Role-based single sign-on (SSO) with SAML 2.0 allows users from your corporate identity provider (IdP) to access Alibaba Cloud by assuming a Resource Access Management (RAM) role. This method enables you to manage user identities centrally in your IdP without having to create and manage individual RAM users in Alibaba Cloud.
How role-based SAML SSO works
Federated users can access Alibaba Cloud resources through the console or programmatically through the APIs.
Console access
The following diagram illustrates the IdP-initiated flow for a user logging on to the Alibaba Cloud Management Console.
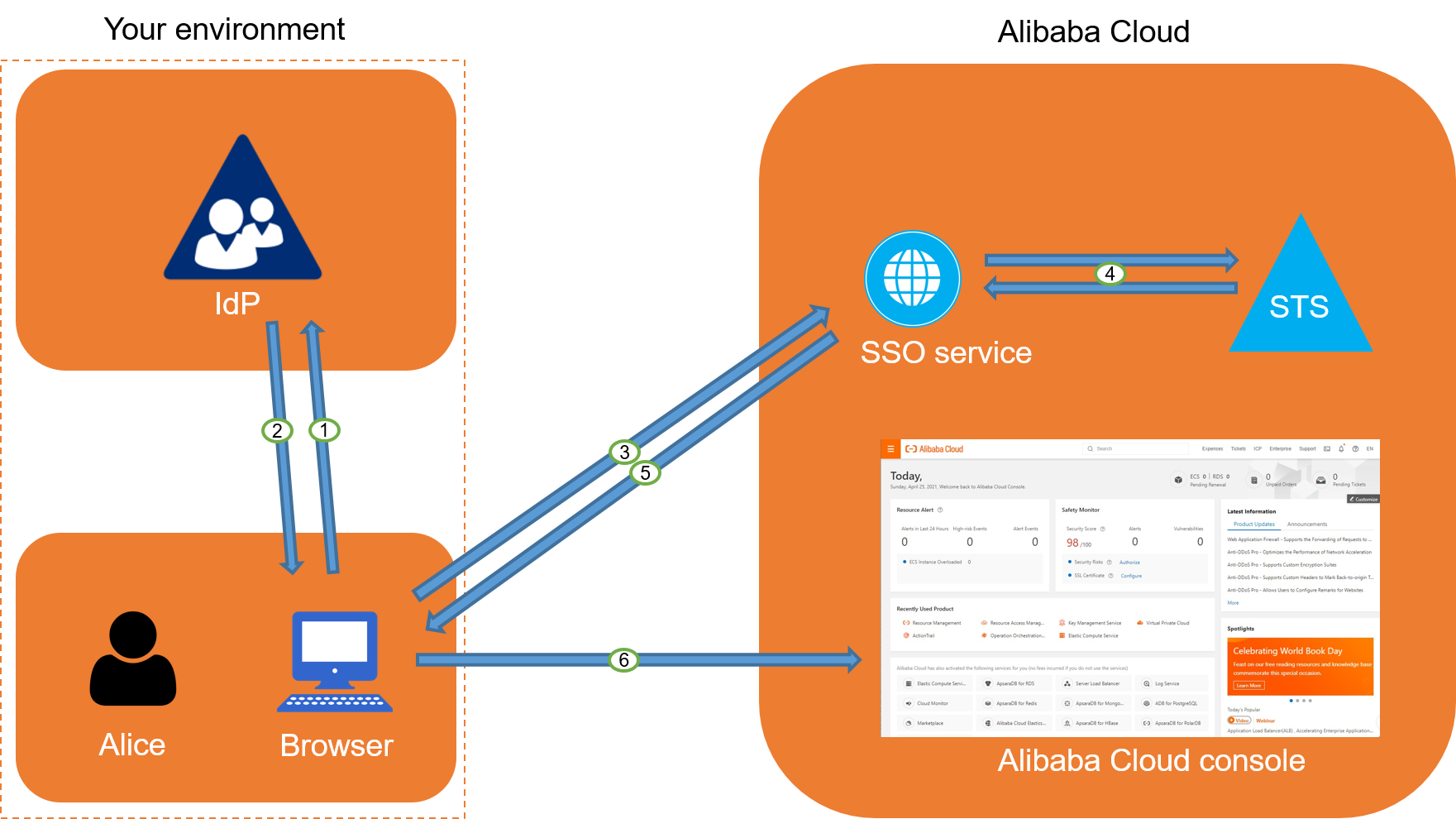
A user logs on to your corporate application portal and selects the Alibaba Cloud application.
Your IdP authenticates the user and generates a SAML response containing an assertion about the user's identity and the RAM roles they are permitted to assume. The IdP sends this response to the user's browser.
The browser forwards the SAML response to the Alibaba Cloud SSO endpoint.
The SSO service validates the assertion. If the assertion specifies multiple roles, the user is prompted to select which RAM role to assume.
The SSO service requests temporary credentials from the Security Token Service (STS) for the selected role.
STS returns a temporary credential, which the SSO service uses to generate a pre-signed URL for console access.
The SSO service redirects the user's browser to the Alibaba Cloud Management Console, and the user is logged on with the permissions of the assumed RAM role.
Programmatic access (API)
Federated users can also get temporary credentials to make direct API calls to Alibaba Cloud services.
