ApsaraDB RDS for SQL Server manages password expiration at the Windows host layer. By default, host account passwords expire after 42 days, which causes logon failures if not addressed. Configure a custom password policy to control how long passwords remain valid and prevent unexpected lockouts.
Host account passwords expire after 42 days by default. Expiration causes logon failures. Configure a password policy before the 42-day limit is reached. Host accounts apply the policy automatically; user accounts require manual application.
Default password behavior
| Account type | Default expiration | Policy application |
|---|---|---|
| Host account | 42 days (Windows default) | Automatic |
| User account | Never expires | Manual |
Limits
This feature is not available for the following instance types:
Shared instances
SQL Server 2008 R2 instances
Serverless ApsaraDB RDS for SQL Server instances
The RDS instance must use a General-purpose or dedicated instance type, and a subscription or pay-as-you-go billing method.
Usage notes
When you create an account and apply the password policy that you configured for the account, the password cannot contain the username of the account. For example, if the username is Test240903, the password cannot be Test240903abc.
Step 1: Configure a password policy
Go to the Instances page. In the top navigation bar, select the region where your RDS instance resides. Find the instance and click its ID.
In the left-side navigation pane, click Accounts.
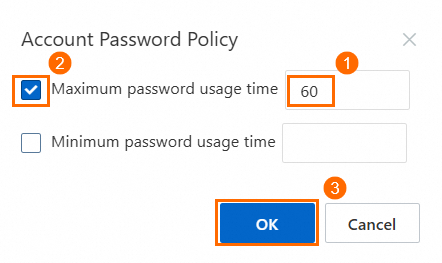
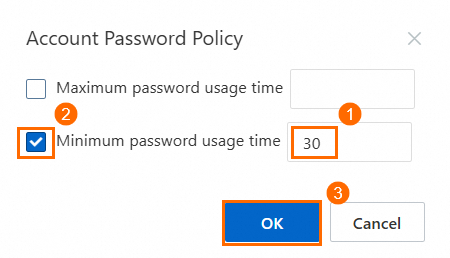
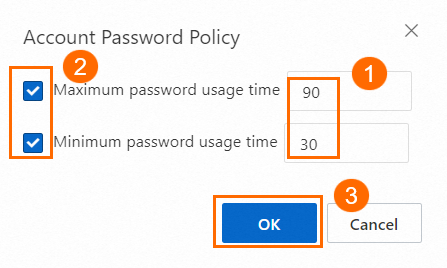
Click Account Password Policy, configure the parameters, select the target policy, and then click OK.
You can configure one or both of the following parameters:
| Parameter | Description | Range (days) |
|---|---|---|
| Maximum password usage time | How long a password can be used before the account must change it. | 0–999 |
| Minimum password usage time | How long a password must be used before the account can change it. Must not exceed Maximum password usage time. | 0–998 |
Example 1: Maximum password age only
To require a password change every 60 days, set Maximum password usage time to 60.
Example 2: Minimum password age only
To prevent password changes within the first 30 days, set Minimum password usage time to 30.
Example 3: Both maximum and minimum password age
To require a password change every 90 days and prevent changes within the first 30 days, set Maximum password usage time to 90 and Minimum password usage time to 30.
Step 2: Apply the policy to user accounts
Host accounts apply the configured policy automatically. For user accounts, apply the policy manually using either of the following approaches.
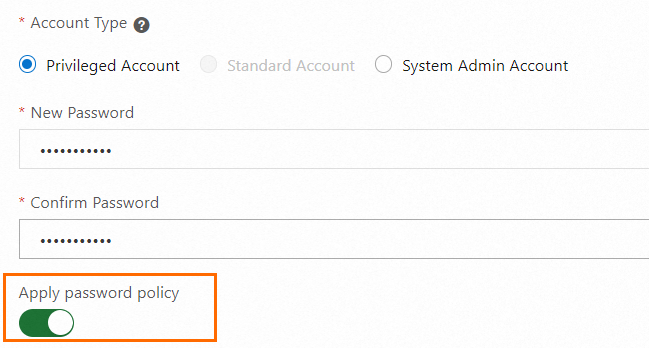
Apply when creating a user account
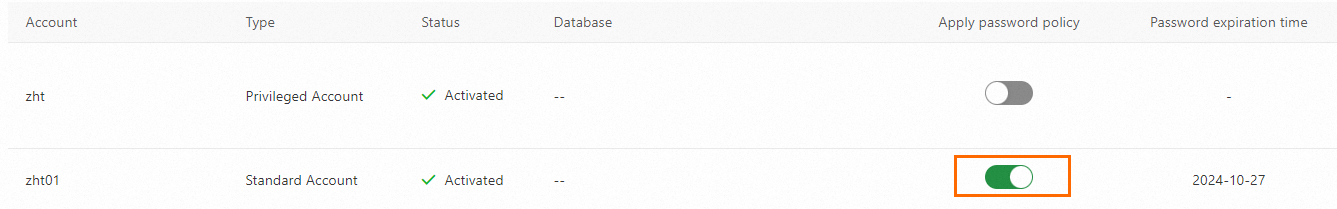
On the Accounts > User Accounts page, apply the password policy when you create a standard account or a privileged account or a database account with SA permissions.
Apply to existing user accounts
On the Accounts > User Accounts page, apply the password policy to existing accounts.
FAQ
Do host accounts apply the policy automatically?
Yes. After you configure the policy in the RDS console, host accounts apply it immediately with no additional steps. User accounts require manual application as described in Step 2.
API reference
ModifyAccountSecurityPolicy — Configure SQL Server account password policies
ModifyAccountCheckPolicy — Modify SQL Server account password policies
CreateAccount — Create a database account (apply policy at creation time)
ModifyAccountSecurityPolicy - Configure SQL Server account password policies
ModifyAccountCheckPolicy - Modify SQL Server account password policies






