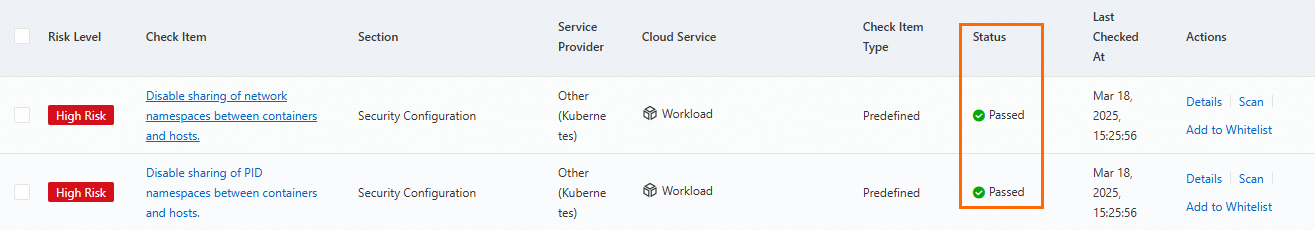
After modifying an instance's configuration, verify the fix:
In the Actions column of the target risk item, click Verify. To verify multiple items at once, select them and click Verify at the bottom of the list.
Once verification passes, the instance status changes to Passed. When all instances under a risk item pass verification, the risk item status also changes to Passed.
Review fix history
For risk items fixed with one-click fix, click Fixing Task Management in the upper-right corner of the CSPM page to view your fix history.
The Fixing Task Management panel shows the fix task ID, check item, and status. From here, you can Roll Back or Verify any fix.
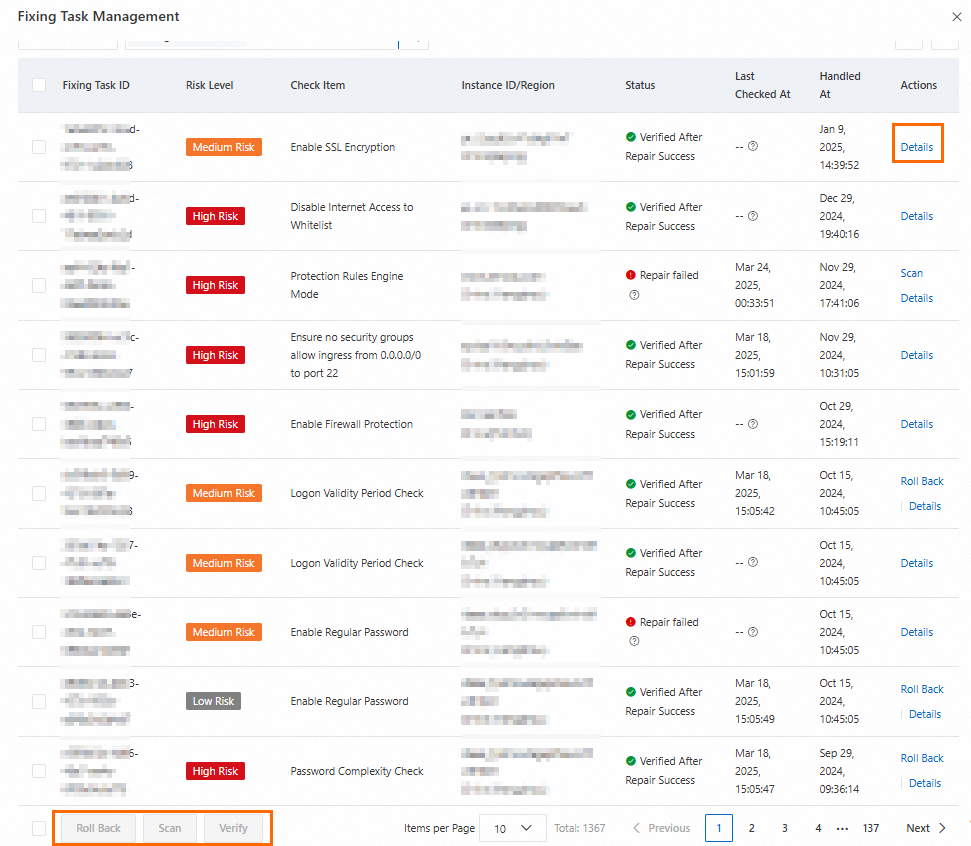
Click Details to view the Check Item Description, Solution, Help, and Fixing Timeline for a specific fix task.