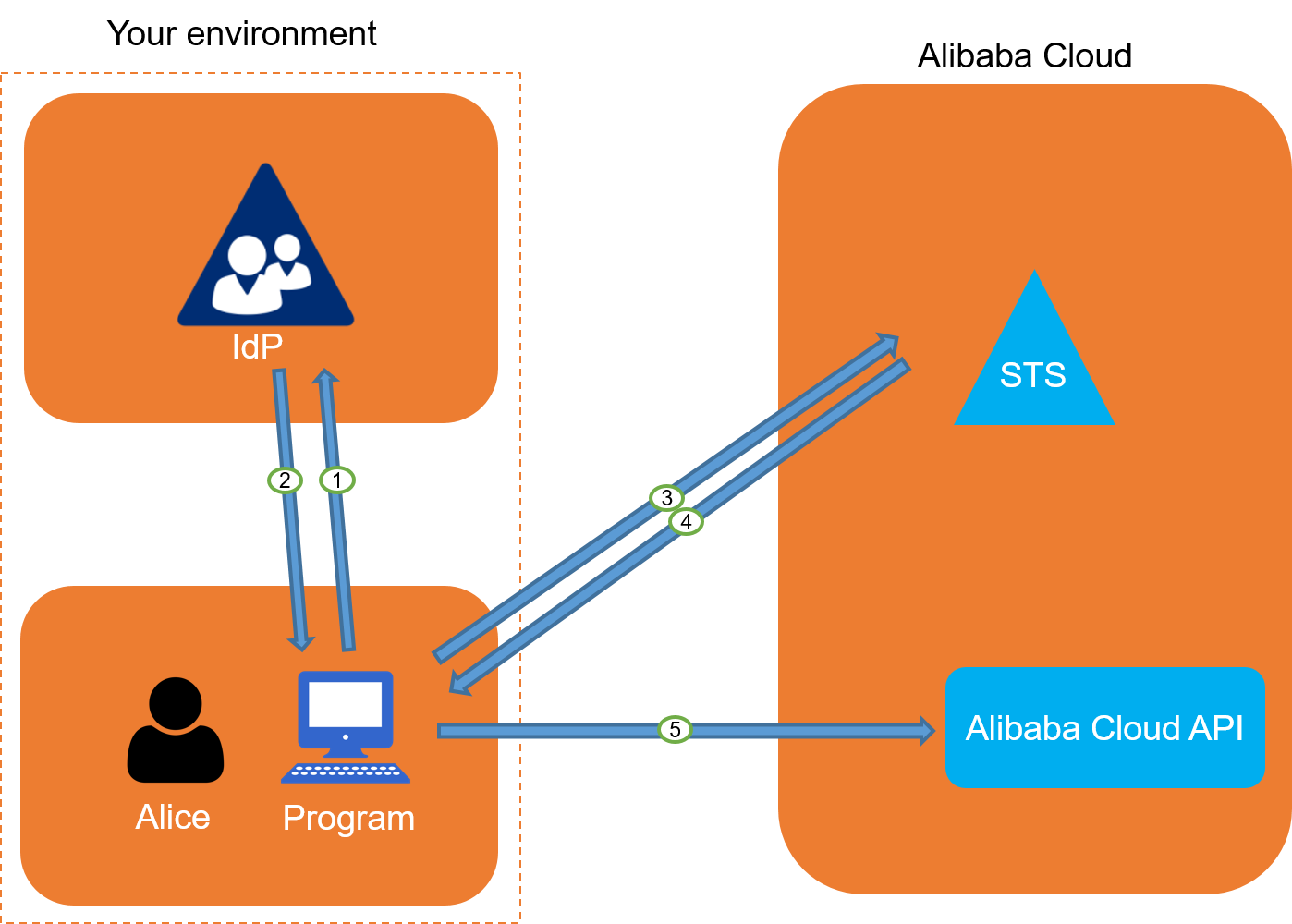
An application or script authenticates a user against your corporate IdP.
The IdP returns a SAML response to the application.
The application calls the AssumeRoleWithSAML API operation of STS, passing the SAML assertion, the ARN of the desired RAM role, and the ARN of the IdP.
STS validates the SAML assertion and confirms that the requested role is included in the assertion's attributes.
If the request is valid, STS returns temporary security credentials (an AccessKey ID, an AccessKey secret, and a security token).
The application uses these temporary credentials to make signed API requests to other Alibaba Cloud services.
Configuration overview
Setting up role-based SSO requires configuring a trust relationship in both Alibaba Cloud and your IdP.
Create a SAML IdP in Alibaba Cloud.
You provide metadata from your corporate IdP to Alibaba Cloud. This tells Alibaba Cloud to trust assertions from your IdP. For more information, see Configure SAML on Alibaba Cloud (as SP).
Create RAM roles for federation.
For each set of permissions you want to grant to federated users, you create a RAM role. The role's trust policy must specify the SAML IdP you created as the trusted principal. For more information, see Create a RAM role for a trusted IdP.
Configure your IdP.
You add Alibaba Cloud as a trusted service provider (SP) in your IdP and configure claim rules to send the required attributes in the SAML assertion. These attributes include the specific RAM roles a user is allowed to assume. For more information, see Configure Alibaba Cloud as the SP in your IdP.
Configuration tutorials
The following topics provide detailed tutorials for configuring role-based SAML SSO with common IdPs: