To help you quickly enable pay-as-you-go services, Security Center lets you activate features and apply recommended protection policies with a single click on the console. These features include host and container security, Cloud Threat Detection and Response (CTDR), Cloud Security Posture Management (CSPM), agentless detection, serverless asset protection, vulnerability fix, application protection, and the SDK for malicious file detection. This topic explains the default one-click onboarding policies and billing details for these services.
If you select Enable the one-click policy to automatically receive your bill the next day. and click Activate and Authorize, Security Center enables several policies by default. All servers are assigned the Host Protection or Hosts and Container Protection level, all serverless assets are authorized, the recommended log ingestion policy for CTDR is applied, periodic scans for CSPM and agentless detection are scheduled, and the default access and detection policies for application protection and the SDK for malicious file detection are activated.
Security Center automatically enables protection, assigns authorizations, ingests logs, and runs scans and detections based on these one-click onboarding policies.
Security Center generates daily bills according to thebilling rules of each enabled feature. To avoid unexpected charges, carefully read and understand the one-click onboarding policies before you enable them.
One-click onboarding policies
Host and container security
After activation and authorization, the host and container security feature automatically assigns a protection level to all servers in your Alibaba Cloud account: Host Protection or Hosts and Container Protection.
Server assets running container environments—including Alibaba Cloud ACK cluster nodes, Intelligent Computing LINGJUN, and servers from self-managed Kubernetes clusters—are automatically bound to Host and Container Protection. All other assets are automatically bound to Host Protection.
You can later go to the Overview page on the Security Center console and use the Quota Management feature to change the protection level assigned to your servers. For more information, see Manage security authorizations for hosts and containers.
The default protection level for new hosts is Unprotected. Use the Quota Management feature to configure an automatic protection level for new hosts.
Serverless security
After completing the activation and authorization, the serverless asset protection feature automatically authorizes all serverless assets in your Alibaba Cloud account.
For Elastic Container Instance (ECI) assets created from managed or dedicated Container Service for Kubernetes (ACK) clusters, ACK Serverless clusters, or ACS clusters, you must install and start the Security Center agent to use the serverless asset protection feature. For more information, see 1. Install and start the Security Center agent for the ECI pods that you want to protect.
You can later go to the page on the Security Center console and use the authorization management options to manage the binding status of your assets. For more information, see 3.2. Bind or unbind authorized assets.
Application protection
After completing activation and authorization, the application protection feature automatically enables full protection for Java processes only and adds them by using the slow connection method.
You can later go to the tab to adjust which servers and processes are onboarded. For more information about automatic full onboarding, see Automatic full onboarding (Java processes only).
Malicious file detection SDK
After activating and authorizing the malicious file detection feature, Security Center automatically creates and enables a default detection policy named Auto_Create_Config. To modify this policy, go to the tab, and click Policy Configuration in the Policy Management area to view and modify the policy. The policy details are as follows:
Detection scope: All OSS buckets in your Alibaba Cloud account.
Detection targets: All new or updated files after the feature is enabled.
Execution cycle: Once per day.
Detection method: By default, files are not decompressed or decrypted.
A detection task based on this policy runs on the same day you activate the service.
Cloud Security Posture Management (CSPM)
For users who have never enabled a periodic CSPM scan policy:
Scan frequency: Once a day. The system randomly generates a specific scan time.
Scan scope:
The scan checks for common high-risk misconfigurations based on security best practices, such as improper security settings, exposed high-risk ports, internet-exposed allowlists, public data read/write permissions, and risks related to identity and privilege management. These checks help improve the security of your cloud products and platform.
On the Security Center console, you can go to the page and view the default check items in the Policy Management panel. The selected check items define the scan scope of the recommended policy.
For users who have previously enabled a periodic CSPM scan policy:
Scan frequency: Same as your existing configuration.
Scan scope: The union of the check items in your existing configuration and the recommended scan scope described above.
Vulnerability fix
After completing the activation and authorization, the pay-as-you-go feature for vulnerability fix becomes active.
Security Center configures an automatic vulnerability fix policy to run daily from 00:00 to 06:00. This policy automatically fixes high-risk vulnerabilities on all affected assets, including newly added hosts. Security Center creates a snapshot before each fix and retains it for one day. For more information, see View and manage vulnerabilities.
Agentless detection
Scan frequency: Once every 5 days.
Scan scope: All machines. The Default Scan for New Assets option is enabled by default.
A detection task based on this policy runs on the same day you activate the service.
Cloud Threat Detection and Response (CTDR)
After you complete the activation and authorization, the CTDR feature automatically ingests logs from the Alibaba Cloud products and data sources listed in the following table.
If your Security Center edition is Free Edition or you have only purchased value-added services, the system does not ingest ActionTrail event logs.
Ordinal number | Alibaba Cloud product | Data source name | Standardization rule name | Standardization method | Standardization classification/structure | Supported security capabilities |
1 | Security Center | DNS request logs | Host DNS request log standardization rule | Scan query | Host logs - Process DNS request logs |
|
2 | Baseline logs | Baseline log standardization rule | Scan query | Security logs - Host baseline logs |
| |
3 | Login flow logs | Login flow log standardization rule | Scan query | Login logs - Host login logs |
| |
4 | Network connectivity logs | Network connectivity log standardization rule | Scan query | Host logs - Process network outbound connection logs |
| |
5 | Process startup logs | Process startup log standardization rule | Scan query | Host logs - Process startup logs |
| |
6 | Security alert logs | Security alert log standardization rule | Real-time consumption | Security logs - Other alert logs | Predefined playbooks | |
7 | Vulnerability logs | Vulnerability log standardization rule | Scan query | Security logs - Vulnerability logs |
| |
8 | Web Application Firewall | WAF alert logs | WAF alert log standardization rule | Real-time consumption | Security logs - Web Application Firewall alert logs |
|
9 | WAF full, block, and block-and-observe logs | WAF full, block, and block-and-observe log standardization rule | Real-time consumption | Network logs - HTTP logs |
| |
10 | Cloud Firewall | Cloud Firewall alert logs | Cloud Firewall alert log standardization rule | Real-time consumption | Security logs - Firewall alert logs |
|
11 | ActionTrail | ActionTrail event logs | ActionTrail event log standardization rule | Real-time consumption | Audit logs - Cloud platform operation audit logs |
|
Anti-ransomware
This feature periodically backs up important file paths on your servers. If a ransomware attack occurs, you can use these backups to restore your servers. To adjust the protection scope, go to the ransomware protection policy management page.
Log Management
Security Center delivers logs to a Logstore. By default, it delivers logs to the China (Shanghai) region for accounts in the Chinese mainland and to the Singapore region for accounts outside the Chinese mainland.
Billing
Basic service fee
When you enable any pay-as-you-go feature of Security Center, the system charges a basic service fee. The billing rules are as follows:
After you enable the service, DingTalk Robot, security reports, and Task Hub are supported by default. To use Task Hub, you must first enable or purchase the vulnerability fixing feature.
Billing method: This fee is billed based on the duration for which the pay-as-you-go service is enabled.
ImportantThe minimum billing unit is one hour. If the duration is less than one hour, it is billed as one hour.
Billing cycle: Billed daily.
Price: USD 0.0072/hour.
Host and container security
After enabling the pay-as-you-go feature for host and container security, fees are calculated based on the number of servers assigned to each protection level and the actual protection duration. The duration is measured in seconds and accrues only when the agent is online. Bills are settled daily.
Protection level | Price | Monthly fee (30-day reference) |
Antivirus | USD 0.000000578 per core per second | USD 1.5 per core per month |
Advanced | USD 0.000005497 per server per second | USD 14.25 per server per month |
Host Protection | USD 0.000013599 per server per second | USD 35.25 per server per month |
Hosts and Container Protection | USD 0.000013599 per server per second+USD 0.000000578 per core per second | USD 35.25 per server per month+USD 1.5 per core per month |
Serverless security
After you enable and authorize serverless assets, serverless protection uses pay-as-you-go, tiered pricing based on cumulative monthly usage.
