Cloud Security Posture Management (CSPM) in Security Center automatically scans your cloud service configurations to identify and help you remediate potential configuration risks before they lead to security vulnerabilities or data breaches.
This topic covers:
Customizing check items (custom and predefined)
Setting up automatic detection policies and whitelist rules
Running scans and remediating failures
Prerequisites
Before you begin, make sure you have:
A paid edition of CSPM activated. For details, see Activate a paid edition of CSPM.
Configure check items
Security Center includes predefined check items for common configuration risks. Before running a scan, customize these items to align with your security baselines and reduce noise in the results.
Custom check items
Custom check items let you define detection logic based on your internal security standards or risk-specific scenarios.
Supported service providers: Alibaba Cloud, Tencent Cloud, and AWS
Detection scenarios: Compliance Risk, AISPM, and Security Risk. For details, see check rules.
How it works
The following diagram shows the workflow for configuring and using custom check items.

Create and publish a custom check item
Go to the creation page. Log in to Security Center console - Risk Governance - CSPMSecurity Center console - Risk Governance - CSPM. In the top-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland. On the Cloud Service Configuration Risk tab, click Create Custom Check Item.
Configure basic information. On the Basic Information Settings tab, configure the following parameters and click Next.
Parameter Description Check Item Category Settings Assign the check item to one or more categories for easier filtering in reports. Click Add to assign multiple categories. Use case The top-level domain. Select Compliance Risk, AISPM, or Security Risk. Standard/Regulation/Chapter Select a predefined option or enter a custom value from the drop-down list. Check Item Description Describe the check item: the service provider, the cloud service it targets, and a brief explanation of the rule. Solution Provide the manual remediation steps to follow if the check detects a risk. Help Enter a URL for a related help document, or enter Noneif unavailable.Risk Level Set the risk level: High, Medium, or Low. For how risk levels are determined, see Assess risk levels. Define check item rules. On the Check Item Rule Settings tab, configure the following and click Next.
Check Item Target: Select the type of cloud service to check under the specified service provider, such as
ECS-InstanceorOSS-Bucket.Associated Asset Settings (Optional): If the check logic involves related assets, click Add Associated Asset to link an asset type (such as a VPC) to the Check Item Target. > Note: If the Associable Attribute list is empty, the selected Check Item Target does not support asset association. Available options depend on what the console displays.
Configure the following fields when adding an associated asset:
Field Description Associable Attribute The property of the Check Item Target used to link to another asset Associated Asset The asset type to link Associated Asset Property The property of the associated asset that maps to the Associable Attribute Check Item Settings: Define the detection logic using conditions.
Conditions follow AND/OR logic:
Scope Rule Within a group Connect conditions with ANDorOR. Each group supports up to 10 conditions.Between groups Connect groups with ANDorOR. Each check item supports up to 5 groups.Example:With three groups and the relationship "
group1ANDgroup2ORgroup3" — group1 uses AND internally, group2 uses OR, and group3 uses AND: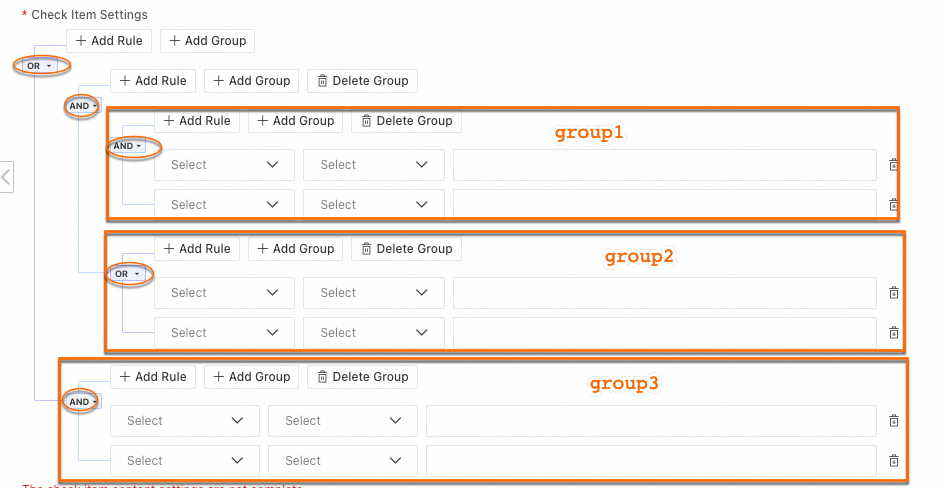
Supported operators:
Operator Description In / NotIn Checks whether a value exists in a specified set Equals / NotEquals Checks whether two values are equal Note: Click the
 icon next to a parameter to view its data type, examples, and description.
