ApsaraDB RDS for SQL Server supports three database account types: privileged, standard, and global read-only. This topic explains when to use each type and how to create them in the console.
Choose an account type
| Account type | Permissions on existing databases | Permissions on new databases | Instance limit |
|---|---|---|---|
| Privileged | Automatically granted db_owner on all databases at creation | No access; grant manually via console | 1 per instance |
| Standard | None by default; grant read/write, read-only, or owner per database at creation | No access; grant manually | No limit |
| Global read-only | Automatically granted read-only on all databases at creation (excludes master and rdscore (if it exists)) | Automatically granted read-only | 2 per instance |
When to use which type:
Privileged account: Use as your primary administration account. It gets
db_owneraccess on all existing databases automatically, making it suitable for DBA tasks across the instance.Standard account: Use for application connections or role-based access. Assign permissions per database and per role (read/write, read-only, or owner) to follow the principle of least privilege.
Global read-only account: Use for read-heavy workloads such as analytics, reporting, or monitoring. It automatically covers all current and future databases without requiring per-database authorization.
Prerequisites
Before you begin, ensure that you have:
A running ApsaraDB RDS for SQL Server instance
A privileged account or superuser account (SA permissions) as the first account on the instance — standard and global read-only accounts can only be created after one exists
(For global read-only accounts only) An instance running SQL Server 2016 or later on the General-purpose or dedicated instance family
Create an account
Go to the Instances page. In the top navigation bar, select the region where your RDS instance resides. Click the instance ID.
In the left navigation pane, click Accounts.
Click Create Account and fill in the parameters for your account type.
Privileged account
| Parameter | Description |
|---|---|
| Database account | Enter a name that starts with a letter and ends with a letter or digit. The name can contain lowercase letters, digits, and underscores (_). Avoid keywords. |
| Account type | Select Privileged Account. One privileged account is allowed per instance. |
| New password | 8–32 characters. Must include at least three of the following: uppercase letters, lowercase letters, digits, and special characters (!@#$%^&*()_+-=). |
| Confirm password | Re-enter the password. |
| Apply password policy | (Optional) Attach a password policy to control the validity period and enhance security. |
| Description | (Optional) Up to 256 characters. |
Standard account
| Parameter | Description |
|---|---|
| Database account | Enter a name that starts with a letter and ends with a letter or digit. The name can contain lowercase letters, digits, and underscores (_). Avoid keywords. |
| Account type | Select Standard Account. |
| Authorize database | (Optional) Grant the account access to one or more databases. In the Unauthorized databases list, select a database, click |
| New password | 8–32 characters. Must include at least three of the following: uppercase letters, lowercase letters, digits, and special characters (!@#$%^&*()_+-=). |
| Confirm password | Re-enter the password. |
| Apply password policy | (Optional) Attach a password policy to control the validity period and enhance security. |
| Description | (Optional) Up to 256 characters. |
Global read-only account
| Parameter | Description |
|---|---|
| Database account | Enter a name that starts with a letter and ends with a letter or digit. The name can contain lowercase letters, digits, and underscores (_). Avoid keywords. |
| Account type | Select Global Read-Only Account. Two global read-only accounts are allowed per instance. After creation, the account is automatically granted read-only access to all existing databases and any databases added later. |
| New password | 8–32 characters. Must include at least three of the following: uppercase letters, lowercase letters, digits, and special characters (!@#$%^&*()_+-=). |
| Confirm password | Re-enter the password. |
| Apply password policy | (Optional) Attach a password policy to control the validity period and enhance security. |
| Description | (Optional) Up to 256 characters. |
Click OK. After the page refreshes, the account appears in the account list.
Permission behavior reference
Each account type behaves differently when databases are added, deleted, or recreated. Understanding this helps you avoid unexpected access issues.
Privileged account
| Scenario | Behavior |
|---|---|
| Account created | Automatically granted db_owner on all existing databases. |
| New database added | No access. Modify the account's permission scope to grant db_owner on the new database. |
| Account deleted | Permanently removes the account and all its permissions. |
| Account recreated | Automatically granted db_owner on all existing databases, regardless of the account name used. New databases still require manual permission updates. |
Standard account
| Scenario | Behavior |
|---|---|
| Account created | No permissions unless you authorize databases at creation. |
| New database added | No access. Manually add the database and set permissions. |
| Account deleted | Permanently removes the account and all permissions. Application connections using this account will fail — update your application credentials promptly. |
| Account recreated with the same name | Starts with no permissions. Original permissions are not restored. Reauthorize databases manually. |
Global read-only account
| Scenario | Behavior |
|---|---|
| Account created | Automatically granted read-only access to all existing databases. No access to master or rdscore (if it exists) system databases. |
| New database added | Automatically granted read-only access. No manual action needed. |
| Account deleted | Permanently removes the account and all its read-only permissions. |
| Account recreated | Automatically granted read-only access to all existing databases. New databases are also covered automatically. |
Security best practices
Use strong passwords. Set a complex password and rotate it regularly. Attach a password policy to enforce expiration rules.
Apply least privilege. Create accounts based on business roles and assign only the permissions each role needs. If write access is not required, use read-only permissions.
