SSL encryption protects data transmitted between a database client and an ApsaraDB RDS for PostgreSQL instance. This topic walks you through configuring a cloud certificate to enable SSL encryption and connecting to your instance using the encrypted connection.
Certificate types
Three certificate types are available for SSL encryption. Each serves a different purpose:
| Item | Cloud certificate | Custom certificate | Client CA certificate |
|---|---|---|---|
| Purpose | Server certificate — the client uses it to authenticate the server | Server certificate — the client uses it to authenticate the server | Client certificate — the server uses it to authenticate the client |
| Issued by | Alibaba Cloud | A certification authority (CA) or self-signed | Self-signed |
| Validity period | 365 days | Customized | Customized |
| Protected endpoints | 1 | 1 or more | Varies based on the cloud or custom certificate used |
You must configure either a cloud certificate or a custom certificate to enable SSL encryption and authenticate the server. Configuring a client CA certificate is optional — it lets the server authenticate the client.
Cloud certificates and custom certificates both protect the server side. To protect both the internal and public endpoints simultaneously, use a custom certificate.
ApsaraDB RDS for PostgreSQL supports TLS 1.0, TLS 1.1, and TLS 1.2.
Prerequisites
Before you begin, ensure that you have:
-
An ApsaraDB RDS for PostgreSQL instance running PostgreSQL 10 or later with cloud disks (Serverless instances are not supported)
-
pgAdmin 4 installed — download it from pgAdmin 4
-
An IP address whitelist configured and at least one account created on the instance — see Configure an IP address whitelist and Create a database and an account
Usage notes
-
Certificate renewal: A cloud certificate is valid for 365 days. Before it expires, Alibaba Cloud sends you an email and an internal message notification, then automatically renews the certificate. To customize the renewal schedule, use the Schedule Event dialog box. See Manage scheduled events.
-
Performance impact: Enabling SSL encryption increases CPU utilization and adds read and write latency.
-
Existing connections: After enabling SSL, close all existing connections and re-establish them for encryption to take effect.
-
Instance restarts: The following operations restart the RDS instance (approximately 3 minutes each). Perform them during off-peak hours:
-
Configuring a cloud certificate
-
Changing the endpoint protected by a configured cloud certificate
-
Disabling SSL encryption
-
Step 1: Enable SSL with a cloud certificate
-
Go to the Instances page. In the top navigation bar, select the region where your RDS instance resides, then click the instance ID.
-
In the left-side navigation pane, click Data Security. On the page that appears, click the SSL tab.
If the SSL tab is not visible, verify that your instance meets the requirements listed in Prerequisites.
-
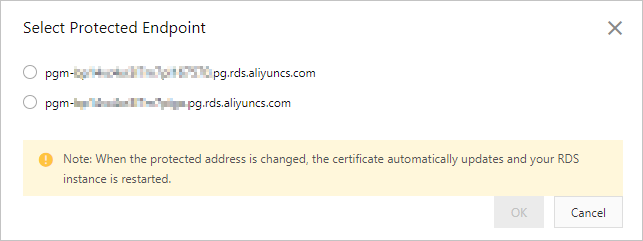
Select Cloud Certificate. Click Configuration next to Configure Database Certificate (to Prevent Database Disguise), then select the endpoint to protect.
- Each cloud certificate protects one endpoint. If your instance has a public endpoint, protect it — the internal endpoint is accessible only within your private network and is lower risk, while the public endpoint is more exposed. - If only the internal endpoint appears in the Select Protected Endpoint dialog box, no public endpoint has been applied for yet. See View and change the endpoints and port numbers of an ApsaraDB RDS for PostgreSQL instance. - After you click save, the instance status changes to Modifying SSL Settings for approximately 3 minutes. Wait until the status returns to Running before proceeding.
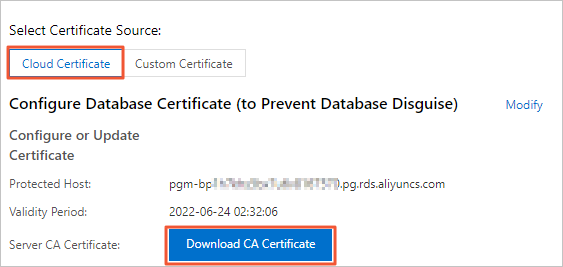
Step 2: Download the server CA certificate
After configuring the cloud certificate, download the server CA certificate and save it to your client machine. The client uses this certificate to authenticate the RDS instance during connection.
-
Select Cloud Certificate, then click Download CA Certificate.
-
Decompress the downloaded file. The package contains three files:
File format Use case PEM Most clients and tools — use this by default JKS Java applications. The JKS file is a pre-converted truststore. Password: apsaradbP7B Windows applications that require PKCS#7-formatted certificate files
Step 3: Connect to your RDS instance over SSL
Connect with pgAdmin
This example uses pgAdmin 4 V6.2.0. If your version differs, refer to the pgAdmin 4 official documentation.
-
Start pgAdmin 4.
If this is the first time you open a newer version of pgAdmin, you'll be prompted to set a master password to protect saved credentials.
