Security Center protects your serverless assets with threat detection, vulnerability scanning, and baseline risk checks. This topic describes how to connect serverless assets to Security Center and start protection.
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account with a paid Security Center edition (Anti-virus, Premium, Enterprise, or Ultimate), or access to the pay-as-you-go purchase page if you are on the Free Edition or free trial
Serverless assets in a Running state under your Alibaba Cloud account
(For ECI assets) Access to the ACK or ACS cluster management console
Supported assets and features
Supported asset types
Security Center supports the following serverless asset types:
Elastic Container Instance (ECI) created from managed ACK clusters, dedicated ACK clusters, and ACK Serverless clusters
ECI instances created from Container Compute Service (ACS)
Serverless App Engine (SAE) instances
Lingjun resources of Platform for AI (PAI)
SAE instances with an instance type of 0.5 cores or less cannot be connected or scanned due to stability constraints.
Supported security features
Security Center provides three security capabilities for serverless assets:
Threat detection: Detects web shell (back door) files, suspicious network connections, and abnormal process behaviors. For the full list of supported checks, see Overview of CWPP (cloud workload) security alerts.
Vulnerability scanning: View detectable vulnerabilities on the Risk Governance > Vulnerabilitys page by clicking the number under Disclosed Vulnerabilities to open the Detectable Vulnerabilities panel. Vulnerability scans run on a scheduled cycle — check the latest scan time on the Vulnerability Management page. Application vulnerabilities support scanning only; fixing is not supported. To eliminate the risk, manually upgrade or modify the software application based on the fixing suggestions in the vulnerability details.
Baseline risk checks: Detects and handles baseline risks, such as Restrict containers from running as root and Prohibit containers with kernel capabilities in the Kubernetes (ECI) Pod General International Security Best Practices Baseline. Baseline checks run on a scheduled cycle — check the latest check time on the Baseline Check page. For supported checks, see Baseline check items.

Security Center classifies connected serverless assets by container runtime status. Supported features vary by instance type:
| Instance type | Supported security features |
|---|---|
| Elastic Container Instance | Threat detection, vulnerability scanning, baseline risk checks |
| RunD container instance | Threat detection |
Billing
The serverless security protection feature uses pay-as-you-go tiered pricing. The public preview ended on July 31, 2024 (UTC+8).
How billing works
Billing starts after you enable and authorize serverless assets.
Billing method: Number of authorized vCores × actual protection duration. Duration is measured in seconds and accumulates only while the client is online.
Billing cycle: Bills are settled daily and generated the next day (T+1).
First billing cycle: Starts from the day you enable the feature to the end of that calendar month. Subsequent cycles are full calendar months.
Pricing tiers
Tiered pricing is based on cumulative monthly usage:
| Cumulative monthly usage (core-seconds) | Price (USD/core/second) | Fee formula (U = daily usage in core-seconds) |
|---|---|---|
| Tier 1: 0–200,000,000 | 0.000003 | 0.000003 × U |
| Tier 2: 200,000,001–1,000,000,000 | 0.000002 | 0.000002 × (U − 200,000,000) + 0.000003 × 200,000,000 |
| Tier 3: 1,000,000,001–9,999,999,999,999 | 0.0000015 | 0.0000015 × (U − 1,000,000,000) + 0.000002 × 800,000,000 + 0.000003 × 200,000,000 |
Example: An account with 20,000 cores of serverless assets with the Security Center client attached.
Day 1: Cumulative monthly usage = 20,000 × 86,400 = 1,728,000,000 core-seconds, spanning all three tiers:
Tier 1 (0–200,000,000): $0.000003 × 200,000,000
Tier 2 (200,000,001–1,000,000,000): $0.000002 × 800,000,000
Tier 3 (1,000,000,001–1,728,000,000): $0.0000015 × 728,000,000
Day 1 total: $3,292
Day 2 onward (cumulative monthly usage already in Tier 3): $0.0000015 × (20,000 × 86,400) = $2,592/day
Stop billing
Security Center immediately stops detection and billing in the following situations:
Stop billing for all serverless assets:
On the Overview page, in the Pay-as-you-go Services area, turn off the Serverless Assets switch.
On the Asset Center > Serverless Assets page, click Stop Service.
Your Alibaba Cloud account has an overdue payment.
Stop billing for a specific asset:
On the Assets > Serverless Asset page, detach authorization from the target asset. See step 3.2 below.
Step 1: Install the Security Center client on ECI pods
ECI assets from ACK and ACS clusters require the Security Center client to be installed and running on each pod before protection can be applied.
Install the client by adding an annotation to your pod spec in YAML. The annotation differs by cluster type.
ACK Serverless cluster
Log on to the Container Service for Kubernetes (ACK) console and go to the management page of the target cluster.
In the left navigation pane, choose Workloads > Pods, then click Create From YAML.
In the YAML template, add the following annotation under
spec > template > metadata:annotations: k8s.aliyun.com/eci-aliyundun-enabled: 'true'Sample YAML:
apiVersion: apps/v1 # for versions before 1.8.0 use apps/v1beta1 kind: Deployment metadata: name: nginx-deployment-basic labels: app: nginx spec: replicas: 2 selector: matchLabels: app: nginx template: metadata: annotations: k8s.aliyun.com/eci-aliyundun-enabled: 'true' labels: app: nginx spec: # nodeSelector: # env: test-team containers: - name: nginx image: nginx:1.7.9 # replace it with your exactly <image_name:tags> ports: - containerPort: 80 resources: limits: cpu: "500m"
If you create a resource from an image instead of YAML, add the pod annotation k8s.aliyun.com/eci-aliyundun-enabled=true in the Advanced section. For details, see Create a stateless application from an image.

Managed or dedicated ACK cluster
Log on to the ACK console and go to the cluster management page. Deploy the ack-virtual-node component to schedule pods to ECI. For details, see Schedule a pod to an ECI.
In the left navigation pane, choose Workloads > Pods, then click Create From YAML. Add the following to your YAML template: Sample YAML:
Under
metadata: add the annotationk8s.aliyun.com/eci-aliyundun-enabled: "true"Under
spec > containers: set the environment variableECI_CONTAINER_TYPE = sidecar
apiVersion: v1 kind: Pod metadata: name: test-aegis-alinux2-lifsea-x86 labels: eci: "true" annotations: k8s.aliyun.com/eci-aliyundun-enabled: "true" spec: containers: - name: sidecar image: registry-vpc.cn-shanghai.aliyuncs.com/eci_open/centos:7 command: - /bin/sh - -c args: - sleep inf env: - name: ECI_CONTAINER_TYPE value: sidecar - name: nginx image: registry-vpc.cn-shanghai.aliyuncs.com/eci_open/centos:7 command: - /bin/sh - -c args: - sleep inf
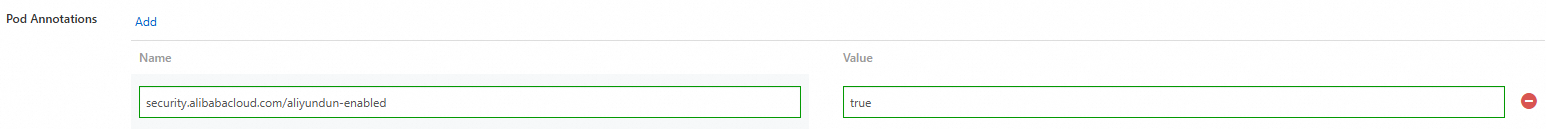
ACS cluster
Log on to the Container Compute Service console and go to the management page of the target cluster.
In the left navigation pane, choose Workloads > Stateless, then click Create From YAML.
In the YAML template, add the following annotation under
spec > template > metadata:annotations: security.alibabacloud.com/aliyundun-enabled: 'true'Sample YAML:
apiVersion: apps/v1 # for versions before 1.8.0 use apps/v1beta1 kind: Deployment metadata: name: nginx-deployment-basic labels: app: nginx spec: replicas: 2 selector: matchLabels: app: nginx template: metadata: labels: app: nginx alibabacloud.com/compute-class: general-purpose alibabacloud.com/compute-qos: default annotations: security.alibabacloud.com/aliyundun-enabled: 'true' spec: # nodeSelector: # env: test-team containers: - name: nginx image: anolis-registry.cn-zhangjiakou.cr.aliyuncs.com/openanolis/nginx:1.14.1-8.6 # replace it with your exactly <image_name:tags> ports: - containerPort: 80 resources: limits: cpu: "500m"
If you create a resource from an image, add the pod annotation security.alibabacloud.com/aliyundun-enabled=true in the Advanced Configuration section. For details, see Create a resource from an image and Overview of ACS pods.
Step 2: Enable pay-as-you-go
Choose the path that matches your current Security Center edition.
Free Edition or free trial users
Go to the Security Center purchase page and log on with your Alibaba Cloud account.
Set Billing Method to Pay-as-you-go and set Serverless Asset Protection to Yes.
Click Custom Quota Binding. In the dialog box, select All Servers or Specific Servers to configure which assets to authorize.
ImportantWithout custom binding, all assets are authorized by default, and new assets are automatically authorized going forward.

Read the Security Center Terms of Service, then click Order Now.
After the order completes, Security Center automatically connects to ECI instances and SAE applications in a Running state and attaches authorization based on your Authorization Management configuration.
Paid edition users (Anti-virus, Premium, Enterprise, or Ultimate)
Log on to the Security Center console.
In the left navigation pane, choose Assets > Serverless Asset. In the upper-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
On the Serverless Asset page, click Activate Now. Alternatively, turn on the Serverless Asset Protection switch in the Pay-as-you-go area on the right side of the Overview page.
In the confirmation dialog box, click Custom Quota Binding to select which assets to authorize, then click OK.
ImportantWithout custom binding, authorization follows this logic: - First time enabling: All assets are authorized by default, and new assets are automatically authorized. - Re-enabling: Previously authorized assets are reattached. If no ECI instances or SAE applications were authorized before, all assets are authorized by default, and authorization is automatically attached to new assets. - After clearing an overdue payment: Previously authorized assets are automatically reattached.
Select Security Center Service Level Agreement., then click Activate Now.
Step 3: Manage authorized assets
3.1 Sync assets
After enabling protection, sync the latest asset information to confirm that the Security Center client is installed and running on your target assets.
Log on to the Security Center console.
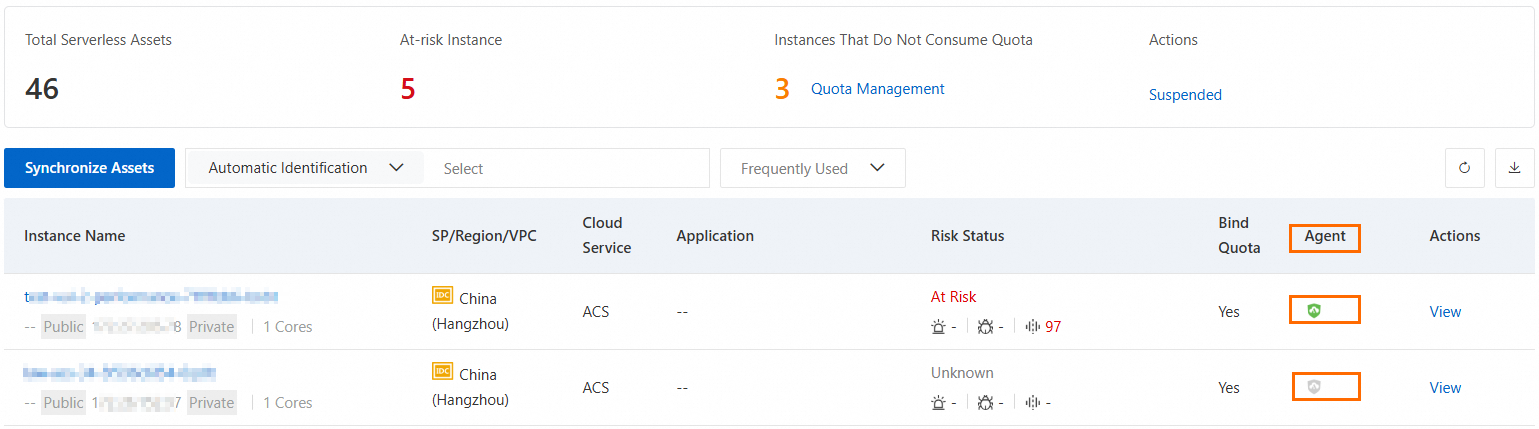
In the left navigation pane, choose Asset > Serverless Asset, then click Synchronize Assets. Security Center pulls the latest serverless asset information and refreshes the list. Syncing takes about one minute.
