Onboard your Azure assets to Security Center to unify asset inventory across clouds, scan for configuration risks with Cloud Security Posture Management (CSPM), and automate security responses. Security Center uses Azure application credentials to call Azure public APIs, read your subscription data, and sync asset and configuration information into a unified multicloud security view.
How it works
Register an application in Azure and create a service principal as the access credential.
Security Center uses that credential to call Azure public APIs, gain read access to your specified subscription, and sync asset and configuration data within that subscription.
Step 1: Create an application credential in Azure
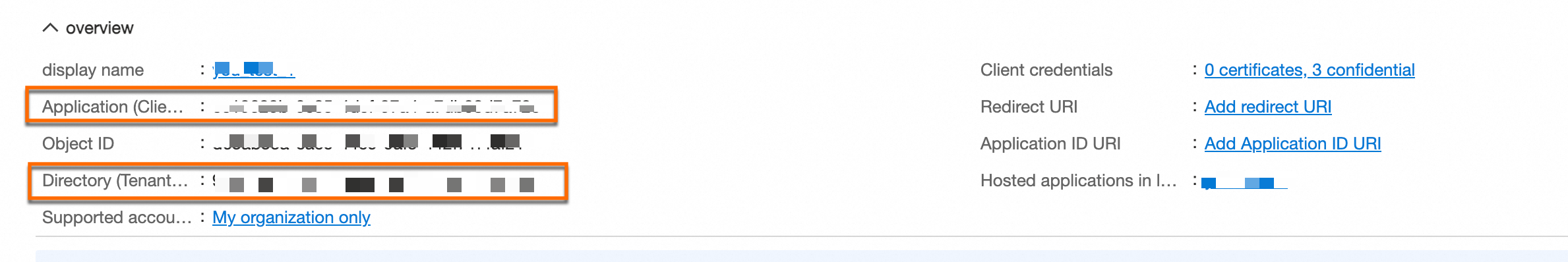
This step registers an application and its service principal in the Azure portal and generates a client secret for API authentication. At the end, you will have three values you need later: Application (client) ID, Directory (tenant) ID, and the client secret Value.
Create an application
Log in to the Azure consoleAzure consoleAzure console.
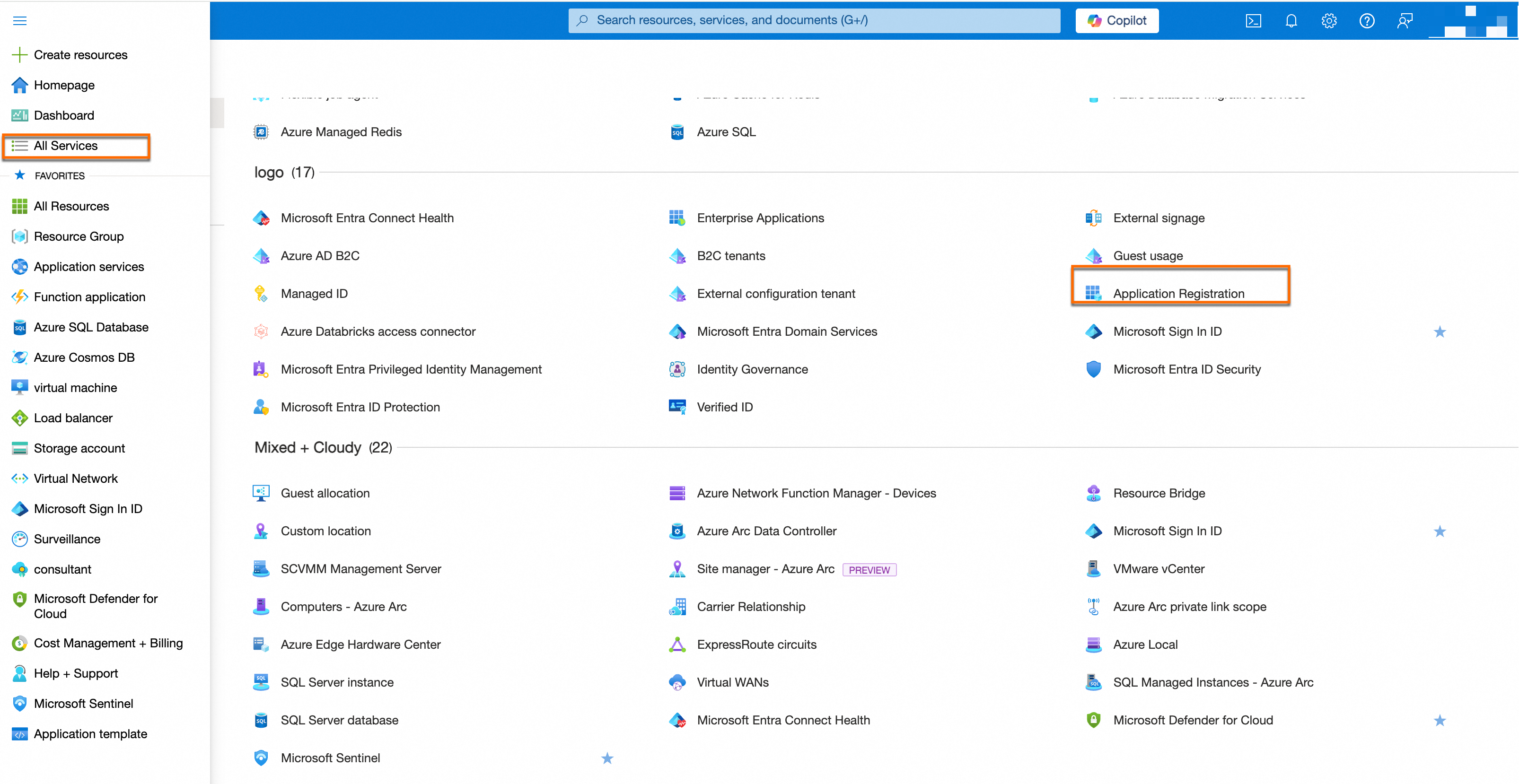
In the left navigation pane, select All Services. Under the Logo section, click Application Registration, or search for Application Registration in the top search bar and open it.
On the Application Registration page, click New Registration.
Complete the registration form, then click Register:
Name: Enter a recognizable name such as
aliyun-sasc-connector. This name appears as the member name in the role assignment step.Supported account types: Select the account scope based on your permission requirements.
After the application is created, the overview page shows your application details. Copy and store the Application (Client) ID and Directory (Tenant) ID — you will need both in a later step.
Generate a client secret
On the application details page, click Manage > AccessKey Leak Detection in the left navigation pane.
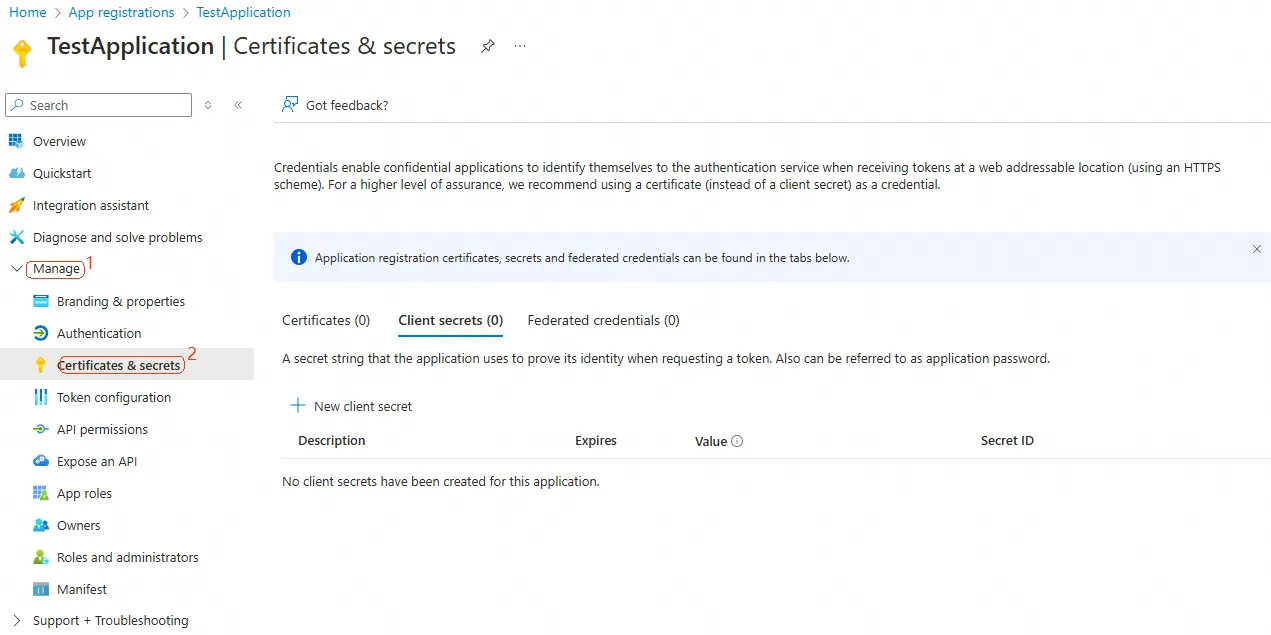
On the Client secrets tab, click + New client secret and configure the following:
Description: Describe the purpose of this secret.
Expires: Set the expiration period. A 180-day expiration is recommended.
ImportantCreate a credential rotation plan and update the secret before it expires to prevent service interruption.
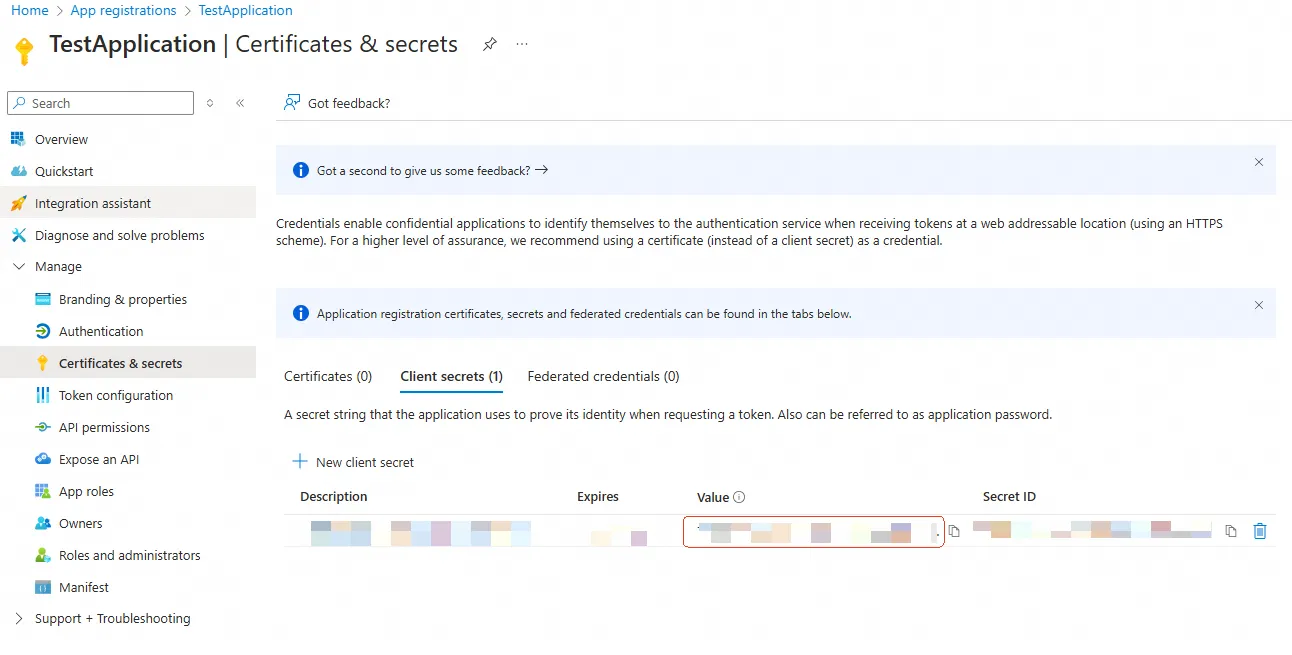
Click Add. The client secret Value appears.
WarningThe client secret Value is visible only once. Copy and store it immediately — you cannot retrieve it after leaving this page.
Step 2: Grant subscription access to the application
Assign the appropriate Azure roles to the application so Security Center can read your asset information. The roles required depend on which Security Center features you plan to use.
| Feature | Required roles | Notes |
|---|---|---|
| Host | Reader | — |
| CSPM | Reader | — |
| Agentic SOC | Reader + custom role with Microsoft.Network permissions | The custom role is required to enable automated threat response through SOAR. For creation steps, see Azure advanced configuration (Agentic SOC). For more information on automated response, see External components (OpenAPI). |
| Agentless Detection | Reader + Disk Snapshot Contributor | — |
Azure allows only one role per assignment. Assign each role separately.
Go to the role assignments page
Log in to the Azure consoleAzure consoleAzure console.
In the left navigation pane, select All Services. Under the System Settings section, click Subscription, or search for Subscription in the top search bar.
Click your target subscription to open its details page, then click Access control.
If you do not have a subscription yet, create one and select products based on your business needs.
On the Access control page, click Add > Add role assignment.
Assign a role
On the role assignment page, select the appropriate role based on the table above, then click Next.
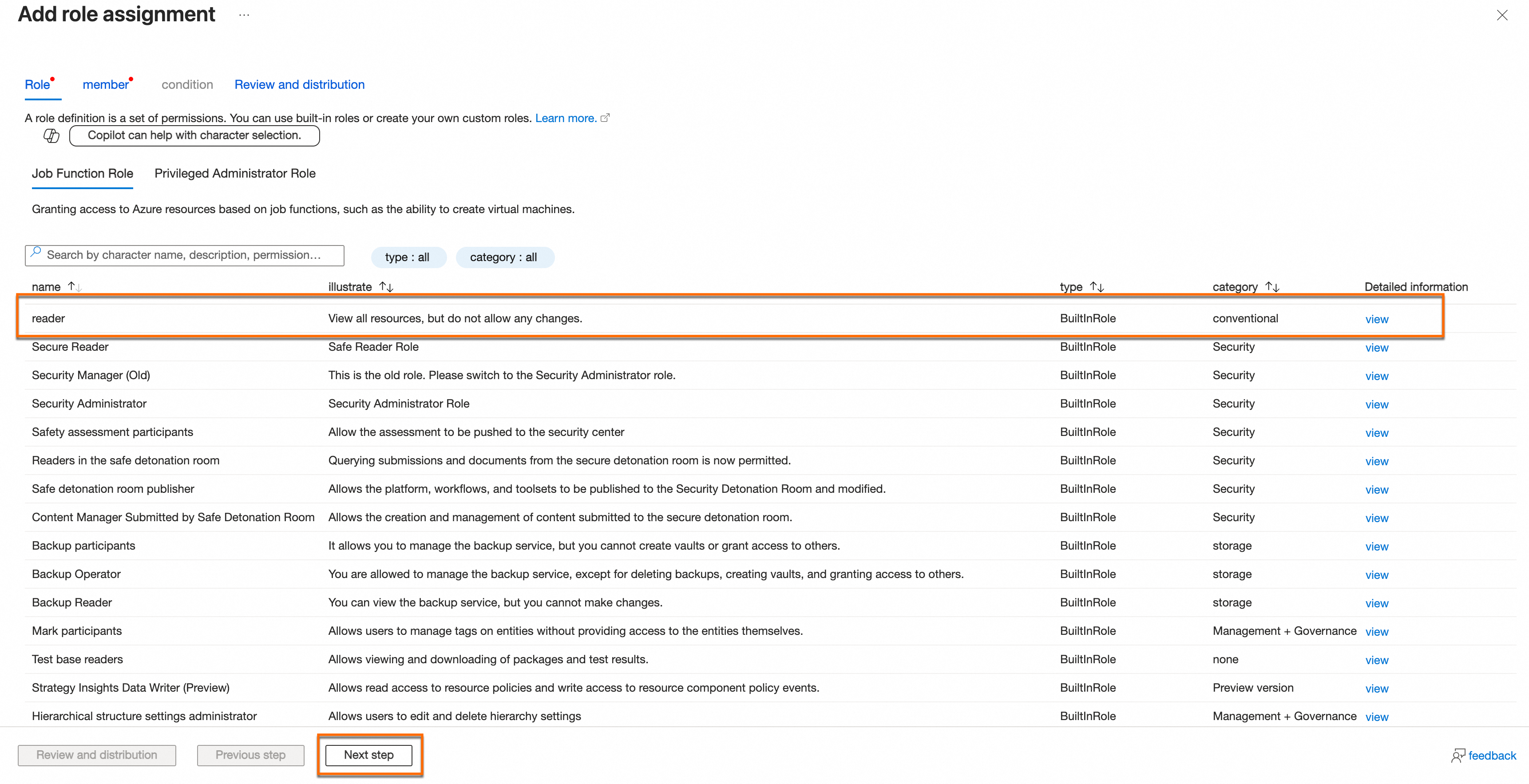
Add the application as a member
On the Members management page, click Add access key and select the application you created in Step 1. Search by application name to locate it quickly.
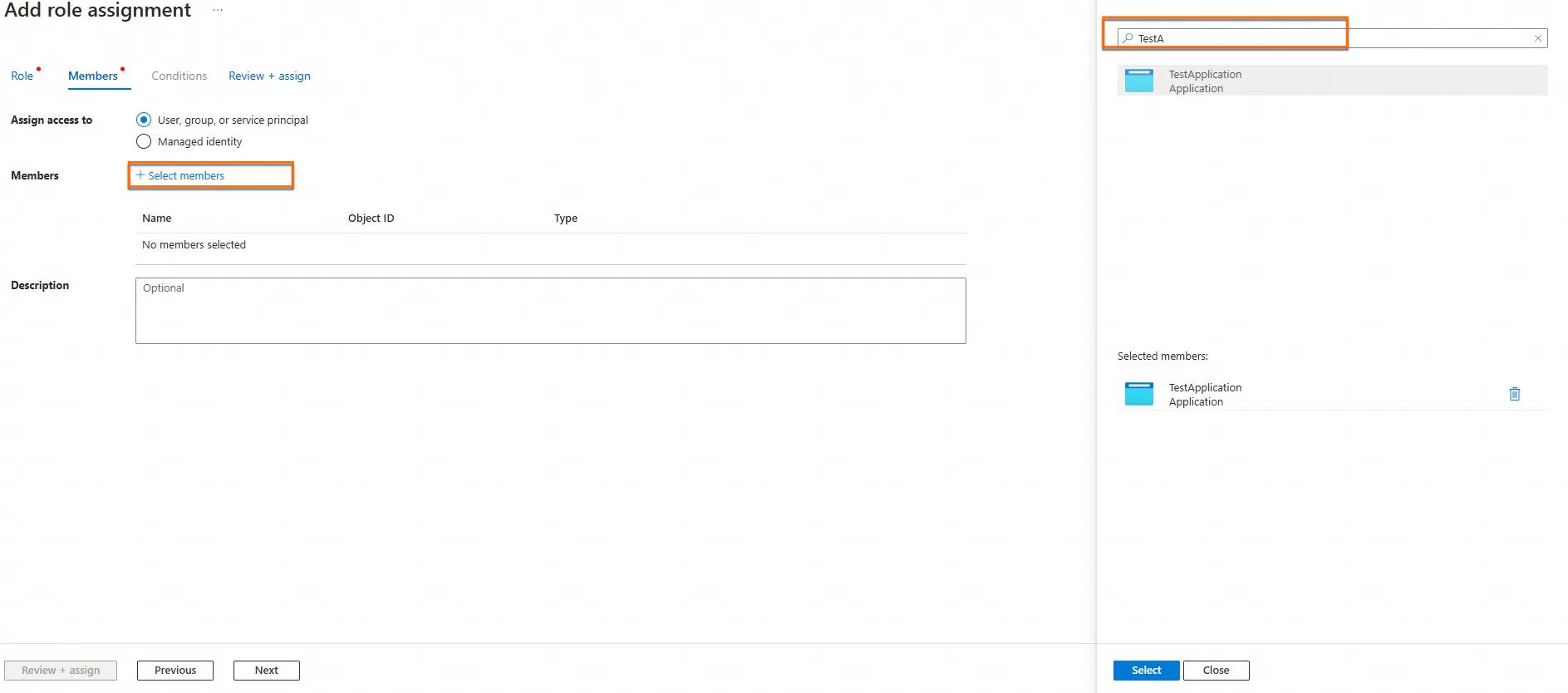
Click Review + assign to complete the authorization.
Authorization may take some time. Please wait patiently.
Repeat this process for each role required by your selected features.
Step 3: Complete onboarding in Security Center
Go to the authorization page
Recommended path:
Log in to the Security Center console.Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region where your protected assets are located: Chinese Mainland or Outside Chinese Mainland.
On the Multi-cloud Configuration Management > Multi-cloud Assets tab, click Grant Permission, then select Azure.
Alternative entry points:
On any of the following pages, find the Onboard or Authorize button in the Multi-cloud Service Access or Add Multi-cloud Asset sections below the ![]() icon:
icon:
Assets > Host
Risk Governance > CSPM > Cloud Service Configuration Risk
Protection Configuration > Host Protection > Agentless Detection
Select features and enter credentials
On the Add Assets Outside Cloud panel, select the features to enable, then click Next:
Host: Automatically discovers and syncs Azure host assets.
CSPM: Scans Azure cloud product configurations and manages configuration risks.
Agentic SOC: Works with SOAR and Script to automate security incident response. For more information, see External components (OpenAPI).
Host Protection > Agentless Detection: Uses snapshot scanning to detect vulnerabilities, baseline deviations, and malicious files on Azure virtual machines without installing a client.
On the Submit AccessKey Pair page, enter the credential information from Step 1:
Enter an AppID: The Application (client) ID.
Enter a password: The client secret Value.
tenant: The Directory (tenant) ID.
Domain (Select Chinese Edition for China and International Edition for others): CenturyLink users select Chinese Edition.
Configure the sync policy
On the Policy Configuration page, configure the following settings:
Select region: Choose the Azure region where your assets reside.
Asset data is stored in the data center corresponding to the region selected in the upper-left corner of the Security Center console: Chinese Mainland uses the Chinese mainland data center, and Outside Chinese Mainland uses the Singapore data center.
Region Management: Enabling this option automatically syncs assets in new Azure regions added to the account. This option is recommended for most deployments.
Host Asset Synchronization Frequency: Set how often Azure host assets sync. Set to Off if you do not need automatic syncing.
This setting applies only if you selected Host during onboarding.