Avoid using a privileged account in applications. Use a standard account with scoped permissions for application connections instead.
FAQ
Can accounts created on a primary instance be used on read-only instances?
How do I create an account without the password complexity requirements?
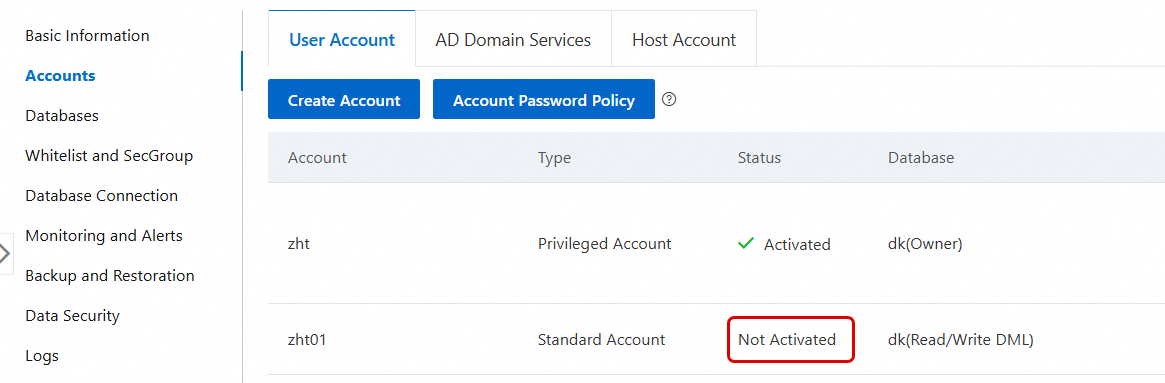
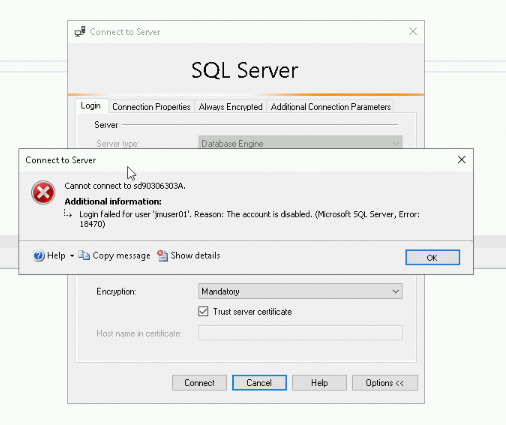
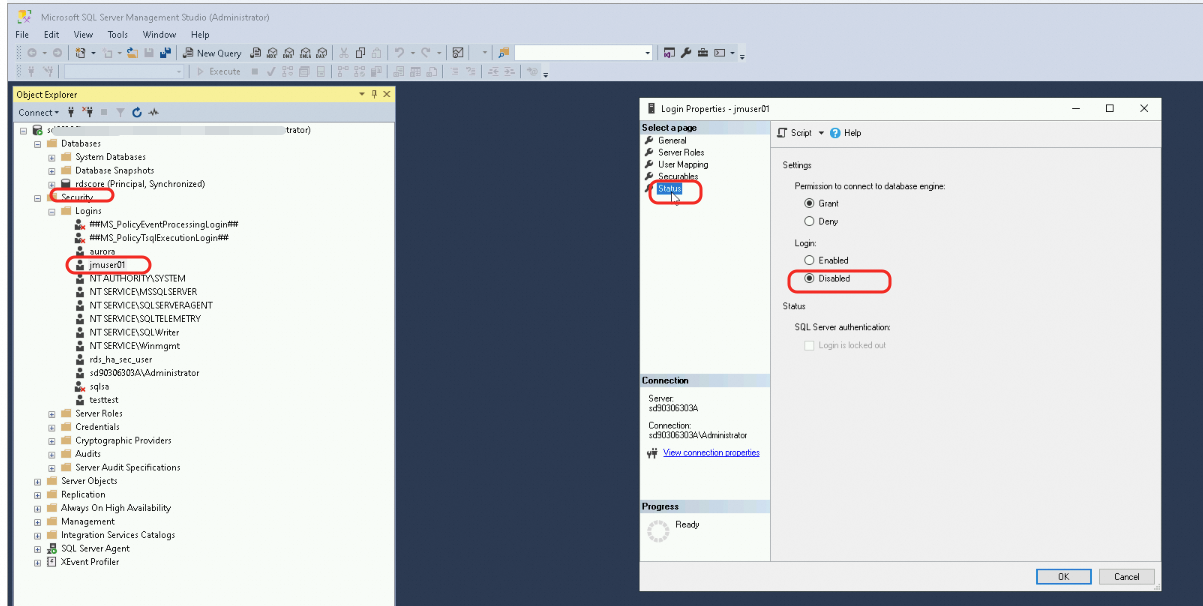
Why does my account show as Inactive and return "The account is disabled."?
Why does CreateAccount return AccountLimitExceeded?
Next steps
Create a database account with SA permissions using the console.
Modify account permissions after adding new databases.
Create accounts via API: CreateAccount.
Delete accounts via API: DeleteAccount.