icon next to a parameter to view its data type, examples, and description.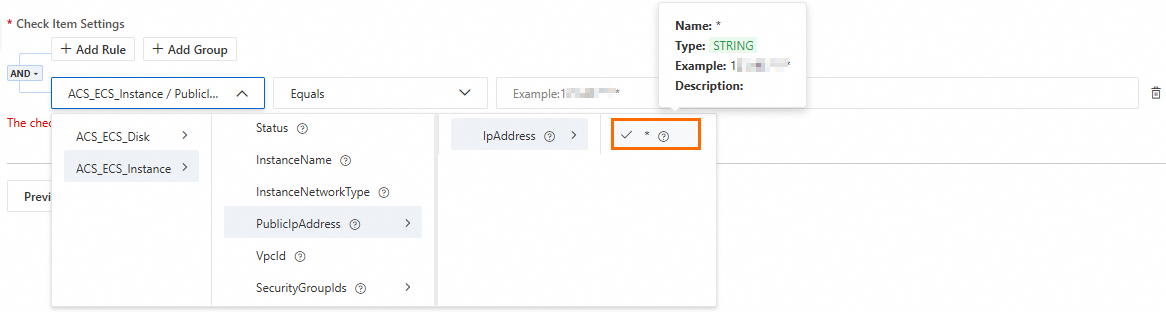
Click Add Condition to expand the configuration area.
Click Add Condition or Add Group to build the rule.
Test the rule.
Click Test on the Check Item Rule Settings tab.
In the Test area, select a matching instance from your account (such as an OSS bucket, ECS instance, or Log Service project), then click Test.
If The check item passed the check. appears, the configuration can parse the data correctly. If the result is unexpected, review your conditions and test again.
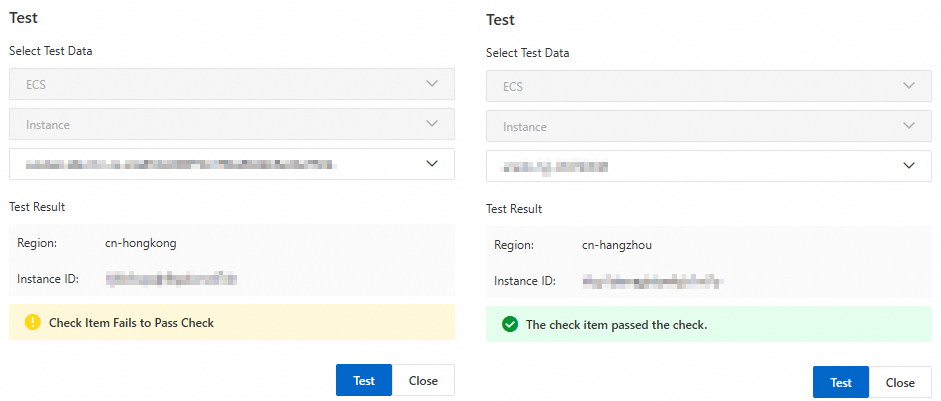
After the result is as expected, click Save.
You can edit, publish, or delete a check item that is saved but not yet published.
Publish the check item. Click Publish on the Check Item Rule Settings tab. Alternatively, go to the custom check item list and click Publish in the Actions column.
Important- Only published check items appear in the check item list and are available for scans. - Published check items cannot be modified. To edit a published item, deactivate it first.
Manage custom check items
In the Custom Check Item Management section in the upper-right corner of the CSPM Risk page, you can view, edit, publish, unpublish, or delete custom check items.
| Action | Behavior |
|---|---|
| Edit | Click the check item name to open its edit page. To modify a published check item, first click Deactivate to make it editable. |
| Unpublish | Permanently deletes the item's associated rules and all historical scan results. This action is irreversible. |
| Delete | Permanently removes the check item along with its historical check data and alert information. |
Predefined check items
For predefined check items that support customization — such as checks for OSS bucket hotlink protection, idle users, or password expiration — you can modify their parameters to match your security baselines.