Cloud Service Synchronization Frequency: Set how often Azure cloud product configurations sync. Set to Off if you do not need automatic syncing.
This setting applies only if you selected Cloud Security Posture Management during onboarding.
AK Service Status Check: Set how often Security Center validates your Azure credentials. Set to Off to disable.
After completing the configuration, click Synchronize Assets. Security Center starts syncing data from your Azure account.
Azure advanced configuration (Agentic SOC)
For reference, see the Azure documentation: Azure permissions for networking and Create custom roles.
Create a custom role with Microsoft.Network permissions to enable automated threat response for Agentic SOC.
Log in to the Azure consoleAzure consoleAzure console.
In the left navigation pane, select All services. Under the System Settings section, click Subscriptions.
Alternatively, search for Subscriptions in the top search bar and open it directly.
Click your target subscription to open its details page, then click Access control (IAM).
On the Access control page, click Add > Add custom role.
Enter the basic information:
Custom role name: Enter a recognizable name such as
aliyun-agentic-soc-role.Baseline check: Select Start from scratch.
On the Permissions tab, click Add permissions. Search for
Microsoft.Networkand click the permission name.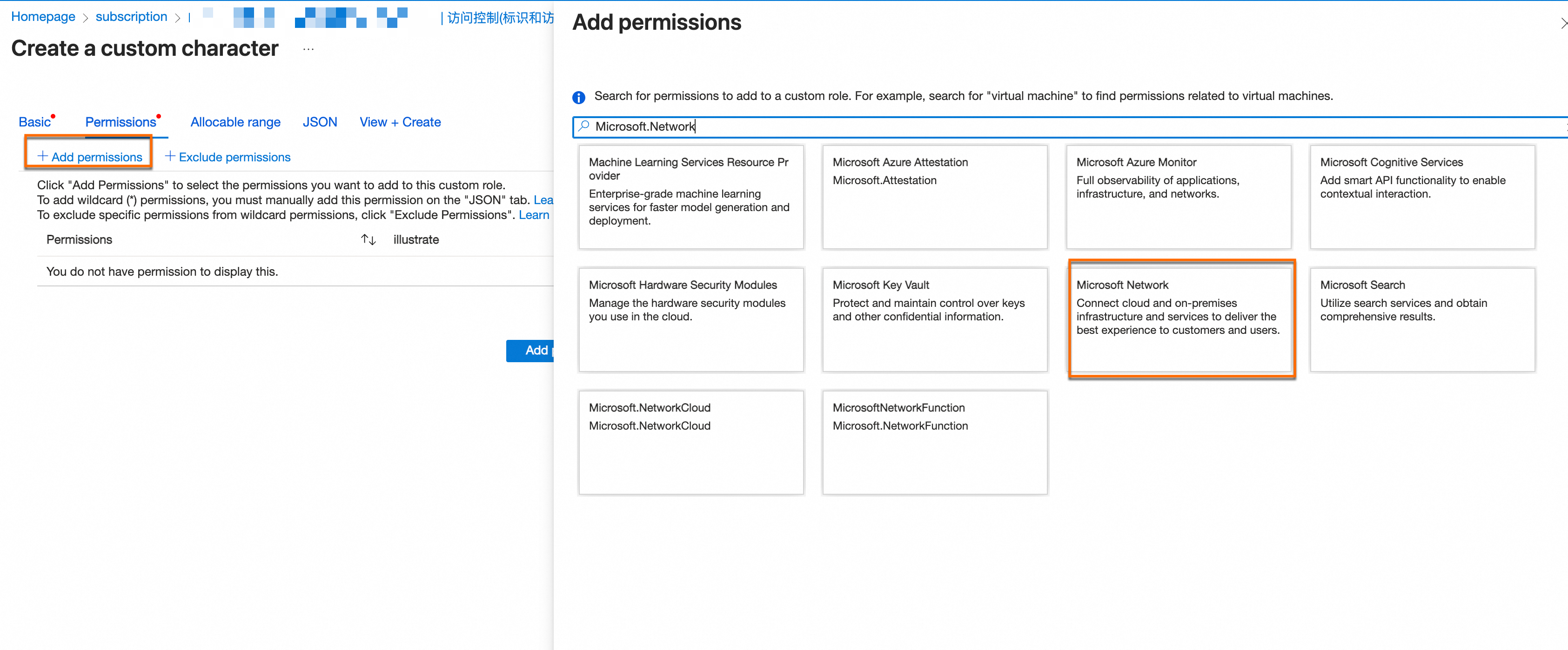
On the permissions list, select all permissions under Actions, then click Add.
Click Review + create. Confirm the details, then click Confirm.
After creating the custom role, return to Step 2 to assign both the Reader role and this custom role to your application.
Manage onboarded assets
Host
Go to Assets > Host. In the Add Multi-cloud Asset section, click the ![]() icon to view your onboarded Azure hosts.
icon to view your onboarded Azure hosts.
To apply protection to your Azure hosts:
Install the client: Install the Security Center client on your Azure hosts. When running the installation command, select Service Provider as the service provider. For detailed steps, see Install the client.
Upgrade for full protection: The default Free Edition provides basic security detection only. To get full protection capabilities — including antivirus, vulnerability remediation, and intrusion prevention — bind an Anti-virus Edition or higher license to your Azure hosts. For details, see Manage host and container security licenses.
For more information, see Manage servers.
CSPM
Go to Assets > Cloud Product. In the left navigation under All Alibaba Cloud Services, click Azure to view your integrated Azure assets.
With CSPM enabled, you can:
Run configuration risk checks: Check for configuration risks in your Azure products. For details, see Set up and run cloud platform configuration risk check policies.
Address risks: Review and fix failed risk checks to improve compliance and security. For details, see View and address failed cloud platform configuration risk checks.
For more information, see View cloud product information.
Agentic SOC
In Agentic SOC > SOAR, select the Azure component from External components (OpenAPI) when creating a custom playbook to automate responses to Azure asset security events.
Agentless Detection
Go to Protection Configuration > Host Protection > Agentless Detection. On the Server Check or Custom Image Check tab, in the Add Multi-cloud Asset area, click the ![]() icon to view detected threats.
icon to view detected threats.
Run detection jobs: Perform multidimensional security checks on your Azure servers for vulnerabilities, malware, baseline deviations, sensitive files, and other security risks.
Analyze and address risks:
Vulnerability risks: Support Add to Whitelist. > Warning: Agentless detection does not support vulnerability remediation.
Baseline check risks: Support Add to Whitelist.
Malware and sensitive file risks: Support Add to Whitelist, Manually Handled, Mark as False Positive, and Ignore.
Cost and risk considerations
Cost: The default Free Edition provides basic security detection only. Full protection capabilities — including antivirus, vulnerability remediation, and intrusion prevention — require binding an Anti-virus Edition or higher license to your onboarded Azure hosts.
Credential security: The client secret links Azure and Security Center. If leaked, it could allow unauthorized access to your asset data. Store it securely and rotate it on a regular schedule.
Credential expiration: If the client secret expires, asset synchronization and security checks stop. Implement a rotation plan and update the secret before it expires.
FAQ
Why can't I see some onboarded Azure resources in Security Center?
Check two things: first, verify in the onboarding configuration that you selected the Azure region where the resource resides. Second, if you recently completed onboarding or changed the configuration, wait for the initial sync to finish — asset synchronization can take a few minutes.
What should I do if credential validation fails after entering the credentials?
If the validation fails due to a permission issue, your client secret has likely expired. Recreate the client secret following the Generate a client secret step in Step 1, then update the credential in Security Center's multicloud configuration.
If the validation fails due to a region issue, the currently selected region may be unavailable. Switch to another available region or the corresponding Domain, then resubmit.