Cumulative monthly usage | Price | Fee calculation formula (U is the daily usage in core-seconds) |
Tier 1: 0 to 200,000,000 core-seconds | USD 0.000003 per core-second | 0.000003 × U (USD) |
Tier 2: 200,000,001 to 1,000,000,000 core-seconds | USD 0.000002 per core-second |
|
Tier 3: 1,000,000,001 to 9,999,999,999,999 core-seconds | USD 0.0000015 per core-second |
|
Application protection
After enabling the pay-as-you-go feature for application protection, the system counts the number of online instances every minute and charges USD 0.0002/instance/minute. Bills are settled daily.
Malicious file detection SDK
Billing for the SDK for malicious file detection is based on the number of files detected, which determines the number of detections. After enabling the pay-as-you-go feature, you are charged USD 0.0002/detection daily.
Cloud Security Posture Management (CSPM)
Quota: CSPM uses Quota as the unit of measurement for its paid features. Performing a billable operation, such as a scan, verification, or successful remediation on an instance, consumes one Quota unit.
For example, if you have 10 cloud services and each service has 15 instances, scanning all instances with 5 check items consumes
10 × 15 × 5 = 750Quota units.Instance: An instance refers to a specific cloud resource, such as an OSS bucket or an ECS security group.
Check item: Check items are categorized as free or paid.
Free check items: The Cloud Service Configuration Risk feature provides a set of free check items for basic risk detection. You can run an unlimited number of scans and verifications. Quota is consumed only upon successful remediation.
ImportantFor users who authorized CSPM (formerly Cloud service configuration check) before July 7, 2023, you retain access to the number of free check items corresponding to your original Security Center edition (80+ for Anti-virus Edition, 90+ for Advanced Edition, and 250+ for Enterprise/Ultimate Edition), both before your current subscription expires and upon renewal.
Paid check items: These require you to purchase a specific edition or activate the CSPM service. The cost is either included in the edition fee or consumes Quota.
Security Center provides more than 80 check items for free. Scans that use only free check items are not billed. For a list of check items in the recommended scan policy, see Recommended periodic scan policy for CSPM.
CSPM supports subscription (prepaid) and pay-as-you-go billing methods. The fees are as follows:
Subscription: Price × Number of authorizations × Purchase duration (calculated based on the Security Center instance's subscription duration).
Authorizations
Price per authorization (USD)
0–100,000
0.0009
100,001–500,000
0.00069
More than 500,000
0.000625.
Pay-as-you-go: Uses a tiered pricing model based on the number of authorizations consumed and is settled daily.
Authorizations
Price
Fee calculation formula (Z is the number of authorizations used per day)
0 to 100,000
USD 0.0009 per authorization
0.0009 × Z (USD)
100,001 to 500,000
USD 0.0007 per authorization
0.0009 × 100,000 + 0.0007 × (Z - 100,000) (USD)
More than 500,000
USD 0.00045 per authorization
0.0009 × 100,000 + 0.0007 × 400,000 + 0.00045 × (Z - 500,000) (USD)
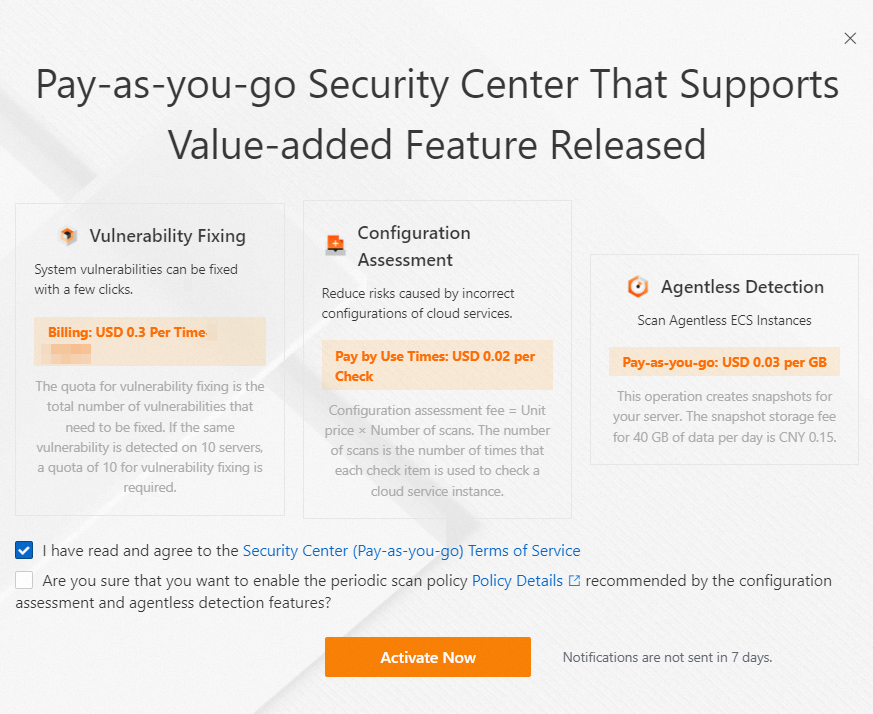
Vulnerability fix
After enabling the pay-as-you-go feature for vulnerability fix, you are charged USD 0.3/remediation daily. For more information, see How vulnerability remediation attempts are counted.