Requirement: A paid edition of CSPM. See Activate a paid edition of CSPM.
Go to Security Center console - Risk Governance - CSPMSecurity Center console - Risk Governance - CSPM. In the top-left corner, select the region where your assets are located.
On the Cloud Service Configuration Risk tab, find a check item where the Support Custom Parameters column shows Yes, then click its name.
In the details panel, click Parameter Configuration.
If this button does not appear, the check item does not support parameter modification.
In the Parameter Configuration panel, click Add Modifiable Parameter in the Modifiable Parameter column and select the parameter to modify from the drop-down list.
Enter the new value in the Edit Parameter column and click OK.
The modified parameter takes effect during the next scan.
Configure check policies
After configuring check items, set up detection policies and whitelist rules to control the scope, schedule, and exceptions for your scans.
Automatic detection policy
On the Risk Governance > Cloud Service Configuration Risk page, click Policy Management in the upper-right corner, then go to the Cloud Service Scan Policy tab.
Turn on the Automatic CSPM Check switch and configure the following settings:
Setting Description Check Cycle How frequently the scan runs Check At The specific time for the scan to start Check Item Selection The predefined or published custom check items to include After selecting check items, the Estimated Quota Consumption for a single scan appears above the list.
This estimate is for reference only. The actual number of scanned instances may vary.
Security Center runs configuration risk scans on your defined schedule automatically.
Whitelist rules
Use whitelist rules to exclude specific check items for designated cloud service instances, preventing unnecessary risk alerts. Whitelist rules apply to both scheduled and on-demand scans.
Create a whitelist rule
On the Risk Governance > Cloud Service Configuration Risk page, click Policy Management in the upper-right corner.
On the Whitelist Rule > By Check Item tab, click Create Whitelist Rule.
In the panel, configure the following and click OK: Policy Effective Scope options:
ImportantExempting all instances is a high-risk operation — new security risks on future instances can go undetected. Use Specific Instances for precise whitelisting, and audit your whitelist rules periodically to confirm they are still necessary.
Parameter Description Check Item The check items to exclude from scans. See check rules. Policy Effective Scope The scope of the exemption. Option Behavior All Instances Exempts all existing and future instances of this cloud service from the check. Related risks are not displayed in the risk list. Specific Instances Applies the exemption only to the selected instances. New instances are still scanned.
Manage whitelist rules
Edit or delete rules: Whitelist rules you create appear in the By Check Item list. Click Edit to modify the scope, or Delete to remove the exemption.
Automatic synchronization: When you manually mark a failed check item as handled or whitelisted while handling risks, the system automatically adds the corresponding rule to this list. For details, see Handle cloud services that fail check items.
Run configuration risk scans
Security Center supports two scan modes:
| Mode | Description |
|---|---|
| Scheduled automatic scans | Runs on the schedule defined in your automatic detection policy |
| On-demand scans | Triggered manually at any time |
Run an on-demand scan:
On the Cloud Service Configuration Risk tab, click Scan Now in the Actions area.
Select a scan mode:
Mode What it scans Full Scan All supported cloud services and check items, including predefined and custom Scan By Policy Only the check items selected in Policy Management
After the scan completes, view all failed check items in the Cloud Service Configuration Risk list and follow each item's Solution to remediate them.
Remediate failed check items
After a scan, go to Risk Governance > CSPM Risk > Cloud Service Configuration Risk to view all failed check items and follow the provided Solution to remediate each risk.
For step-by-step guidance, see View and handle failed check items.
FAQ
What should I do if I find a logic error in a published custom check item?
Deactivate the check item first: in the upper-right corner of the CSPM Risk page, click Custom Check Item Management, find the item, and select Deactivate.
Unpublishing a check item permanently deletes all of its historical scan results. This action is irreversible.
After modifying and testing the rule, click Publish to make it active again.
How can I find the custom check items I created?
On the Cloud Service Configuration Risk tab of the Risk Governance > CSPM Risk page, your custom check items are grouped under the categories you assigned during creation.