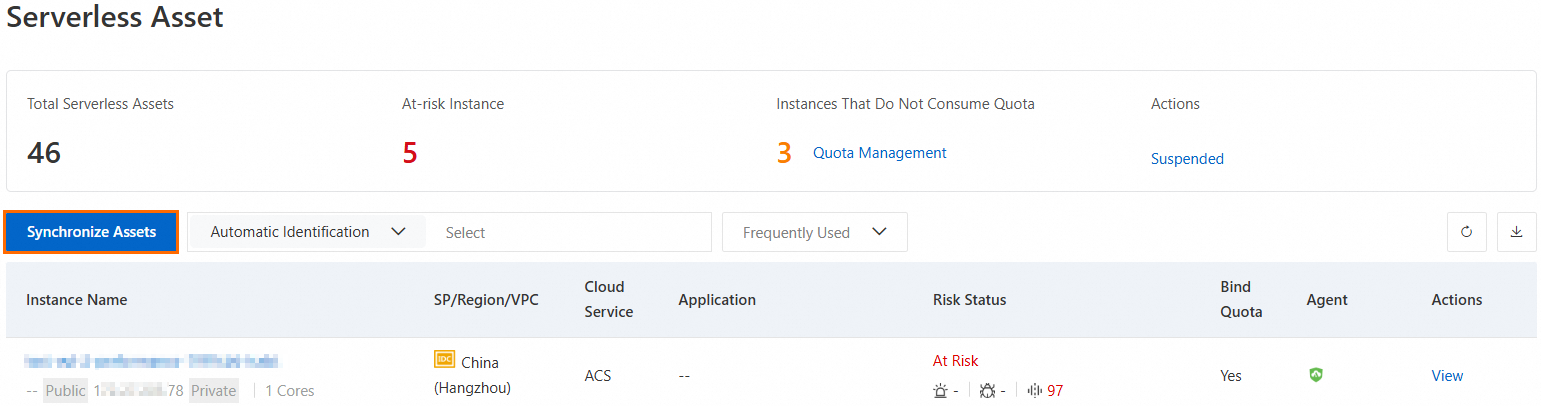
After syncing, check the Agent column for each asset. If the icon is gray, follow step 1 to install or repair the client, then restart the asset instance. Click Synchronize Assets again to refresh the status.
Green: The client is online and running. Attach authorization to start protection.
Gray: The client is offline (not installed, network issues, or other reasons). Security features are unavailable even after attaching authorization.
After creating or restarting any serverless asset instance, click Synchronize Assets to update the asset list.
