By default, RDS for PostgreSQL uses the prefer authentication mode, which lets clients connect without SSL by passing PGSSLMODE=disable. This means SSL encryption can be bypassed even after you enable it on the instance. To block non-SSL connections entirely, configure client access control using one of the methods described in this topic.
Prerequisites
Before you begin, ensure that you have:
SSL encryption enabled on your RDS instance. See Configure SSL encryption or Configure a custom certificate
(Required for Method 1 only) A client CA certificate configured on the RDS instance. See Configure a client CA certificate
Choose a method
| Method | How it works | When to use |
|---|---|---|
| Method 1: Configure a client ACL | The RDS instance validates the client using a client certificate and private key before allowing the connection | You want certificate-based client verification in addition to SSL enforcement |
| Method 2: Configure pg_hba.cnf | Changes the connection type in pg_hba.cnf to hostssl, rejecting all non-SSL connections | You want a straightforward SSL enforcement without client certificate validation |
Method 1: Configure a client ACL
After a client CA certificate is configured, set up an Access Control List (ACL) on the RDS instance. The instance validates the client using the client certificate and private key before establishing the connection.
Configuring the ACL takes approximately 1 minute, during which no operations can be performed on the RDS instance.
Go to the instance details page, then click Modify to the right of Configure ACL.
Select one of the following authentication methods: For most production use cases, use
verify-full(PostgreSQL 12 or later) orverify-ca.Authentication method What it does Version requirement verify-caEstablishes an SSL connection and validates the client certificate against the CA — verify-fullEstablishes an SSL connection, validates the client certificate, and checks that the Common Name (CN) in the certificate matches the connecting username PostgreSQL 12 or later certUses the client certificate (instead of a password) to authenticate; establishes an SSL connection and validates the CN against the username —
Method 2: Configure pg_hba.cnf
Use the AD Domain Service Configuration feature to modify pg_hba.cnf and set the connection type to hostssl. This rejects all non-SSL client connections.
Go to the Instances page. In the top navigation bar, select the region where your RDS instance resides, then click the instance ID.
In the left navigation pane, click Accounts, then click the AD Domain Services tab.
In the first record, change the value in the TYPE column to
hostssl.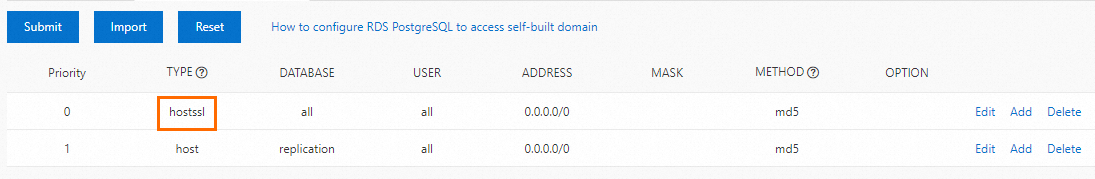
Click Submit.
NoteAfter you click Submit, the instance status changes to Maintaining Instance for approximately 1 minute. The new configuration applies only to new connections. Close existing connections and reconnect for the change to take effect.