-
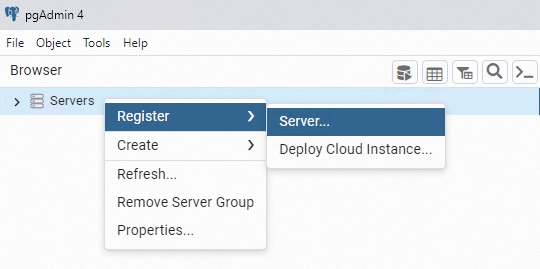
Right-click Servers and choose Register > Server.
-
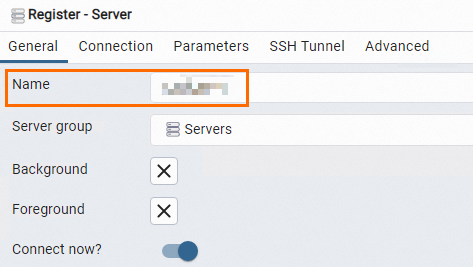
On the General tab, enter a name for the server.
-
Click the Connection tab and fill in the connection details.
Parameter Description Host name/address The endpoint of the RDS instance. Use the internal endpoint to connect over a private network, or the public endpoint to connect over the Internet. To find these values, see View and change the endpoints and port numbers of an ApsaraDB RDS for PostgreSQL instance. Port The port number of the RDS instance. Username The account username. See Create a database and an account. Password The account password. 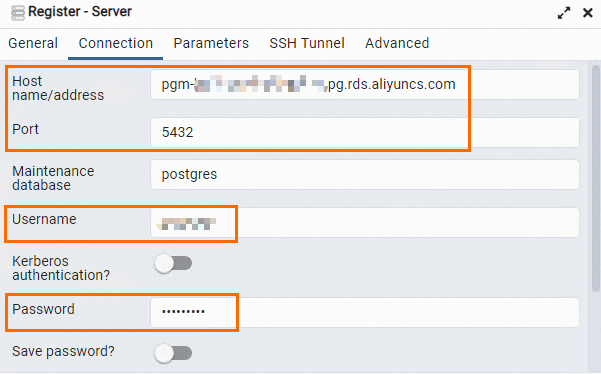
-
Click the Parameters tab and configure the SSL settings.
Parameter Description SSL mode For security purposes, we recommend that you set this parameter to Require, Verify-CA, or Verify-Full. The following describes each value: Require — the client encrypts connections but does not validate the RDS instance. Verify-CA — the client encrypts connections and validates the RDS instance. Verify-Full — the client encrypts connections, validates the RDS instance, and checks whether the CN or DNS specified in the server CA certificate matches the Host name/address value. Root certificate Required when SSL mode is set to Verify-CA or Verify-Full. Set this to the path of the PEM file downloaded in step 2 (for example, D:\CA\aliyunCA\). -
Click Save. If the connection details are correct, pgAdmin connects to the instance successfully.
ImportantThe
postgresdatabase is a system database. Do not run operations on it.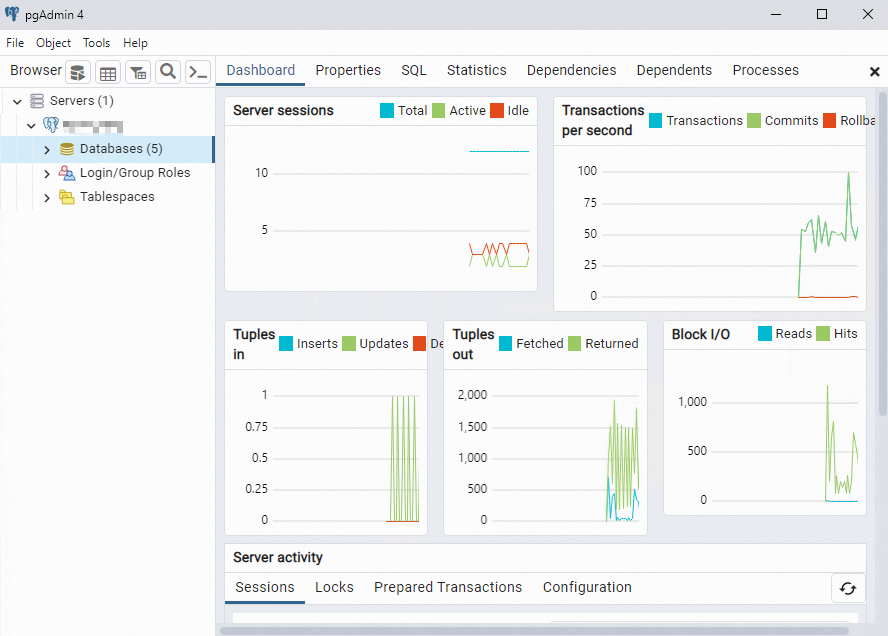
For additional connection methods (psql command-line client, Java JDBC, and others), see Connect to an ApsaraDB RDS for PostgreSQL instance over SSL connections.
Next steps
-
Configure a custom certificate on an ApsaraDB RDS for PostgreSQL instance — to protect multiple endpoints simultaneously or use your own CA-signed certificate
-
Configure a client CA certificate on an ApsaraDB RDS for PostgreSQL instance — to have the server authenticate the client
-
Connect to an ApsaraDB RDS for PostgreSQL instance over SSL connections — for connection examples using JDBC and other clients