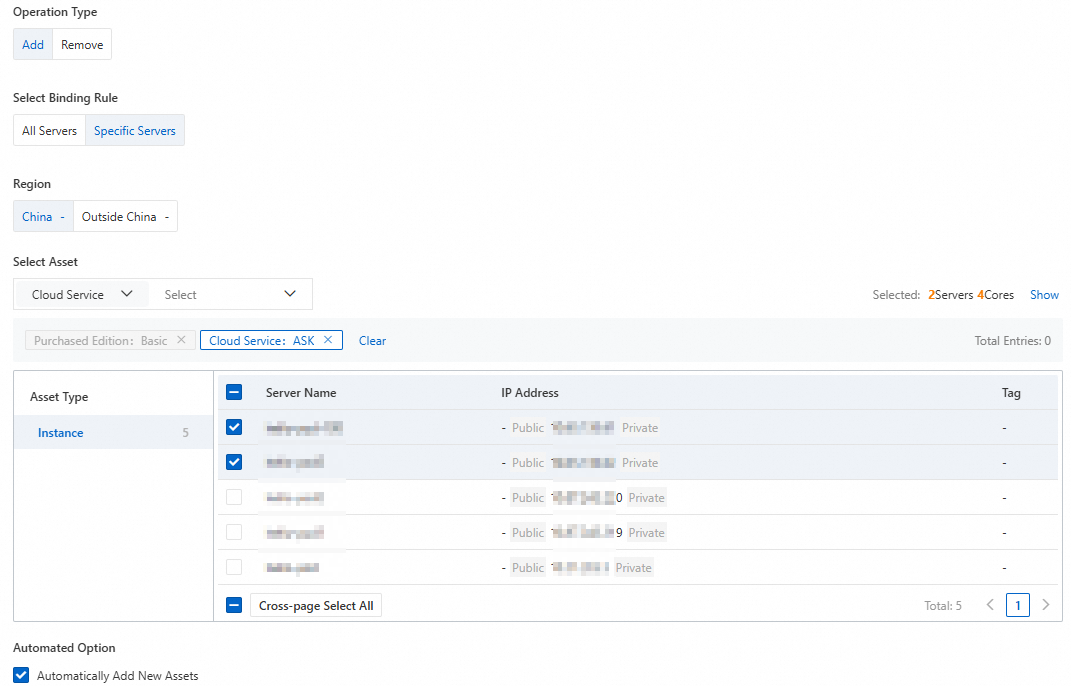
3.2 Attach or detach authorization
After the Security Center client is online, attach authorization to enable security protection for the asset. Detach authorization from assets that no longer require protection.
Choose the approach based on your protection scope:
| Approach | When to use | Effect |
|---|---|---|
| Protect all assets | Default binding is already in place | Authorizes all assets and automatically authorizes new ones |
| Protect specific assets | Use Custom Quota Binding during activation | Selects only the target assets for protection |
| Exclude specific assets | All assets are bound by default and some do not need protection | Detach authorization from assets that do not require protection |
To attach or detach authorization:
On the Assets > Serverless Asset page, click AInstances That Do Not Consume Quota under Quota Management above the asset list.
In the Quota Management dialog box, select Add or Remove, select the target assets, then click OK. To automatically authorize new serverless assets going forward, select Automatically Add New Assets.
Step 4: View and handle security risks
After an asset is connected and authorized, Security Center starts real-time threat detection for that instance. Vulnerability scans and baseline risk checks run on their respective scheduled cycles. Check the latest scan time on the Vulnerability Management or Baseline Check page.
On the Assets > Serverless Asset page, check the Risk Status column. An At-risk Instance label indicates that alerts, vulnerabilities, or baseline risks have been detected.
Click the asset name or click View in the Actions column to open the asset's risk detail page.
Click the Alerts, Vulnerabilities, or Configuration Risks card to view the corresponding risk items.

Handle alerts: Click Details in the Actions column to review the alert and determine whether it represents a real risk. Then click Handle:
Real risk: isolate the threat.
Not a real risk or can be deferred: add to whitelist, ignore, or mark as manually handled.
Handle vulnerabilities: Click the Vulnerabilities card to view detected vulnerabilities. Address all detected vulnerabilities promptly, as they represent weaknesses that attackers can exploit. One-click fixing is not supported for application vulnerabilities — fix them manually following the instructions in the vulnerability details. For more information, see View and handle vulnerabilities.
Handle baseline risks: Click the Configuration Risks card to view detected baseline risks. Click Details in the Actions column to review the risk details and hardening suggestions, then decide whether to fix or whitelist the risk. If the Fix button appears in the Risk Handling list on the risk details page, fix the baseline risk directly in Security Center.
What's next
Review threat detection alert types in Overview of CWPP (cloud workload) security alerts
Review all supported baseline checks in Baseline check items
Learn how to handle detected vulnerabilities in View and handle vulnerabilities