Agentless detection
Agentless detection scan fee
Billing method: Pay-as-you-go.
Billing cycle: Daily.
Unit price: USD 0.03/GB.
Billable usage: Calculated based on the actual data volume of the scanned images, not the total disk capacity.
ECS resource usage fees
ImportantWe recommend that when you configure host detection tasks, you select Retain Only At-risk Image. The system then automatically deletes risk-free images after the scan to reduce storage costs.
Image fees: The detection task creates an image for the server. You are charged for the image based on its usage capacity and duration. These fees are charged by ECS. For more information, see Image billing.
Cloud Threat Detection and Response (CTDR)
CTDR billing is based on the volume of ingested logs and the amount of stored data.
Subscription billing:
Log Ingestion Traffic: Tiered pricing is used. The minimum purchase is 100 GB/day, with a step size of 100 GB/day. The prices are as follows (where X is the traffic ingested per day):
X=100 GB: USD 0.45/GB/day.
200 GB =< X < 9,999,999,999 GB: USD 0.42/GB/day.
Log Storage Capacity: USD 100/1,000 GB/month (Minimum purchase of 1,000 GB, with a step size of 1,000 GB).
Intelligent Usage Analysis:
The minimum purchase is 100 GB/day. The purchase quantity must be consistent with the Log Ingestion Traffic.
Price: USD 9.6/100 GB/day.
NoteThe usage is reset to zero at 00:00 every day. If the limit is exceeded, the system automatically throttles traffic.
Number of Managed Instances:
The minimum purchase is 10 instances/month, with a step size of 10 instances/month.
USD 1.434/instance/month.
NoteEach instance is counted only once. Duplicates are automatically removed.
Pay-as-you-go billing: Fees are based on the cumulative daily log traffic from your products and use a tiered pricing model. The final daily bill is the sum of the fees from each usage tier.
ImportantThe minimum billing unit is 1 GB. If the data volume is less than 1 GB, it is billed as 1 GB.
Log ingestion traffic tier
Price
Fee calculation formula (Y is the traffic ingested per day in GB)
1 to 10 (GB/day)
USD 2.2/GB
2.2 × Y (USD)
11 to 50 (GB/day)
USD 1.6/GB
2.2 × 10 + 1.6 × (Y - 10) (USD)
51 to 100 (GB/day)
USD 1.4/GB
2.2 × 10 + 1.6 × 40 + 1.4 × (Y - 50) (USD)
>100 (GB/day)
USD 1.2/GB
2.2 × 10 + 1.6 × 40 + 1.4 × 50 + 1.2 × (Y - 100) (USD)
Anti-ransomware
Charges are based on the size of the backup files and their storage duration. The price is USD 0.00013/GB/hour.
Log Management
Charges are based on the total daily storage volume (GB). The price is USD 7.2/1,000 GB.
FAQ
Modifying recommended policies
Yes, you can.
To modify the protection level assigned to a server, see Manage security authorizations for hosts and containers.
To modify the authorization binding for a serverless asset, see 3.2. Bind or unbind authorized assets.
To modify the default detection policy for OSS files in the SDK for malicious file detection, see Malicious File Detection.
To modify the periodic scan policy for CSPM, see Set and run a check policy.
To modify the scan policy for agentless detection, see Agentless detection.
To modify the log types ingested by CTDR, see Connect services to CTDR.
To modify the access configuration for an application protection policy, see Protection policy management.